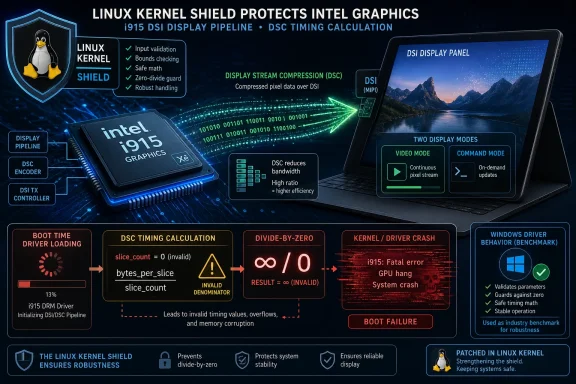
CVE-2026-31767 is a Linux kernel vulnerability published on May 1, 2026, affecting Intel’s i915 DSI display path, where a faulty Display Stream Compression timing adjustment can trigger a local divide-by-zero crash on certain systems. The bug is rated medium severity, not because it opens a glamorous remote compromise path, but because it can take down a machine at precisely the wrong layer: the graphics driver loading path. For WindowsForum readers, the interesting twist is that the Linux fix explicitly points to Windows driver behavior as the model. This is a small CVE, but it says something large about modern platform maintenance: display plumbing has become security-relevant infrastructure.
The mechanics of CVE-2026-31767 are almost comically narrow. In the Linux kernel’s
That distinction matters because command mode and video mode are not just two labels for the same screen. In DSI video mode, the host streams pixel data continuously in a way that makes horizontal and vertical timing values central to the display pipeline. In command mode, the panel is driven more transactionally; timing still exists, but the driver is not supposed to treat those values the same way.
The Linux bug took a rule that made sense in one mode and applied it in another. On some machines, that made the adjusted horizontal total so small that a later calculation produced
Security scoring systems translate that into availability impact. Humans should translate it into something plainer: on affected hardware, loading the graphics driver could crash the kernel.
That is why the CVSS 3.1 score of 5.5 feels both accurate and unsatisfying. The attack vector is local, privileges are required, user interaction is not required, and the consequence is denial of service rather than data theft or code execution. Yet the affected code sits in a path that many users never consciously touch and most administrators do not test deeply unless they manage Linux laptops, tablets, embedded devices, kiosks, or custom images.
Driver developers do not generally cite Windows behavior as a matter of admiration. They cite it because hardware vendors, firmware assumptions, and platform validation tend to orbit Windows first. If a panel, firmware table, or display controller quirk has been validated against the Windows graphics stack, matching that behavior can be the difference between a usable device and a black screen.
That does not mean Windows is automatically correct. It means Windows is often the reference environment that OEMs actually tested before shipping hardware. In the consumer PC ecosystem, especially with tablets, convertibles, and machines using tightly integrated panels, “what Windows does” can become a practical specification even when the official hardware documentation leaves room for interpretation.
CVE-2026-31767 is therefore not just a Linux bug. It is a small case study in how Windows compatibility still shapes the broader PC platform. The Linux i915 driver was doing something that made theoretical sense if one applied a compression-timing adjustment broadly. The fix narrowed that behavior to the mode where the hardware guidance and Windows implementation both suggested it belonged.
For Windows users, there is no immediate reason to panic. The submitted material identifies this as a Linux kernel vulnerability, and the affected component is the Linux i915 Direct Rendering Manager driver path, not the Windows Intel graphics driver. But the fact that the Windows driver appears in the remediation rationale tells us something about the hidden dependency chain behind every display panel: firmware, vendor documentation, OS driver behavior, and years of platform assumptions all meet at boot.
That distinction has been obsolete for years. Modern graphics drivers sit deep in the kernel, parse complex state, negotiate with firmware, touch power management, expose user-mode interfaces, and handle increasingly elaborate display protocols. Even when a given bug is “only” a denial-of-service issue, the blast radius can include boot reliability, remote management, kiosk uptime, and recovery workflows.
Display Stream Compression is a good example of this complexity. DSC exists because modern displays push enormous amounts of data: high resolutions, high refresh rates, HDR, multiple panels, and thin portable devices with bandwidth and power constraints. Compression allows hardware to move display data efficiently, but it also adds another layer of arithmetic and mode negotiation into driver code that used to be simpler.
DSI adds its own complications. It is common in mobile-style panels, tablets, convertibles, and devices that do not behave like the old desktop monitor attached by HDMI or DisplayPort. The more PC hardware borrows from phone and tablet design, the more desktop operating systems inherit mobile display assumptions.
That makes a divide-by-zero in a DSI path less surprising than it first sounds. The driver is not merely “drawing the screen.” It is interpreting panel capabilities, applying compression rules, calculating timings, and choosing behavior based on whether the panel is in video mode or command mode. One wrong assumption in that chain can turn into a kernel fault.
It tells administrators two things. First, the patch is a stability fix for a crash condition, not necessarily a complete enablement fix for every affected machine. Second, the triggering scenario is not hypothetical in the abstract; it was observed on real hardware with a real DSI panel configuration.
This matters because many CVEs in the Linux kernel are born from code auditing or rare race conditions that most users will never encounter. CVE-2026-31767 lives closer to the hardware enablement world, where an affected machine can fail during driver initialization before the user has a clean path to diagnose much of anything.
The MateBook E is also symbolically fitting. Devices like it sit at the boundary between PC and tablet, exactly where DSI panels and firmware-mediated display quirks become more likely. They are the sort of hardware Windows tends to support first and Linux support often reaches through reverse engineering, vendor crumbs, and painstaking driver work.
The patch’s honesty is important. It does not claim the device is fixed. It claims the kernel no longer crashes in that path. That is a narrower improvement, but a crucial one: a broken display is a problem; a broken display plus a kernel crash is a recovery problem.
For users testing newer kernels on niche Intel tablet hardware, that difference can decide whether the machine is merely inconvenient or effectively unusable without external workarounds.
The practical exposure is narrower. A system needs to be running an affected kernel, using the relevant Intel i915 DSI path, and hitting the problematic DSC command-mode timing scenario. A headless Linux server on Intel hardware is not suddenly endangered in the same way as a tablet-style machine with a DSI panel.
This is where vulnerability management tools can mislead by flattening context. A scanner sees a kernel version and a CPE match. It may not know whether the machine has the relevant panel, whether i915 is loaded, whether the affected code path is reachable, or whether the system is a fleet-critical kiosk sitting in a lobby.
That does not make the CVE irrelevant. It means the triage process should be evidence-based. The right first question is not “Does any Linux kernel in my environment match this CPE?” but “Do we operate devices where Intel i915 DSI display initialization matters to availability?”
For many enterprises, the answer will be no. For hardware labs, Linux desktop fleets, educational tablet programs, industrial panels, thin clients, and developers running recent kernels on convertibles, the answer may be yes.
That can irritate people who want CVEs to mean “urgent security incident.” But availability is part of security, and kernel crashes are not benign just because they lack a flashy exploit chain. If a local user with sufficient privileges can reliably trigger a system crash, that is a denial-of-service condition. If the crash can occur during routine driver loading on affected hardware, the operational stakes are even more obvious.
The bigger issue is not that this bug received a CVE. The bigger issue is that CVE feeds now mix catastrophic remotely exploitable flaws with hardware-specific crash fixes in the same river of alerts. Administrators are expected to distinguish them quickly, usually while patch windows, vendor advisories, and compliance tooling all shout at once.
The result is a triage burden that falls hardest on smaller teams. A medium Linux kernel CVE may be ignorable, urgent, or somewhere in between depending entirely on the hardware estate. Generic severity scoring cannot capture that estate-specific reality.
For WindowsForum’s audience, this is familiar from the Windows side too. A CVE affecting a Windows component may matter greatly to domain controllers and barely at all to isolated clients. A graphics-driver bug may be irrelevant to servers but painful for workstations used in design, manufacturing, or classroom environments. The label starts the conversation; it does not finish it.
But local does not always mean unimportant. In multi-user Linux environments, labs, classrooms, shared workstations, or systems where users can trigger hardware paths indirectly, local availability bugs may be more than theoretical. In managed fleets, local also includes software already running on the box, whether legitimate, compromised, or misconfigured.
That said, the exploitability story here should not be inflated. The description points to a driver load and hardware-specific timing calculation, not a universal one-command crash across all Linux desktops. A remote attacker would need a separate foothold or an indirect path to trigger the condition. Nothing in the submitted information suggests data exposure, integrity compromise, or arbitrary code execution.
The most realistic concern is operational reliability. If you deploy Linux on hardware with DSI panels and Intel graphics, you want the patched kernel because display initialization should not be capable of taking the machine down. If you run servers, virtual machines, or desktops without the relevant display path, this CVE is more likely to be a compliance item than an emergency.
That is the mature reading of a medium-severity kernel CVE: patch it, but do not pretend every kernel bug has the same operational meaning.
That matters for enthusiasts and developers more than for most enterprises. People running release candidates expect breakage, but they also form the early warning system that catches bugs before stable users inherit them. In graphics drivers, that testing is especially valuable because display hardware diversity is enormous and vendor documentation rarely covers every real-world panel quirk.
The affected stable ranges are the more important operational story. Fixes are identified in stable patch references, meaning distributions and downstream vendors can pick them up through ordinary kernel update channels. Users should not need to hand-apply an i915 patch unless they are building custom kernels or maintaining specialized images.
The cadence also shows how quickly a low-level bug can move from upstream commit to CVE record to scanner finding. The CVE was received from kernel.org on May 1, 2026, and NVD analysis updates followed on May 11, 2026. That ten-day gap is normal enough, but it is long enough for confusion: distribution trackers, vendor advisories, and scanners may not agree at the same moment.
If your tooling reports this CVE but your distribution kernel version does not appear to match the vanilla kernel version ranges, check your vendor’s backport status. Enterprise Linux distributions often patch vulnerabilities without changing the upstream-looking version number in the way newcomers expect.
The least dramatic answer is usually the right one. Microsoft’s security ecosystem tracks CVEs beyond the classic Windows client and server surface, especially where Microsoft products, cloud images, Linux workloads, or dependency inventories may be involved. A CVE appearing in an MSRC-facing location does not automatically mean Windows itself is vulnerable.
For Windows administrators, the important distinction is product applicability. The submitted description is unambiguously about the Linux kernel. The vulnerable component is not DirectX, WDDM, the Windows display driver model, or an Intel Windows driver package delivered through Windows Update. It is the Linux DRM i915 DSI implementation.
That distinction matters because CVE dashboards often travel faster than context. A security team may see “Microsoft” and “CVE” in the same workflow and assume Patch Tuesday relevance. Here, the more plausible operational link is mixed estate management: Azure Linux images, Windows Subsystem for Linux adjacent inventories, Defender vulnerability management, third-party scanners, or organizations that use Microsoft tooling to track non-Windows assets.
The irony is that Windows appears in this CVE as a behavioral reference, not as the affected platform. The Linux fix aligns the i915 logic with what the Windows driver already did for this mode distinction. In this case, Windows is less the patient and more the chart on the wall.
The hard part is realizing which assumption is wrong. If a driver applies a compression ratio to horizontal timing values, that may appear reasonable when looking at one mode or one class of panel. The bug emerges when that logic crosses a boundary where the same values no longer carry the same meaning.
This is why hardware driver bugs can be so frustrating. The code may be clean, the math may be straightforward, and the failure may still happen because the model is wrong for a specific hardware state. In CVE-2026-31767, the state is DSI command mode.
The division by zero is the visible crash. The deeper issue is an invalid transformation of display timing data. Once the horizontal total is adjusted into nonsense territory, the later calculation has little chance of producing a safe result.
That is also why the fix does not make the MateBook E display work. Removing the bad adjustment prevents a kernel crash, but it does not solve every missing piece of panel enablement. Stability fixes and hardware support fixes overlap, but they are not identical.
For mainstream distribution users, the practical answer is to install the kernel update supplied by the distribution, reboot into it, and confirm the running kernel changed. For users running custom kernels, release candidates, or hardware-enablement branches, the answer is to verify whether one of the referenced stable fixes or the underlying upstream commit is included.
For administrators, the more interesting work is inventory. Identify machines with Intel integrated graphics using the i915 driver and DSI-connected internal panels. Pay special attention to tablet-style devices, convertibles, embedded displays, and any fleet where Linux was installed onto hardware originally sold primarily for Windows.
Then examine how those machines are used. A developer’s spare test tablet is not a production incident. A check-in kiosk, classroom device, medical cart, point-of-sale terminal, or field-service tablet has a different availability profile.
This is where Windows management habits can help Linux operations. Windows admins are used to thinking in terms of hardware rings, driver validation, staged rollout, and rollback plans. Linux desktop fleets need the same discipline when the affected layer is graphics. A kernel update that fixes one display crash can still introduce another regression on a different GPU, dock, or panel.
Patch quickly where the hardware matches. Test deliberately where uptime matters. Avoid blanket panic where the component is not present.
That dual-boot context is worth spelling out because hardware bugs blur OS boundaries in users’ minds. The same panel, firmware, and GPU exist whether Windows or Linux boots. But the vulnerable code path is operating-system-specific. Windows may initialize the panel using logic that avoids this crash; Linux needed a patch to do the same.
If your machine has been booting Linux reliably, this CVE does not mean it will suddenly fail tomorrow. Vulnerabilities are not magic weather systems. But if you are testing new kernels on Intel tablet hardware, especially around the affected version ranges, the fix is worth having.
For users who hit a crash during graphics initialization, recovery may require booting an older kernel, using a fallback kernel, disabling modesetting temporarily, or updating from a rescue environment. Those are unpleasant workflows, and they are exactly why a “medium” graphics CVE can feel high-severity to the person staring at a dead screen.
The bigger lesson for enthusiasts is to keep at least one known-good kernel installed. Rolling kernels are fun until the only visible output path breaks.
CPEs describe software products and versions. CVE-2026-31767 depends heavily on hardware configuration and driver path reachability. A Linux kernel version may be vulnerable in theory while a given deployment cannot trigger the affected path. Conversely, a patched distribution kernel may carry a backported fix while still reporting a version number that looks old.
That mismatch is a recurring problem in kernel vulnerability management. Vanilla upstream version ranges are necessary for tracking, but distribution kernels are curated products. Red Hat, SUSE, Ubuntu, Debian, Arch, Fedora, and specialist vendors do not all expose vulnerability status through the same version semantics.
The “missing CPE” question should therefore be paired with three operational checks. Which distribution kernel package is installed? Does that package include the patch? Does the system actually use the affected i915 DSI DSC command-mode path?
Security teams that stop at the first question will overcount. Teams that ignore the first question because the bug sounds hardware-specific may underpatch. The right answer is to connect version data to hardware inventory and vendor advisory status.
That is harder than reading a CVSS score, but it is also what serious vulnerability management has become.
The PC platform has become less standardized in the places users cannot see. Internal panels use mobile-style interfaces. Compression is routine. Firmware hands opaque hints to operating systems. Vendor documentation, Windows driver behavior, and Linux reverse engineering meet in code paths that may run before a user can open a terminal.
That is not a Linux-only story. Windows administrators see the same class of complexity through display driver rollbacks, firmware updates, docking station regressions, and GPU vendor hotfixes. The difference is that Linux often exposes the reasoning in public commit messages, letting us watch the platform learn from the behavior Windows already encoded.
There is an uncomfortable dependency there. Linux should not have to treat Windows behavior as scripture, but ignoring it can be impractical when hardware was validated primarily against Windows. The healthiest outcome is not imitation for its own sake; it is convergence on the behavior the hardware actually expects.
In this case, convergence means not applying DSC horizontal timing adjustments in DSI command mode. That sounds minor because it is. It also prevents a kernel crash because minor assumptions in kernel graphics code can have major consequences.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Medium-Severity Bug That Lives in the Boot-Time Danger Zone
A Medium-Severity Bug That Lives in the Boot-Time Danger Zone
The mechanics of CVE-2026-31767 are almost comically narrow. In the Linux kernel’s drm/i915/dsi code, the driver adjusted horizontal timing values based on a Display Stream Compression ratio even when the panel was operating in DSI command mode. According to the kernel-side description, Intel’s display programming guidance appears to require that adjustment only in video mode, and the Windows driver reportedly follows that interpretation.That distinction matters because command mode and video mode are not just two labels for the same screen. In DSI video mode, the host streams pixel data continuously in a way that makes horizontal and vertical timing values central to the display pipeline. In command mode, the panel is driven more transactionally; timing still exists, but the driver is not supposed to treat those values the same way.
The Linux bug took a rule that made sense in one mode and applied it in another. On some machines, that made the adjusted horizontal total so small that a later calculation produced
line_time_us == 0. The next step tried to use that value when determining the vertical total, and the kernel hit a divide-by-zero condition.Security scoring systems translate that into availability impact. Humans should translate it into something plainer: on affected hardware, loading the graphics driver could crash the kernel.
That is why the CVSS 3.1 score of 5.5 feels both accurate and unsatisfying. The attack vector is local, privileges are required, user interaction is not required, and the consequence is denial of service rather than data theft or code execution. Yet the affected code sits in a path that many users never consciously touch and most administrators do not test deeply unless they manage Linux laptops, tablets, embedded devices, kiosks, or custom images.
The Windows Driver Is the Quiet Benchmark in a Linux CVE
The line in the fix description that will jump out to WindowsForum readers is not the divide-by-zero. It is the comparison: “this is also how the Windows driver does things.” In a Linux kernel CVE, that is a rare bit of cross-platform candor.Driver developers do not generally cite Windows behavior as a matter of admiration. They cite it because hardware vendors, firmware assumptions, and platform validation tend to orbit Windows first. If a panel, firmware table, or display controller quirk has been validated against the Windows graphics stack, matching that behavior can be the difference between a usable device and a black screen.
That does not mean Windows is automatically correct. It means Windows is often the reference environment that OEMs actually tested before shipping hardware. In the consumer PC ecosystem, especially with tablets, convertibles, and machines using tightly integrated panels, “what Windows does” can become a practical specification even when the official hardware documentation leaves room for interpretation.
CVE-2026-31767 is therefore not just a Linux bug. It is a small case study in how Windows compatibility still shapes the broader PC platform. The Linux i915 driver was doing something that made theoretical sense if one applied a compression-timing adjustment broadly. The fix narrowed that behavior to the mode where the hardware guidance and Windows implementation both suggested it belonged.
For Windows users, there is no immediate reason to panic. The submitted material identifies this as a Linux kernel vulnerability, and the affected component is the Linux i915 Direct Rendering Manager driver path, not the Windows Intel graphics driver. But the fact that the Windows driver appears in the remediation rationale tells us something about the hidden dependency chain behind every display panel: firmware, vendor documentation, OS driver behavior, and years of platform assumptions all meet at boot.
Display Drivers Are No Longer Just About Pixels
For a long time, display drivers were treated by many administrators as a nuisance category rather than a security category. They caused flicker, sleep bugs, multi-monitor weirdness, and the occasional black screen after Patch Tuesday. They did not always register mentally beside SMB, RDP, browsers, authentication stacks, or kernel networking.That distinction has been obsolete for years. Modern graphics drivers sit deep in the kernel, parse complex state, negotiate with firmware, touch power management, expose user-mode interfaces, and handle increasingly elaborate display protocols. Even when a given bug is “only” a denial-of-service issue, the blast radius can include boot reliability, remote management, kiosk uptime, and recovery workflows.
Display Stream Compression is a good example of this complexity. DSC exists because modern displays push enormous amounts of data: high resolutions, high refresh rates, HDR, multiple panels, and thin portable devices with bandwidth and power constraints. Compression allows hardware to move display data efficiently, but it also adds another layer of arithmetic and mode negotiation into driver code that used to be simpler.
DSI adds its own complications. It is common in mobile-style panels, tablets, convertibles, and devices that do not behave like the old desktop monitor attached by HDMI or DisplayPort. The more PC hardware borrows from phone and tablet design, the more desktop operating systems inherit mobile display assumptions.
That makes a divide-by-zero in a DSI path less surprising than it first sounds. The driver is not merely “drawing the screen.” It is interpreting panel capabilities, applying compression rules, calculating timings, and choosing behavior based on whether the panel is in video mode or command mode. One wrong assumption in that chain can turn into a kernel fault.
The Huawei MateBook E Detail Makes the Bug Real
The kernel description notes that the change does not actually make the display on the Huawei MateBook E work, but it does stop the kernel from exploding when the driver loads. That sentence is unusually blunt, and it is more useful than most vulnerability prose.It tells administrators two things. First, the patch is a stability fix for a crash condition, not necessarily a complete enablement fix for every affected machine. Second, the triggering scenario is not hypothetical in the abstract; it was observed on real hardware with a real DSI panel configuration.
This matters because many CVEs in the Linux kernel are born from code auditing or rare race conditions that most users will never encounter. CVE-2026-31767 lives closer to the hardware enablement world, where an affected machine can fail during driver initialization before the user has a clean path to diagnose much of anything.
The MateBook E is also symbolically fitting. Devices like it sit at the boundary between PC and tablet, exactly where DSI panels and firmware-mediated display quirks become more likely. They are the sort of hardware Windows tends to support first and Linux support often reaches through reverse engineering, vendor crumbs, and painstaking driver work.
The patch’s honesty is important. It does not claim the device is fixed. It claims the kernel no longer crashes in that path. That is a narrower improvement, but a crucial one: a broken display is a problem; a broken display plus a kernel crash is a recovery problem.
For users testing newer kernels on niche Intel tablet hardware, that difference can decide whether the machine is merely inconvenient or effectively unusable without external workarounds.
NVD’s CPE Range Is Broad, but the Real Exposure Is Hardware-Specific
The NVD change history attached to CVE-2026-31767 lists affected Linux kernel version ranges including 5.6 up to before 6.12.81, 6.13 up to before 6.18.22, 6.19 up to before 6.19.12, and 7.0 release candidates rc1 through rc6. That looks broad enough to alarm anyone scanning dashboards by version number alone.The practical exposure is narrower. A system needs to be running an affected kernel, using the relevant Intel i915 DSI path, and hitting the problematic DSC command-mode timing scenario. A headless Linux server on Intel hardware is not suddenly endangered in the same way as a tablet-style machine with a DSI panel.
This is where vulnerability management tools can mislead by flattening context. A scanner sees a kernel version and a CPE match. It may not know whether the machine has the relevant panel, whether i915 is loaded, whether the affected code path is reachable, or whether the system is a fleet-critical kiosk sitting in a lobby.
That does not make the CVE irrelevant. It means the triage process should be evidence-based. The right first question is not “Does any Linux kernel in my environment match this CPE?” but “Do we operate devices where Intel i915 DSI display initialization matters to availability?”
For many enterprises, the answer will be no. For hardware labs, Linux desktop fleets, educational tablet programs, industrial panels, thin clients, and developers running recent kernels on convertibles, the answer may be yes.
The Security Label Is Doing Stability Work
CVE-2026-31767 is a classic example of the modern Linux kernel CVE machine assigning a security identifier to what many users would instinctively call a stability bug. There is no theft of secrets here. There is no remote worm. There is no privilege escalation in the description. There is a local, privileged path to crashing the kernel through a driver calculation error.That can irritate people who want CVEs to mean “urgent security incident.” But availability is part of security, and kernel crashes are not benign just because they lack a flashy exploit chain. If a local user with sufficient privileges can reliably trigger a system crash, that is a denial-of-service condition. If the crash can occur during routine driver loading on affected hardware, the operational stakes are even more obvious.
The bigger issue is not that this bug received a CVE. The bigger issue is that CVE feeds now mix catastrophic remotely exploitable flaws with hardware-specific crash fixes in the same river of alerts. Administrators are expected to distinguish them quickly, usually while patch windows, vendor advisories, and compliance tooling all shout at once.
The result is a triage burden that falls hardest on smaller teams. A medium Linux kernel CVE may be ignorable, urgent, or somewhere in between depending entirely on the hardware estate. Generic severity scoring cannot capture that estate-specific reality.
For WindowsForum’s audience, this is familiar from the Windows side too. A CVE affecting a Windows component may matter greatly to domain controllers and barely at all to isolated clients. A graphics-driver bug may be irrelevant to servers but painful for workstations used in design, manufacturing, or classroom environments. The label starts the conversation; it does not finish it.
The Local Attack Requirement Should Not Put Everyone to Sleep
The CVSS vector for CVE-2026-31767 requires local access and low privileges. That combination often pushes bugs down the queue, and usually for good reason. Remote unauthenticated bugs deserve faster treatment than local denial-of-service issues.But local does not always mean unimportant. In multi-user Linux environments, labs, classrooms, shared workstations, or systems where users can trigger hardware paths indirectly, local availability bugs may be more than theoretical. In managed fleets, local also includes software already running on the box, whether legitimate, compromised, or misconfigured.
That said, the exploitability story here should not be inflated. The description points to a driver load and hardware-specific timing calculation, not a universal one-command crash across all Linux desktops. A remote attacker would need a separate foothold or an indirect path to trigger the condition. Nothing in the submitted information suggests data exposure, integrity compromise, or arbitrary code execution.
The most realistic concern is operational reliability. If you deploy Linux on hardware with DSI panels and Intel graphics, you want the patched kernel because display initialization should not be capable of taking the machine down. If you run servers, virtual machines, or desktops without the relevant display path, this CVE is more likely to be a compliance item than an emergency.
That is the mature reading of a medium-severity kernel CVE: patch it, but do not pretend every kernel bug has the same operational meaning.
Release Candidates in the Affected List Signal a Fast-Moving Kernel Line
One detail in the NVD record deserves careful interpretation: Linux kernel 7.0 release candidates rc1 through rc6 appear in the affected CPE configuration. Release candidates are test builds, not stable production kernels for conservative environments. Their presence tells us the bug existed in development or pre-release lines as well as supported stable series.That matters for enthusiasts and developers more than for most enterprises. People running release candidates expect breakage, but they also form the early warning system that catches bugs before stable users inherit them. In graphics drivers, that testing is especially valuable because display hardware diversity is enormous and vendor documentation rarely covers every real-world panel quirk.
The affected stable ranges are the more important operational story. Fixes are identified in stable patch references, meaning distributions and downstream vendors can pick them up through ordinary kernel update channels. Users should not need to hand-apply an i915 patch unless they are building custom kernels or maintaining specialized images.
The cadence also shows how quickly a low-level bug can move from upstream commit to CVE record to scanner finding. The CVE was received from kernel.org on May 1, 2026, and NVD analysis updates followed on May 11, 2026. That ten-day gap is normal enough, but it is long enough for confusion: distribution trackers, vendor advisories, and scanners may not agree at the same moment.
If your tooling reports this CVE but your distribution kernel version does not appear to match the vanilla kernel version ranges, check your vendor’s backport status. Enterprise Linux distributions often patch vulnerabilities without changing the upstream-looking version number in the way newcomers expect.
The MSRC Link Is a Cataloging Clue, Not a Windows Panic Button
The user-submitted source points to Microsoft’s Security Update Guide entry for CVE-2026-31767. That is bound to raise eyebrows: why is a Linux kernel i915 bug showing up in a Microsoft security context?The least dramatic answer is usually the right one. Microsoft’s security ecosystem tracks CVEs beyond the classic Windows client and server surface, especially where Microsoft products, cloud images, Linux workloads, or dependency inventories may be involved. A CVE appearing in an MSRC-facing location does not automatically mean Windows itself is vulnerable.
For Windows administrators, the important distinction is product applicability. The submitted description is unambiguously about the Linux kernel. The vulnerable component is not DirectX, WDDM, the Windows display driver model, or an Intel Windows driver package delivered through Windows Update. It is the Linux DRM i915 DSI implementation.
That distinction matters because CVE dashboards often travel faster than context. A security team may see “Microsoft” and “CVE” in the same workflow and assume Patch Tuesday relevance. Here, the more plausible operational link is mixed estate management: Azure Linux images, Windows Subsystem for Linux adjacent inventories, Defender vulnerability management, third-party scanners, or organizations that use Microsoft tooling to track non-Windows assets.
The irony is that Windows appears in this CVE as a behavioral reference, not as the affected platform. The Linux fix aligns the i915 logic with what the Windows driver already did for this mode distinction. In this case, Windows is less the patient and more the chart on the wall.
The Fix Is Simple Because the Model Was Wrong
The patch title says almost everything: do not do DSC horizontal timing adjustments in command mode. It is a small change in policy, not a sprawling rewrite. That is often how low-level bugs look after the hard part is done.The hard part is realizing which assumption is wrong. If a driver applies a compression ratio to horizontal timing values, that may appear reasonable when looking at one mode or one class of panel. The bug emerges when that logic crosses a boundary where the same values no longer carry the same meaning.
This is why hardware driver bugs can be so frustrating. The code may be clean, the math may be straightforward, and the failure may still happen because the model is wrong for a specific hardware state. In CVE-2026-31767, the state is DSI command mode.
The division by zero is the visible crash. The deeper issue is an invalid transformation of display timing data. Once the horizontal total is adjusted into nonsense territory, the later calculation has little chance of producing a safe result.
That is also why the fix does not make the MateBook E display work. Removing the bad adjustment prevents a kernel crash, but it does not solve every missing piece of panel enablement. Stability fixes and hardware support fixes overlap, but they are not identical.
Kernel Graphics Bugs Expose the Limits of Generic Patch Advice
The safest general advice is to update to a kernel containing the fix. That is true and boring. It is also incomplete.For mainstream distribution users, the practical answer is to install the kernel update supplied by the distribution, reboot into it, and confirm the running kernel changed. For users running custom kernels, release candidates, or hardware-enablement branches, the answer is to verify whether one of the referenced stable fixes or the underlying upstream commit is included.
For administrators, the more interesting work is inventory. Identify machines with Intel integrated graphics using the i915 driver and DSI-connected internal panels. Pay special attention to tablet-style devices, convertibles, embedded displays, and any fleet where Linux was installed onto hardware originally sold primarily for Windows.
Then examine how those machines are used. A developer’s spare test tablet is not a production incident. A check-in kiosk, classroom device, medical cart, point-of-sale terminal, or field-service tablet has a different availability profile.
This is where Windows management habits can help Linux operations. Windows admins are used to thinking in terms of hardware rings, driver validation, staged rollout, and rollback plans. Linux desktop fleets need the same discipline when the affected layer is graphics. A kernel update that fixes one display crash can still introduce another regression on a different GPU, dock, or panel.
Patch quickly where the hardware matches. Test deliberately where uptime matters. Avoid blanket panic where the component is not present.
For Dual-Booters and Lab Machines, the Risk Is Mostly on the Penguin Side
Many WindowsForum readers run Linux in dual-boot setups, on spare laptops, on lab tablets, or inside home infrastructure. CVE-2026-31767 is unlikely to affect their Windows installation directly, but it may affect the Linux side if the machine uses the relevant Intel display path.That dual-boot context is worth spelling out because hardware bugs blur OS boundaries in users’ minds. The same panel, firmware, and GPU exist whether Windows or Linux boots. But the vulnerable code path is operating-system-specific. Windows may initialize the panel using logic that avoids this crash; Linux needed a patch to do the same.
If your machine has been booting Linux reliably, this CVE does not mean it will suddenly fail tomorrow. Vulnerabilities are not magic weather systems. But if you are testing new kernels on Intel tablet hardware, especially around the affected version ranges, the fix is worth having.
For users who hit a crash during graphics initialization, recovery may require booting an older kernel, using a fallback kernel, disabling modesetting temporarily, or updating from a rescue environment. Those are unpleasant workflows, and they are exactly why a “medium” graphics CVE can feel high-severity to the person staring at a dead screen.
The bigger lesson for enthusiasts is to keep at least one known-good kernel installed. Rolling kernels are fun until the only visible output path breaks.
The CPE Question Is the Right One, but It Has the Wrong Center of Gravity
The submitted NVD text asks, “Are we missing a CPE here?” That is the database maintainer’s version of a practical question: is the affected software list complete? It is a useful question, but for this CVE the more important answer lives below the CPE layer.CPEs describe software products and versions. CVE-2026-31767 depends heavily on hardware configuration and driver path reachability. A Linux kernel version may be vulnerable in theory while a given deployment cannot trigger the affected path. Conversely, a patched distribution kernel may carry a backported fix while still reporting a version number that looks old.
That mismatch is a recurring problem in kernel vulnerability management. Vanilla upstream version ranges are necessary for tracking, but distribution kernels are curated products. Red Hat, SUSE, Ubuntu, Debian, Arch, Fedora, and specialist vendors do not all expose vulnerability status through the same version semantics.
The “missing CPE” question should therefore be paired with three operational checks. Which distribution kernel package is installed? Does that package include the patch? Does the system actually use the affected i915 DSI DSC command-mode path?
Security teams that stop at the first question will overcount. Teams that ignore the first question because the bug sounds hardware-specific may underpatch. The right answer is to connect version data to hardware inventory and vendor advisory status.
That is harder than reading a CVSS score, but it is also what serious vulnerability management has become.
The Small Crash That Explains a Bigger Maintenance Problem
CVE-2026-31767 will not be remembered like a major remote code execution flaw. It will not dominate incident-response calls or force emergency weekend patching for most organizations. Its importance is quieter: it shows how much fragile, security-relevant behavior is buried inside the driver assumptions that make modern hardware usable.The PC platform has become less standardized in the places users cannot see. Internal panels use mobile-style interfaces. Compression is routine. Firmware hands opaque hints to operating systems. Vendor documentation, Windows driver behavior, and Linux reverse engineering meet in code paths that may run before a user can open a terminal.
That is not a Linux-only story. Windows administrators see the same class of complexity through display driver rollbacks, firmware updates, docking station regressions, and GPU vendor hotfixes. The difference is that Linux often exposes the reasoning in public commit messages, letting us watch the platform learn from the behavior Windows already encoded.
There is an uncomfortable dependency there. Linux should not have to treat Windows behavior as scripture, but ignoring it can be impractical when hardware was validated primarily against Windows. The healthiest outcome is not imitation for its own sake; it is convergence on the behavior the hardware actually expects.
In this case, convergence means not applying DSC horizontal timing adjustments in DSI command mode. That sounds minor because it is. It also prevents a kernel crash because minor assumptions in kernel graphics code can have major consequences.
The Patch Window Is Really a Hardware Inventory Exercise
This CVE is best handled neither as a fire drill nor as trivia. Treat it as a targeted kernel update and a reminder to improve visibility into the hardware paths your systems actually use.- Systems running affected Linux kernel versions should receive vendor-supplied kernel updates, especially if they use Intel i915 graphics with DSI-connected internal panels.
- Windows client and server installations are not identified as the affected platform in the submitted vulnerability description.
- The most plausible real-world impact is a local denial-of-service crash during or around graphics driver initialization on specific hardware.
- Scanner results based only on upstream Linux kernel CPE ranges should be checked against distribution backports and actual device hardware.
- Machines used as kiosks, tablets, classroom devices, embedded panels, or hardware test systems deserve more attention than ordinary servers without the relevant display path.
- Keeping a known-good fallback kernel remains one of the simplest defenses against graphics regressions on Linux enthusiast and lab systems.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center