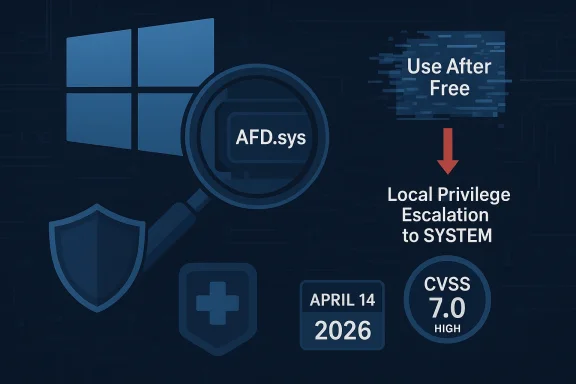
Microsoft’s CVE-2026-32073 is the kind of Windows security advisory that makes defenders stop and re-evaluate their patch queue: it is a local elevation-of-privilege flaw in the Windows Ancillary Function Driver for WinSock, better known as AFD.sys, and it is already being tracked as a use-after-free issue with a high CVSS 3.1 score of 7.0. Public tracking services show the advisory as published on April 14, 2026, with Microsoft’s own Security Update Guide link attached as the canonical reference point. The practical takeaway is simple: a low-privileged local attacker may be able to turn a foothold into a much more powerful position, including system-level control. (feedly.com)
AFD.sys has been a recurring focus for Windows security teams for years because it sits in the networking stack, where even small logic bugs can have outsized consequences. As a kernel-mode component, it runs with the kind of trust that makes memory-corruption flaws especially dangerous, and Microsoft has repeatedly had to address elevation-of-privilege weaknesses in this area over multiple Patch Tuesday cycles. That history matters because it shows the issue is not an isolated oddity; it is part of a broader pattern of kernel attack surface risk. (feedly.com)
The new CVE follows a familiar template: the public description is short, but the implications are obvious to anyone who has watched Windows exploit trends over the last decade. A use-after-free flaw typically means the code keeps using memory after it has been released, which can lead to memory corruption and, in the kernel, potentially reliable privilege escalation. Microsoft’s current Security Update Guide framework is designed to surface exactly this kind of high-value vulnerability information quickly, even when full root-cause detail is still sparse. (cvefeed.io)
That sparse disclosure is not a weakness in Microsoft’s process so much as a reflection of the modern vulnerability pipeline. The Security Update Guide is now the authoritative source for the CVE record, and Microsoft has been steadily adding more structure to how it communicates root cause, severity, and exploitability over time. In practice, that means defenders often get the actionable information first, while the deeper technical narrative arrives later, if at all.
There is also a broader operational context here: AFD.sys sits in a class of Windows components that attackers prize because they are local, high-trust, and present on nearly every machine. When a bug in that layer is disclosed, it is rarely interesting only to researchers; it is relevant to enterprise administrators, red teams, endpoint vendors, and anyone responsible for hardening Windows estate reliability. That is why even a one-line advisory can produce immediate patching pressure across fleets. (feedly.com)
The modern lesson is that attack surface density matters as much as raw code volume. A component that every workstation and server depends on can become a high-value exploit target even if the bug itself appears narrow. That is exactly why these AFD.sys CVEs draw so much attention from defenders. (feedly.com)
The CVSS vector reflects that shape of risk. The score is 7.0 High, with Local attack vector, High attack complexity, Low privileges required, and No user interaction. In other words, this is not the sort of bug that is trivially exploitable from a distance, but it is still highly valuable once an attacker has landed on the machine. (feedly.com)
For CVE-2026-32073, the vendor appears to be signaling enough confidence to publish a fix and attach a precise weakness class, CWE-416: Use After Free. That does not automatically mean attackers already have a public exploit, but it does mean Microsoft considers the issue real, actionable, and patchable. That distinction is crucial because confidence levels drive how quickly enterprises move from awareness to remediation. (cvefeed.io)
The AFD.sys context makes the issue even more concerning because this driver lives close to the core networking path. That does not automatically mean the bug is remotely reachable, but it does mean the code is likely to be exercised through legitimate Windows networking interfaces and local system calls that already operate inside a privileged trust boundary. Local privilege escalation flaws often emerge exactly in those kinds of transitions. (cvefeed.io)
The adversary’s goal is usually not the bug itself but the post-bug state: arbitrary write, controlled read, or control-flow disruption. From there, the leap from user context to SYSTEM access becomes feasible if the exploit chain is strong enough. Microsoft’s high-impact classification reflects that reality. (feedly.com)
This is not unique to AFD.sys, of course. Kernel drivers, file systems, and input subsystems regularly produce local elevation-of-privilege flaws because they process high-value inputs under strong trust assumptions. But AFD.sys stands out because it blends legacy networking semantics with deep kernel privileges, which is a dangerous combination when memory management goes wrong.
That matters for enterprises because it changes the meaning of “patch this month.” A recurring driver family is not just a one-off bug; it is a signal that local privilege escalation should remain high on the hardening agenda. Endpoint controls, least privilege, and privileged access hygiene all become more important when kernel bugs keep surfacing. (feedly.com)
This kind of span also implies that older supported branches remain in the blast radius. That is an important reminder for organizations that still run long-lived images or deferred update rings, because the presence of a patch in a current release does not automatically mean older estates are safe. Mixed-version environments are often where local EoP bugs do the most damage. (feedly.com)
That breadth also raises questions about regression risk. Broad kernel fixes can sometimes introduce new stability concerns, especially in network-heavy environments. Administrators will want to test carefully, but testing should not be used as a delay tactic when the risk is local SYSTEM compromise. (feedly.com)
A practical rollout order could look like this:
The absence of a public proof-of-concept, at least in the sources reviewed, should not reassure defenders too much. Many local EoP bugs are exploited quietly long before commodity tooling appears, especially when the reward is kernel-level control. Low noise does not mean low risk. (feedly.com)
The fact that user interaction is not required also raises the ceiling on automation. Exploits that do not depend on a victim clicking a prompt are easier to operationalize in chained intrusion workflows. That is one reason the CVSS vector still lands in high-severity territory even without a remote attack path. (feedly.com)
The important part is that Microsoft has already published a fix, which shifts the issue from theory to operations. Once a patch is available, the debate changes from “how bad is it?” to “how fast can we deploy safely?” That is a much more useful discussion for defenders, even if some technical specifics remain unpublished. (feedly.com)
For CVE-2026-32073, the combination of a named CWE, a published fix, and broad affected-system coverage points to a high-confidence, actionable event. That is enough to justify immediate remediation planning even without a full exploit write-up. Waiting for a PoC is a losing strategy in this category. (feedly.com)
The most important operational question is whether CVE-2026-32073 remains a quiet patching item or becomes part of a broader exploitation campaign. If future telemetry shows exploitation attempts, that will instantly elevate urgency for organizations that delayed deployment. Until then, the rational stance is still to treat it as a high-priority local privilege escalation and close the gap before attackers do. (feedly.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
AFD.sys has been a recurring focus for Windows security teams for years because it sits in the networking stack, where even small logic bugs can have outsized consequences. As a kernel-mode component, it runs with the kind of trust that makes memory-corruption flaws especially dangerous, and Microsoft has repeatedly had to address elevation-of-privilege weaknesses in this area over multiple Patch Tuesday cycles. That history matters because it shows the issue is not an isolated oddity; it is part of a broader pattern of kernel attack surface risk. (feedly.com)The new CVE follows a familiar template: the public description is short, but the implications are obvious to anyone who has watched Windows exploit trends over the last decade. A use-after-free flaw typically means the code keeps using memory after it has been released, which can lead to memory corruption and, in the kernel, potentially reliable privilege escalation. Microsoft’s current Security Update Guide framework is designed to surface exactly this kind of high-value vulnerability information quickly, even when full root-cause detail is still sparse. (cvefeed.io)
That sparse disclosure is not a weakness in Microsoft’s process so much as a reflection of the modern vulnerability pipeline. The Security Update Guide is now the authoritative source for the CVE record, and Microsoft has been steadily adding more structure to how it communicates root cause, severity, and exploitability over time. In practice, that means defenders often get the actionable information first, while the deeper technical narrative arrives later, if at all.
There is also a broader operational context here: AFD.sys sits in a class of Windows components that attackers prize because they are local, high-trust, and present on nearly every machine. When a bug in that layer is disclosed, it is rarely interesting only to researchers; it is relevant to enterprise administrators, red teams, endpoint vendors, and anyone responsible for hardening Windows estate reliability. That is why even a one-line advisory can produce immediate patching pressure across fleets. (feedly.com)
Why AFD.sys keeps returning to the spotlight
AFD.sys is not flashy, but it is foundational. It mediates socket-related behavior that underpins Windows networking, which means its code paths are both broad and security-sensitive. Kernel networking drivers have historically been rich hunting ground for elevation-of-privilege bugs because they process complex inputs under privileged context and often accumulate legacy behaviors over time.The modern lesson is that attack surface density matters as much as raw code volume. A component that every workstation and server depends on can become a high-value exploit target even if the bug itself appears narrow. That is exactly why these AFD.sys CVEs draw so much attention from defenders. (feedly.com)
What Microsoft Is Saying
The public description for CVE-2026-32073 is concise: use after free in Windows Ancillary Function Driver for WinSock allows an authorized attacker to elevate privileges locally. That phrasing tells defenders several important things at once. The attacker already needs local access, the issue is not remote, and the end result is privilege escalation rather than a crash or simple denial of service. (cvefeed.io)The CVSS vector reflects that shape of risk. The score is 7.0 High, with Local attack vector, High attack complexity, Low privileges required, and No user interaction. In other words, this is not the sort of bug that is trivially exploitable from a distance, but it is still highly valuable once an attacker has landed on the machine. (feedly.com)
Reading the confidence signal correctly
Microsoft’s Security Update Guide has long been more than a name-and-number catalog. Its job is to help customers judge how much certainty exists around the vulnerability and how urgently they should respond, especially when technical details are limited. That is why Microsoft’s descriptions and associated metadata matter even when the root cause is not fully public.For CVE-2026-32073, the vendor appears to be signaling enough confidence to publish a fix and attach a precise weakness class, CWE-416: Use After Free. That does not automatically mean attackers already have a public exploit, but it does mean Microsoft considers the issue real, actionable, and patchable. That distinction is crucial because confidence levels drive how quickly enterprises move from awareness to remediation. (cvefeed.io)
- The flaw is local, not remote.
- The attacker must be authorized on the system.
- The impact is privilege escalation, not simple instability.
- The weakness class is CWE-416, which is often associated with memory corruption.
- Microsoft has already shipped a security update. (feedly.com)
Technical Shape of the Bug
A use-after-free condition is one of the most dangerous memory-safety failures in systems software because it can create a race between object lifetime and later access. Once a freed object is reused or corrupted, the program may follow attacker-influenced pointers, write to unintended memory, or invoke methods on an object whose internal state no longer exists. In kernel mode, those failures can become very serious very quickly. (cvefeed.io)The AFD.sys context makes the issue even more concerning because this driver lives close to the core networking path. That does not automatically mean the bug is remotely reachable, but it does mean the code is likely to be exercised through legitimate Windows networking interfaces and local system calls that already operate inside a privileged trust boundary. Local privilege escalation flaws often emerge exactly in those kinds of transitions. (cvefeed.io)
Why use-after-free bugs matter in the kernel
When a kernel object is freed, its memory may be returned to a pool and later repurposed for something else. If AFD.sys continues to use the old pointer, an attacker may be able to influence what data sits there next, creating a path toward controlled corruption. That is why memory-safety bugs in kernel drivers remain such a persistent problem even in mature platforms like Windows. (cvefeed.io)The adversary’s goal is usually not the bug itself but the post-bug state: arbitrary write, controlled read, or control-flow disruption. From there, the leap from user context to SYSTEM access becomes feasible if the exploit chain is strong enough. Microsoft’s high-impact classification reflects that reality. (feedly.com)
What is still unknown
Microsoft’s public entry gives only the vulnerability class and impact, not the specific code path, trigger condition, or exploit chain. That is normal for early advisories, but it also means defenders should be careful not to overfit to assumptions about the exact trigger. The correct response is not speculation; it is patching and monitoring. (cvefeed.io)- No public proof-of-concept was evident in the tracking sources reviewed.
- The advisory does not expose the exact affected function or call sequence.
- The likely exploitation path remains local and authenticated.
- The vulnerability class strongly suggests memory-corruption risk.
- The fixed build set appears broad across supported Windows versions. (feedly.com)
A Familiar Windows Pattern
AFD.sys vulnerabilities have appeared often enough that the name alone now triggers a familiar defender reaction. Microsoft has previously addressed a range of AFD-related elevation-of-privilege bugs, and the component’s long-term presence in the networking stack means it has a large and complex attack surface. The recurring pattern is important because it suggests the driver’s security story is still not fully “done.”This is not unique to AFD.sys, of course. Kernel drivers, file systems, and input subsystems regularly produce local elevation-of-privilege flaws because they process high-value inputs under strong trust assumptions. But AFD.sys stands out because it blends legacy networking semantics with deep kernel privileges, which is a dangerous combination when memory management goes wrong.
The significance of repeat offenders
When the same subsystem keeps reappearing in advisories, it usually means one of three things. Either the attack surface is genuinely hard to secure, the code is too intertwined with legacy behavior to simplify quickly, or both. In the case of Windows networking drivers, both explanations are plausible and likely reinforce each other. (feedly.com)That matters for enterprises because it changes the meaning of “patch this month.” A recurring driver family is not just a one-off bug; it is a signal that local privilege escalation should remain high on the hardening agenda. Endpoint controls, least privilege, and privileged access hygiene all become more important when kernel bugs keep surfacing. (feedly.com)
Enterprise vs consumer impact
For consumers, the immediate implication is simple: if the machine is shared, poorly maintained, or used for risky software installs, a local foothold can become much more serious after exploitation. For enterprises, the concern is broader and more structural: a low-privileged user account on an unpatched endpoint can become the launch point for lateral movement, credential theft, or security-tool tampering. Those are very different operational risks, but they stem from the same technical flaw. (feedly.com)- Consumer systems risk local takeover after malware gets a foothold.
- Enterprise systems risk privilege escalation inside a managed environment.
- Servers may face higher operational consequence because of shared roles.
- Endpoints with broad local access are especially exposed.
- Identity controls matter because the flaw requires an authenticated local attacker. (feedly.com)
Scope of Affected Systems
The available public trackers indicate that CVE-2026-32073 affects a broad set of Windows editions, including Windows Server 2012, 2012 R2, 2016, 2019, 2022, 2025, and multiple desktop releases from Windows 10 1607 through Windows 11 26H1. That breadth is what turns a technical bug into an enterprise-scale patching event. (feedly.com)This kind of span also implies that older supported branches remain in the blast radius. That is an important reminder for organizations that still run long-lived images or deferred update rings, because the presence of a patch in a current release does not automatically mean older estates are safe. Mixed-version environments are often where local EoP bugs do the most damage. (feedly.com)
Why version spread matters
A vulnerability that crosses server and client lines is harder to triage because it touches both management planes and workstation fleets. Security teams cannot assume that “servers are unaffected” or that “this is only for desktops.” The advisories suggest the opposite: the driver is pervasive enough that Microsoft had to fix a large cross-section of the Windows product line. (feedly.com)That breadth also raises questions about regression risk. Broad kernel fixes can sometimes introduce new stability concerns, especially in network-heavy environments. Administrators will want to test carefully, but testing should not be used as a delay tactic when the risk is local SYSTEM compromise. (feedly.com)
What this means for patch management
The first priority is simple inventory. Organizations should identify all Windows systems that fall within the affected version families, then verify which devices have already received April 14, 2026 updates. The second priority is ring-based deployment, beginning with high-value endpoints and internet-facing or user-heavy systems where local access is easiest to obtain. (feedly.com)A practical rollout order could look like this:
- Identify all supported Windows versions in production.
- Confirm patch status on privileged workstations and servers.
- Move to general endpoint fleets and VDI pools.
- Validate stability in high-network-use environments.
- Close the loop with compliance reporting and exception handling. (feedly.com)
Why This Matters for Attackers
Local privilege escalation flaws remain among the most valuable bugs in any operating system because they are the bridge from a limited foothold to full control. Attackers who land through phishing, an exposed service, a malicious download, or stolen credentials often need exactly this kind of bug to finish the job. CVE-2026-32073 is valuable because it can convert “I’m in” into “I own the box.” (feedly.com)The absence of a public proof-of-concept, at least in the sources reviewed, should not reassure defenders too much. Many local EoP bugs are exploited quietly long before commodity tooling appears, especially when the reward is kernel-level control. Low noise does not mean low risk. (feedly.com)
The threat model in plain English
An attacker does not need to exploit this over the network if they already have a beachhead. That is what makes local kernel bugs so dangerous in ransomware and post-compromise operations. Once inside, the attacker can elevate, disable controls, dump credentials, and move laterally with far less resistance. (feedly.com)The fact that user interaction is not required also raises the ceiling on automation. Exploits that do not depend on a victim clicking a prompt are easier to operationalize in chained intrusion workflows. That is one reason the CVSS vector still lands in high-severity territory even without a remote attack path. (feedly.com)
Indicators defenders should consider
While Microsoft’s public advisory is sparse, defenders can still use a few common-sense signals to focus monitoring. Kernel crashes, suspicious privilege changes, and unusual activity around local accounts can all be worth investigating, especially if they occur on systems that have not yet been updated. Those signals are not proof of exploitation, but they are valuable triage clues. (feedly.com)- Unexpected elevation from standard-user activity.
- Abnormal security logs around local logon sessions.
- Kernel instability or unexplained network driver crashes.
- Endpoint tamper events after a local compromise.
- Repeated failures from security tools on the same host. (feedly.com)
Microsoft’s Disclosure Model
Microsoft’s current disclosure model is built to communicate enough detail for action while preserving some technical uncertainty early in the cycle. The company has moved toward clearer vulnerability classification, including CWE tagging and richer Security Update Guide metadata, precisely because customers need structured guidance rather than a vague warning. CVE-2026-32073 fits that pattern cleanly.The important part is that Microsoft has already published a fix, which shifts the issue from theory to operations. Once a patch is available, the debate changes from “how bad is it?” to “how fast can we deploy safely?” That is a much more useful discussion for defenders, even if some technical specifics remain unpublished. (feedly.com)
Confidence, exploitability, and practical urgency
Microsoft’s confidence framework exists because not all vulnerability records are equally mature. Some are inferred, some are corroborated, and some are fully confirmed by vendor analysis. The more confidence there is, the more likely defenders should treat the issue as operationally real rather than simply informational.For CVE-2026-32073, the combination of a named CWE, a published fix, and broad affected-system coverage points to a high-confidence, actionable event. That is enough to justify immediate remediation planning even without a full exploit write-up. Waiting for a PoC is a losing strategy in this category. (feedly.com)
How this differs from rumor-driven tracking
Some third-party sources may overstate precision, especially when they infer exact affected versions or exploit mechanics from sparse data. Defenders should prefer Microsoft’s advisory and the strongest corroborating sources, using third-party intelligence mainly as a supplement. That approach avoids false certainty and keeps response decisions grounded in vendor-confirmed facts. (feedly.com)Strengths and Opportunities
The good news is that this is a well-understood class of vulnerability, Microsoft has already issued a fix, and defenders have the advantage of clear remediation guidance even if the exploit mechanics are not fully public. For security teams that already operate disciplined update rings, CVE-2026-32073 is the sort of event where good process pays off quickly. It is also a chance to review whether local privilege escalation is being treated as a core risk, not just a postscript to ransomware planning.- Microsoft has published a security update, so the path to remediation is clear.
- The advisory is specific enough to support inventory-driven patching.
- CVSS and CWE metadata make the issue easy to prioritize.
- The attack vector is local, which lets defenders focus on trusted-user boundaries.
- Organizations can use the event to test privileged access controls.
- It is a strong reminder to harden endpoint least privilege.
- Kernel-driver risk can be folded into broader patch governance improvements. (feedly.com)
Risks and Concerns
The main concern is not just exploitation of a single machine, but the operational cascade that can follow a successful local escalation. Once an attacker gains system-level privileges, they can tamper with security controls, pivot more easily, and hide their activity with far fewer restrictions. The other concern is patch lag: broad Windows estates, especially those with legacy systems, rarely update all at once.- A low-privileged foothold can become SYSTEM access.
- Legacy Windows versions may stay exposed longer during rollout.
- Kernel exploitation can lead to security-tool tampering.
- Mixed fleet management increases the risk of partial remediation.
- Local EoP bugs are often chained into larger intrusion campaigns.
- Regression fears may slow patching in network-sensitive environments.
- Sparse public detail can create a false sense of ambiguity. (feedly.com)
Looking Ahead
What happens next will depend on how quickly Microsoft’s update is adopted and whether researchers eventually publish deeper technical analysis of the bug. If history is any guide, AFD.sys disclosures tend to attract more attention over time, not less, because the driver sits in a security-sensitive part of the Windows stack. That means defenders should expect the advisory to mature, not disappear.The most important operational question is whether CVE-2026-32073 remains a quiet patching item or becomes part of a broader exploitation campaign. If future telemetry shows exploitation attempts, that will instantly elevate urgency for organizations that delayed deployment. Until then, the rational stance is still to treat it as a high-priority local privilege escalation and close the gap before attackers do. (feedly.com)
- Verify whether April 14, 2026 updates are installed everywhere they should be.
- Prioritize servers, admin workstations, and high-value endpoints first.
- Watch for unusual local privilege changes and kernel instability.
- Review least-privilege policies for shared or overbroad user accounts.
- Prepare for follow-up technical reporting if researchers publish exploit details. (feedly.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center