Microsoft’s CVE-2026-32191 entry for Microsoft Bing Images Remote Code Execution is the sort of advisory that immediately commands attention because it combines three elements security teams dislike most: a recognizable Microsoft surface, a browser-facing image workflow, and an RCE classification. Just as importantly, the Microsoft Security Response Center uses its update guide to publish CVE records as an authoritative disclosure channel, which means the record itself is meant to be the first stop for defenders assessing credibility and urgency. In practical terms, this vulnerability matters not only because of what it could allow, but because image-driven attack paths have historically been a reliable bridge from simple content viewing to code execution when parsing logic goes wrong. Microsoft’s broader Bing transparency reporting also confirms that Bing’s visual features process uploaded and queried images, underscoring why image-related bugs in that stack warrant close scrutiny.
The first thing to understand about CVE-2026-32191 is that Microsoft’s security ecosystem now treats CVEs in cloud and service contexts as serious disclosure events even when remediation is fully handled on Microsoft’s side. That transparency shift is important because Bing is not a traditional desktop app; it is a live service with client-facing features, server-side logic, and a constantly changing pipeline. Microsoft’s own MSRC guidance explains that the Security Update Guide is the canonical place where these CVE records are surfaced, and that cloud service CVEs are now disclosed more openly than they were in the past.
That policy shift matters because it changes how defenders should interpret severity. A Bing-related RCE does not necessarily imply a single vulnerable EXE sitting on an endpoint, but it does imply that a service path has been identified where attacker-controlled input can cross a trust boundary and influence execution behavior. In cloud-era Microsoft security disclosures, that is exactly the kind of vulnerability the company wants customers and partners to see early, even when the fix may be fully service-side.
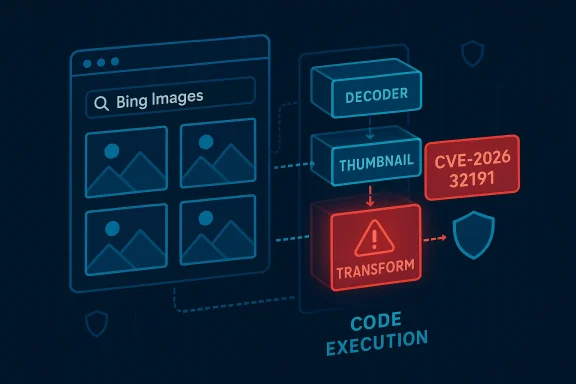
The broader history here is also hard to ignore. Microsoft image-handling vulnerabilities have long been a recurring theme, from old Windows Metafile and graphics rendering flaws to more recent image-codec issues in Windows components. Those bugs taught the industry a lasting lesson: image parsing is rarely “just display logic.” It is often a chain of decoders, transforms, thumbnailers, caches, and rendering helpers that can be reached from multiple surfaces, including web services, apps, and background tasks.
That historical pattern is why a Bing Images RCE should be read as more than a single isolated bug. It is a reminder that search-as-a-service is now inseparable from media-processing logic, preview logic, and machine-generated transformations. If one part of that chain is exploitable, the impact can extend well beyond a simple bad image preview.
Bing Images is especially interesting because image-related operations in the Bing ecosystem are not limited to static web pages. Microsoft’s transparency documents show that Bing supports image upload and visual search workflows, and that its image-handling features operate across consumer and service contexts. That means the relevant attack surface is not just “a webpage that renders pictures,” but a layered image pipeline with content analysis, storage, retrieval, and in some cases AI-assisted interactions.
In Microsoft’s ecosystem, history has repeatedly shown that image-related flaws can affect both endpoints and services. The line between client-side rendering and server-side handling is often thin, especially when thumbnails, previews, or transformation services are involved. If Bing Images participates in any such chain, the security implications are broader than a single page load. (cyberpress.org)
At the same time, the MSRC ecosystem distinguishes between CVEs and broader advisories. Microsoft notes that some security issues may not qualify for a CVE and instead appear in the Security Advisory tab, while the update guide continues to serve as the unified location for both vulnerabilities and related security information. That distinction matters because it means a CVE title typically reflects a real, scoped technical problem, not just a generic concern.
The wording also implies a meaningful confidence level. Microsoft generally reserves CVE publication for vulnerabilities it is willing to track and remediate formally, which usually means the underlying issue has enough substance to justify a numbered entry. That does not tell us the exploit quality is high, but it does tell us the claim is not merely speculative.
If the vulnerability indeed lives in a rendering or processing path, then the likely risk centers on how Bing normalizes image inputs, generates previews, or handles downstream transformations. Image services often do this work at scale and under tight latency constraints, which can encourage aggressive optimization. Those optimizations are precisely where memory-safety mistakes and boundary errors can hide.
Key areas to scrutinize include:
Microsoft’s recent Windows imaging disclosures show how subtle those bugs can be. In one case, researchers found that exploitation depended on specific processing behavior rather than ordinary viewing, and that multiple preconditions made real-world abuse harder than a headline might suggest. The lesson is that an RCE label does not always mean trivial exploitation, but it always means the bug deserves urgent attention. (cyberpress.org)
That broad reach is why attackers care about Microsoft web services. A service-side vulnerability can yield scale, persistence, and access patterns unavailable in a one-off endpoint exploit. It can also be patched centrally, which is good for defenders but attractive to attackers during the window between disclosure and remediation.
That distinction matters because enterprise defenders must think about shared services and downstream trust. Even if the exploit lands in Microsoft’s infrastructure rather than on an endpoint, a compromise of backend processing can still create data exposure, integrity risks, or weaponized content delivery. Service-side does not mean impact-side is small.
More recent Windows imaging advisories reinforce the same pattern. Microsoft has continued to patch graphics-component issues where crafted images could cause code execution under specific conditions, and independent writeups have stressed that exploitation may require more than simply opening a file. The common thread is that image pipelines are complex, and complexity breeds security risk. (cyberpress.org)
The result is a more complicated threat model. A Bing Images flaw could affect different layers depending on where the bug sits, and the remediation strategy may require both service fixes and broader hardening in the media pipeline. This is where modern cloud vulnerability management becomes especially important.
What we cannot confirm from the public metadata alone is the exact root cause, exploit path, or whether the issue requires user interaction, backend processing, or special content conditions. In other words, the CVE title tells us the category, but not the full anatomy. That is normal early in a disclosure cycle, and it is why caution is warranted when attributing technical specifics.
From an attacker’s perspective, the publication of an RCE-class Bing Images CVE signals that Microsoft has identified a credible path worth fixing. From a defender’s perspective, it signals that image-related inputs and processing should be treated as high-risk until more is known. That is enough to justify immediate attention even without a full exploit narrative.
The Bing Images issue also creates an opportunity for deeper hardening across image pipelines, which are often shared among search, AI, and content delivery systems. If Microsoft uses the incident to reinforce parser isolation, validation layers, and sandboxing, the benefit could extend beyond this single CVE. That is the best outcome defenders can hope for from a bug class like this.
Another concern is that Bing’s image workflows may intersect with other Microsoft services in ways the public does not fully see. If a vulnerability is reachable through a shared backend or transformation service, the exposure could be broader than a single consumer-facing feature suggests. That makes dependency mapping as important as patching.
It will also matter whether third-party security researchers publish independent analysis that corroborates the cause or exploitation model. In modern vulnerability handling, external validation often determines whether a bug remains a narrow service issue or becomes part of a broader class of image-processing risk. The more concrete the technical details become, the more urgent the defensive response will be. (cyberpress.org)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
The first thing to understand about CVE-2026-32191 is that Microsoft’s security ecosystem now treats CVEs in cloud and service contexts as serious disclosure events even when remediation is fully handled on Microsoft’s side. That transparency shift is important because Bing is not a traditional desktop app; it is a live service with client-facing features, server-side logic, and a constantly changing pipeline. Microsoft’s own MSRC guidance explains that the Security Update Guide is the canonical place where these CVE records are surfaced, and that cloud service CVEs are now disclosed more openly than they were in the past.That policy shift matters because it changes how defenders should interpret severity. A Bing-related RCE does not necessarily imply a single vulnerable EXE sitting on an endpoint, but it does imply that a service path has been identified where attacker-controlled input can cross a trust boundary and influence execution behavior. In cloud-era Microsoft security disclosures, that is exactly the kind of vulnerability the company wants customers and partners to see early, even when the fix may be fully service-side.
The broader history here is also hard to ignore. Microsoft image-handling vulnerabilities have long been a recurring theme, from old Windows Metafile and graphics rendering flaws to more recent image-codec issues in Windows components. Those bugs taught the industry a lasting lesson: image parsing is rarely “just display logic.” It is often a chain of decoders, transforms, thumbnailers, caches, and rendering helpers that can be reached from multiple surfaces, including web services, apps, and background tasks.
That historical pattern is why a Bing Images RCE should be read as more than a single isolated bug. It is a reminder that search-as-a-service is now inseparable from media-processing logic, preview logic, and machine-generated transformations. If one part of that chain is exploitable, the impact can extend well beyond a simple bad image preview.
Why This Vulnerability Class Matters
Remote code execution vulnerabilities in image workflows are uniquely dangerous because they often promise a deceptively simple delivery mechanism. An attacker does not need a USB stick, a phishing macro, or a local foothold if a crafted image can cross a parser boundary and trigger memory corruption or a logic flaw. The attack story becomes even more potent when the vulnerable code sits in a service that already touches untrusted user-generated media.Bing Images is especially interesting because image-related operations in the Bing ecosystem are not limited to static web pages. Microsoft’s transparency documents show that Bing supports image upload and visual search workflows, and that its image-handling features operate across consumer and service contexts. That means the relevant attack surface is not just “a webpage that renders pictures,” but a layered image pipeline with content analysis, storage, retrieval, and in some cases AI-assisted interactions.
The significance of image parsing
Image parsing bugs matter because they tend to be reachable, repeatable, and hard to spot during normal use. A user can do everything “right” from their perspective and still trigger unsafe processing if the service accepts an image that looks benign on the surface. That is why image vulnerabilities often earn outsized attention: they can be weaponized in ways that are quiet, scalable, and hard to attribute immediately.In Microsoft’s ecosystem, history has repeatedly shown that image-related flaws can affect both endpoints and services. The line between client-side rendering and server-side handling is often thin, especially when thumbnails, previews, or transformation services are involved. If Bing Images participates in any such chain, the security implications are broader than a single page load. (cyberpress.org)
What Microsoft’s Disclosure Model Tells Us
Microsoft’s current disclosure model is important because it helps us infer what the company believes about a given issue’s credibility. MSRC states that CVEs are its standardized way of publishing vulnerability information, and that cloud service CVEs are now surfaced to improve transparency even when customers may not need to patch locally. That tells defenders that a published Bing CVE is not a rumor; it is a formal signal from Microsoft’s security organization.At the same time, the MSRC ecosystem distinguishes between CVEs and broader advisories. Microsoft notes that some security issues may not qualify for a CVE and instead appear in the Security Advisory tab, while the update guide continues to serve as the unified location for both vulnerabilities and related security information. That distinction matters because it means a CVE title typically reflects a real, scoped technical problem, not just a generic concern.
Why the title matters
The title Microsoft Bing Images Remote Code Execution Vulnerability suggests that Microsoft believes the issue is tied specifically to image-related functionality rather than Bing overall. That is a significant narrowing of the threat surface. It points defenders toward media ingestion, media rendering, or media transformation logic instead of search ranking or authentication.The wording also implies a meaningful confidence level. Microsoft generally reserves CVE publication for vulnerabilities it is willing to track and remediate formally, which usually means the underlying issue has enough substance to justify a numbered entry. That does not tell us the exploit quality is high, but it does tell us the claim is not merely speculative.
Attack Surface in Bing Images
Bing Images sits at the intersection of search, visual discovery, and media handling. Microsoft’s Bing transparency reports show that Bing supports image queries, visual search, and image upload pathways, which means images can be processed in multiple ways before a user ever sees a result. In security terms, that creates several possible choke points where malformed or specially crafted media can cause trouble.If the vulnerability indeed lives in a rendering or processing path, then the likely risk centers on how Bing normalizes image inputs, generates previews, or handles downstream transformations. Image services often do this work at scale and under tight latency constraints, which can encourage aggressive optimization. Those optimizations are precisely where memory-safety mistakes and boundary errors can hide.
Potential entry points
Defenders should think in terms of entry points, not just products. The relevant path might be an upload flow, a thumbnail generation service, a preview endpoint, a visual search pipeline, or an image recomposition process. Any one of these could become the trigger if an attacker can cause the service to parse content in an unexpected state.Key areas to scrutinize include:
- Image upload validation
- Preview and thumbnail generation
- Re-encoding or transcoding
- Metadata extraction
- Visual search preprocessing
- AI-assisted image handling
- Cross-service content reuse
How RCE Usually Emerges in Image Pipelines
Remote code execution in image pipelines usually appears when a parser makes an unsafe assumption about structure, size, type, or state. The exploit may involve out-of-bounds memory access, type confusion, a use-after-free condition, an uninitialized pointer, or a logic path that hands control to attacker-influenced data. Once the wrong primitive exists, the rest becomes a race against modern mitigations. (cyberpress.org)Microsoft’s recent Windows imaging disclosures show how subtle those bugs can be. In one case, researchers found that exploitation depended on specific processing behavior rather than ordinary viewing, and that multiple preconditions made real-world abuse harder than a headline might suggest. The lesson is that an RCE label does not always mean trivial exploitation, but it always means the bug deserves urgent attention. (cyberpress.org)
From parser bug to code execution
The technical path from malformed image to code execution usually unfolds in stages:- The service accepts or fetches the image.
- A decoder, transformer, or thumbnailer processes it.
- Memory corruption or unsafe control flow occurs.
- An attacker uses auxiliary primitives to stabilize execution.
- Code execution becomes possible, often with service-level privileges. (cyberpress.org)
Why Bing Is a Valuable Target
Bing is not merely a consumer search box. It is part of Microsoft’s broader web, cloud, advertising, and AI ecosystem, which means a compromise in one image-related surface may have wide blast radius depending on where the vulnerable code runs. Bing’s visual features are also tightly connected to Microsoft’s larger product portfolio, including Copilot-facing experiences and image-driven discovery.That broad reach is why attackers care about Microsoft web services. A service-side vulnerability can yield scale, persistence, and access patterns unavailable in a one-off endpoint exploit. It can also be patched centrally, which is good for defenders but attractive to attackers during the window between disclosure and remediation.
Consumer versus enterprise impact
For consumers, the risk is often easiest to imagine as malicious content exposure, unsafe image processing, or secondary compromise through a service connected to a personal Microsoft account. For enterprises, the concern is broader because Bing-integrated workflows can intersect with managed identities, content moderation pipelines, browser sessions, and productivity tools. The enterprise impact is frequently indirect but amplified.That distinction matters because enterprise defenders must think about shared services and downstream trust. Even if the exploit lands in Microsoft’s infrastructure rather than on an endpoint, a compromise of backend processing can still create data exposure, integrity risks, or weaponized content delivery. Service-side does not mean impact-side is small.
Historical Context: Microsoft and Image-Based RCE
Microsoft has lived through this movie before. Two decades ago, the Windows Metafile vulnerability demonstrated how an image format could become an execution vector when rendering logic mishandled crafted content. That history still shapes how security teams interpret image-processing advisories today.More recent Windows imaging advisories reinforce the same pattern. Microsoft has continued to patch graphics-component issues where crafted images could cause code execution under specific conditions, and independent writeups have stressed that exploitation may require more than simply opening a file. The common thread is that image pipelines are complex, and complexity breeds security risk. (cyberpress.org)
Why this matters in 2026
In 2026, image handling is no longer just about rendering pixels. It touches thumbnails, previews, search indexing, AI analysis, content safety, and cloud-side transformations. That means each new vulnerability should be read against a much larger operational backdrop than the classic “open image, get pwned” story from older Windows bugs.The result is a more complicated threat model. A Bing Images flaw could affect different layers depending on where the bug sits, and the remediation strategy may require both service fixes and broader hardening in the media pipeline. This is where modern cloud vulnerability management becomes especially important.
What We Can and Cannot Confirm
What we can confirm is that Microsoft has a formal CVE entry for CVE-2026-32191 tied to Microsoft Bing Images Remote Code Execution Vulnerability, and Microsoft’s own disclosure framework indicates that such entries represent real, tracked security issues. We can also confirm that Bing supports image-centric workflows and that image-processing bugs have a long history of producing high-impact exploitation opportunities.What we cannot confirm from the public metadata alone is the exact root cause, exploit path, or whether the issue requires user interaction, backend processing, or special content conditions. In other words, the CVE title tells us the category, but not the full anatomy. That is normal early in a disclosure cycle, and it is why caution is warranted when attributing technical specifics.
Confidence assessment
The confidence in the existence of the vulnerability should be considered high because Microsoft itself is publishing the CVE through its update guide. The confidence in the exact attack mechanics should be treated as moderate until additional technical detail appears. That distinction is crucial for defenders who need to prioritize without overfitting to rumor.From an attacker’s perspective, the publication of an RCE-class Bing Images CVE signals that Microsoft has identified a credible path worth fixing. From a defender’s perspective, it signals that image-related inputs and processing should be treated as high-risk until more is known. That is enough to justify immediate attention even without a full exploit narrative.
Strengths and Opportunities
Microsoft’s handling of modern CVEs gives defenders something valuable: a formal disclosure channel that is increasingly transparent about cloud and service issues. For security teams, that reduces ambiguity and helps accelerate triage, patch validation, and communication. It also gives organizations a cleaner way to track exposure across Microsoft services.The Bing Images issue also creates an opportunity for deeper hardening across image pipelines, which are often shared among search, AI, and content delivery systems. If Microsoft uses the incident to reinforce parser isolation, validation layers, and sandboxing, the benefit could extend beyond this single CVE. That is the best outcome defenders can hope for from a bug class like this.
- Clearer MSRC disclosure channels improve incident response.
- Centralized service patching can reduce enterprise remediation burden.
- Image pipeline hardening may protect multiple Microsoft products at once.
- Security review of Bing visual features can reduce future attack surface.
- Better transparency helps defenders separate confirmed risk from speculation.
- Service-side remediation can limit endpoint deployment churn.
- Cross-team lessons can improve the safety of AI and search media workflows.
Risks and Concerns
The biggest concern is that image-related service vulnerabilities can be easy to underestimate because they are visually ordinary. Users think in terms of pictures, previews, and search results, while attackers think in terms of parsers, memory states, and trust boundaries. That mismatch is what makes these bugs persistently dangerous.Another concern is that Bing’s image workflows may intersect with other Microsoft services in ways the public does not fully see. If a vulnerability is reachable through a shared backend or transformation service, the exposure could be broader than a single consumer-facing feature suggests. That makes dependency mapping as important as patching.
- Unknown exploitability conditions can delay precise risk scoring.
- Shared backend components may widen the blast radius.
- Image-processing complexity increases regression risk after fixes.
- AI-adjacent workflows may introduce new preprocessing paths.
- Service-side compromise can affect many users at once.
- False assumptions about “just a web feature” can weaken response urgency.
- Patch opacity can make validation harder for enterprise defenders.
Looking Ahead
The next important development will be whether Microsoft adds more technical detail to the CVE record or expands the advisory through MSRC’s broader transparency channels. If the company clarifies the affected path, defenders will be able to determine whether the risk sits in upload handling, preview generation, indexing, or some other media-processing stage. Until then, the safest assumption is that image-related workflows should be reviewed with heightened caution.It will also matter whether third-party security researchers publish independent analysis that corroborates the cause or exploitation model. In modern vulnerability handling, external validation often determines whether a bug remains a narrow service issue or becomes part of a broader class of image-processing risk. The more concrete the technical details become, the more urgent the defensive response will be. (cyberpress.org)
- Monitor MSRC updates for revised severity or exploitability details.
- Review any Bing-integrated image workflows in enterprise environments.
- Validate whether internal tools call Bing visual services directly or indirectly.
- Watch for independent research on Bing image parsing or preprocessing.
- Reassess compensating controls around content ingestion and rendering.
Source: MSRC Security Update Guide - Microsoft Security Response Center