CVE-2026-31777 is a medium-severity Linux kernel vulnerability published May 1, 2026, affecting the ALSA ctxfi sound driver, where a missing error check around
The Linux kernel fix behind CVE-2026-31777 is almost comically modest: the ctxfi driver assumed that an index-mapping helper returned a valid value, and the patch adds the error handling that should have been there in the first place. The vulnerable path sits in ALSA, the Advanced Linux Sound Architecture subsystem, and specifically in the Creative X-Fi-oriented ctxfi driver rather than in a core networking, filesystem, or privilege-boundary component.
Yet the CVE machinery does not care whether a bug lives in a glamorous subsystem. Once the Linux kernel project assigns and publishes a CVE, scanners, dashboards, ticketing systems, distro trackers, cloud inventories, and compliance tools all ingest it. A bug in an audio driver can suddenly appear beside remote code execution flaws in a weekly vulnerability report, dressed in the same CVE formatting and the same score vocabulary.
That is the first lesson for WindowsForum readers who live across Windows, Linux, WSL, Azure, Hyper-V, containers, and fleet management consoles: not every CVE that lands in a Microsoft-facing or enterprise-facing feed is a Microsoft vulnerability in the ordinary sense. Some are upstream Linux issues that matter because Microsoft, like every large platform vendor now, ships, hosts, scans, mirrors, or supports Linux in some part of its ecosystem.
The supplied MSRC link is therefore more of a routing clue than a blame marker. It tells us this issue is visible to Microsoft’s vulnerability update universe, not that Windows itself suddenly has an ALSA sound-driver problem. In 2026, that distinction matters because enterprise vulnerability management has become less about operating-system tribes and more about inventory boundaries.
Translated into administrator English, this is not a remote worm, not a credential theft bug, and not an obvious path to kernel-level compromise based on the public description. The modeled impact is denial of service: a local user with some level of access can potentially push the affected kernel path into a bad state severe enough to affect system availability.
That matters on multi-user Linux systems, shared lab machines, development workstations, audio production boxes, and unusual embedded or kiosk deployments where the hardware and driver combination is present. It matters much less on a headless server that never loads the ctxfi module, never exposes the hardware, and has no local untrusted users. CVSS gives you the severity grammar; inventory tells you whether the sentence applies.
The problem with vulnerability dashboards is that they often flatten that distinction. A Medium kernel CVE can become a red ticket simply because the word “kernel” appears, while the actual exposure depends on whether the driver is compiled, loaded, reachable, and paired with relevant hardware. For this CVE, those qualifiers are not fine print. They are the story.
That is a familiar failure mode. One function knows how to report “this mapping failed,” while another function proceeds as though the answer must be a usable index. The result can be an out-of-range access, invalid state, or a crash path, depending on how the returned value is consumed and what surrounding checks exist.
The fix, as described, is not an architectural rewrite. It is the sort of defensive programming patch that says: before trusting the mapping, check whether it failed. That simplicity is not a reason to dismiss the CVE. It is a reason to remember that kernel security is often made of small obligations repeated thousands of times.
The ctxfi driver is also a good reminder that old or niche hardware support can remain security-relevant long after it has stopped being fashionable. Driver code tends to persist because Linux prides itself on broad hardware compatibility. That compatibility is a strength, but it also means obscure code paths continue to exist in production kernels, sometimes far from the attention given to networking stacks, GPU drivers, or virtualization code.
Kernel CVE versioning is notoriously awkward because upstream kernels, stable kernels, long-term support trees, and distribution kernels do not line up neatly. A flaw can be introduced years ago, fixed upstream in one branch, backported into several stable branches, and then appear in vendor kernels with their own patch stacks and version numbers. A raw CPE range is rarely enough to determine whether a given Red Hat, Ubuntu, Debian, SUSE, Amazon, or Microsoft-flavored kernel is actually vulnerable.
The Debian tracker snapshot is a useful example of that complexity. It shows some Debian releases still marked vulnerable while newer unstable or development versions are fixed. That does not mean every Debian machine is equally exposed; it means the distro’s security tracking had not yet marked those source packages as fixed at the time represented by the tracker.
For enterprise IT, the right response is not to hand-compare upstream kernel numbers and panic. The right response is to check the distribution advisory, the actual package build, and the loaded module state. In Linux, the version string is only the beginning of the evidence.
That behavior is not necessarily wrong. A scanner usually cannot prove absence of reachability across every runtime path, hardware permutation, and module-loading policy. But administrators should understand the difference between an affected package and an exploitable deployment.
With a driver-level issue, exposure often depends on four practical facts. Is the vulnerable driver built into the kernel or available as a module? Is the relevant module loaded? Is matching hardware present or emulated? Can a local low-privilege user trigger the vulnerable path? If those answers are mostly no, the operational risk falls sharply even if the package version remains technically in range.
This distinction is especially important for Windows-centric environments that now manage Linux through adjacent platforms. A CVE may surface in Microsoft Defender, Azure inventory, container scanning, WSL-related workflows, or third-party EDR dashboards. The alert might be real, but the practical response may be “patch during the next kernel maintenance window” rather than “declare an incident.”
That is why MSRC visibility matters even when the vulnerable code is not Windows code. Microsoft’s security universe now spans products and services where Linux is part of the stack. Azure hosts Linux at scale. Developers run Linux userspaces on Windows. Enterprises monitor heterogeneous fleets from Microsoft consoles. The clean old boundary between “Windows vulnerability” and “Linux vulnerability” has dissolved at the management layer.
For Windows administrators, the practical shift is cultural as much as technical. You do not need to become a kernel audio-driver specialist, but you do need to know when a Linux CVE in a Microsoft-adjacent feed applies to your environment. The answer increasingly lives in asset classification rather than brand recognition.
This is also where vulnerability management teams can lose credibility with system owners. If every upstream Linux CVE is escalated as though it were a domain-controller emergency, engineers learn to ignore the queue. If, instead, the alert is enriched with module, hardware, privilege, and workload context, the same CVE becomes actionable.
That does not make the vulnerability irrelevant. Local denial-of-service bugs can be useful in shared systems, lab environments, thin-client deployments, and chained attacks where an intruder already has a foothold and wants to disrupt recovery or monitoring. Availability is a real security property, especially for systems that perform real-time audio, industrial control support, or user-facing kiosk functions.
But most enterprise Linux risk prioritization starts with internet exposure, privilege escalation, remote code execution, and sensitive data access. CVE-2026-31777 does not appear to sit in those higher-risk buckets based on the public description and NVD scoring. The severity label is doing its job: Medium is not zero, but it is not a five-alarm fire.
This is the moment where mature patching programs separate themselves from immature ones. Mature programs patch the kernel through standard maintenance, confirm whether the driver is present where it matters, and document any risk acceptance for non-exposed systems. Immature programs either ignore it entirely because “it is just sound” or overreact because “it is kernel.”
For desktop Linux systems and developer workstations, the answer is generally straightforward: take the distribution’s next kernel update and reboot. For production servers, the calculus is more layered. If the machine is headless, lacks the affected hardware, and does not load the driver, the urgency may be lower. If the machine supports untrusted local users or specialized audio hardware, the window tightens.
Containers add another layer of confusion. Most containers share the host kernel, so rebuilding a container image usually does not fix a host kernel driver vulnerability. Conversely, a container scanner may flag kernel-adjacent CVE data in a way that does not map cleanly to the container’s own filesystem. The patch target is the host kernel, host image, or distribution kernel package, not necessarily the application container.
WSL deserves its own note. WSL uses Microsoft-managed kernel plumbing rather than a normal distro-owned hardware kernel in many common configurations, and it does not map directly onto a physical ALSA ctxfi sound-card driver scenario. Administrators should avoid assuming that every Linux kernel CVE applies to every WSL installation in the same way it applies to a bare-metal Linux workstation.
An upstream kernel version range can be useful for researchers and automated enrichment, but administrators live in package names, vendor errata, cloud image IDs, appliance firmware, and kernel build strings. A vulnerability can be fixed in a vendor kernel that still reports a base version inside the upstream vulnerable range. It can also remain present in a long-term kernel that looks old but has a sprawling backport history.
That is why the right evidence chain starts with the vendor that built your kernel. For Debian, Ubuntu, Red Hat, SUSE, Amazon Linux, Oracle Linux, Azure Linux, and appliance vendors, the authoritative remediation state usually comes from the distro or product advisory, not from a naked upstream CPE range. NVD is a valuable index, but it is not a substitute for package-level truth.
There is also a hidden administrative cost here. Every ambiguous CPE creates work: security teams file tickets, platform teams investigate applicability, and managers ask why a Medium CVE remains open. Better vulnerability metadata reduces that waste, but until the ecosystem improves, local asset intelligence remains the compensating control.
There is a long-standing tension here. Linux users value the fact that hardware can keep working long after a vendor has moved on. Removing drivers aggressively would break systems and anger users. Keeping drivers indefinitely means maintainers must continue to review, fix, and harden code paths that few people exercise daily.
From a security perspective, modularity is the pressure valve. If a driver is not needed, it should not be loaded. If a device class is irrelevant to a server fleet, administrators can use kernel configuration, module blacklisting, secure boot policies, or hardened images to reduce reachable attack surface. Patching remains necessary, but reducing exposure is what turns an urgent bug into a managed one.
The industry talks endlessly about “least privilege” for users and services. The same instinct applies to hardware support. A server does not need every sound, TV tuner, USB gadget, and legacy adapter driver available at runtime simply because the generic distribution kernel can provide it.
That does not mean dismissing the CVE. It means refusing to let the CVE number do all the thinking. Security work is full of these medium-severity issues that are individually unglamorous and collectively important. They become dangerous when they are ignored everywhere or escalated everywhere.
For Windows-heavy shops, the same discipline applies across boundaries. If Defender, Azure, MSRC, or a third-party scanner surfaces a Linux kernel CVE, the first question is not “Why is Microsoft telling me about ALSA?” The first question is “Which asset, image, package, and runtime condition caused this alert?”
The answer may be a Linux VM in Azure, a developer workstation, a lab host, a Kubernetes node, or an inherited appliance. Each has a different remediation path. The feed is the beginning of triage, not the end of it.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
daio_device_index() could allow a local privileged user to trigger a high-impact availability failure on affected kernels. That sounds narrow because it is narrow, but the interesting part is not the sound card. The interesting part is how a small driver bug can travel through the modern vulnerability ecosystem, from kernel.org to NVD to vendor portals, and arrive on an administrator’s desk looking larger, stranger, or more urgent than the code change itself deserves.
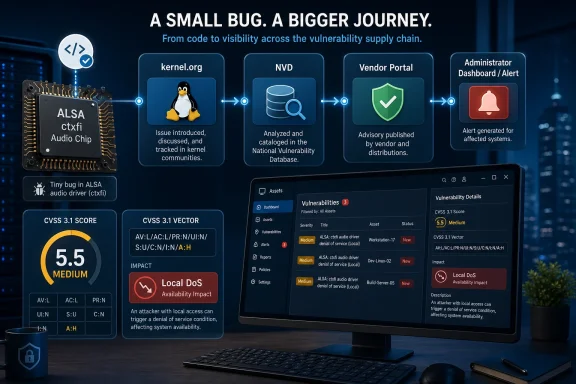 A Sound Driver Bug Becomes a Supply-Chain Signal
A Sound Driver Bug Becomes a Supply-Chain Signal
The Linux kernel fix behind CVE-2026-31777 is almost comically modest: the ctxfi driver assumed that an index-mapping helper returned a valid value, and the patch adds the error handling that should have been there in the first place. The vulnerable path sits in ALSA, the Advanced Linux Sound Architecture subsystem, and specifically in the Creative X-Fi-oriented ctxfi driver rather than in a core networking, filesystem, or privilege-boundary component.Yet the CVE machinery does not care whether a bug lives in a glamorous subsystem. Once the Linux kernel project assigns and publishes a CVE, scanners, dashboards, ticketing systems, distro trackers, cloud inventories, and compliance tools all ingest it. A bug in an audio driver can suddenly appear beside remote code execution flaws in a weekly vulnerability report, dressed in the same CVE formatting and the same score vocabulary.
That is the first lesson for WindowsForum readers who live across Windows, Linux, WSL, Azure, Hyper-V, containers, and fleet management consoles: not every CVE that lands in a Microsoft-facing or enterprise-facing feed is a Microsoft vulnerability in the ordinary sense. Some are upstream Linux issues that matter because Microsoft, like every large platform vendor now, ships, hosts, scans, mirrors, or supports Linux in some part of its ecosystem.
The supplied MSRC link is therefore more of a routing clue than a blame marker. It tells us this issue is visible to Microsoft’s vulnerability update universe, not that Windows itself suddenly has an ALSA sound-driver problem. In 2026, that distinction matters because enterprise vulnerability management has become less about operating-system tribes and more about inventory boundaries.
The CVSS Score Says “Medium,” But the Vector Says “Local Crash”
NVD lists CVE-2026-31777 with a CVSS 3.1 base score of 5.5, rated Medium. The vector is the key: local attack vector, low attack complexity, low privileges required, no user interaction, unchanged scope, no confidentiality impact, no integrity impact, and high availability impact.Translated into administrator English, this is not a remote worm, not a credential theft bug, and not an obvious path to kernel-level compromise based on the public description. The modeled impact is denial of service: a local user with some level of access can potentially push the affected kernel path into a bad state severe enough to affect system availability.
That matters on multi-user Linux systems, shared lab machines, development workstations, audio production boxes, and unusual embedded or kiosk deployments where the hardware and driver combination is present. It matters much less on a headless server that never loads the ctxfi module, never exposes the hardware, and has no local untrusted users. CVSS gives you the severity grammar; inventory tells you whether the sentence applies.
The problem with vulnerability dashboards is that they often flatten that distinction. A Medium kernel CVE can become a red ticket simply because the word “kernel” appears, while the actual exposure depends on whether the driver is compiled, loaded, reachable, and paired with relevant hardware. For this CVE, those qualifiers are not fine print. They are the story.
The Missing Check Is the Kind of Bug Kernel Hardening Was Built to Catch
The public kernel description is short but revealing. The ctxfi driver “blindly assumed” a proper value fromdaio_device_index(), but that assumption was not always true. In kernel code, a helper returning an error-coded integer is only safe if every caller treats it as potentially hostile.That is a familiar failure mode. One function knows how to report “this mapping failed,” while another function proceeds as though the answer must be a usable index. The result can be an out-of-range access, invalid state, or a crash path, depending on how the returned value is consumed and what surrounding checks exist.
The fix, as described, is not an architectural rewrite. It is the sort of defensive programming patch that says: before trusting the mapping, check whether it failed. That simplicity is not a reason to dismiss the CVE. It is a reason to remember that kernel security is often made of small obligations repeated thousands of times.
The ctxfi driver is also a good reminder that old or niche hardware support can remain security-relevant long after it has stopped being fashionable. Driver code tends to persist because Linux prides itself on broad hardware compatibility. That compatibility is a strength, but it also means obscure code paths continue to exist in production kernels, sometimes far from the attention given to networking stacks, GPU drivers, or virtualization code.
NVD’s Version Range Looks Broad Because Kernel Metadata Is Messy
The NVD change history attached to the supplied data lists Linux kernel 7.0 release candidates rc1 through rc6, plus kernel versions from 2.6.31 up to but excluding 6.19.12. That is a strikingly broad range, and it may alarm anyone reading it without context.Kernel CVE versioning is notoriously awkward because upstream kernels, stable kernels, long-term support trees, and distribution kernels do not line up neatly. A flaw can be introduced years ago, fixed upstream in one branch, backported into several stable branches, and then appear in vendor kernels with their own patch stacks and version numbers. A raw CPE range is rarely enough to determine whether a given Red Hat, Ubuntu, Debian, SUSE, Amazon, or Microsoft-flavored kernel is actually vulnerable.
The Debian tracker snapshot is a useful example of that complexity. It shows some Debian releases still marked vulnerable while newer unstable or development versions are fixed. That does not mean every Debian machine is equally exposed; it means the distro’s security tracking had not yet marked those source packages as fixed at the time represented by the tracker.
For enterprise IT, the right response is not to hand-compare upstream kernel numbers and panic. The right response is to check the distribution advisory, the actual package build, and the loaded module state. In Linux, the version string is only the beginning of the evidence.
This Is Why “Affected” Does Not Always Mean “Exploitable”
Security scanners are paid to be suspicious, not nuanced. If a scanner sees a kernel package version that falls into a vulnerable range, it may flag CVE-2026-31777 even if the machine has no Creative X-Fi hardware, no ctxfi module loaded, and no realistic path for an untrusted local user to reach the code.That behavior is not necessarily wrong. A scanner usually cannot prove absence of reachability across every runtime path, hardware permutation, and module-loading policy. But administrators should understand the difference between an affected package and an exploitable deployment.
With a driver-level issue, exposure often depends on four practical facts. Is the vulnerable driver built into the kernel or available as a module? Is the relevant module loaded? Is matching hardware present or emulated? Can a local low-privilege user trigger the vulnerable path? If those answers are mostly no, the operational risk falls sharply even if the package version remains technically in range.
This distinction is especially important for Windows-centric environments that now manage Linux through adjacent platforms. A CVE may surface in Microsoft Defender, Azure inventory, container scanning, WSL-related workflows, or third-party EDR dashboards. The alert might be real, but the practical response may be “patch during the next kernel maintenance window” rather than “declare an incident.”
Microsoft’s Presence in the Feed Reflects the New Shape of Windows Infrastructure
A decade ago, a Linux ALSA bug showing up in a Windows community would have felt like category confusion. In 2026, it is routine. Windows estates increasingly include Linux guests, Linux containers, Linux-based appliances, Azure Linux images, WSL developer machines, Kubernetes nodes, and cross-platform endpoint agents.That is why MSRC visibility matters even when the vulnerable code is not Windows code. Microsoft’s security universe now spans products and services where Linux is part of the stack. Azure hosts Linux at scale. Developers run Linux userspaces on Windows. Enterprises monitor heterogeneous fleets from Microsoft consoles. The clean old boundary between “Windows vulnerability” and “Linux vulnerability” has dissolved at the management layer.
For Windows administrators, the practical shift is cultural as much as technical. You do not need to become a kernel audio-driver specialist, but you do need to know when a Linux CVE in a Microsoft-adjacent feed applies to your environment. The answer increasingly lives in asset classification rather than brand recognition.
This is also where vulnerability management teams can lose credibility with system owners. If every upstream Linux CVE is escalated as though it were a domain-controller emergency, engineers learn to ignore the queue. If, instead, the alert is enriched with module, hardware, privilege, and workload context, the same CVE becomes actionable.
The Local Privilege Requirement Keeps This Out of the Nightmare Category
The CVSS vector’s local, low-privilege requirements are worth dwelling on because they define the realistic threat model. An attacker needs local access with some privileges. There is no public indication in the supplied data that a remote network packet, malicious web page, or unauthenticated request can hit this bug.That does not make the vulnerability irrelevant. Local denial-of-service bugs can be useful in shared systems, lab environments, thin-client deployments, and chained attacks where an intruder already has a foothold and wants to disrupt recovery or monitoring. Availability is a real security property, especially for systems that perform real-time audio, industrial control support, or user-facing kiosk functions.
But most enterprise Linux risk prioritization starts with internet exposure, privilege escalation, remote code execution, and sensitive data access. CVE-2026-31777 does not appear to sit in those higher-risk buckets based on the public description and NVD scoring. The severity label is doing its job: Medium is not zero, but it is not a five-alarm fire.
This is the moment where mature patching programs separate themselves from immature ones. Mature programs patch the kernel through standard maintenance, confirm whether the driver is present where it matters, and document any risk acceptance for non-exposed systems. Immature programs either ignore it entirely because “it is just sound” or overreact because “it is kernel.”
The Patch Is Simple; the Rollout Is Not
Kernel patches are never just patches. Even a small fix can mean a reboot, a maintenance window, compatibility testing, DKMS module rebuilds, hypervisor coordination, or image refreshes. That operational friction is why Medium kernel CVEs often linger longer than application flaws.For desktop Linux systems and developer workstations, the answer is generally straightforward: take the distribution’s next kernel update and reboot. For production servers, the calculus is more layered. If the machine is headless, lacks the affected hardware, and does not load the driver, the urgency may be lower. If the machine supports untrusted local users or specialized audio hardware, the window tightens.
Containers add another layer of confusion. Most containers share the host kernel, so rebuilding a container image usually does not fix a host kernel driver vulnerability. Conversely, a container scanner may flag kernel-adjacent CVE data in a way that does not map cleanly to the container’s own filesystem. The patch target is the host kernel, host image, or distribution kernel package, not necessarily the application container.
WSL deserves its own note. WSL uses Microsoft-managed kernel plumbing rather than a normal distro-owned hardware kernel in many common configurations, and it does not map directly onto a physical ALSA ctxfi sound-card driver scenario. Administrators should avoid assuming that every Linux kernel CVE applies to every WSL installation in the same way it applies to a bare-metal Linux workstation.
The CPE Question Is a Symptom of a Bigger Inventory Problem
The supplied NVD text includes the familiar “Are we missing a CPE here?” prompt. For this CVE, that question is more than boilerplate. CPEs are often blunt instruments for kernel vulnerabilities because Linux is not distributed as one product in one uniform form.An upstream kernel version range can be useful for researchers and automated enrichment, but administrators live in package names, vendor errata, cloud image IDs, appliance firmware, and kernel build strings. A vulnerability can be fixed in a vendor kernel that still reports a base version inside the upstream vulnerable range. It can also remain present in a long-term kernel that looks old but has a sprawling backport history.
That is why the right evidence chain starts with the vendor that built your kernel. For Debian, Ubuntu, Red Hat, SUSE, Amazon Linux, Oracle Linux, Azure Linux, and appliance vendors, the authoritative remediation state usually comes from the distro or product advisory, not from a naked upstream CPE range. NVD is a valuable index, but it is not a substitute for package-level truth.
There is also a hidden administrative cost here. Every ambiguous CPE creates work: security teams file tickets, platform teams investigate applicability, and managers ask why a Medium CVE remains open. Better vulnerability metadata reduces that waste, but until the ecosystem improves, local asset intelligence remains the compensating control.
The Driver Nobody Thinks About Still Ships in the Kernel Nobody Can Ignore
The ctxfi driver supports Creative X-Fi-family audio hardware, which is not exactly the center of today’s enterprise threat model. That makes CVE-2026-31777 a useful counterexample to the idea that only fashionable components matter. Kernel attack surface includes decades of hardware enablement, and old support code can still be compiled into modern distributions.There is a long-standing tension here. Linux users value the fact that hardware can keep working long after a vendor has moved on. Removing drivers aggressively would break systems and anger users. Keeping drivers indefinitely means maintainers must continue to review, fix, and harden code paths that few people exercise daily.
From a security perspective, modularity is the pressure valve. If a driver is not needed, it should not be loaded. If a device class is irrelevant to a server fleet, administrators can use kernel configuration, module blacklisting, secure boot policies, or hardened images to reduce reachable attack surface. Patching remains necessary, but reducing exposure is what turns an urgent bug into a managed one.
The industry talks endlessly about “least privilege” for users and services. The same instinct applies to hardware support. A server does not need every sound, TV tuner, USB gadget, and legacy adapter driver available at runtime simply because the generic distribution kernel can provide it.
Vulnerability Feeds Need Triage, Not Theater
CVE-2026-31777 is a perfect test of whether an organization’s vulnerability management process is calibrated. The wrong process sees “Linux kernel,” “availability high,” and a broad version range, then generates noise. The better process asks whether any managed system actually loads ctxfi, whether local untrusted users exist, whether the vendor kernel is fixed, and when the next reboot window occurs.That does not mean dismissing the CVE. It means refusing to let the CVE number do all the thinking. Security work is full of these medium-severity issues that are individually unglamorous and collectively important. They become dangerous when they are ignored everywhere or escalated everywhere.
For Windows-heavy shops, the same discipline applies across boundaries. If Defender, Azure, MSRC, or a third-party scanner surfaces a Linux kernel CVE, the first question is not “Why is Microsoft telling me about ALSA?” The first question is “Which asset, image, package, and runtime condition caused this alert?”
The answer may be a Linux VM in Azure, a developer workstation, a lab host, a Kubernetes node, or an inherited appliance. Each has a different remediation path. The feed is the beginning of triage, not the end of it.
The Practical Read on This Particular Kernel Flaw
CVE-2026-31777 deserves a patch, but it does not deserve panic. The most useful response is to turn the generic CVE into a concrete environmental fact pattern.- Systems running affected Linux kernels should receive vendor-provided kernel updates when available, with reboots scheduled according to normal kernel maintenance policy.
- Administrators should check whether the ctxfi driver is built, available, or loaded before treating every Linux host as equally exposed.
- The public scoring points to local denial of service, not remote code execution or data theft, based on the available NVD vector.
- Distribution advisories and package versions should carry more operational weight than broad upstream CPE ranges.
- Container findings should be traced back to the host kernel, because rebuilding an application image will usually not remediate a host driver flaw.
- Microsoft-facing visibility does not make this a Windows vulnerability; it reflects the mixed Windows-and-Linux reality of modern enterprise estates.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center