CVE-2026-31552 is a reminder that kernel security failures do not always arrive as dramatic memory corruption bugs or remote code execution chains. This Linux Wi-Fi driver flaw turns on a deceptively small change: returning -EAGAIN instead of -ENOMEM when the wlcore driver cannot expand packet headroom. That mismatch can trap the transmit path in an infinite retry loop, leading to a CPU soft lockup and a high-severity availability impact. For WindowsForum readers, the key takeaway is not panic over Wi-Fi in Windows, but a sharper understanding of how Linux kernel vulnerabilities surface through Microsoft’s ecosystem, embedded devices, WSL-adjacent environments, Azure workloads, and enterprise vulnerability management.
CVE-2026-31552 affects the Linux kernel wlcore Wi-Fi driver, a driver family associated with Texas Instruments wireless chipsets such as wl1271-class devices. The issue was published in late April 2026 and is tracked by kernel.org as the source CNA, with Microsoft also listing the vulnerability in its Security Update Guide. The reported CVSS 3.1 score from kernel.org is 7.5 High, with the impact limited to availability rather than confidentiality or integrity.
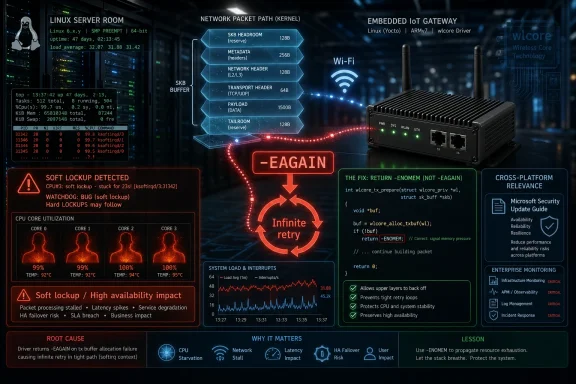
The flaw sits in the transmit path, where packet buffers are prepared before being handed to wireless hardware. A prior hardening change attempted to ensure sufficient socket-buffer headroom before calling
That distinction matters because kernel networking code often gives return values very specific operational meanings. In this case, -EAGAIN was interpreted by
The result is a tight loop under
The affected path begins when
That misclassification changes the control flow. The transmit worker flushes the aggregation buffer, places the same socket buffer back at the head of the queue, and tries again immediately. Because the same packet still lacks the required headroom, the same failure repeats.
Several implementation details make the problem more severe:
The earlier upstream hardening change was intended to prevent unsafe use of
CVE-2026-31552 shows how one bug fix can expose another bug in the surrounding assumptions. The system moved from a potentially unsafe buffer operation to a potentially non-terminating retry loop. That is progress in one dimension, but a regression in another.
Soft lockups occur when a CPU spends too long in kernel mode without scheduling normally. The operating system may detect that a CPU is stuck, log warnings, and potentially recover only partially. On production systems, that may present as frozen networking, elevated load, stalled device activity, or an eventual watchdog-triggered reset.
The high CVSS availability rating reflects that denial-of-service angle. The published vector indicates network attack surface, low attack complexity, no privileges, and no user interaction, but no confidentiality or integrity impact. In plain language, the threat model is less about stealing data and more about making a system stop behaving reliably.
The risk depends heavily on whether the vulnerable driver is present, loaded, and reachable in the target environment. A cloud VM without wlcore hardware is unlikely to care. An embedded Linux device using TI WiLink hardware in a remote site deserves much closer scrutiny.
Important differentiators include:
Those details matter because kernel versioning is often misunderstood. A system running an older major kernel is not automatically vulnerable unless it falls within the affected range and contains the relevant backport. Conversely, a newer-looking branch may be exposed if it incorporated the problematic change before the corrective patch arrived.
The fix has been published across several stable kernel commits, which suggests the issue was propagated through backports. This is common in kernel maintenance: a fix or hardening change lands upstream, then stable maintainers carry it into supported branches. When that change interacts badly with branch-specific code, the regression may appear in multiple supported series.
Administrators should focus on three checks:
For CVE-2026-31552, asset context is essential. A Debian, Ubuntu, Red Hat, SUSE, Yocto, Android-derived, or embedded vendor kernel can all package the same upstream concept differently. The kernel version string alone is evidence, not a verdict.
Security teams should treat CPE results as a starting point. The next step is to check vendor advisories, installed changelogs, and actual module usage. A high-quality triage process combines vulnerability intelligence with runtime facts.
For typical Windows desktop users, the practical risk is low unless they operate Linux systems, Linux-based appliances, WSL environments with custom kernels, or cloud workloads using affected Linux images. The vulnerability is not about Intel, Qualcomm, Realtek, or Broadcom drivers in Windows. It is specifically about Linux wlcore behavior.
That distinction is important for WindowsForum readers because Microsoft’s security portal increasingly functions as a cross-platform risk dashboard. Microsoft is no longer only a Windows vendor in the security sense. It ships, hosts, scans, and supports Linux in many enterprise contexts.
Windows users should interpret the listing this way:
However, advanced users sometimes compile custom WSL kernels, run Linux VMs with device passthrough, or test embedded images under virtualization. In those scenarios, the question becomes more technical: is the affected code compiled, can it be reached, and does the runtime environment include the relevant hardware or emulation? For most people, the answer will be no, but specialized labs should still verify.
The broader lesson is that Windows-adjacent Linux risk is no longer hypothetical. Developers build firmware on Windows laptops, run Linux build containers, deploy to Azure, and test IoT images through mixed environments. A Linux kernel CVE can therefore land on a Windows administrator’s desk even when Windows itself is not vulnerable.
A data center fleet made up of virtual machines probably has little practical exposure. A manufacturer with field-deployed Linux gateways using SDIO-connected wireless modules may have much more. The same CVE can be noise for one organization and urgent for another.
Azure customers should distinguish between Microsoft-hosted Linux services, their own Linux VMs, marketplace images, and container base images. A kernel driver flaw usually matters most where customers control the kernel or run hardware-facing Linux. Containers share the host kernel, so container images themselves are not usually the place where a Wi-Fi driver fix is applied.
Potentially relevant environments include:
Enterprise exposure is more fragmented. Large organizations often forget about non-server Linux assets: kiosks, scanners, badge systems, conference-room controllers, point-of-sale terminals, lab equipment, and manufacturing devices. Those systems may be hard to inventory and slow to patch.
The risk is not merely whether an attacker can crash one device. The operational question is whether enough devices can be disrupted to affect service delivery. If a fleet of Wi-Fi-connected embedded systems can be driven into soft lockups, availability becomes a business issue.
Because vendor kernels are often patched without obvious upstream version changes, do not rely solely on
A practical triage sequence looks like this:
Look for signs involving soft lockup, wlcore transmit paths, workqueue activity, or repeated Wi-Fi recovery attempts. On embedded systems, serial console logs can be invaluable because remote logging may stop when networking fails. If devices reboot unexpectedly, correlate watchdog resets with wireless traffic conditions.
Monitoring should not be limited to security tooling. Operations dashboards that track CPU saturation, link flaps, packet drops, and device heartbeat failures may detect the issue faster than a vulnerability scanner. Availability bugs often announce themselves as reliability problems before they look like security incidents.
For mainstream distributions, administrators should wait for vendor-packaged kernels unless they have a strong reason to self-patch. Distribution kernels carry additional testing, ABI considerations, module signing rules, and platform-specific patches. Manually cherry-picking kernel commits can solve one problem while introducing another.
Embedded vendors face a harder task. They may have to backport the fix into long-lived product kernels, rebuild images, validate wireless behavior, and distribute updates through controlled channels. Where immediate patching is not possible, mitigation may involve disabling unused wlcore modules or reducing exposure to untrusted Wi-Fi conditions.
Recommended remediation actions include:
Live patching may not cover this issue, depending on vendor support and the exact driver code involved. Many live-patching services focus on high-impact core kernel vulnerabilities rather than every network driver fix. Administrators should confirm coverage rather than assume it.
For embedded systems, reboot planning may be tied to maintenance windows, battery state, physical access, or safety constraints. That makes prioritization critical. A low-exposure lab board can wait; a remote industrial gateway with wlcore Wi-Fi may not.
Traditional static analysis is good at certain memory errors, null dereferences, and lock-order patterns. Large language model-based review may add value when the problem depends on intent: what does -EAGAIN mean to this caller, and is that meaning still true after a backport? That is a more contextual question.
Still, the Linux kernel is not a safe playground for unverified AI suggestions. Maintainers must validate the reasoning, test the patch, and ensure the fix does not break legitimate retry behavior. AI can widen the reviewer’s peripheral vision, but it cannot own responsibility for kernel correctness.
Practical lessons from the AI-review angle include:
CVE-2026-31552 appears tied to the aftermath of a previous hardening change that ensured skb headroom before
This is not an indictment of stable kernels. It is an argument for better review tooling, stronger regression tests, and careful attention to branch-specific control flow. The kernel ecosystem moves fast because it has to; the challenge is making that speed safer.
For Windows administrators, this changes the job description. Patch Tuesday remains important, but it is no longer the whole patch story. Many organizations now run hybrid estates where Windows, Linux, firmware, hypervisors, containers, and SaaS dependencies all feed into the same risk queue.
Competitively, vendors that explain cross-platform exposure clearly will win trust. Customers do not want inflated alerts, but they also do not want blind spots. The best security portals will distinguish native exposure, hosted exposure, container exposure, and informational tracking.
The wlcore case is especially relevant for older hardware. Wi-Fi chipsets can remain in products long after they vanish from mainstream laptops. Industrial buyers may expect devices to run for ten years, while software maintenance assumptions may be much shorter.
The market implication is clear: long-term device support is a security feature. Vendors that cannot deliver kernel fixes to field devices should be judged accordingly. Enterprises should ask about kernel maintenance before buying embedded platforms, not after the first CVE wave arrives.
Key ecosystem pressures include:
Watch for whether vendors classify the flaw as applicable, not affected, or already fixed through previous backports. Some Linux distributions may carry the vulnerable change only in limited kernel builds. Others may publish fixed packages while retaining the same major kernel version string.
Security and operations teams should track:
Those questions are more important than this single CVE. The future of enterprise security is full of cross-platform ambiguity, and ambiguity is expensive. Teams that combine inventory, vendor intelligence, runtime telemetry, and disciplined reboot practices will move faster with less noise.
For WindowsForum readers, the practical message is clear: this is not a Windows Wi-Fi fire drill, but it is a Microsoft-era security story. As Windows, Linux, cloud, containers, and embedded systems continue to overlap, administrators need to read vulnerability records through the lens of actual exposure rather than brand labels. CVE-2026-31552 is a small kernel patch with a large operational lesson: in systems software, even one wrong return code can turn a recoverable failure into a denial-of-service condition, and the organizations best prepared to respond are the ones that already know exactly where their kernels, drivers, and devices are running.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 Overview
Overview
CVE-2026-31552 affects the Linux kernel wlcore Wi-Fi driver, a driver family associated with Texas Instruments wireless chipsets such as wl1271-class devices. The issue was published in late April 2026 and is tracked by kernel.org as the source CNA, with Microsoft also listing the vulnerability in its Security Update Guide. The reported CVSS 3.1 score from kernel.org is 7.5 High, with the impact limited to availability rather than confidentiality or integrity.The flaw sits in the transmit path, where packet buffers are prepared before being handed to wireless hardware. A prior hardening change attempted to ensure sufficient socket-buffer headroom before calling
skb_push, a routine used to prepend data to a network packet buffer. That earlier protection was sensible, but its failure path introduced a new semantic problem: a memory allocation failure could be reported as a retryable condition.That distinction matters because kernel networking code often gives return values very specific operational meanings. In this case, -EAGAIN was interpreted by
wlcore_tx_work_locked() as a sign that an aggregation buffer was full, prompting the driver to flush, requeue the same packet, and immediately retry. If the underlying condition was actually insufficient memory headroom, the retry would not make progress.The result is a tight loop under
wl->mutex, using GFP_ATOMIC allocation rules and repeatedly attempting the same operation. In practical terms, the system can burn CPU without escaping the loop, triggering a soft lockup and degrading or denying service. The fix is direct: return -ENOMEM so the packet can be dropped and the loop can terminate.How the wlcore Bug Works
The error-code mismatch
At the center of CVE-2026-31552 is a classic systems programming problem: an error code was technically valid in one context but operationally wrong in another. -EAGAIN usually communicates “try again,” while -ENOMEM tells the caller that memory allocation failed. Those meanings are not interchangeable inside low-level driver loops.The affected path begins when
wl1271_prepare_tx_frame() calls into allocation logic through wl1271_tx_allocate(). If pskb_expand_head() fails while trying to ensure enough headroom, the failure needs to tell the caller that memory is the blocker. Instead, returning -EAGAIN caused the upper transmit worker to treat the situation like a full aggregation buffer.That misclassification changes the control flow. The transmit worker flushes the aggregation buffer, places the same socket buffer back at the head of the queue, and tries again immediately. Because the same packet still lacks the required headroom, the same failure repeats.
Several implementation details make the problem more severe:
- The same skb is retried, rather than discarded or deferred safely.
- The loop happens immediately, leaving little room for external recovery.
- The mutex remains held, increasing the risk of blocking related driver work.
- GFP_ATOMIC allocation limits the ability to wait for memory reclaim.
- The exit condition becomes unreachable, matching the CWE-835 classification.
Why headroom matters
In Linux networking, a socket buffer, or skb, carries packet data along with reserved space at the beginning and end of the buffer. That reserved front space is called headroom, and drivers often need it to prepend protocol headers, hardware descriptors, or firmware-specific metadata. If headroom is insufficient, the kernel may attempt to expand or copy the buffer.The earlier upstream hardening change was intended to prevent unsafe use of
skb_push when headroom was inadequate. That is the right instinct: pushing data before the start of an skb can corrupt memory or trigger a defensive kernel panic. But defensive fixes must preserve the semantics expected by every caller.CVE-2026-31552 shows how one bug fix can expose another bug in the surrounding assumptions. The system moved from a potentially unsafe buffer operation to a potentially non-terminating retry loop. That is progress in one dimension, but a regression in another.
Why a Small Return Code Became a High-Severity CVE
Infinite loops in kernel context
A user-space infinite loop can often be killed by the scheduler, a service manager, or an administrator. A kernel-space infinite loop is more dangerous because it can occupy privileged execution paths, hold locks, and prevent the system from making forward progress. CVE-2026-31552 earns attention because it can cause a CPU soft lockup, not merely a failed packet transmission.Soft lockups occur when a CPU spends too long in kernel mode without scheduling normally. The operating system may detect that a CPU is stuck, log warnings, and potentially recover only partially. On production systems, that may present as frozen networking, elevated load, stalled device activity, or an eventual watchdog-triggered reset.
The high CVSS availability rating reflects that denial-of-service angle. The published vector indicates network attack surface, low attack complexity, no privileges, and no user interaction, but no confidentiality or integrity impact. In plain language, the threat model is less about stealing data and more about making a system stop behaving reliably.
Availability is still security
Enterprise defenders sometimes rank denial-of-service below data theft, but the distinction is not always comforting. An availability failure in a gateway, industrial controller, embedded access device, or field-deployed Linux appliance can disrupt operations just as effectively as a more glamorous exploit. If Wi-Fi connectivity is part of the control plane, a driver lockup can become an operational incident.The risk depends heavily on whether the vulnerable driver is present, loaded, and reachable in the target environment. A cloud VM without wlcore hardware is unlikely to care. An embedded Linux device using TI WiLink hardware in a remote site deserves much closer scrutiny.
Important differentiators include:
- Whether CONFIG_WLCORE is enabled in the kernel build.
- Whether wlcore_sdio or wlcore_spi is loaded on the system.
- Whether TI wl12xx or wl18xx-class hardware is present.
- Whether untrusted Wi-Fi traffic can influence the transmit path.
- Whether watchdogs or HA failover can recover from a soft lockup.
Affected Kernels and Patch Status
Version ranges to prioritize
NVD’s initial enrichment lists multiple vulnerable Linux kernel ranges, including several stable and long-term lines. The affected configurations include Linux 7.0 release candidates, Linux 6.19, and selected version ranges across 5.10, 5.15, 6.1, 6.6, 6.12, 6.18, and 6.19 maintenance branches. The fixed versions identified in the public data include later point releases such as 5.10.253, 5.15.203, 6.1.167, 6.6.130, 6.12.78, 6.18.20, and 6.19.10 for the listed affected ranges.Those details matter because kernel versioning is often misunderstood. A system running an older major kernel is not automatically vulnerable unless it falls within the affected range and contains the relevant backport. Conversely, a newer-looking branch may be exposed if it incorporated the problematic change before the corrective patch arrived.
The fix has been published across several stable kernel commits, which suggests the issue was propagated through backports. This is common in kernel maintenance: a fix or hardening change lands upstream, then stable maintainers carry it into supported branches. When that change interacts badly with branch-specific code, the regression may appear in multiple supported series.
Administrators should focus on three checks:
- Kernel branch and exact point release, not just major version.
- Distribution backport status, because vendors may patch without changing the visible upstream version.
- Driver enablement, because an affected version may not expose the vulnerable code path if wlcore is absent.
Why CPE data is useful but incomplete
CPE entries help scanners map software inventory to vulnerability records, but they are blunt instruments for kernel flaws. Linux distributions frequently maintain custom kernels with vendor patches, backports, and configuration differences. That means a scanner may flag a system that is not practically exposed, or miss a downstream package where the fix has not yet landed.For CVE-2026-31552, asset context is essential. A Debian, Ubuntu, Red Hat, SUSE, Yocto, Android-derived, or embedded vendor kernel can all package the same upstream concept differently. The kernel version string alone is evidence, not a verdict.
Security teams should treat CPE results as a starting point. The next step is to check vendor advisories, installed changelogs, and actual module usage. A high-quality triage process combines vulnerability intelligence with runtime facts.
What Windows Users Should Actually Take From This
MSRC listing does not mean Windows Wi-Fi is vulnerable
Because the CVE appears in Microsoft’s Security Update Guide, Windows users may wonder whether their Windows 10 or Windows 11 Wi-Fi stack is exposed. The answer is almost certainly more nuanced: CVE-2026-31552 is a Linux kernel vulnerability, not a native Windows WLAN driver flaw. Microsoft tracks many non-Windows vulnerabilities because its ecosystem includes Linux-based products, Azure services, container images, developer tooling, and supply-chain dependencies.For typical Windows desktop users, the practical risk is low unless they operate Linux systems, Linux-based appliances, WSL environments with custom kernels, or cloud workloads using affected Linux images. The vulnerability is not about Intel, Qualcomm, Realtek, or Broadcom drivers in Windows. It is specifically about Linux wlcore behavior.
That distinction is important for WindowsForum readers because Microsoft’s security portal increasingly functions as a cross-platform risk dashboard. Microsoft is no longer only a Windows vendor in the security sense. It ships, hosts, scans, and supports Linux in many enterprise contexts.
Windows users should interpret the listing this way:
- Native Windows clients are not the primary target of this CVE.
- WSL users should check custom kernel usage, especially if they build or test kernels manually.
- Azure Linux and container users should follow their image vendor’s updates.
- Developers working on embedded Linux should validate wlcore exposure.
- Security teams should avoid blanket assumptions based only on MSRC presence.
The WSL and virtualization angle
The Windows Subsystem for Linux typically does not expose arbitrary physical Wi-Fi driver stacks inside a Linux guest in the way a bare-metal Linux installation does. WSL networking is abstracted through Windows-managed components, and mainstream WSL users are unlikely to load a TI wlcore wireless driver. That makes widespread consumer WSL exposure improbable.However, advanced users sometimes compile custom WSL kernels, run Linux VMs with device passthrough, or test embedded images under virtualization. In those scenarios, the question becomes more technical: is the affected code compiled, can it be reached, and does the runtime environment include the relevant hardware or emulation? For most people, the answer will be no, but specialized labs should still verify.
The broader lesson is that Windows-adjacent Linux risk is no longer hypothetical. Developers build firmware on Windows laptops, run Linux build containers, deploy to Azure, and test IoT images through mixed environments. A Linux kernel CVE can therefore land on a Windows administrator’s desk even when Windows itself is not vulnerable.
Enterprise Linux, Azure, and Embedded Fleet Impact
Where wlcore is most likely to appear
The wlcore driver family is most relevant in embedded and specialized Linux systems, not ordinary enterprise servers. TI WiLink-era chipsets have appeared in development boards, industrial devices, handheld equipment, legacy tablets, and custom hardware platforms. That makes CVE-2026-31552 a classic asset-discovery problem.A data center fleet made up of virtual machines probably has little practical exposure. A manufacturer with field-deployed Linux gateways using SDIO-connected wireless modules may have much more. The same CVE can be noise for one organization and urgent for another.
Azure customers should distinguish between Microsoft-hosted Linux services, their own Linux VMs, marketplace images, and container base images. A kernel driver flaw usually matters most where customers control the kernel or run hardware-facing Linux. Containers share the host kernel, so container images themselves are not usually the place where a Wi-Fi driver fix is applied.
Potentially relevant environments include:
- Embedded Linux devices using TI wlcore-compatible Wi-Fi hardware.
- Industrial IoT gateways with wireless uplinks.
- Custom Yocto or Buildroot images that backport stable kernel fixes.
- Development boards based on older ARM platforms.
- Linux laptops or tablets with supported wlcore hardware.
- Hardware validation labs testing wireless driver regressions.
Consumer versus enterprise exposure
Consumer Linux users are less likely to encounter wlcore today unless they run older or niche hardware. Most modern laptops use Intel, Qualcomm, MediaTek, Broadcom, or Realtek Wi-Fi chipsets with entirely different drivers. For mainstream desktop Linux, this CVE may appear in scanners but not translate into practical exploitability.Enterprise exposure is more fragmented. Large organizations often forget about non-server Linux assets: kiosks, scanners, badge systems, conference-room controllers, point-of-sale terminals, lab equipment, and manufacturing devices. Those systems may be hard to inventory and slow to patch.
The risk is not merely whether an attacker can crash one device. The operational question is whether enough devices can be disrupted to affect service delivery. If a fleet of Wi-Fi-connected embedded systems can be driven into soft lockups, availability becomes a business issue.
Detection and Triage
Practical checks for administrators
The first step is to determine whether the affected driver exists and is active. On Linux systems, administrators can inspect kernel configuration, loaded modules, hardware identifiers, and distribution security status. The goal is to separate theoretical exposure from reachable risk.Because vendor kernels are often patched without obvious upstream version changes, do not rely solely on
uname -r. Distribution changelogs and security trackers can be more accurate than raw version comparisons. In embedded environments, the build manifest may be the only reliable record.A practical triage sequence looks like this:
- Identify the running kernel branch and package release.
- Check whether wlcore, wlcore_sdio, wlcore_spi, wl12xx, or related modules are present.
- Verify whether TI wl1271, wl1273, wl128x, wl18xx, or compatible hardware exists.
- Consult the distribution or device vendor for fixed kernel packages.
- Apply updates in a staged environment before broad deployment.
- Monitor for soft lockup warnings, watchdog events, and Wi-Fi transmit stalls.
- Document exceptions where the driver is not compiled or not reachable.
Signals in logs and monitoring
A system affected by this bug may not produce a clean exploit signature. Instead, defenders may see symptoms: high CPU usage in kernel context, watchdog warnings, wireless transmit stalls, or repeated driver activity before a hang. The most useful evidence may come from kernel logs captured before the device becomes unresponsive.Look for signs involving soft lockup, wlcore transmit paths, workqueue activity, or repeated Wi-Fi recovery attempts. On embedded systems, serial console logs can be invaluable because remote logging may stop when networking fails. If devices reboot unexpectedly, correlate watchdog resets with wireless traffic conditions.
Monitoring should not be limited to security tooling. Operations dashboards that track CPU saturation, link flaps, packet drops, and device heartbeat failures may detect the issue faster than a vulnerability scanner. Availability bugs often announce themselves as reliability problems before they look like security incidents.
Remediation and Patch Management
Safer update paths
The preferred remediation is to install a kernel version or vendor update containing the CVE-2026-31552 fix. The upstream correction changes the error handling so memory-headroom failure returns -ENOMEM, allowing the problematic packet to be dropped and the loop to end. It is small, but it lands in a sensitive path.For mainstream distributions, administrators should wait for vendor-packaged kernels unless they have a strong reason to self-patch. Distribution kernels carry additional testing, ABI considerations, module signing rules, and platform-specific patches. Manually cherry-picking kernel commits can solve one problem while introducing another.
Embedded vendors face a harder task. They may have to backport the fix into long-lived product kernels, rebuild images, validate wireless behavior, and distribute updates through controlled channels. Where immediate patching is not possible, mitigation may involve disabling unused wlcore modules or reducing exposure to untrusted Wi-Fi conditions.
Recommended remediation actions include:
- Install the vendor-provided fixed kernel as soon as it is available.
- Reboot into the fixed kernel, because kernel package installation alone is not enough.
- Disable wlcore modules where the hardware is not required.
- Prioritize remotely deployed Wi-Fi-dependent devices that are difficult to recover physically.
- Test suspend, resume, roaming, and high-throughput Wi-Fi scenarios after patching.
- Update golden images and build recipes so the flaw does not return in future deployments.
Why reboot discipline matters
Kernel patching has one unforgiving rule: the system must run the fixed kernel, not merely install it. Enterprises often accumulate servers or devices with updated packages but old running kernels. For a driver-level denial-of-service flaw, that gap can leave systems exposed for weeks.Live patching may not cover this issue, depending on vendor support and the exact driver code involved. Many live-patching services focus on high-impact core kernel vulnerabilities rather than every network driver fix. Administrators should confirm coverage rather than assume it.
For embedded systems, reboot planning may be tied to maintenance windows, battery state, physical access, or safety constraints. That makes prioritization critical. A low-exposure lab board can wait; a remote industrial gateway with wlcore Wi-Fi may not.
AI-Assisted Code Review Enters the Story
Useful signal, not a replacement
One unusual detail in the public description is that the issue was found by an experimental code review agent based on Gemini 3.1 Pro while reviewing backports into the 6.18.y stable series. That is noteworthy, not because AI “solved” kernel security, but because the bug is exactly the kind of semantic mismatch automated review may increasingly catch. The code compiled, the return value was plausible, and the failure emerged from cross-function meaning.Traditional static analysis is good at certain memory errors, null dereferences, and lock-order patterns. Large language model-based review may add value when the problem depends on intent: what does -EAGAIN mean to this caller, and is that meaning still true after a backport? That is a more contextual question.
Still, the Linux kernel is not a safe playground for unverified AI suggestions. Maintainers must validate the reasoning, test the patch, and ensure the fix does not break legitimate retry behavior. AI can widen the reviewer’s peripheral vision, but it cannot own responsibility for kernel correctness.
Practical lessons from the AI-review angle include:
- Backports need semantic review, not just conflict resolution.
- Return codes are part of an API contract, even inside one driver.
- AI tools may be useful at spotting inconsistent caller expectations.
- Human maintainers remain essential for validating fixes.
- Security teams should expect more AI-discovered CVEs in routine code paths.
The backport risk
Stable backports are necessary, but they are not mechanically risk-free. A patch designed for one kernel version may depend on surrounding code that differs in older branches. Even when the patch applies cleanly, its behavior may not be equivalent.CVE-2026-31552 appears tied to the aftermath of a previous hardening change that ensured skb headroom before
skb_push. That hardening addressed a real class of packet-buffer risk. The new CVE shows how the stable process must balance urgency, breadth, and precision.This is not an indictment of stable kernels. It is an argument for better review tooling, stronger regression tests, and careful attention to branch-specific control flow. The kernel ecosystem moves fast because it has to; the challenge is making that speed safer.
Competitive and Ecosystem Implications
Linux security in a Microsoft world
Microsoft’s tracking of CVE-2026-31552 illustrates how deeply Linux now intersects with Microsoft’s business. Azure, containers, developer tooling, security products, GitHub workflows, and cross-platform endpoint management all make Linux vulnerabilities relevant to Microsoft customers. A Security Update Guide entry for a Linux CVE is not an oddity anymore; it is normal infrastructure hygiene.For Windows administrators, this changes the job description. Patch Tuesday remains important, but it is no longer the whole patch story. Many organizations now run hybrid estates where Windows, Linux, firmware, hypervisors, containers, and SaaS dependencies all feed into the same risk queue.
Competitively, vendors that explain cross-platform exposure clearly will win trust. Customers do not want inflated alerts, but they also do not want blind spots. The best security portals will distinguish native exposure, hosted exposure, container exposure, and informational tracking.
Rival platforms and embedded accountability
Linux remains the dominant operating system for embedded and IoT devices, which means driver CVEs can have long tails. Apple, Microsoft, Google, and traditional Linux vendors all face similar problems in hardware-adjacent code, but the Linux ecosystem’s openness makes both discovery and patch diffusion more visible. That visibility is a strength when vendors respond quickly, and a liability when downstream devices are abandoned.The wlcore case is especially relevant for older hardware. Wi-Fi chipsets can remain in products long after they vanish from mainstream laptops. Industrial buyers may expect devices to run for ten years, while software maintenance assumptions may be much shorter.
The market implication is clear: long-term device support is a security feature. Vendors that cannot deliver kernel fixes to field devices should be judged accordingly. Enterprises should ask about kernel maintenance before buying embedded platforms, not after the first CVE wave arrives.
Key ecosystem pressures include:
- More CVEs from kernel.org’s cautious assignment model.
- Greater demand for SBOMs and kernel configuration transparency.
- More scrutiny of embedded Linux maintenance promises.
- Growing use of AI-assisted review in open-source security pipelines.
- Pressure on vulnerability scanners to reduce false positives with runtime context.
Strengths and Opportunities
CVE-2026-31552 is not good news, but it does highlight several healthy trends in the modern security ecosystem. The flaw was identified, assigned, described, and patched through the public kernel process, with downstream visibility through NVD and Microsoft’s security tracking. That transparency gives defenders a chance to respond before the issue becomes another mysterious reliability failure in the field.- The fix is conceptually small, making it easier to review and backport safely.
- The vulnerability has a clear failure mode, centered on availability and soft lockup risk.
- Kernel.org’s CNA process provides direct upstream context, reducing ambiguity around affected code.
- Microsoft’s tracking improves visibility for hybrid Windows-Linux environments.
- AI-assisted review showed practical value in spotting a subtle semantic regression.
- Driver-level exposure can be scoped through hardware and module inventory, limiting unnecessary panic.
- The case reinforces better return-code discipline for kernel developers and reviewers.
Risks and Concerns
The main concern is not that every Linux system is suddenly exposed, but that the systems most likely to be affected may be the hardest to patch. Embedded Wi-Fi devices, industrial gateways, and customized kernels often lag behind upstream fixes. In those environments, a high-availability flaw can persist long after mainstream distributions have moved on.- Asset owners may misread MSRC visibility as a Windows client issue, wasting triage time.
- Scanners may overreport vulnerable kernels without checking whether wlcore is present.
- Embedded vendors may underreport exposure if they do not publish timely advisories.
- Backported fixes can create regressions when branch-specific semantics differ.
- Soft lockups may be mistaken for generic hardware instability, delaying root-cause analysis.
- Remote recovery may be difficult if a Wi-Fi-dependent device hangs under load.
- Organizations may install fixed kernels but fail to reboot, leaving old code active.
What to Watch Next
Vendor advisories and downstream kernels
The next phase will be downstream vendor response. Distribution maintainers, embedded platform vendors, and cloud-image publishers will decide how quickly the upstream fix lands in supported channels. For enterprise teams, those vendor-specific advisories matter more than generic CPE matches.Watch for whether vendors classify the flaw as applicable, not affected, or already fixed through previous backports. Some Linux distributions may carry the vulnerable change only in limited kernel builds. Others may publish fixed packages while retaining the same major kernel version string.
Security and operations teams should track:
- Fixed kernel package releases from relevant Linux distributions.
- Embedded device firmware updates from hardware vendors.
- Scanner plugin revisions that refine affected-version detection.
- Reports of real-world soft lockups tied to wlcore transmit activity.
- Any follow-up fixes if related wlcore error paths show similar semantics.
The broader lesson for patch governance
CVE-2026-31552 should be used as a tabletop exercise for kernel patch governance. Can your organization identify which systems load a specific driver? Can it distinguish a Linux kernel CVE that matters to Azure workloads from one that matters to embedded devices? Can it confirm that a patched kernel is actually running after maintenance?Those questions are more important than this single CVE. The future of enterprise security is full of cross-platform ambiguity, and ambiguity is expensive. Teams that combine inventory, vendor intelligence, runtime telemetry, and disciplined reboot practices will move faster with less noise.
For WindowsForum readers, the practical message is clear: this is not a Windows Wi-Fi fire drill, but it is a Microsoft-era security story. As Windows, Linux, cloud, containers, and embedded systems continue to overlap, administrators need to read vulnerability records through the lens of actual exposure rather than brand labels. CVE-2026-31552 is a small kernel patch with a large operational lesson: in systems software, even one wrong return code can turn a recoverable failure into a denial-of-service condition, and the organizations best prepared to respond are the ones that already know exactly where their kernels, drivers, and devices are running.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center