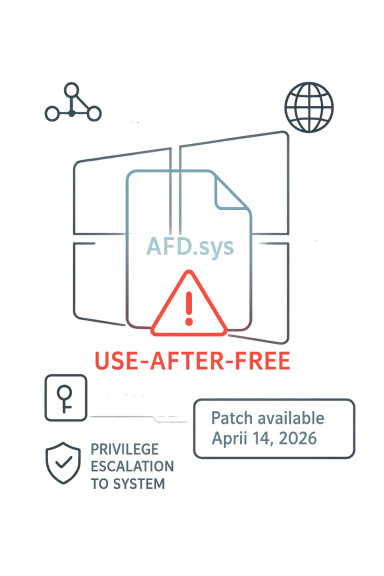
Microsoft’s CVE-2026-33100 advisory for the Windows Ancillary Function Driver for WinSock is another reminder that the most operationally important Windows flaws are often the ones that never generate splashy headlines. The public record currently describes a use-after-free issue that lets an authorized local attacker elevate privileges, and third-party tracking now places the vulnerability at CVSS 7.0 with a local attack vector and no user interaction required. Feedly’s timeline shows the disclosure landing on April 14, 2026, with Microsoft patches available the same day and no public proof-of-concept or confirmed exploitation at the time of publication. (feedly.com)
The first thing defenders should notice is not the CVE number itself, but the component name. AFD.sys, Microsoft’s Ancillary Function Driver for WinSock, sits in a deeply privileged part of the Windows networking stack, which is why bugs here so often translate into meaningful post-compromise control. In plain English, this is the kind of flaw that rarely helps a remote intruder break in from the internet by itself, but it can be extremely valuable once an attacker already has a foothold on a machine. (feedly.com)
Microsoft’s own vulnerability guidance framework emphasizes the difference between “a vulnerability exists” and “we understand the root cause and exploitability well.” That matters because confidence signals influence how quickly defenders should treat a report, especially when the technical write-up is still thin. The Security Response Center has also stated that its CVE pages and machine-readable advisories are intended to help customers track remediation and understand the vendor’s assessment as disclosures evolve.
CVE-2026-33100 arrives in a long and increasingly familiar line of WinSock/AFD issues. Over the last year, Microsoft and the broader ecosystem have repeatedly cataloged local privilege-escalation bugs in the same subsystem, and that pattern is itself significant. When a driver family shows up over and over again in security advisories, the lesson is not that the patches are isolated; it is that the attack surface remains attractive, sensitive, and hard to fully eliminate.
The public details are still limited, so it is wise to avoid overclaiming. What we do know is that Microsoft has acknowledged the bug, the disclosure is already mirrored by multiple security intelligence sources, and the patch is available. That combination makes this a real operational event rather than a theoretical discussion, even if the exact exploitation mechanics remain partially opaque. (feedly.com)
In previous months, Microsoft repeatedly patched related AFD.sys weaknesses, including flaws described publicly as use-after-free, race-condition, improper-access-control, and other local EoP defects. The fact that multiple advisories are landing in the same family should not be read as redundancy; it should be read as a sign that the component continues to expose high-value primitives to attackers. A driver that mediates low-level socket behavior is exactly the kind of code where memory-safety mistakes can be converted into privilege escalation.
The broader Windows security story in 2026 has also emphasized how much of modern exploitation is local rather than remote. Once attackers get in through phishing, a stolen session, a browser flaw, or a misconfigured service account, the next step is often privilege escalation. That is why local EoP bugs routinely rank as high operational priority, even when they do not earn the public drama that remote code execution flaws attract. (feedly.com)
Microsoft’s own metadata model matters here. The company uses advisories, severity guidance, and confidence signals to help enterprises judge whether a disclosure is mature, corroborated, or still in early validation. Even when the advisory is sparse, the existence of a vendor update and the publication of a CVE indicate that the issue has crossed from rumor into actionable remediation territory.
The same record places the issue in the High severity band with a CVSS v3.1 vector of AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H. That combination tells you the flaw is local, requires low privileges, and does not involve user interaction, but it is somewhat harder to exploit than the easiest local privesc bugs. Even so, the impact remains severe because successful abuse can yield full confidentiality, integrity, and availability compromise on the affected host. (feedly.com)
The vendor and ecosystem signals are still converging. Feedly notes that NVD published first details and that GitHub Advisories released a security advisory shortly afterward, which reinforces that the record is not a lone, weakly supported claim. When multiple independent channels are aligning on the same core description, defenders can have more confidence in the existence of the issue even if the exploit chain itself is not yet public. (feedly.com)
That distinction is especially important for defenders who triage at scale. Security teams do not just need to know whether a CVE exists; they need to know whether to patch now, stage a rollout, hunt for compromise, or watch for exploitation reports. Microsoft’s confidence framework is meant to help customers make that judgment before all the technical details are public.
In practical terms, confidence is a risk multiplier. A sparse advisory with weak confidence may justify monitoring and preparation, while a high-confidence kernel bug in a privileged Windows driver is a much stronger trigger for immediate action. CVE-2026-33100 is already beyond the threshold where “wait and see” is the prudent default. (feedly.com)
This is where server estates and endpoint fleets diverge. On workstations, a local EoP bug can expose user data, authentication material, browser tokens, and EDR tampering opportunities. On servers, the same flaw can be more serious because it may be used to pivot into services, deployment systems, or internal trust boundaries that extend far beyond one machine. (feedly.com)
The biggest enterprise challenge is patch timing. Windows environments often contain device diversity, long-lived LTS systems, and line-of-business applications that make immediate patching painful. But the presence of a kernel-level privilege escalation in a networking driver should tilt the decision toward rapid validation and deployment rather than slow, routine maintenance cycles. (feedly.com)
Home users also tend to underestimate the importance of local elevation bugs because they sound technical rather than visible. But on a personal PC, SYSTEM-level control means persistence, credential theft, security-product tampering, and deeper abuse of the machine. If Windows Update offers the fix, it is the kind of patch most users should apply without delay. (feedly.com)
The real consumer lesson is that “local” does not mean “safe.” It means the attacker needs a path in first, and once that path exists, the difference between a normal user account and full control may be exactly this kind of driver bug. In a world of browser exploits, macro malware, and stolen session tokens, that is not a narrow risk profile at all. (feedly.com)
For Microsoft, repeated AFD patches are a double-edged signal. On one hand, they demonstrate active response and ongoing hardening. On the other, they remind customers that core Windows components remain under sustained pressure, and that patching cadence alone does not eliminate structural risk. A mature security program has to assume that popular kernel interfaces will continue to attract discovery and exploitation efforts.
For defenders, the broader market effect is more subtle but important. Every high-profile local privesc in Windows nudges enterprises to strengthen application control, remove unnecessary local admin rights, harden service accounts, and improve post-exploitation telemetry. That is a healthy evolution, but it only happens when advisories are treated as operational lessons rather than isolated patch notes. (feedly.com)
The best remediation strategy is layered. Patch first, then validate local privilege boundaries, then review telemetry for suspicious behavior around the advisory window. Enterprises should also prioritize systems that handle sensitive credentials, developer workstations, jump boxes, and administrative endpoints, because those machines amplify the consequences of a successful local escalation. (feedly.com)
The second area to watch is adoption. A patch existing on paper is not the same as a patch deployed across servers, VDI pools, and remote endpoints. If the advisory turns out to affect widely used Windows builds in enterprise fleets, the speed of real-world rollout will matter more than the formal publication date.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
The first thing defenders should notice is not the CVE number itself, but the component name. AFD.sys, Microsoft’s Ancillary Function Driver for WinSock, sits in a deeply privileged part of the Windows networking stack, which is why bugs here so often translate into meaningful post-compromise control. In plain English, this is the kind of flaw that rarely helps a remote intruder break in from the internet by itself, but it can be extremely valuable once an attacker already has a foothold on a machine. (feedly.com)Microsoft’s own vulnerability guidance framework emphasizes the difference between “a vulnerability exists” and “we understand the root cause and exploitability well.” That matters because confidence signals influence how quickly defenders should treat a report, especially when the technical write-up is still thin. The Security Response Center has also stated that its CVE pages and machine-readable advisories are intended to help customers track remediation and understand the vendor’s assessment as disclosures evolve.
CVE-2026-33100 arrives in a long and increasingly familiar line of WinSock/AFD issues. Over the last year, Microsoft and the broader ecosystem have repeatedly cataloged local privilege-escalation bugs in the same subsystem, and that pattern is itself significant. When a driver family shows up over and over again in security advisories, the lesson is not that the patches are isolated; it is that the attack surface remains attractive, sensitive, and hard to fully eliminate.
The public details are still limited, so it is wise to avoid overclaiming. What we do know is that Microsoft has acknowledged the bug, the disclosure is already mirrored by multiple security intelligence sources, and the patch is available. That combination makes this a real operational event rather than a theoretical discussion, even if the exact exploitation mechanics remain partially opaque. (feedly.com)
Background
AFD.sys has been on Windows defenders’ radar for years because it is kernel mode, network-adjacent, and security-critical. That alone makes it a natural target for attackers looking to turn a low-privilege local foothold into SYSTEM-level control. Windows privileges are not just a policy layer; they are the difference between a compromised user session and complete control of the host, security tools, and sometimes domain reachability. (feedly.com)In previous months, Microsoft repeatedly patched related AFD.sys weaknesses, including flaws described publicly as use-after-free, race-condition, improper-access-control, and other local EoP defects. The fact that multiple advisories are landing in the same family should not be read as redundancy; it should be read as a sign that the component continues to expose high-value primitives to attackers. A driver that mediates low-level socket behavior is exactly the kind of code where memory-safety mistakes can be converted into privilege escalation.
The broader Windows security story in 2026 has also emphasized how much of modern exploitation is local rather than remote. Once attackers get in through phishing, a stolen session, a browser flaw, or a misconfigured service account, the next step is often privilege escalation. That is why local EoP bugs routinely rank as high operational priority, even when they do not earn the public drama that remote code execution flaws attract. (feedly.com)
Microsoft’s own metadata model matters here. The company uses advisories, severity guidance, and confidence signals to help enterprises judge whether a disclosure is mature, corroborated, or still in early validation. Even when the advisory is sparse, the existence of a vendor update and the publication of a CVE indicate that the issue has crossed from rumor into actionable remediation territory.
Why AFD.sys keeps resurfacing
AFD.sys is attractive because it sits near core system boundaries. Bugs in this area can lead to arbitrary memory access, corrupted state, or privilege boundary failures, and those are exactly the ingredients that attackers need to escape the sandbox of a low-privilege account. The repeated appearance of AFD-related EoPs is not just a Microsoft patching cadence; it is a map of where defenders must expect persistent pressure. (feedly.com)- Kernel proximity increases the value of any memory-safety flaw.
- Local attack requirements make exploitation harder than a web bug, but still dangerous after compromise.
- Repeated advisories suggest a durable attack surface rather than a one-off mistake.
- SYSTEM-level escalation can neutralize many endpoint defenses immediately.
What the Public Record Actually Says
Feedly’s current record says CVE-2026-33100 is a use-after-free vulnerability in Windows Ancillary Function Driver for WinSock that allows an authorized attacker to elevate privileges locally. It also notes that no public proof-of-concept or confirmed exploitation is visible at the moment, and that Microsoft patches are available as of April 14, 2026. That is the clearest available snapshot of the case right now. (feedly.com)The same record places the issue in the High severity band with a CVSS v3.1 vector of AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H. That combination tells you the flaw is local, requires low privileges, and does not involve user interaction, but it is somewhat harder to exploit than the easiest local privesc bugs. Even so, the impact remains severe because successful abuse can yield full confidentiality, integrity, and availability compromise on the affected host. (feedly.com)
The vendor and ecosystem signals are still converging. Feedly notes that NVD published first details and that GitHub Advisories released a security advisory shortly afterward, which reinforces that the record is not a lone, weakly supported claim. When multiple independent channels are aligning on the same core description, defenders can have more confidence in the existence of the issue even if the exploit chain itself is not yet public. (feedly.com)
Why “authorized attacker” matters
The wording authorized attacker is a subtle but important clue. It usually means the issue is not an initial-access bug; instead, it helps someone who already has a local account, a foothold, or a constrained process context to climb privileges. That may sound narrower than a remote bug, but in enterprise environments it is often the difference between a contained incident and a machine that becomes a launchpad for lateral movement. (feedly.com)- The bug is local, not remote.
- It does not require user interaction.
- The attacker must already have some access.
- The likely payoff is SYSTEM-level control.
Why the Confidence Metric Matters
Microsoft’s confidence metric exists because the existence of a reported vulnerability and the maturity of the technical details are not the same thing. A report can be real but incompletely understood, or it can be precise enough that an exploit developer can start reproducing it quickly. The higher the confidence, the stronger the signal that the advisory reflects a genuine and technically credible issue.That distinction is especially important for defenders who triage at scale. Security teams do not just need to know whether a CVE exists; they need to know whether to patch now, stage a rollout, hunt for compromise, or watch for exploitation reports. Microsoft’s confidence framework is meant to help customers make that judgment before all the technical details are public.
In practical terms, confidence is a risk multiplier. A sparse advisory with weak confidence may justify monitoring and preparation, while a high-confidence kernel bug in a privileged Windows driver is a much stronger trigger for immediate action. CVE-2026-33100 is already beyond the threshold where “wait and see” is the prudent default. (feedly.com)
Reading the advisory like a defender
The right way to interpret a vendor confidence signal is not as a substitute for CVSS, but as a companion to it. CVSS tells you the likely severity profile, while confidence tells you how trustworthy and mature the report appears to be. Those are related, but they are not interchangeable. (feedly.com)- High confidence usually means stronger remediation urgency.
- Sparse technical detail does not mean low risk.
- Kernel bugs deserve fast attention even without exploit code.
- Local-only flaws can still be disastrous after initial compromise.
Enterprise Risk: Why This Matters More Than It Sounds
For enterprises, the danger is not that CVE-2026-33100 will replace perimeter defenses overnight. The danger is that it may give attackers a reliable way to finish the job after another weakness, credential theft, or endpoint foothold has already opened the door. In modern intrusion chains, local privilege escalation is often the step that converts an alert into a breach. (feedly.com)This is where server estates and endpoint fleets diverge. On workstations, a local EoP bug can expose user data, authentication material, browser tokens, and EDR tampering opportunities. On servers, the same flaw can be more serious because it may be used to pivot into services, deployment systems, or internal trust boundaries that extend far beyond one machine. (feedly.com)
The biggest enterprise challenge is patch timing. Windows environments often contain device diversity, long-lived LTS systems, and line-of-business applications that make immediate patching painful. But the presence of a kernel-level privilege escalation in a networking driver should tilt the decision toward rapid validation and deployment rather than slow, routine maintenance cycles. (feedly.com)
Practical implications by environment
A security team does not need a full exploit write-up to act. It needs enough confidence to know that unpatched systems are likely to be more exposed than patched ones, and that the residual risk of delay is meaningful. The vendor patch availability removes most of the justification for standing still. (feedly.com)- Endpoints face immediate post-compromise privilege escalation risk.
- Servers may expose broader blast radius if abused.
- Admins should treat local privilege gains as a precursor to lateral movement.
- SOC teams should watch for suspicious driver and token activity after rollout.
Consumer Impact: What Home Users Should Know
For consumers, the advisory does not imply that random internet users are being remotely hacked through this CVE alone. Instead, it points to a risk that becomes important after malware, an untrusted local account, or another compromise already exists on the device. That distinction is comforting only in a limited sense, because modern commodity malware often arrives with exactly that kind of foothold. (feedly.com)Home users also tend to underestimate the importance of local elevation bugs because they sound technical rather than visible. But on a personal PC, SYSTEM-level control means persistence, credential theft, security-product tampering, and deeper abuse of the machine. If Windows Update offers the fix, it is the kind of patch most users should apply without delay. (feedly.com)
The real consumer lesson is that “local” does not mean “safe.” It means the attacker needs a path in first, and once that path exists, the difference between a normal user account and full control may be exactly this kind of driver bug. In a world of browser exploits, macro malware, and stolen session tokens, that is not a narrow risk profile at all. (feedly.com)
What users should do
Most users do not need exploit analysis; they need good hygiene and quick patch adoption. The availability of a Microsoft fix on the same day as disclosure means this is more about deployment discipline than technical debate. (feedly.com)- Install the latest Windows security updates.
- Reboot when prompted so the kernel driver change takes effect.
- Avoid running untrusted software with local admin rights.
- Keep endpoint protection and tamper protection enabled.
- Watch for unusual prompts, driver failures, or privilege changes after patching.
Competitive and Ecosystem Implications
AFD.sys has become a proving ground for Windows local privilege escalation research, and that has implications well beyond one advisory. Security vendors, red-teamers, exploit brokers, and defenders all watch this class closely because the payoff is high and the technical barrier is often lower than for a remote kernel exploit. The more often these issues appear, the more likely the ecosystem is to refine exploit development and defensive detection around them.For Microsoft, repeated AFD patches are a double-edged signal. On one hand, they demonstrate active response and ongoing hardening. On the other, they remind customers that core Windows components remain under sustained pressure, and that patching cadence alone does not eliminate structural risk. A mature security program has to assume that popular kernel interfaces will continue to attract discovery and exploitation efforts.
For defenders, the broader market effect is more subtle but important. Every high-profile local privesc in Windows nudges enterprises to strengthen application control, remove unnecessary local admin rights, harden service accounts, and improve post-exploitation telemetry. That is a healthy evolution, but it only happens when advisories are treated as operational lessons rather than isolated patch notes. (feedly.com)
Why the market keeps caring about AFD bugs
Even when public details are sparse, security products can still build detections around process behavior, unusual token changes, and exploit-like memory activity. That is why AFD advisories often matter to more than just Microsoft customers; they shape endpoint protection logic, threat-hunting playbooks, and vulnerability prioritization across the market. In practical terms, one Windows kernel bug can influence the workflows of many security vendors at once. (feedly.com)- Detection engineering tends to improve after recurring kernel issues.
- EDR vendors watch for privilege jumps and suspicious driver interactions.
- Patch-management teams use these CVEs to justify faster rollout windows.
- Threat actors value local escalation paths that bypass user-level controls.
Patch Prioritization and Mitigation Strategy
The patch decision here is straightforward: install the Microsoft fix. Because the flaw is local and requires prior access, some teams may be tempted to delay it in favor of a higher-profile internet-facing issue. That would be a mistake if the machine is exposed to user activity, remote management, or shared access, because those conditions make local escalation much more likely to matter. (feedly.com)The best remediation strategy is layered. Patch first, then validate local privilege boundaries, then review telemetry for suspicious behavior around the advisory window. Enterprises should also prioritize systems that handle sensitive credentials, developer workstations, jump boxes, and administrative endpoints, because those machines amplify the consequences of a successful local escalation. (feedly.com)
Recommended defensive sequence
A disciplined rollout reduces surprise without slowing the response too much. The goal is not just to install a patch, but to make sure the fix lands cleanly across your estate and does not create blind spots in monitoring. (feedly.com)- Confirm affected build numbers in your inventory.
- Stage the Microsoft update on representative systems.
- Validate networking, security software, and line-of-business behavior.
- Roll out broadly on a prioritized schedule.
- Hunt for abnormal privilege changes or failed exploit attempts after deployment.
Strengths and Opportunities
The strongest part of Microsoft’s response is that the patch is already available, which gives defenders a concrete remediation path instead of a waiting game. The advisory’s local-only framing also helps teams prioritize based on actual blast radius rather than on fear alone. Equally important, the publication of a CVE and the appearance of parallel ecosystem tracking create enough corroboration to make this a real, actionable item rather than speculation.- Patch availability on day of disclosure
- Clear local privilege-escalation impact
- No user interaction required
- Strong fit for existing enterprise patch workflows
- Good candidate for endpoint detection tuning
- Opportunity to remove unnecessary local admin rights
- Chance to harden high-value Windows hosts
Risks and Concerns
The biggest concern is that local privilege escalation is often underestimated because it does not look dramatic from the outside. If an attacker already has a foothold, this kind of bug can rapidly convert a narrow compromise into full host control, and that can happen quietly. Another concern is that AFD.sys has a history of recurring problems, which means defenders should assume the attack surface remains attractive even after this patch cycle.- Underestimation because the flaw is local
- Potential use after initial compromise
- SYSTEM-level takeover on affected systems
- Recurrent vulnerability history in the same driver family
- Possible security-tool tampering after exploitation
- Slow enterprise patching on legacy or fragile systems
- Limited public detail can delay some triage decisions
What to Watch Next
The next important signal will be whether Microsoft or independent researchers publish more technical detail about the root cause and exploitability. If that happens, defenders will be able to refine detection logic and determine whether the issue resembles prior AFD patterns or introduces a new exploitation primitive. The other thing to watch is whether exploit chatter appears quickly, because AFD bugs often attract attention from both researchers and offensive operators.The second area to watch is adoption. A patch existing on paper is not the same as a patch deployed across servers, VDI pools, and remote endpoints. If the advisory turns out to affect widely used Windows builds in enterprise fleets, the speed of real-world rollout will matter more than the formal publication date.
Watch list
- Microsoft follow-up guidance or clarification
- NVD enrichment updates and metadata changes
- Evidence of proof-of-concept code or exploit chaining
- EDR detections and threat-hunting guidance from vendors
- Enterprise patch adoption and any compatibility issues
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: