CVE-2026-43126 is a Linux kernel vulnerability published on May 6, 2026, in the ALSA OSS mixer compatibility layer, where missing disconnect checks could allow pending mixer operations to touch a sound card after teardown. The bug is not a Windows flaw, but it matters to WindowsForum readers because Linux now lives inside Windows estates: WSL hosts, dual-boot workstations, developer laptops, appliances, CI runners, and cloud images. The lesson is larger than a single audio patch. Modern endpoint risk increasingly hides in the compatibility layers everyone forgot they still shipped.
On paper, CVE-2026-43126 looks almost comically narrow. It lives in
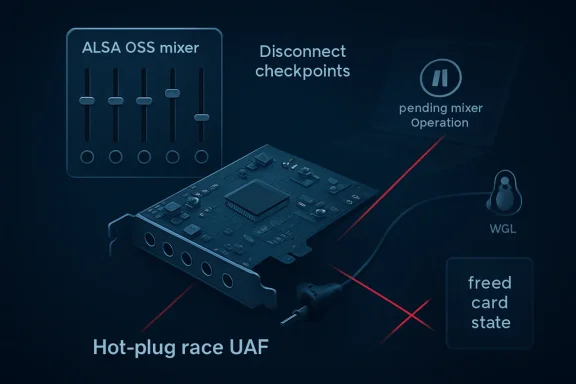
That title tells the whole story if you already speak kernel. The ALSA OSS mixer layer calls kcontrol operations one by one, and those calls can still be pending while a sound card is disconnecting. If the disconnect path wins the race and frees the relevant card state, a later mixer access may be staring at memory that is no longer owned by the object it thinks it is using.
That is the classic use-after-free shape: not a spectacular cryptographic break, not a remote wormable server hole, but a lifetime-management failure in privileged code. In the kernel, even mundane race conditions deserve respect because the boundary between “local denial of service” and “possible privilege escalation under the right heap conditions” is rarely as clean as advisory prose makes it sound.
The fix is correspondingly modest. The kernel now adds sanity checks at OSS mixer entry points to verify that the card has not already disconnected, with locking arranged so the subsequent context is covered. This is not a redesign of Linux audio. It is a guardrail added where an old compatibility interface meets hot-pluggable hardware and concurrent kernel control paths.
That is what makes this CVE interesting. The vulnerable code is not the fashionable top of the audio stack. It is the legacy bridge underneath: the layer that lets old assumptions keep working while the rest of the system evolves around them. Compatibility is a product feature, but in kernel space it is also a liability ledger.
The ALSA documentation has long noted that OSS mixer emulation is not a trivial one-to-one shim. ALSA builds mixer elements out of multiple controls, translating old OSS mixer concepts into ALSA’s richer model. That means an apparently simple legacy operation may fan out into several control operations beneath the surface.
That translation complexity matters during disconnect. A USB audio interface, docking station, virtual sound card, Bluetooth adapter, or odd embedded audio path may disappear while userspace is still probing, polling, or adjusting mixer state. If each control operation is called individually, and if teardown is happening at the same time, every unchecked entry point becomes a possible stale-reference opportunity.
The uncomfortable truth for administrators is that “we do not use OSS” is not always the same as “we do not ship the OSS compatibility code.” Kernel configuration, distribution defaults, container host images, appliance builds, and vendor kernels can keep old modules around for reasons nobody remembers until a CVE forces the inventory discussion.
The pattern is simple. Code keeps a pointer to an object. Another path frees that object. The first path later uses the pointer as if nothing happened. If an attacker can influence timing and memory reuse, the stale pointer may become a crash primitive, an information leak, or in more serious cases a route to code execution in kernel context.
CVE-2026-43126, based on the public description, is rooted in disconnect timing. The advisory language points to “potential UAF scenarios” and says pending calls may not always be caught when the device disconnects. That wording is careful, but it is also a reminder that kernel races often arrive first as theoretical-looking correctness fixes and later as security entries once the lifetime hazard is recognized.
For most systems, the realistic immediate risk is local denial of service. A user or process with access to relevant audio device interfaces could potentially trigger bad timing around mixer access and disconnect handling. On desktops and developer machines, that may mean a crash. On multi-user Linux hosts, lab systems, or shared workstations with attached audio devices, the local attack surface deserves more scrutiny.
The harder question is privilege escalation. Public advisories often avoid overpromising exploitability unless a working exploit is known, and NVD had not enriched the CVE with its own severity or vector at publication time. But defenders should avoid the opposite mistake: assuming “audio bug” means “toy bug.” Kernel memory corruption in a local interface is still kernel memory corruption.
That asymmetry is now normal. Linux kernel CVEs can surface quickly from upstream fixes, while downstream scoring, distribution advisories, vulnerability management databases, and enterprise dashboards take time to converge. A vulnerability may be real, patched, and relevant before the familiar spreadsheet fields are filled in.
This creates a practical problem for IT. Many patch processes still treat NVD scoring as the starting gun. If the score is absent, the ticket sits in a gray state: acknowledged but not prioritized, visible but not actionable. For kernel bugs, that posture is increasingly outdated.
The better signal is the upstream fix itself. Here, the kernel stable tree has patches that add disconnect checkpoints in the affected ALSA OSS mixer access paths. The description is not speculative about the code defect; it says the vulnerability has been resolved in the Linux kernel. That is enough to begin exposure assessment.
This does not mean every workstation must be rebooted in panic. It does mean the absence of an NVD score should not be confused with absence of risk. When the vulnerable component is privileged kernel code and the fix is already available, the right operational question is not “what number did the database assign?” but “where do we run kernels that include this code path, and when will they receive the patched build?”
That is not a branding curiosity. It reflects the infrastructure reality Windows admins already live in. Azure runs Linux. WSL brings Linux kernels and userlands onto Windows developer machines. Containers blur host and guest responsibilities. Security tools ingest CVE data across operating systems because adversaries do not care which team owns the asset tag.
For WindowsForum’s audience, the key point is not that Windows 11 suddenly has an ALSA bug. It does not in the ordinary desktop sense. The point is that Windows-centered organizations often operate Linux-adjacent systems without treating them as first-class patching subjects.
A developer laptop might run Windows as the primary OS, WSL for build tooling, Docker Desktop for containers, a USB audio dock, and a pile of Linux-based test images. A security dashboard may show the Windows host as compliant while missing the kernel exposure of a Linux VM, local lab box, or appliance image. CVE-2026-43126 is small enough to be manageable, but it points at that larger blind spot.
The same applies to hybrid fleets. A help desk may own Windows endpoints, a platform team may own Linux build runners, and a vendor may own the firmware or appliance kernel. The vulnerable code does not care about org charts. If the kernel includes the ALSA OSS mixer layer and exposes it to userspace in a plausible way, it belongs in the patch conversation.
Kernel code has to survive all of that while presenting stable interfaces to userspace. That is harder than it sounds. A userspace program can open a device, issue a control call, block, retry, fork, crash, or race with another process. Meanwhile, the hardware may be removed and the kernel must tear down internal state without leaving dangling references behind.
Audio is especially rich in this kind of complexity. It mixes old APIs, new APIs, physical devices, virtual devices, per-card controls, user-facing volume tools, compatibility modules, and often hardware that appears through USB. Most users experience the stack as a volume slider. Kernel developers experience it as a maze of lifetime rules.
The patch for CVE-2026-43126 uses a familiar defensive technique: check the card’s disconnected state at the points where OSS mixer operations enter the relevant control paths. The description notes that the read-write semaphore is taken just before the check, so the rest of the context should be protected. That phrase is doing important work. The bug is not that nobody knew devices disconnect; it is that the check had to be placed where the lock and the lifetime guarantee actually line up.
This is how many kernel hardening fixes look. They are not glamorous. They are careful rearrangements of checks, locks, and object ownership boundaries. But those dull-looking patches are often the difference between a race that crashes a system once a year and a race that becomes an exploit primitive.
On a single-user desktop, a local crash may be annoying rather than catastrophic. On a shared workstation, kiosk, lab machine, classroom system, or Linux host used by multiple low-privilege users, local denial of service becomes operational risk. On a developer endpoint, a local kernel exploit can be a stepping stone from a compromised user account to secrets, source code, signing material, cached credentials, or lateral movement.
The audio angle may reduce exposure on many servers because headless systems often omit sound support entirely. That is a real mitigating factor. But it should be verified, not assumed. Cloud images, generic distribution kernels, and workstation builds often include broad hardware support by default, even when a specific machine does not appear to use it.
Access control also matters. If the relevant OSS mixer device nodes are not present, not loaded, or not accessible to untrusted users, practical exploitability falls. If
That is why the right answer is inventory, not theatrics. Determine whether affected kernels are present. Determine whether the OSS mixer compatibility layer is enabled or loadable. Determine whether local users or processes can reach the interface. Then patch through the normal kernel update channel and plan the reboot that kernel fixes almost always require.
This is where Linux patch management differs from the Windows muscle memory. A fixed upstream commit does not always map cleanly to “kernel version X is safe.” Stable trees backport fixes. Enterprise distributions backport fixes without bumping to the newest upstream kernel. Appliance vendors may patch internally while preserving an old-looking version string.
For admins, the useful test is not simply
Custom kernels are the exception where commit-level checking becomes unavoidable. If your organization builds kernels for kiosks, industrial systems, VDI images, gaming rigs, audio workstations, or lab appliances, the responsibility comes home. You need to know whether
The mitigation story is similarly pragmatic. If you can update, update. If you cannot, consider disabling or blacklisting the OSS mixer module where it is not needed, tightening device permissions, and reducing untrusted local access. Those are compensating controls, not substitutes for a fixed kernel.
The answer depends on the WSL generation, kernel build, device exposure, and whether the vulnerable subsystem is present and reachable. WSL 2 uses a real Linux kernel maintained through Microsoft’s update channels, but it is not a generic bare-metal desktop kernel with every hardware path exposed in the same way. Audio support in WSL has evolved through integration layers rather than traditional direct access to arbitrary sound hardware.
That means CVE-2026-43126 should not be treated as an automatic WSL emergency. At the same time, it should not be dismissed reflexively. The right stance is to keep WSL kernels current, rely on Microsoft’s servicing path for WSL kernel updates, and avoid assuming that a Linux CVE is irrelevant merely because the host is Windows.
For developers, this is part of a broader hygiene pattern. WSL distributions, container base images, language runtimes, package managers, and local VM kernels all need maintenance. The Windows Update green checkmark is necessary, but it is no longer sufficient for a workstation that functions as a small private cloud.
The same logic applies to Docker Desktop and local Kubernetes environments. A Windows laptop may be the physical device, but the vulnerable code may live in a Linux VM or image maintained on a different cadence. The modern endpoint is a stack, not a single operating system.
The OSS mixer compatibility layer exists because software compatibility matters. Removing it would break some workloads, especially in old applications, specialist tools, embedded deployments, and environments where nobody wants to touch working audio code. Keeping it means maintaining an adapter between old userspace expectations and modern ALSA internals.
Every adapter like that becomes a place where assumptions can drift. The old interface assumes a certain model of devices and controls. The newer subsystem has its own locking, object lifetime, and disconnect semantics. Hardware hot-plug behavior changes. Userspace probes more aggressively. Test coverage improves. Eventually somebody notices that a path lacks the same disconnect checkpoint discipline as its neighbors.
That is not an indictment of ALSA specifically. It is the ordinary entropy of long-lived systems software. Windows has its own strata of compatibility code, shims, legacy drivers, and subsystems kept alive because customers depend on them. The difference is only the naming convention and the patch pipeline.
The responsible argument is not “legacy bad.” It is that legacy code deserves explicit ownership. If an interface remains compiled into privileged code, it remains part of the threat model. If a compatibility option is not needed, it should not be present by accident.
A more mature process would score exposure before debating severity adjectives. Is this a server kernel or a workstation kernel? Is sound support enabled? Is OSS mixer emulation available? Are untrusted local users present? Is the system physically accessible? Can USB or virtual audio devices be connected or disconnected? Is the machine part of a build pipeline or privileged administrative environment?
Those questions produce a more useful answer than waiting for a universal CVSS number. A headless, locked-down server with no sound modules loaded may be low priority. A multi-user Linux desktop lab with USB audio devices and delayed kernel patching deserves faster action. A developer workstation holding production credentials sits somewhere uncomfortable in between.
Vulnerability management also needs to understand kernel reboot debt. Linux kernel patches frequently require a reboot to take effect unless live-patching is available and covers the specific fix. Organizations that install updates but defer reboots indefinitely are not patched in the way their dashboards imply.
The best-run fleets treat kernel exposure as a lifecycle issue. They maintain kernel versions, schedule reboots, validate module configuration, and avoid shipping broad compatibility features where a smaller kernel profile will do. CVE-2026-43126 is a reminder that even the mixer device can become a governance problem when nobody owns the old code path.
CVE-2026-43126 should be handled as a Linux kernel maintenance item with a narrow but real local attack surface. If your environment has no Linux systems, no WSL, no Linux-based appliances, and no container hosts, this CVE is probably not your problem. Very few serious organizations can honestly say all of that.
For everyone else, the work is straightforward. Track distribution advisories. Update affected kernels. Reboot into the fixed kernel. Remove or disable OSS mixer compatibility where it is not needed. Check vendor appliances and custom images rather than assuming they inherit the patch automatically.
There is also a communication lesson. Users may see “ALSA,” “OSS,” and “mixer” and assume this is about whether their speakers work. IT should explain that the concern is not audio quality, volume controls, or PipeWire policy. The concern is a kernel race in a legacy control interface that could produce use-after-free behavior during device disconnect.
That distinction matters because good security communication reduces both panic and apathy. This is not the next internet-wide emergency. It is also not meaningless. It is the sort of vulnerability that becomes manageable when treated promptly and messy when buried under “awaiting enrichment.”
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Sound Bug Becomes a Systems Management Story
A Sound Bug Becomes a Systems Management Story
On paper, CVE-2026-43126 looks almost comically narrow. It lives in sound/core/oss/mixer_oss.c, a corner of the Linux kernel that exists to make ALSA present an old Open Sound System-style mixer interface to programs that still expect /dev/mixer semantics. The patch title is plain: “ALSA: mixer: oss: Add card disconnect checkpoints.”That title tells the whole story if you already speak kernel. The ALSA OSS mixer layer calls kcontrol operations one by one, and those calls can still be pending while a sound card is disconnecting. If the disconnect path wins the race and frees the relevant card state, a later mixer access may be staring at memory that is no longer owned by the object it thinks it is using.
That is the classic use-after-free shape: not a spectacular cryptographic break, not a remote wormable server hole, but a lifetime-management failure in privileged code. In the kernel, even mundane race conditions deserve respect because the boundary between “local denial of service” and “possible privilege escalation under the right heap conditions” is rarely as clean as advisory prose makes it sound.
The fix is correspondingly modest. The kernel now adds sanity checks at OSS mixer entry points to verify that the card has not already disconnected, with locking arranged so the subsequent context is covered. This is not a redesign of Linux audio. It is a guardrail added where an old compatibility interface meets hot-pluggable hardware and concurrent kernel control paths.
The Old OSS Compatibility Layer Is Still Part of the Attack Surface
The Open Sound System era is long behind mainstream Linux desktops. ALSA replaced OSS as the default kernel sound architecture years ago, and today many users think in terms of PulseAudio, PipeWire, JACK, or desktop volume panels rather than raw mixer ioctls. But the kernel’s compatibility layers do not vanish just because the industry’s mental model has moved on.That is what makes this CVE interesting. The vulnerable code is not the fashionable top of the audio stack. It is the legacy bridge underneath: the layer that lets old assumptions keep working while the rest of the system evolves around them. Compatibility is a product feature, but in kernel space it is also a liability ledger.
The ALSA documentation has long noted that OSS mixer emulation is not a trivial one-to-one shim. ALSA builds mixer elements out of multiple controls, translating old OSS mixer concepts into ALSA’s richer model. That means an apparently simple legacy operation may fan out into several control operations beneath the surface.
That translation complexity matters during disconnect. A USB audio interface, docking station, virtual sound card, Bluetooth adapter, or odd embedded audio path may disappear while userspace is still probing, polling, or adjusting mixer state. If each control operation is called individually, and if teardown is happening at the same time, every unchecked entry point becomes a possible stale-reference opportunity.
The uncomfortable truth for administrators is that “we do not use OSS” is not always the same as “we do not ship the OSS compatibility code.” Kernel configuration, distribution defaults, container host images, appliance builds, and vendor kernels can keep old modules around for reasons nobody remembers until a CVE forces the inventory discussion.
Use-After-Free Bugs Are Where Boring Code Gets Dangerous
Use-after-free vulnerabilities have a reputation problem. They are often described in dry memory-safety language that makes them sound less urgent than remote code execution flaws with marketing names. Yet many of the most serious kernel exploitation chains over the last decade have leaned on exactly this class of bug.The pattern is simple. Code keeps a pointer to an object. Another path frees that object. The first path later uses the pointer as if nothing happened. If an attacker can influence timing and memory reuse, the stale pointer may become a crash primitive, an information leak, or in more serious cases a route to code execution in kernel context.
CVE-2026-43126, based on the public description, is rooted in disconnect timing. The advisory language points to “potential UAF scenarios” and says pending calls may not always be caught when the device disconnects. That wording is careful, but it is also a reminder that kernel races often arrive first as theoretical-looking correctness fixes and later as security entries once the lifetime hazard is recognized.
For most systems, the realistic immediate risk is local denial of service. A user or process with access to relevant audio device interfaces could potentially trigger bad timing around mixer access and disconnect handling. On desktops and developer machines, that may mean a crash. On multi-user Linux hosts, lab systems, or shared workstations with attached audio devices, the local attack surface deserves more scrutiny.
The harder question is privilege escalation. Public advisories often avoid overpromising exploitability unless a working exploit is known, and NVD had not enriched the CVE with its own severity or vector at publication time. But defenders should avoid the opposite mistake: assuming “audio bug” means “toy bug.” Kernel memory corruption in a local interface is still kernel memory corruption.
The NVD Delay Is Not a Reason to Delay Patching
One of the first things security teams will notice is that the NVD record is marked as awaiting enrichment. At publication, NVD had not provided CVSS 4.0, CVSS 3.x, or CVSS 2.0 scoring of its own. The CVE came from kernel.org, with stable commit references already available.That asymmetry is now normal. Linux kernel CVEs can surface quickly from upstream fixes, while downstream scoring, distribution advisories, vulnerability management databases, and enterprise dashboards take time to converge. A vulnerability may be real, patched, and relevant before the familiar spreadsheet fields are filled in.
This creates a practical problem for IT. Many patch processes still treat NVD scoring as the starting gun. If the score is absent, the ticket sits in a gray state: acknowledged but not prioritized, visible but not actionable. For kernel bugs, that posture is increasingly outdated.
The better signal is the upstream fix itself. Here, the kernel stable tree has patches that add disconnect checkpoints in the affected ALSA OSS mixer access paths. The description is not speculative about the code defect; it says the vulnerability has been resolved in the Linux kernel. That is enough to begin exposure assessment.
This does not mean every workstation must be rebooted in panic. It does mean the absence of an NVD score should not be confused with absence of risk. When the vulnerable component is privileged kernel code and the fix is already available, the right operational question is not “what number did the database assign?” but “where do we run kernels that include this code path, and when will they receive the patched build?”
Microsoft’s Presence in the Record Reflects the New Mixed Estate
The MSRC page for CVE-2026-43126 may surprise readers who still divide the world cleanly into Windows vulnerabilities and Linux vulnerabilities. Microsoft’s security ecosystem now tracks more than the classic Windows Patch Tuesday universe. The company documents vulnerabilities affecting components that matter to its customers, including open-source software used in Microsoft products, services, platforms, or customer environments.That is not a branding curiosity. It reflects the infrastructure reality Windows admins already live in. Azure runs Linux. WSL brings Linux kernels and userlands onto Windows developer machines. Containers blur host and guest responsibilities. Security tools ingest CVE data across operating systems because adversaries do not care which team owns the asset tag.
For WindowsForum’s audience, the key point is not that Windows 11 suddenly has an ALSA bug. It does not in the ordinary desktop sense. The point is that Windows-centered organizations often operate Linux-adjacent systems without treating them as first-class patching subjects.
A developer laptop might run Windows as the primary OS, WSL for build tooling, Docker Desktop for containers, a USB audio dock, and a pile of Linux-based test images. A security dashboard may show the Windows host as compliant while missing the kernel exposure of a Linux VM, local lab box, or appliance image. CVE-2026-43126 is small enough to be manageable, but it points at that larger blind spot.
The same applies to hybrid fleets. A help desk may own Windows endpoints, a platform team may own Linux build runners, and a vendor may own the firmware or appliance kernel. The vulnerable code does not care about org charts. If the kernel includes the ALSA OSS mixer layer and exposes it to userspace in a plausible way, it belongs in the patch conversation.
Hot-Plug Hardware Keeps Finding Race Conditions
Disconnect bugs are a recurring theme because modern systems are built around disappearance. Devices vanish. USB cables move. Docks sleep. Thunderbolt chains reset. Bluetooth paths flap. Virtual devices are created and destroyed by containers, hypervisors, test harnesses, and audio servers.Kernel code has to survive all of that while presenting stable interfaces to userspace. That is harder than it sounds. A userspace program can open a device, issue a control call, block, retry, fork, crash, or race with another process. Meanwhile, the hardware may be removed and the kernel must tear down internal state without leaving dangling references behind.
Audio is especially rich in this kind of complexity. It mixes old APIs, new APIs, physical devices, virtual devices, per-card controls, user-facing volume tools, compatibility modules, and often hardware that appears through USB. Most users experience the stack as a volume slider. Kernel developers experience it as a maze of lifetime rules.
The patch for CVE-2026-43126 uses a familiar defensive technique: check the card’s disconnected state at the points where OSS mixer operations enter the relevant control paths. The description notes that the read-write semaphore is taken just before the check, so the rest of the context should be protected. That phrase is doing important work. The bug is not that nobody knew devices disconnect; it is that the check had to be placed where the lock and the lifetime guarantee actually line up.
This is how many kernel hardening fixes look. They are not glamorous. They are careful rearrangements of checks, locks, and object ownership boundaries. But those dull-looking patches are often the difference between a race that crashes a system once a year and a race that becomes an exploit primitive.
The Risk Is Local, But Local Does Not Mean Harmless
Security triage tends to overvalue network reachability. Remote unauthenticated bugs are obviously urgent, and they deserve that urgency. But local kernel bugs sit in a different threat model, not a harmless one.On a single-user desktop, a local crash may be annoying rather than catastrophic. On a shared workstation, kiosk, lab machine, classroom system, or Linux host used by multiple low-privilege users, local denial of service becomes operational risk. On a developer endpoint, a local kernel exploit can be a stepping stone from a compromised user account to secrets, source code, signing material, cached credentials, or lateral movement.
The audio angle may reduce exposure on many servers because headless systems often omit sound support entirely. That is a real mitigating factor. But it should be verified, not assumed. Cloud images, generic distribution kernels, and workstation builds often include broad hardware support by default, even when a specific machine does not appear to use it.
Access control also matters. If the relevant OSS mixer device nodes are not present, not loaded, or not accessible to untrusted users, practical exploitability falls. If
snd_mixer_oss is built as a module and never loaded, exposure may be lower. If the kernel has the code built in and the system provides legacy mixer interfaces to userspace, the risk picture changes.That is why the right answer is inventory, not theatrics. Determine whether affected kernels are present. Determine whether the OSS mixer compatibility layer is enabled or loadable. Determine whether local users or processes can reach the interface. Then patch through the normal kernel update channel and plan the reboot that kernel fixes almost always require.
Distribution Patching Will Matter More Than Commit Hashes
The CVE references upstream stable commits, but most administrators should not be hand-applying kernel patches from git. The operational unit is the distribution kernel package: Ubuntu, Debian, Fedora, Red Hat Enterprise Linux, SUSE, Arch, Alpine, Oracle, Amazon Linux, vendor appliances, Android-derived builds, or custom embedded kernels. Each will make its own decision about backporting, version strings, and advisory language.This is where Linux patch management differs from the Windows muscle memory. A fixed upstream commit does not always map cleanly to “kernel version X is safe.” Stable trees backport fixes. Enterprise distributions backport fixes without bumping to the newest upstream kernel. Appliance vendors may patch internally while preserving an old-looking version string.
For admins, the useful test is not simply
uname -r in isolation. It is whether the distribution’s kernel changelog or security advisory includes the ALSA OSS mixer disconnect checkpoint fix for CVE-2026-43126 or its upstream commit lineage. In enterprise environments, vulnerability scanners should be tuned to understand vendor backports rather than blindly flagging based on major kernel version.Custom kernels are the exception where commit-level checking becomes unavoidable. If your organization builds kernels for kiosks, industrial systems, VDI images, gaming rigs, audio workstations, or lab appliances, the responsibility comes home. You need to know whether
CONFIG_SND_MIXER_OSS is enabled and whether the relevant patch has landed in your maintained branch.The mitigation story is similarly pragmatic. If you can update, update. If you cannot, consider disabling or blacklisting the OSS mixer module where it is not needed, tightening device permissions, and reducing untrusted local access. Those are compensating controls, not substitutes for a fixed kernel.
WSL Changes the Conversation, But Not in the Simplest Way
Whenever a Linux kernel CVE appears on a Windows-centered site, WSL inevitably enters the room. The question is reasonable: if Windows users run Linux through Windows Subsystem for Linux, are they affected by a Linux kernel ALSA vulnerability?The answer depends on the WSL generation, kernel build, device exposure, and whether the vulnerable subsystem is present and reachable. WSL 2 uses a real Linux kernel maintained through Microsoft’s update channels, but it is not a generic bare-metal desktop kernel with every hardware path exposed in the same way. Audio support in WSL has evolved through integration layers rather than traditional direct access to arbitrary sound hardware.
That means CVE-2026-43126 should not be treated as an automatic WSL emergency. At the same time, it should not be dismissed reflexively. The right stance is to keep WSL kernels current, rely on Microsoft’s servicing path for WSL kernel updates, and avoid assuming that a Linux CVE is irrelevant merely because the host is Windows.
For developers, this is part of a broader hygiene pattern. WSL distributions, container base images, language runtimes, package managers, and local VM kernels all need maintenance. The Windows Update green checkmark is necessary, but it is no longer sufficient for a workstation that functions as a small private cloud.
The same logic applies to Docker Desktop and local Kubernetes environments. A Windows laptop may be the physical device, but the vulnerable code may live in a Linux VM or image maintained on a different cadence. The modern endpoint is a stack, not a single operating system.
The Patch Is Small Because the Design Debt Is Large
It is tempting to see a patch like this and ask why the checks were not always there. That is emotionally satisfying and technically lazy. Kernel subsystems evolve over decades, often carrying compatibility behavior from hardware eras that predate the people now debugging them.The OSS mixer compatibility layer exists because software compatibility matters. Removing it would break some workloads, especially in old applications, specialist tools, embedded deployments, and environments where nobody wants to touch working audio code. Keeping it means maintaining an adapter between old userspace expectations and modern ALSA internals.
Every adapter like that becomes a place where assumptions can drift. The old interface assumes a certain model of devices and controls. The newer subsystem has its own locking, object lifetime, and disconnect semantics. Hardware hot-plug behavior changes. Userspace probes more aggressively. Test coverage improves. Eventually somebody notices that a path lacks the same disconnect checkpoint discipline as its neighbors.
That is not an indictment of ALSA specifically. It is the ordinary entropy of long-lived systems software. Windows has its own strata of compatibility code, shims, legacy drivers, and subsystems kept alive because customers depend on them. The difference is only the naming convention and the patch pipeline.
The responsible argument is not “legacy bad.” It is that legacy code deserves explicit ownership. If an interface remains compiled into privileged code, it remains part of the threat model. If a compatibility option is not needed, it should not be present by accident.
Security Teams Need Better Audio for Their Kernel Alerts
One reason bugs like CVE-2026-43126 get mishandled is that they fall between mental categories. Audio sounds like a desktop feature. OSS sounds obsolete. ALSA sounds like Linux trivia. Kernel UAF sounds serious. The resulting ticket can bounce between teams until the patch lands by routine update or gets ignored as low relevance.A more mature process would score exposure before debating severity adjectives. Is this a server kernel or a workstation kernel? Is sound support enabled? Is OSS mixer emulation available? Are untrusted local users present? Is the system physically accessible? Can USB or virtual audio devices be connected or disconnected? Is the machine part of a build pipeline or privileged administrative environment?
Those questions produce a more useful answer than waiting for a universal CVSS number. A headless, locked-down server with no sound modules loaded may be low priority. A multi-user Linux desktop lab with USB audio devices and delayed kernel patching deserves faster action. A developer workstation holding production credentials sits somewhere uncomfortable in between.
Vulnerability management also needs to understand kernel reboot debt. Linux kernel patches frequently require a reboot to take effect unless live-patching is available and covers the specific fix. Organizations that install updates but defer reboots indefinitely are not patched in the way their dashboards imply.
The best-run fleets treat kernel exposure as a lifecycle issue. They maintain kernel versions, schedule reboots, validate module configuration, and avoid shipping broad compatibility features where a smaller kernel profile will do. CVE-2026-43126 is a reminder that even the mixer device can become a governance problem when nobody owns the old code path.
The Practical Reading for WindowsForum Readers
The Windows angle here is not panic; it is perimeter collapse. A Windows professional in 2026 is often responsible for systems that are only partly Windows. The developer desktop, the build server, the security appliance, the Linux VM under a Windows tool, and the Azure workload all belong to the same operational reality.CVE-2026-43126 should be handled as a Linux kernel maintenance item with a narrow but real local attack surface. If your environment has no Linux systems, no WSL, no Linux-based appliances, and no container hosts, this CVE is probably not your problem. Very few serious organizations can honestly say all of that.
For everyone else, the work is straightforward. Track distribution advisories. Update affected kernels. Reboot into the fixed kernel. Remove or disable OSS mixer compatibility where it is not needed. Check vendor appliances and custom images rather than assuming they inherit the patch automatically.
There is also a communication lesson. Users may see “ALSA,” “OSS,” and “mixer” and assume this is about whether their speakers work. IT should explain that the concern is not audio quality, volume controls, or PipeWire policy. The concern is a kernel race in a legacy control interface that could produce use-after-free behavior during device disconnect.
That distinction matters because good security communication reduces both panic and apathy. This is not the next internet-wide emergency. It is also not meaningless. It is the sort of vulnerability that becomes manageable when treated promptly and messy when buried under “awaiting enrichment.”
The Five Checks That Turn This CVE From Noise Into Work
For most organizations, CVE-2026-43126 belongs in the next kernel patch cycle, with faster handling for exposed multi-user or developer systems. The useful response is not dramatic; it is disciplined.- Confirm which Linux kernels in your estate include ALSA OSS mixer support, especially workstation, lab, appliance, and custom kernel builds.
- Check your distribution or vendor advisory rather than relying only on upstream version numbers, because many vendors backport kernel fixes.
- Prioritize systems where untrusted local users, hot-pluggable audio devices, USB docks, or developer secrets make a local kernel bug more consequential.
- Keep WSL and Linux VM kernels current, even if the Windows host itself is fully patched.
- Disable or avoid loading OSS mixer compatibility where no workload actually needs legacy
/dev/mixerbehavior. - Do not treat missing NVD enrichment as missing risk when the upstream kernel has already accepted a security-relevant fix.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center