CVE-2026-31533 is a critical Linux kernel use-after-free flaw in the kernel TLS encryption path, published April 23, 2026, involving
For years, Windows administrators could treat Linux kernel CVEs as something that happened on the other side of the rack. That mental model has been obsolete for a while, but CVE-2026-31533 is a useful stress test because it does not arrive as a neat Windows component bug with a familiar KB number, reboot flow, and desktop-facing update banner.
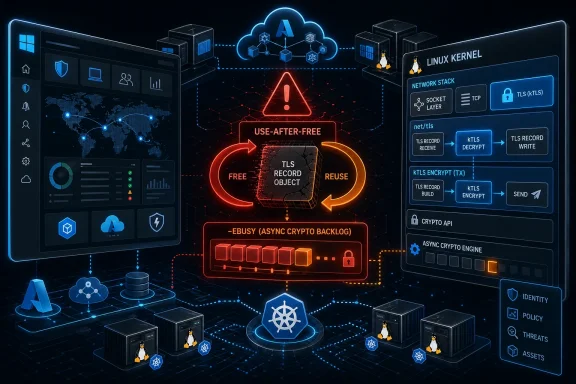
The vulnerability sits in the Linux kernel’s
The flaw is a classic low-level failure with a modern blast radius. A crypto request returns
That is why the CVSS 3.1 score assigned by kernel.org is 9.8 critical, with the familiar worst-case network vector: network-accessible, low complexity, no privileges required, no user interaction, and high impact to confidentiality, integrity, and availability. NVD had not supplied its own final score at the time reflected in the public record, but it had already associated the weakness with CWE-416, use-after-free. For defenders, the absence of a final NVD score is not a reason to wait; the vendor CNA’s scoring already says enough.
That is not a glamorous exploit primitive on its face. It is accounting. A sentinel value initialized to one is decremented at the wrong time. A scatterlist entry’s offset and length are restored twice. A wait function that should block for pending asynchronous callbacks can be tricked into believing there is nothing left to wait for.
But kernel security has always been full of bugs that look mundane until you ask what object lifetime they invalidate. Here, the bad accounting can allow a later
That is the essence of a use-after-free: not merely a crash, but a violation of the kernel’s ownership model. In benign conditions, it may panic or corrupt memory in ways that are difficult to reproduce. In hostile conditions, depending on surrounding allocation behavior, it may become a foothold for code execution or privilege escalation inside the kernel. The CVSS vector treats the theoretical remote impact as severe, and kernel operators should do the same until their distribution tells them otherwise.
The
The presence of
Backlogging crypto requests is a reasonable design. If the crypto layer cannot process an AEAD encryption request immediately, queuing it through cryptd is preferable to stalling everything or failing prematurely. But asynchronous design creates a contract: once work is queued, ownership and cleanup must be unambiguous.
CVE-2026-31533 breaks that contract. The callback path believes it owns cleanup, while the synchronous error path also decides to clean up after an async wait returns an error. Each path is defensible in isolation. Together, they violate the reference counting logic that tells the rest of the TLS code whether outstanding encryption work still exists.
This is why kernel bugs often evade casual review. The dangerous line is not always a reckless pointer dereference. It is the second “safe” cleanup call that only becomes unsafe when an uncommon return code, a queued callback, and a later send path line up in the right order. In production, those edge conditions tend to appear first under load, which is precisely where kTLS is most likely to be deployed.
The second clarification is more uncomfortable: Microsoft publishing or tracking a Linux kernel CVE is no longer unusual. Microsoft operates and ships Linux in meaningful ways. Azure hosts Linux at vast scale. Azure Linux is Microsoft’s own Linux distribution for cloud and infrastructure scenarios. WSL uses a Linux kernel component in its architecture. Security tooling, container hosts, AKS nodes, IoT deployments, and third-party appliances running in Microsoft-centered environments may all pull Windows administrators into Linux kernel patch triage.
That creates a taxonomy problem. A vulnerability can be “in Microsoft’s security guide” without being “in Windows.” It can affect assets managed by a Microsoft customer without affecting Windows Server itself. It can appear in enterprise scanners as a Microsoft-adjacent finding even though the actual remediation is a Linux kernel update from a distro channel, cloud image refresh, node replacement, or appliance vendor patch.
This is where many patch programs still stumble. They are organized around product families, not execution contexts. CVE-2026-31533 asks a more practical question: where in your estate is a vulnerable Linux kernel running with kTLS-capable networking paths, and who owns the reboot?
That distinction matters because enterprise Linux does not map cleanly to upstream kernel version numbers. Vendors routinely backport fixes without changing to a brand-new upstream kernel release. A server reporting a 5.15-derived kernel is not automatically vulnerable or safe based solely on the visible major and minor version. The package release, distro advisory, and vendor changelog matter.
The same is true in cloud environments. Golden images, marketplace appliances, Kubernetes node pools, and container-optimized hosts can lag behind upstream fixes even when the cloud provider has already published patched images. A fixed kernel sitting in a repository does not protect a running VM until the package is installed and the machine is booted into that kernel, unless a live-patching mechanism specifically covers the flaw.
For Windows-heavy administrators, this is one of the less forgiving parts of Linux patch management. Installing the package is only half the story. The running kernel is the security boundary. If
The vulnerability description implies a chain involving kernel TLS encryption, crypto request backlogging, the async cryptd callback, error handling in
But “specific” is not “impractical.” Kernel networking paths are reachable by design. TLS-enabled services are reachable by design. High-throughput workloads may be more likely to trigger backlog behavior. If BPF verdict programs are involved in the vulnerable path, the configuration and deployment model become part of the exploitability picture.
Defenders should resist two bad instincts. The first is panic: ripping out services before understanding exposure can cause more harm than the vulnerability. The second is complacency: dismissing a kernel use-after-free because the internal description sounds complicated has aged badly too many times. The right response is boring and disciplined—inventory, patch, reboot, verify.
That matters for risk communication. A CISO reading a Microsoft Security Update Guide entry may assume there is a Windows patch. A Windows admin may search WSUS or Intune and find nothing relevant. A Linux engineer may already have the fix queued through the distro’s kernel stream. Meanwhile, the vulnerability management platform keeps the ticket open because it sees
The answer is not to force every vulnerability into a Windows-shaped process. The answer is to make the process understand mixed estates. If the affected asset is an Azure Linux node, handle it through the Azure Linux update mechanism. If it is Ubuntu on Azure, follow Canonical’s advisory and package stream. If it is SUSE, Red Hat, Debian, Amazon Linux, or an appliance image, follow that vendor. If it is WSL, watch Microsoft’s WSL servicing path rather than assuming a general-purpose Linux distro kernel package applies.
This is the operational future Microsoft helped create by embracing Linux in the cloud. It is a better future than the old religious war, but it is not simpler. The administrator’s map now has to include kernels that do not come from Redmond but still run inside Redmond’s orbit.
The security tradeoff is that the kernel becomes responsible for more protocol-adjacent state. Bugs that might once have lived in a user-space TLS library can now appear in kernel paths that touch socket buffers, scatterlists, crypto APIs, BPF verdicts, and asynchronous callbacks. The blast radius changes because a process-level crash becomes kernel memory corruption.
This does not mean kTLS is a bad idea. It means kTLS should be treated like any other acceleration feature that moves complexity downward in the stack. When performance-critical code enters the kernel, patch latency matters more. So does configuration awareness. So does knowing whether a given service or distribution actually enables and uses the feature.
Many organizations will discover during this CVE that they do not know where kTLS is active. They know where Nginx runs, where Envoy runs, where storage appliances live, and where Kubernetes nodes terminate traffic. They may not know which of those paths use kernel TLS, which kernels have the vulnerable commits, and which hosts are merely carrying code that is not reachable in their configuration. That uncertainty is exactly why critical kernel CVEs tend to become broad patch events.
This is where severity ratings collide with calendars. A critical remotely reachable kernel flaw should normally move near the top of the queue. But many affected systems will be production Linux servers running under Windows-centric change management programs that are optimized for Patch Tuesday, not rolling kernel advisories.
The right comparison is not “does this feel worse than a Windows RCE?” The right comparison is “which internet-facing or high-risk Linux kernels in our estate are in the affected range, and how quickly can we get them onto a fixed build?” Some systems will be straightforward. Others—appliances, custom images, pinned Kubernetes nodes, legacy cloud VMs—will reveal debt.
There is also a verification trap. After patching, defenders should confirm the running kernel, not merely the installed package. In Linux incidents, it is common to find machines that installed a fixed kernel days earlier but never rebooted into it. That distinction is invisible to teams that treat package compliance as equivalent to runtime compliance.
The opposite mistake is also possible. A platform can appear safe because its version string looks unfamiliar, while the underlying kernel contains the affected code. That is why vendor advisories remain the authoritative remediation guide. The CPE is a starting point, not a court verdict.
Security teams should triage by exposure and ownership. Internet-facing TLS services, load balancers, reverse proxies, service mesh gateways, storage endpoints, and nodes running heavy encrypted traffic deserve early attention. Internal systems still matter, especially where untrusted tenants, containers, or lateral movement paths can reach the vulnerable networking surface. But the patch order should reflect real attack paths, not just a spreadsheet sorted by CVSS.
For Windows administrators pulled into the ticket, the useful move is not to debate whether “Linux belongs to another team.” It is to identify the asset owner, the distribution, the kernel package source, and the reboot plan. The CVE does not care which team’s name is on the CMDB entry.
That matters because many newer Linux deployments are not simple socket servers anymore. They are layered with eBPF policy engines, CNI plugins, traffic redirectors, tracing agents, and sidecar-heavy architectures. The kernel networking path is no longer just the kernel and the application; it is a crowded control plane.
This makes exposure analysis harder. A traditional server inventory might tell you what applications listen on which ports. It may not tell you which BPF programs are attached, which verdict paths can free records, or whether traffic handling differs between ordinary flows and accelerated TLS flows. In other words, the exploitability question may live below the level of tools many Windows-first shops routinely use.
That is not an argument for disabling BPF or kTLS on sight. It is an argument for understanding that modern Linux infrastructure has its own equivalent of Windows driver risk: privileged, high-performance kernel extensions and paths that can turn small lifecycle bugs into serious incidents.
That can frustrate centralized security teams because one CVE becomes many answers. One vendor may mark a branch affected and ship a fix. Another may mark a configuration not affected because the feature is disabled or the vulnerable patch was never backported. Another may need more time to publish packages. Appliances may hide the kernel entirely and expose only a firmware version.
This is why a good vulnerability program records evidence of fix, not just evidence of concern. A closed ticket should say which advisory applied, which package or image version fixed it, whether the host rebooted or live patching covered it, and how the running state was verified. Anything less becomes archaeology during the next audit.
The broader lesson is that Linux kernel CVEs should be treated as supply-chain events. The vulnerable code may be upstream, but the actionable answer lives downstream.
A mature response starts with classification. This is a Linux kernel kTLS use-after-free, not a Windows TLS flaw. It carries a critical vendor score. It has upstream stable patches. It affects multiple kernel branches. It requires distribution-specific confirmation. It likely requires a reboot unless live patching is available and explicitly covers the issue.
The next step is prioritization. Systems terminating or processing TLS at high volume should move first, especially if they are internet-facing or multi-tenant. Cloud nodes and Kubernetes workers should be evaluated through image and node-pool lifecycle, not just in-place patching. Appliances should be escalated to vendors quickly, because customers may not have the ability to inspect or patch the kernel themselves.
Finally, the program should close the loop. Do not stop at “patched.” Confirm the running kernel. Confirm the scanner result against vendor advisories. Confirm that old vulnerable kernels are not still selectable in the bootloader. Confirm that autoscaling groups and golden images will not quietly launch vulnerable replacements next week.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
tls_do_encryption() cleanup logic after an -EBUSY crypto backlog condition and now tracked by Microsoft through its Security Update Guide. The WindowsForum angle is not that Windows’ own TLS stack suddenly broke. It is that Microsoft’s estate now includes enough Linux—Azure Linux, WSL-adjacent tooling, cloud images, appliances, containers, and managed infrastructure—that a kernel CVE can land in Redmond’s vulnerability machinery and still matter to Windows shops. That is the real story: the Microsoft perimeter is no longer bounded by NT.
 Microsoft’s Linux Problem Is Now Everyone’s Patch Problem
Microsoft’s Linux Problem Is Now Everyone’s Patch Problem
For years, Windows administrators could treat Linux kernel CVEs as something that happened on the other side of the rack. That mental model has been obsolete for a while, but CVE-2026-31533 is a useful stress test because it does not arrive as a neat Windows component bug with a familiar KB number, reboot flow, and desktop-facing update banner.The vulnerability sits in the Linux kernel’s
net/tls subsystem, specifically in the path that handles kernel TLS encryption when crypto requests are backlogged. Kernel TLS, usually shortened to kTLS, is designed to move parts of TLS record handling into the kernel so high-throughput network stacks can avoid some of the overhead of bouncing data between user space and kernel space. That makes it especially relevant to servers, proxies, storage appliances, container hosts, and performance-tuned cloud workloads.The flaw is a classic low-level failure with a modern blast radius. A crypto request returns
-EBUSY, which means the operation is not done but has been queued for asynchronous handling. A callback is expected to finish the job. Under an error condition, however, the synchronous path also performs cleanup that the callback will perform later, creating a double-cleanup situation that corrupts internal state and can leave a freed TLS record exposed to a delayed callback.That is why the CVSS 3.1 score assigned by kernel.org is 9.8 critical, with the familiar worst-case network vector: network-accessible, low complexity, no privileges required, no user interaction, and high impact to confidentiality, integrity, and availability. NVD had not supplied its own final score at the time reflected in the public record, but it had already associated the weakness with CWE-416, use-after-free. For defenders, the absence of a final NVD score is not a reason to wait; the vendor CNA’s scoring already says enough.
The Bug Is Small Because Kernel Bugs Often Are
The technical fix is almost comically modest compared with the severity label. The broken path double-decrementsctx->encrypt_pending and double-restores a scatterlist entry after crypto_aead_encrypt() returns -EBUSY. The fix is to stop doing synchronous cleanup when the asynchronous callback has already taken responsibility for that state.That is not a glamorous exploit primitive on its face. It is accounting. A sentinel value initialized to one is decremented at the wrong time. A scatterlist entry’s offset and length are restored twice. A wait function that should block for pending asynchronous callbacks can be tricked into believing there is nothing left to wait for.
But kernel security has always been full of bugs that look mundane until you ask what object lifetime they invalidate. Here, the bad accounting can allow a later
sendmsg path to free a tls_rec while a cryptd callback still holds the right to touch it. When that callback finally fires, it reaches back into memory that may no longer belong to the TLS record.That is the essence of a use-after-free: not merely a crash, but a violation of the kernel’s ownership model. In benign conditions, it may panic or corrupt memory in ways that are difficult to reproduce. In hostile conditions, depending on surrounding allocation behavior, it may become a foothold for code execution or privilege escalation inside the kernel. The CVSS vector treats the theoretical remote impact as severe, and kernel operators should do the same until their distribution tells them otherwise.
The -EBUSY Path Is Where Performance Meets Risk
The presence of -EBUSY in the advisory is not incidental. This bug lives at the intersection of performance optimization and asynchronous execution, where the kernel tries not to make fast networking wait for crypto work that can be queued and completed later. That is exactly the kind of machinery that makes modern servers fast, and exactly the kind that punishes sloppy lifetime management.Backlogging crypto requests is a reasonable design. If the crypto layer cannot process an AEAD encryption request immediately, queuing it through cryptd is preferable to stalling everything or failing prematurely. But asynchronous design creates a contract: once work is queued, ownership and cleanup must be unambiguous.
CVE-2026-31533 breaks that contract. The callback path believes it owns cleanup, while the synchronous error path also decides to clean up after an async wait returns an error. Each path is defensible in isolation. Together, they violate the reference counting logic that tells the rest of the TLS code whether outstanding encryption work still exists.
This is why kernel bugs often evade casual review. The dangerous line is not always a reckless pointer dereference. It is the second “safe” cleanup call that only becomes unsafe when an uncommon return code, a queued callback, and a later send path line up in the right order. In production, those edge conditions tend to appear first under load, which is precisely where kTLS is most likely to be deployed.
This Is Not SChannel, But Windows Shops Should Still Care
The first clarification for WindowsForum readers is simple: CVE-2026-31533 is not a Windows SChannel vulnerability. It is not a flaw in Windows’ native TLS implementation, not a browser TLS bug, and not a sign that every Windows endpoint accepting HTTPS connections is exposed through this code path.The second clarification is more uncomfortable: Microsoft publishing or tracking a Linux kernel CVE is no longer unusual. Microsoft operates and ships Linux in meaningful ways. Azure hosts Linux at vast scale. Azure Linux is Microsoft’s own Linux distribution for cloud and infrastructure scenarios. WSL uses a Linux kernel component in its architecture. Security tooling, container hosts, AKS nodes, IoT deployments, and third-party appliances running in Microsoft-centered environments may all pull Windows administrators into Linux kernel patch triage.
That creates a taxonomy problem. A vulnerability can be “in Microsoft’s security guide” without being “in Windows.” It can affect assets managed by a Microsoft customer without affecting Windows Server itself. It can appear in enterprise scanners as a Microsoft-adjacent finding even though the actual remediation is a Linux kernel update from a distro channel, cloud image refresh, node replacement, or appliance vendor patch.
This is where many patch programs still stumble. They are organized around product families, not execution contexts. CVE-2026-31533 asks a more practical question: where in your estate is a vulnerable Linux kernel running with kTLS-capable networking paths, and who owns the reboot?
The Version Ranges Tell a Messier Story Than the Score
The public NVD change history lists several affected Linux kernel ranges, including stable lines beginning at 5.15.160, 6.1.84, 6.6.18, 6.7.6, 6.8.1, 6.13, and 6.19, with fixed endpoints identified across those branches. It also lists 7.0 release candidates. The exact impact for a given organization depends less on the headline CVE and more on the kernel build that actually shipped with the distribution or platform in use.That distinction matters because enterprise Linux does not map cleanly to upstream kernel version numbers. Vendors routinely backport fixes without changing to a brand-new upstream kernel release. A server reporting a 5.15-derived kernel is not automatically vulnerable or safe based solely on the visible major and minor version. The package release, distro advisory, and vendor changelog matter.
The same is true in cloud environments. Golden images, marketplace appliances, Kubernetes node pools, and container-optimized hosts can lag behind upstream fixes even when the cloud provider has already published patched images. A fixed kernel sitting in a repository does not protect a running VM until the package is installed and the machine is booted into that kernel, unless a live-patching mechanism specifically covers the flaw.
For Windows-heavy administrators, this is one of the less forgiving parts of Linux patch management. Installing the package is only half the story. The running kernel is the security boundary. If
uname -r, the package manager, and the bootloader do not agree on what is active, the vulnerability scanner may continue to flag the host—and it may be right.Exploitability Is the Question, Not the Excuse
A critical CVSS score does not prove that reliable remote exploitation exists in the wild. It says the conditions described by the scoring model are severe. With kernel memory corruption, that distinction matters, but it should not become a lullaby.The vulnerability description implies a chain involving kernel TLS encryption, crypto request backlogging, the async cryptd callback, error handling in
tls_encrypt_async_wait(), a subsequent sendmsg, and bpf_exec_tx_verdict() freeing the TLS record while the callback is still pending. That is not the same as “any packet instantly owns the box.” It suggests an attacker must drive a fairly specific code path.But “specific” is not “impractical.” Kernel networking paths are reachable by design. TLS-enabled services are reachable by design. High-throughput workloads may be more likely to trigger backlog behavior. If BPF verdict programs are involved in the vulnerable path, the configuration and deployment model become part of the exploitability picture.
Defenders should resist two bad instincts. The first is panic: ripping out services before understanding exposure can cause more harm than the vulnerability. The second is complacency: dismissing a kernel use-after-free because the internal description sounds complicated has aged badly too many times. The right response is boring and disciplined—inventory, patch, reboot, verify.
The Microsoft Angle Is About Supply Chains, Not Brand Names
The MSRC listing is a reminder that vulnerability ownership has become entangled with supply chains. Microsoft may not have authored the vulnerable code path. Windows may not execute it. Yet Microsoft customers may still encounter the CVE through Microsoft channels because the affected software can appear in Microsoft-supported or Microsoft-hosted environments.That matters for risk communication. A CISO reading a Microsoft Security Update Guide entry may assume there is a Windows patch. A Windows admin may search WSUS or Intune and find nothing relevant. A Linux engineer may already have the fix queued through the distro’s kernel stream. Meanwhile, the vulnerability management platform keeps the ticket open because it sees
linux_kernel CPEs and a critical score.The answer is not to force every vulnerability into a Windows-shaped process. The answer is to make the process understand mixed estates. If the affected asset is an Azure Linux node, handle it through the Azure Linux update mechanism. If it is Ubuntu on Azure, follow Canonical’s advisory and package stream. If it is SUSE, Red Hat, Debian, Amazon Linux, or an appliance image, follow that vendor. If it is WSL, watch Microsoft’s WSL servicing path rather than assuming a general-purpose Linux distro kernel package applies.
This is the operational future Microsoft helped create by embracing Linux in the cloud. It is a better future than the old religious war, but it is not simpler. The administrator’s map now has to include kernels that do not come from Redmond but still run inside Redmond’s orbit.
kTLS Is a Performance Feature With Security Consequences
Kernel TLS exists because copying encrypted traffic through user space has a cost. For workloads serving large volumes of TLS traffic, offloading record handling to the kernel can reduce overhead and make better use of NIC and crypto capabilities. That is a legitimate optimization, not an exotic stunt.The security tradeoff is that the kernel becomes responsible for more protocol-adjacent state. Bugs that might once have lived in a user-space TLS library can now appear in kernel paths that touch socket buffers, scatterlists, crypto APIs, BPF verdicts, and asynchronous callbacks. The blast radius changes because a process-level crash becomes kernel memory corruption.
This does not mean kTLS is a bad idea. It means kTLS should be treated like any other acceleration feature that moves complexity downward in the stack. When performance-critical code enters the kernel, patch latency matters more. So does configuration awareness. So does knowing whether a given service or distribution actually enables and uses the feature.
Many organizations will discover during this CVE that they do not know where kTLS is active. They know where Nginx runs, where Envoy runs, where storage appliances live, and where Kubernetes nodes terminate traffic. They may not know which of those paths use kernel TLS, which kernels have the vulnerable commits, and which hosts are merely carrying code that is not reachable in their configuration. That uncertainty is exactly why critical kernel CVEs tend to become broad patch events.
The Patch Is Simple; The Reboot Is Political
The upstream fix skips the synchronous cleanup when the-EBUSY async wait returns an error, because the callback has already handled the pending encryption count and scatterlist restoration. In source terms, that is targeted surgery. In enterprise terms, it is a kernel update, and kernel updates mean reboots, live patch exceptions, maintenance windows, and service-owner negotiations.This is where severity ratings collide with calendars. A critical remotely reachable kernel flaw should normally move near the top of the queue. But many affected systems will be production Linux servers running under Windows-centric change management programs that are optimized for Patch Tuesday, not rolling kernel advisories.
The right comparison is not “does this feel worse than a Windows RCE?” The right comparison is “which internet-facing or high-risk Linux kernels in our estate are in the affected range, and how quickly can we get them onto a fixed build?” Some systems will be straightforward. Others—appliances, custom images, pinned Kubernetes nodes, legacy cloud VMs—will reveal debt.
There is also a verification trap. After patching, defenders should confirm the running kernel, not merely the installed package. In Linux incidents, it is common to find machines that installed a fixed kernel days earlier but never rebooted into it. That distinction is invisible to teams that treat package compliance as equivalent to runtime compliance.
The Scanner Finding Needs Human Translation
Vulnerability scanners are likely to produce noisy results around CVE-2026-31533 because kernel CPE matching is blunt. NVD’s affected configuration ranges are useful, but scanners often struggle with backported fixes, vendor-specific kernel naming, and cloud image variants. A host can look vulnerable by upstream version while carrying a vendor backport that fixes the bug.The opposite mistake is also possible. A platform can appear safe because its version string looks unfamiliar, while the underlying kernel contains the affected code. That is why vendor advisories remain the authoritative remediation guide. The CPE is a starting point, not a court verdict.
Security teams should triage by exposure and ownership. Internet-facing TLS services, load balancers, reverse proxies, service mesh gateways, storage endpoints, and nodes running heavy encrypted traffic deserve early attention. Internal systems still matter, especially where untrusted tenants, containers, or lateral movement paths can reach the vulnerable networking surface. But the patch order should reflect real attack paths, not just a spreadsheet sorted by CVSS.
For Windows administrators pulled into the ticket, the useful move is not to debate whether “Linux belongs to another team.” It is to identify the asset owner, the distribution, the kernel package source, and the reboot plan. The CVE does not care which team’s name is on the CMDB entry.
The BPF Detail Should Get Defenders’ Attention
One phrase in the vulnerability description deserves more attention than it will probably get:bpf_exec_tx_verdict(). BPF has become a powerful part of Linux networking and observability, used by security tools, service meshes, load balancers, and custom packet-processing logic. Its presence in the described use-after-free path does not mean BPF is the vulnerable component, but it does place the bug in a modern, programmable networking context.That matters because many newer Linux deployments are not simple socket servers anymore. They are layered with eBPF policy engines, CNI plugins, traffic redirectors, tracing agents, and sidecar-heavy architectures. The kernel networking path is no longer just the kernel and the application; it is a crowded control plane.
This makes exposure analysis harder. A traditional server inventory might tell you what applications listen on which ports. It may not tell you which BPF programs are attached, which verdict paths can free records, or whether traffic handling differs between ordinary flows and accelerated TLS flows. In other words, the exploitability question may live below the level of tools many Windows-first shops routinely use.
That is not an argument for disabling BPF or kTLS on sight. It is an argument for understanding that modern Linux infrastructure has its own equivalent of Windows driver risk: privileged, high-performance kernel extensions and paths that can turn small lifecycle bugs into serious incidents.
Distros Will Decide the Practical Blast Radius
Upstream kernel fixes are the beginning of remediation, not the end. The practical blast radius will be determined by distribution advisories, cloud provider images, appliance vendors, container host maintainers, and live patch providers. SUSE, Ubuntu, Amazon Linux, Red Hat-family distributions, Debian-family distributions, and Microsoft’s own Linux-related channels may each communicate exposure differently.That can frustrate centralized security teams because one CVE becomes many answers. One vendor may mark a branch affected and ship a fix. Another may mark a configuration not affected because the feature is disabled or the vulnerable patch was never backported. Another may need more time to publish packages. Appliances may hide the kernel entirely and expose only a firmware version.
This is why a good vulnerability program records evidence of fix, not just evidence of concern. A closed ticket should say which advisory applied, which package or image version fixed it, whether the host rebooted or live patching covered it, and how the running state was verified. Anything less becomes archaeology during the next audit.
The broader lesson is that Linux kernel CVEs should be treated as supply-chain events. The vulnerable code may be upstream, but the actionable answer lives downstream.
The Patch Window Is a Test of Mixed-OS Maturity
CVE-2026-31533 is not remarkable because Linux had a kernel memory bug. Linux has a vast kernel, fast-moving subsystems, and an enormous deployment base; serious bugs will happen. It is remarkable because it exposes how many Microsoft-centered environments now depend on Linux patch discipline.A mature response starts with classification. This is a Linux kernel kTLS use-after-free, not a Windows TLS flaw. It carries a critical vendor score. It has upstream stable patches. It affects multiple kernel branches. It requires distribution-specific confirmation. It likely requires a reboot unless live patching is available and explicitly covers the issue.
The next step is prioritization. Systems terminating or processing TLS at high volume should move first, especially if they are internet-facing or multi-tenant. Cloud nodes and Kubernetes workers should be evaluated through image and node-pool lifecycle, not just in-place patching. Appliances should be escalated to vendors quickly, because customers may not have the ability to inspect or patch the kernel themselves.
Finally, the program should close the loop. Do not stop at “patched.” Confirm the running kernel. Confirm the scanner result against vendor advisories. Confirm that old vulnerable kernels are not still selectable in the bootloader. Confirm that autoscaling groups and golden images will not quietly launch vulnerable replacements next week.
The Admin’s Short List for This Specific CVE
The practical answer is not exotic, but it does require crossing the Windows/Linux boundary without losing the thread. Treat this as a kernel lifecycle issue first and a Microsoft-branded advisory second.- Determine whether any Linux systems in your estate run kernels in the affected ranges or vendor builds derived from them.
- Prioritize internet-facing TLS infrastructure, high-throughput encrypted services, Kubernetes nodes, cloud images, and appliances that may use kernel TLS.
- Follow the advisory from the actual kernel supplier, because enterprise distributions may backport the fix without changing to an obviously newer upstream kernel.
- Install the fixed kernel or platform image, then verify the machine is running the fixed kernel after reboot or confirmed live patch application.
- Do not treat the MSRC listing as proof that Windows SChannel is affected, and do not treat the lack of a Windows KB as proof that your Microsoft-hosted Linux assets are safe.
- Record the package, image, advisory, reboot status, and runtime kernel evidence so the finding does not reappear as an unresolved scanner ghost.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center