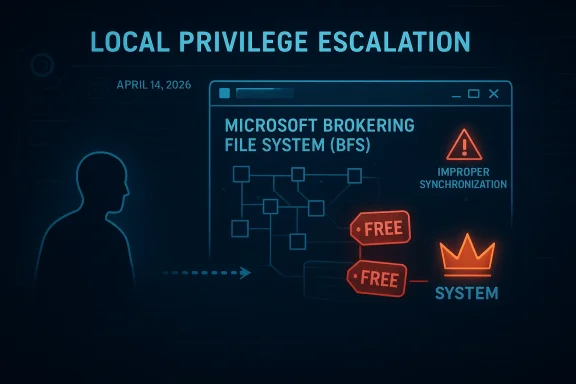
Microsoft’s CVE-2026-32219 is the kind of Windows flaw that security teams dread because it sits squarely in the privilege-escalation lane: an authenticated low-privilege attacker can use it to reach SYSTEM-level control on affected machines. The advisory is for the Microsoft Brokering File System component, a recurring hotspot for local elevation-of-privilege bugs, and the first public descriptions point to a double free condition tied to improper synchronization. That combination is especially concerning because it implies a memory-safety flaw in a kernel-adjacent code path, not just a logic mistake in a user-mode service. Microsoft issued updates on April 14, 2026, and third-party vulnerability feeds currently rate the issue as high severity with local attack prerequisites and no user interaction required once the attacker has local access. (feedly.com)
The Brokering File System has become one of those Windows subsystems that defenders watch closely, not because it is widely discussed by end users, but because it repeatedly attracts vulnerability research. Over the last several years, Microsoft has patched multiple BFS-related elevation-of-privilege issues, and that pattern matters: repeated fixes in the same subsystem usually mean a rich and persistent attack surface rather than a one-off coding mistake. In practical terms, that means the subsystem deserves the same sort of scrutiny many administrators already give to the Windows kernel, graphics stack, and print components. (feedly.com)
This latest CVE fits a familiar Windows hardening story. Microsoft has spent the last two years publicly emphasizing filesystem redirection risks, junction traversal, and local privilege escalation patterns that begin with a compromised standard user and end with SYSTEM. In 2025, Microsoft even shipped RedirectionGuard as a mitigation to reduce the attack surface created by unsafe junction traversal in Windows 11. That broader context matters because it shows how local file-system abuse remains one of the most productive privilege-escalation paths on Windows, and BFS appears to be part of that landscape.
The interesting part about CVE-2026-32219 is not only the bug class, but the confidence level around the public details. The advisory information currently circulating is more concrete than a vague “possible issue,” yet it still leaves room for caution because public write-ups are being assembled from ecosystem data rather than a long vendor narrative. That means defenders should treat the finding as real and actionable, but analysts should still avoid over-reading the exact exploit mechanics until Microsoft’s own advisory text and related documentation are fully digested. (feedly.com)
For enterprise teams, the core lesson is straightforward: this is the kind of vulnerability that rewards fast patching and strong endpoint hygiene. For consumers, it is another reminder that local admin exposure is never harmless, and that malware operating under a low-privilege foothold can still pivot to full compromise if the operating system hands it a vulnerable privileged code path. The attack may begin locally, but the impact can extend to the entire machine, the user’s files, and the trust boundary of any secrets stored on it. (feedly.com)
This is also why BFS-related bugs are often discussed alongside broader Windows filesystem redirection issues. Microsoft’s own RedirectionGuard material explains how privileged services and filesystem interactions can be exposed to attacker influence in ways that are difficult to reason about safely. Even if CVE-2026-32219 is not itself a junction traversal bug, it lives in the same defensive universe: privileged filesystem logic is hard, and attackers know it.
Microsoft’s broader transparency work also helps explain how these advisories are emerging. Since 2024, MSRC has been publishing machine-readable CSAF alongside the traditional Security Update Guide and CVRF channels, explicitly to improve CVE response and remediation workflows. That means security teams are now expected to ingest Microsoft vulnerability data faster and more automatically than before, which is exactly what local EoP issues demand when they land on Patch Tuesday.
There is also a useful caution here: third-party vulnerability aggregators are already surfacing details and sometimes extrapolating affected versions. That can be helpful for triage, but it is not a substitute for Microsoft’s own guidance. Administrators should use the vendor’s published build and package information as the final authority, while treating outside summaries as an early-warning system. Speed is useful; precision is better. (feedly.com)
Microsoft’s 2025 RedirectionGuard blog is relevant here because it describes the broader threat model in plain language. A compromised local user can influence operations in a privileged process by manipulating filesystem behavior, and once that privileged process is tricked, the consequences can range from file tampering to privilege escalation. BFS bugs live in that same ecosystem of concern, even if the exact exploitation primitive differs from one CVE to another.
This is one reason repeated BFS advisories deserve attention. A single CVE can be a one-off; a cluster of similar CVEs across several years suggests recurring difficulty in getting a security-sensitive subsystem fully correct. That does not mean Microsoft is neglecting the area. It means the area itself is inherently hard, and the attack surface is likely to remain attractive to both researchers and criminals. (feedly.com)
The operational challenge is that many security tools are optimized to catch the obvious first-stage attacks. Privilege escalation often happens quickly after the first compromise and can occur before telemetry, response playbooks, or EDR triage fully catch up. That is why these vulnerabilities tend to be disproportionately important even when they are technically local-only. Local is not the same as safe. (feedly.com)
There is also a patch-management implication. Because Microsoft has already released a fix, the real question is no longer whether mitigation exists but whether it is deployed everywhere it needs to be. Organizations with slow rings, disconnected devices, VDI farms, or long-lived server images often discover that “available” and “installed” are very different things. (feedly.com)
This is also why the presence or absence of a public proof-of-concept matters less than some readers assume. Feedly’s summary currently says there is no evidence of public exploit code or active exploitation, but that status can change quickly once researchers, criminals, or internal red teams get involved. The absence of public weaponization is reassuring, but it is not a reason to delay patching on real systems. (feedly.com)
The CVE data also hints at the modern reality of vulnerability intelligence: vendors, aggregators, and advisory platforms often publish layered information at different speeds. Microsoft’s own move toward CSAF and richer advisory data is meant to reduce that lag, but defenders still need to reconcile multiple feeds, avoid stale assumptions, and keep a clear distinction between confirmed facts and provisional technical interpretation.
CVE-2026-32219 does not appear to be a junction issue in the available public summary, but the strategic connection is still useful. It reinforces the message that Windows filesystem security is a layered problem: mitigations, code hygiene, service design, and patch cadence all matter, and weakness in any layer can still produce a critical endpoint compromise. (feedly.com)
In that sense, Microsoft’s newer transparency work is just as important as the patches themselves. The shift to machine-readable advisory formats helps defenders automate ingestion, map affected builds more accurately, and reduce time to remediation. That is especially valuable for recurring local EoP classes, where the difference between a same-day patch and a two-week lag can be the difference between containment and incident response.
Microsoft is likely to continue tightening privileged filesystem behavior, both through targeted patches and through broader mitigation work. If the company keeps expanding class-based protections like RedirectionGuard and keeps pushing richer advisory metadata through CSAF and the Security Update Guide, defenders will gain better tools for response. But the burden will still fall on organizations to translate those tools into real patch compliance.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
The Brokering File System has become one of those Windows subsystems that defenders watch closely, not because it is widely discussed by end users, but because it repeatedly attracts vulnerability research. Over the last several years, Microsoft has patched multiple BFS-related elevation-of-privilege issues, and that pattern matters: repeated fixes in the same subsystem usually mean a rich and persistent attack surface rather than a one-off coding mistake. In practical terms, that means the subsystem deserves the same sort of scrutiny many administrators already give to the Windows kernel, graphics stack, and print components. (feedly.com)This latest CVE fits a familiar Windows hardening story. Microsoft has spent the last two years publicly emphasizing filesystem redirection risks, junction traversal, and local privilege escalation patterns that begin with a compromised standard user and end with SYSTEM. In 2025, Microsoft even shipped RedirectionGuard as a mitigation to reduce the attack surface created by unsafe junction traversal in Windows 11. That broader context matters because it shows how local file-system abuse remains one of the most productive privilege-escalation paths on Windows, and BFS appears to be part of that landscape.
The interesting part about CVE-2026-32219 is not only the bug class, but the confidence level around the public details. The advisory information currently circulating is more concrete than a vague “possible issue,” yet it still leaves room for caution because public write-ups are being assembled from ecosystem data rather than a long vendor narrative. That means defenders should treat the finding as real and actionable, but analysts should still avoid over-reading the exact exploit mechanics until Microsoft’s own advisory text and related documentation are fully digested. (feedly.com)
For enterprise teams, the core lesson is straightforward: this is the kind of vulnerability that rewards fast patching and strong endpoint hygiene. For consumers, it is another reminder that local admin exposure is never harmless, and that malware operating under a low-privilege foothold can still pivot to full compromise if the operating system hands it a vulnerable privileged code path. The attack may begin locally, but the impact can extend to the entire machine, the user’s files, and the trust boundary of any secrets stored on it. (feedly.com)
What Microsoft Appears to Have Fixed
The public description currently associated with CVE-2026-32219 says the flaw is a double free vulnerability in Microsoft Brokering File System that allows an authorized attacker to elevate privileges locally. A double free is one of the more dangerous memory-corruption patterns because it can corrupt allocator metadata, destabilize object lifetimes, and sometimes be shaped into arbitrary code execution or privileged control-flow manipulation depending on the surrounding implementation. The use of “improper synchronization” in the same summary suggests the bug may be related to concurrency and state management rather than a single incorrect call site. (feedly.com)Why double free bugs are so serious
A double free means memory is released more than once. In a modern system, that can lead to object reuse, stale pointers, or heap corruption, and the precise exploitability depends on how the allocator and driver code behave. The fact that the vulnerability is described as local and privilege-related strongly suggests the attacker must already have a foothold, but once they do, a memory-safety bug can be a reliable route to system compromise if the surrounding conditions are favorable. (feedly.com)- Double free issues often create unpredictable but powerful memory corruption.
- Concurrency flaws can make state transitions race-dependent and harder to test.
- Kernel-adjacent components tend to magnify impact because they run with elevated privileges.
- Local attackers can chain this class of bug with other post-exploitation techniques.
- Privilege escalation remains a top-tier Windows attack objective because it turns limited access into full machine control.
The role of synchronization
The mention of improper synchronization is important because it tells us something about how the bug may arise. Race conditions can produce inconsistent object ownership, particularly when one thread frees or drops a resource while another thread still believes the resource is valid. In file-system and driver code, that kind of mistake can be especially dangerous because operations often span multiple paths, callbacks, or state transitions. (feedly.com)This is also why BFS-related bugs are often discussed alongside broader Windows filesystem redirection issues. Microsoft’s own RedirectionGuard material explains how privileged services and filesystem interactions can be exposed to attacker influence in ways that are difficult to reason about safely. Even if CVE-2026-32219 is not itself a junction traversal bug, it lives in the same defensive universe: privileged filesystem logic is hard, and attackers know it.
- Concurrency bugs are harder to fuzz reliably.
- State lifetime errors can remain latent for years.
- Privileged code paths tend to be reused by many higher-level features.
- Memory-safety failures can sometimes be turned into more than just a crash.
- The attack surface grows as Windows continues to add mitigation layers and compatibility behaviors.
Timeline and Disclosure Signals
The first public signals around CVE-2026-32219 appeared on April 14, 2026, which is the same day Microsoft’s security cadence would normally place a large number of fixes in front of administrators. That timing matters because a Patch Tuesday disclosure often pushes defenders into rapid triage mode, especially when a flaw is high-impact but local in scope. The ecosystem is already treating the issue as real, with the public data indicating the patch is available and the vulnerability has been assigned a CVE. (feedly.com)What the current metadata suggests
The currently visible metadata classifies the vulnerability as CVSS 7 with a local attack vector, high attack complexity, low privileges required, and no user interaction. Those numbers tell a nuanced story: the bug is not remotely exploitable by anyone on the internet, but once an attacker has local code execution, the path to privilege escalation may be straightforward enough to matter operationally. In other words, this is the kind of flaw that is especially valuable in post-compromise scenarios. (feedly.com)Microsoft’s broader transparency work also helps explain how these advisories are emerging. Since 2024, MSRC has been publishing machine-readable CSAF alongside the traditional Security Update Guide and CVRF channels, explicitly to improve CVE response and remediation workflows. That means security teams are now expected to ingest Microsoft vulnerability data faster and more automatically than before, which is exactly what local EoP issues demand when they land on Patch Tuesday.
There is also a useful caution here: third-party vulnerability aggregators are already surfacing details and sometimes extrapolating affected versions. That can be helpful for triage, but it is not a substitute for Microsoft’s own guidance. Administrators should use the vendor’s published build and package information as the final authority, while treating outside summaries as an early-warning system. Speed is useful; precision is better. (feedly.com)
- The disclosure date indicates a freshly published vulnerability, not a legacy issue resurfacing.
- The local-only model reduces internet-wide exposure but not enterprise risk.
- The high attack complexity label should not be mistaken for low business urgency.
- Public metadata may evolve as Microsoft refines advisory content.
- Early third-party summaries are useful, but they are still secondary sources.
Why Patch Tuesday timing matters
Patch Tuesday is not just a release ritual; it is an operational forcing function. Enterprises tend to batch testing, deployment, and exception handling around this cadence, which makes same-day disclosures especially sensitive for VPN-borne malware, insider threats, and endpoint persistence. A local privilege-escalation bug in a component like BFS can become a high-value prize when paired with phishing, stolen credentials, or sandbox escape chains. (feedly.com)The Brokering File System Problem
The Microsoft Brokering File System is not a consumer-facing brand name, which is part of why attackers like it. Less celebrated Windows components often sit behind richer features, supporting privileged operations that ordinary applications rely on without thinking too hard about the path they are taking. When those components fail, they can fail in ways that let a low-privilege user borrow trust from a more privileged code path. (feedly.com)Why obscure components attract attention
Security researchers are drawn to subsystems that act as brokers, intermediaries, or handlers of privileged filesystem work. These components frequently mediate access between ordinary applications and higher-trust parts of the OS, which means they must be correct under pressure and across many edge cases. If one of those paths has a lifetime bug, a race, or an improper ownership transfer, the attacker may get exactly what they want: a way to coerce privileged code into doing their work for them. (feedly.com)Microsoft’s 2025 RedirectionGuard blog is relevant here because it describes the broader threat model in plain language. A compromised local user can influence operations in a privileged process by manipulating filesystem behavior, and once that privileged process is tricked, the consequences can range from file tampering to privilege escalation. BFS bugs live in that same ecosystem of concern, even if the exact exploitation primitive differs from one CVE to another.
This is one reason repeated BFS advisories deserve attention. A single CVE can be a one-off; a cluster of similar CVEs across several years suggests recurring difficulty in getting a security-sensitive subsystem fully correct. That does not mean Microsoft is neglecting the area. It means the area itself is inherently hard, and the attack surface is likely to remain attractive to both researchers and criminals. (feedly.com)
- Brokered file operations are often privileged by design.
- Privileged mediation can create large blast radius when it fails.
- Attackers prefer obscure subsystems because defenders monitor them less aggressively.
- Repeated CVEs usually signal a structural hardening challenge, not a one-time typo.
- Local EoP bugs are ideal for post-exploitation chaining.
Historical context
Microsoft has been steadily surfacing filesystem redirection and local escalation issues as part of its broader vulnerability transparency push. The company has also been speaking more openly about entire classes of filesystem weaknesses, not just specific CVEs, because mitigations like RedirectionGuard only work when developers and administrators understand the attacker model. CVE-2026-32219 arrives inside that larger strategy, and it reinforces the idea that local filesystem security remains a core Windows battleground.Why This Matters to Enterprise Defenders
For enterprise defenders, the important detail is that local privilege escalation is often the second stage of a breach, not the first. By the time an attacker is testing BFS or other privileged subsystems, they may already have a standard-user shell, a foothold through malware, or a compromised endpoint account. That makes the vulnerability a force multiplier: it turns partial access into full endpoint control. (feedly.com)Enterprise impact vs. consumer impact
Consumers usually experience this kind of bug through the lens of malware persistence or machine takeover. Enterprises, by contrast, need to think in terms of lateral movement, credential theft, helpdesk abuse, and fleet-wide response costs. A local SYSTEM escalation on a managed device may be enough to disable protections, dump secrets, or establish a more durable foothold that survives routine user-level containment. (feedly.com)The operational challenge is that many security tools are optimized to catch the obvious first-stage attacks. Privilege escalation often happens quickly after the first compromise and can occur before telemetry, response playbooks, or EDR triage fully catch up. That is why these vulnerabilities tend to be disproportionately important even when they are technically local-only. Local is not the same as safe. (feedly.com)
There is also a patch-management implication. Because Microsoft has already released a fix, the real question is no longer whether mitigation exists but whether it is deployed everywhere it needs to be. Organizations with slow rings, disconnected devices, VDI farms, or long-lived server images often discover that “available” and “installed” are very different things. (feedly.com)
- Treat local EoP as an urgent post-compromise risk.
- Prioritize devices with untrusted software exposure.
- Validate patch rollout on laptops, VDI, and server images.
- Correlate endpoint alerts with new admin-group membership and suspicious service creation.
- Assume attackers may chain this flaw with stolen credentials or signed malware.
What good triage looks like
Good triage starts with confirming affected Windows builds, then mapping exposure to endpoint roles. Admin workstations, developer laptops, jump hosts, and any machines that routinely run untrusted code deserve early attention because they are most likely to provide the attacker with the low-privilege foothold needed to begin exploitation. From there, defenders should watch for privilege changes, suspicious child processes, unusual driver activity, and abrupt tampering with security tooling. (feedly.com)The Security Research Angle
CVE-2026-32219 also tells us something about where research attention is going in Windows. The combination of filesystem logic, privileged brokering, and memory safety is an attractive target because it sits at the intersection of legacy compatibility and modern hardening. Researchers increasingly look for bugs in these seams because that is where a lot of high-value impact still hides. (feedly.com)Why attackers value local privilege escalation
A local privilege escalation bug is rarely the final objective in an intrusion chain. Instead, it is the bridge between a noisy, low-privilege entry and a more stable operational position. Once an attacker reaches SYSTEM, they can often disable defenses, harvest tokens or secrets, tamper with services, and prepare for lateral movement with much less friction. (feedly.com)This is also why the presence or absence of a public proof-of-concept matters less than some readers assume. Feedly’s summary currently says there is no evidence of public exploit code or active exploitation, but that status can change quickly once researchers, criminals, or internal red teams get involved. The absence of public weaponization is reassuring, but it is not a reason to delay patching on real systems. (feedly.com)
The CVE data also hints at the modern reality of vulnerability intelligence: vendors, aggregators, and advisory platforms often publish layered information at different speeds. Microsoft’s own move toward CSAF and richer advisory data is meant to reduce that lag, but defenders still need to reconcile multiple feeds, avoid stale assumptions, and keep a clear distinction between confirmed facts and provisional technical interpretation.
- Researchers are increasingly focused on brokered privileged paths.
- Memory-safety flaws remain potent because they can translate into full compromise.
- Public exploit absence should be read as temporary, not permanent.
- Advisory ecosystems are faster than they used to be, but they are still fragmented.
- The strongest defenses are still patching, least privilege, and strong endpoint hardening.
A note on exploitability
The public material currently points to high attack complexity, which often means exploitation is possible but finicky, timing-sensitive, or dependent on specific allocator behavior or race conditions. That can slow down mass exploitation, but it does not remove risk for targeted actors. In many real-world incidents, “hard to exploit” only delays the attacker until they have enough time to perfect their chain. (feedly.com)How Microsoft’s Broader Mitigation Strategy Fits In
Microsoft’s response to filesystem abuse in recent years has not been limited to one-off patches. The company has increasingly framed the issue as a class of problems that requires both code fixes and platform mitigations. RedirectionGuard is the clearest public example of that philosophy, designed to stop unsafe junction traversal in Windows 11 and reduce the burden on developers who would otherwise have to defend every file operation manually.Why class-based defenses matter
Class-based defenses are important because attackers rarely stay loyal to one bug pattern. If one route is blocked, they pivot to another weak link with similar properties. By addressing the broader family of filesystem redirection and privilege-escalation issues, Microsoft improves the baseline even when a specific CVE is fixed only once. That is the right strategy for a platform as large and heterogeneous as Windows.CVE-2026-32219 does not appear to be a junction issue in the available public summary, but the strategic connection is still useful. It reinforces the message that Windows filesystem security is a layered problem: mitigations, code hygiene, service design, and patch cadence all matter, and weakness in any layer can still produce a critical endpoint compromise. (feedly.com)
In that sense, Microsoft’s newer transparency work is just as important as the patches themselves. The shift to machine-readable advisory formats helps defenders automate ingestion, map affected builds more accurately, and reduce time to remediation. That is especially valuable for recurring local EoP classes, where the difference between a same-day patch and a two-week lag can be the difference between containment and incident response.
- Platform mitigations reduce reliance on developer perfectness.
- Advisory transparency improves the defender’s time-to-action.
- Hardening is more effective when it addresses entire classes of bugs.
- Patch management still remains the decisive control in many environments.
- Better metadata makes automation more trustworthy.
Consumer vs. enterprise protections
Consumers benefit most from automatic updates and modern Windows builds that receive hardening improvements transparently. Enterprises, however, have to manage compatibility, change windows, and validation cycles, which can slow protection if internal processes are heavy. That gap is one reason enterprise patch discipline remains a security differentiator rather than a mere housekeeping task. (feedly.com)Strengths and Opportunities
Microsoft’s handling of CVE-2026-32219 shows a few encouraging signs. The advisory appears quickly after disclosure, the patch is already available, and the surrounding platform work suggests the company is thinking not only about individual bugs but about the broader attack surface they belong to. That is exactly the right direction for Windows security in 2026.- The flaw has a clear local privilege-escalation impact, making prioritization straightforward.
- Microsoft has already released security updates, reducing uncertainty for defenders.
- The Brokering File System keeps receiving scrutiny, which can drive deeper hardening.
- Microsoft’s CSAF publication model can improve machine-readable response workflows.
- The RedirectionGuard work shows Microsoft is addressing classes of filesystem attacks, not only single CVEs.
- The public metadata is specific enough to support immediate operational triage. (feedly.com)
- The local-only model reduces the chance of mass internet wormability, which is at least one small silver lining. (feedly.com)
Risks and Concerns
The biggest concern is that local privilege escalation bugs are often underestimated because they are not remotely exploitable. That is a mistake. In real intrusions, an attacker usually needs exactly this kind of bug to move from a user-level foothold to complete machine control, and that can happen very quickly once the initial access has been established.- SYSTEM compromise on a single endpoint can be enough to derail an enterprise incident.
- The bug class is attractive for post-exploitation chaining.
- Race-condition-based flaws can be hard to reproduce but still exploitable in practice.
- Public summaries may lag behind the attacker’s real understanding of the issue.
- Systems that do not patch promptly can become high-value targets.
- Endpoint protection may miss the escalation if defenders are watching only the first-stage intrusion.
- Legacy build management can leave pockets of exposed devices long after the patch is public.
Looking Ahead
The next question is not whether CVE-2026-32219 exists; the public data already supports that it does. The real questions are how reliably it can be exploited, whether it will be chained with other post-compromise techniques, and how quickly enterprises will actually deploy the fix across heterogeneous Windows fleets. Those are the questions that determine whether a local flaw remains a bulletin-item curiosity or becomes an operational headache. (feedly.com)Microsoft is likely to continue tightening privileged filesystem behavior, both through targeted patches and through broader mitigation work. If the company keeps expanding class-based protections like RedirectionGuard and keeps pushing richer advisory metadata through CSAF and the Security Update Guide, defenders will gain better tools for response. But the burden will still fall on organizations to translate those tools into real patch compliance.
- Verify whether Windows 11 24H2, 25H2, 26H1, and Windows Server 2025 endpoints are fully patched. (feedly.com)
- Review whether any managed devices have recent signs of local privilege escalation or suspicious service tampering.
- Prioritize endpoints most likely to host an initial foothold, such as developer systems and admin workstations.
- Watch for Microsoft to refine the advisory with more detailed technical notes or build guidance.
- Expect security tools and vendor intelligence feeds to add more exploitability context over time.
- Use this CVE as a reminder that filesystem security remains one of Windows’ most persistent attack surfaces.
Source: MSRC Security Update Guide - Microsoft Security Response Center