Microsoft listed CVE-2026-34331 on May 12, 2026 as a Win32k elevation-of-privilege vulnerability in Windows, meaning a successful attacker would need some local foothold first but could potentially use the flaw to gain higher privileges on an affected system. That is not the kind of bug that lights up the internet like a wormable remote-code-execution flaw, but it is exactly the kind of bug that makes defenders nervous after an initial compromise. Win32k sits in the old, complicated, performance-sensitive part of Windows where user interface, graphics, and kernel privilege have been colliding for decades. The lesson is simple: this is a patch-now vulnerability not because Microsoft has told us every technical detail, but because the component and impact category have a long history of turning “local only” into “game over” inside real intrusions.
Elevation-of-privilege bugs have always suffered from a marketing problem. They do not usually let a stranger on the internet pop a server from across the world, and they do not sound as cinematic as a browser zero-click or an Exchange pre-authentication exploit. But in the post-phishing, post-token-theft, post-malware-loader world, privilege escalation is the second act of the attack — the moment when a nuisance becomes an administrator.
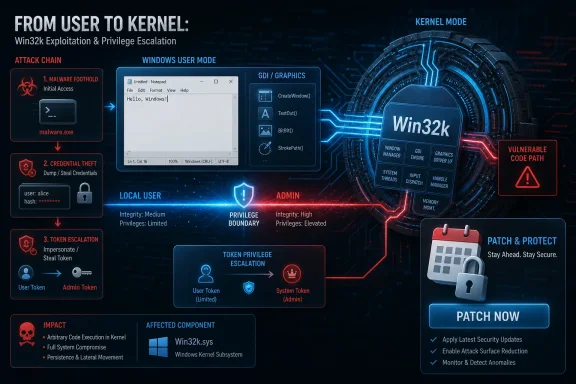
That framing matters for CVE-2026-34331. Microsoft’s title identifies the vulnerable component as Win32k and the impact as elevation of privilege. In plain English, an attacker would first need to be able to run code or otherwise interact locally on the machine, then exploit the flaw to cross a privilege boundary. For home users, that often means malware that escapes the limits of a standard account. For enterprises, it means an intruder who has landed on one endpoint and wants to disable security tooling, dump credentials, tamper with logs, or move laterally.
The uncomfortable part is that this is how many modern Windows compromises work. The initial entry point is frequently noisy and replaceable: a malicious attachment, a stolen password, a vulnerable VPN appliance, a fake installer, a drive-by exploit, or a user persuaded to run something they should not. The privilege escalation primitive is what gives that entry point staying power.
Microsoft’s public Security Update Guide entries are deliberately sparse compared with the old bulletin era. The company now leans on CVSS, exploitability assessments, affected product tables, and revision histories rather than long narrative descriptions. That makes sense for machine-readable patch management, but it leaves defenders reading between the lines. With CVE-2026-34331, the line worth reading is Win32k.
That design has been hardened repeatedly, but its basic risk profile is obvious. A subsystem that accepts complex inputs from ordinary desktop processes while maintaining privileged state is a natural target for local privilege escalation. Attackers love surfaces where low-privileged code can poke at high-privileged logic, especially when that logic has accumulated compatibility constraints over decades.
The Windows security story over the past 15 years is partly the story of Microsoft trying to put guardrails around exactly this kind of component. Kernel address randomization, stronger pool mitigations, Control Flow Guard, virtualization-based security, AppContainer isolation, browser sandboxes, and driver-signing rules have all raised the bar. But raising the bar is not the same as removing the surface. Win32k has remained a recurring name in Windows patch notes because it is both powerful and unavoidable.
This is where the “local” label can mislead casual readers. Local privilege escalation does not mean physically sitting at a keyboard. It means the attacker already has a way to execute code in a lower-privileged context. In corporate environments, that condition is not rare. It is often the attacker’s opening move.
For CVE-2026-34331, Microsoft’s acknowledgement is itself meaningful. Even if the public entry does not provide exploit code, root-cause analysis, or a proof-of-concept walkthrough, the presence of the CVE in Microsoft’s own guide tells defenders that this is not merely speculative chatter. The vendor is treating it as a real vulnerability requiring a security update.
That does not mean every attacker immediately has a working exploit. CVSS tries to separate several ideas that tend to blur together in headlines: severity, exploit maturity, remediation availability, and confidence. A bug can be severe but hard to exploit. A bug can be easy to exploit but unavailable to remote attackers. A bug can be fully confirmed while technical details remain private. Administrators who collapse all of that into a single score are effectively outsourcing judgment to a decimal.
The more useful question is how the vulnerability fits into an attacker’s chain. Win32k elevation-of-privilege issues tend to matter most when paired with something else. A browser sandbox escape, a malicious document, a compromised developer toolchain, or a low-privilege service account all become more dangerous when the attacker can climb into a stronger security context. The vulnerability is not necessarily the spear tip; it is the pry bar.
The Security Update Guide’s current style reflects Microsoft’s answer to that tension: structured metadata first, narrative second. Product teams, vulnerability scanners, and enterprise patch platforms can ingest CVE identifiers, affected builds, severity ratings, and remediation status. Humans get just enough context to know what class of bug they are looking at.
For a Win32k elevation-of-privilege flaw, that can feel unsatisfying. Sysadmins want to know whether standard users are exposed, whether exploitation requires a GUI session, whether Server Core is affected, whether Remote Desktop changes the calculus, whether mitigations reduce exposure, and whether any public proof of concept exists. Those details are not always present on day one, and sometimes they never arrive in a form that feels complete.
But sparse disclosure should not be confused with low importance. Microsoft has been steadily moving toward more standardized vulnerability descriptions, including CWE-style weakness mapping and CVSS fields, because the industry increasingly relies on automation to triage risk. That helps large organizations, but it also puts more burden on IT teams to understand what the fields imply. A confirmed EoP in a kernel-adjacent Windows component is rarely something to defer just because the prose is thin.
On a locked-down kiosk, the calculus may be different. On a developer workstation, it is worse. Developers often hold credentials, signing access, cloud tokens, package-manager permissions, and administrative exceptions that turn an endpoint compromise into a supply-chain incident. A local privilege escalation bug on a developer box is not just a local problem; it may be a bridge into build systems and production secrets.
Servers sit somewhere in the middle. A traditional Windows Server that does not expose desktop sessions and runs only a narrow set of services may have less obvious Win32k exposure than a heavily used Remote Desktop Session Host. But enterprises have a habit of turning servers into admin workstations, management consoles, print servers, legacy app hosts, and troubleshooting desktops. The moment interactive logon becomes routine, GUI subsystem bugs become more interesting.
Remote Desktop deserves particular attention. A vulnerability does not need to be remotely exploitable over the network to become relevant to remote operations. If a low-privileged domain account can log into a terminal server and trigger a local privilege escalation, the attack is still remote in the attacker’s lived experience. The boundary being crossed is local, but the blast radius is organizational.
This is especially true for components with a long vulnerability lineage. Researchers and exploit developers do not begin from zero every month. They bring harnesses, debugging setups, symbol knowledge, crash triage workflows, and prior exploit techniques. Even when mitigations change, the surrounding terrain is familiar.
That does not mean CVE-2026-34331 will necessarily be exploited in the wild. Many vulnerabilities never are, at least not publicly. Some are too brittle, too version-specific, too easily detected, or too hard to weaponize reliably. But defenders do not get to know that in advance.
The practical rule is dull but effective: patch before the exploit ecosystem catches up. For home systems, that usually means allowing Windows Update to do its job and rebooting promptly. For enterprises, it means getting the update into rings quickly, watching for regression signals, and avoiding the familiar trap of letting endpoint patches drift while server patches receive all the ceremony.
Credential theft, session hijacking, malicious OAuth grants, help-desk social engineering, poisoned installers, cracked software, and browser exploitation all create low-privileged footholds. Once that foothold exists, the attacker’s next problem is control. Can they persist? Can they evade EDR? Can they steal higher-value credentials? Can they tamper with backup agents or security logs? Privilege escalation answers those questions.
Windows has also become better at containing untrusted code, which paradoxically makes EoP bugs more valuable. Sandboxes, standard-user deployments, application control, and least-privilege policies all force attackers to find a way upward. When defenders do the right thing, the attacker’s dependency on privilege escalation increases.
That is why treating CVE-2026-34331 as “only local” misses the strategic picture. The bug’s value is not in starting an intrusion. Its value is in completing one. Security teams that prioritize only the first stage of an attack chain are defending the front door while leaving the staircase unguarded.
The consumer risk usually arrives bundled with something else. A trojanized game mod, fake driver updater, malicious archive, pirated application, or phishing attachment may land with ordinary user rights and then use a local bug to dig deeper. Once elevated, malware can tamper with security settings, install services, hide persistence mechanisms, and access data that should have remained outside its reach.
For enterprises, the work is more layered. Patch deployment is necessary, but so is measuring where the vulnerability would matter most if exploited. Devices used by administrators, developers, help desks, finance staff, and executives deserve closer attention than generic pooled machines. So do RDS hosts, VDI images, lab systems, and any endpoint class where users routinely run untrusted code.
There is also a telemetry angle. Security teams should watch for unusual child processes, privilege changes, suspicious driver interactions, tampering with endpoint protection, unexpected service creation, and credential-access behavior after patch release. Even without a public exploit, a Windows EoP disclosure can become a useful hunting prompt. The goal is not to invent indicators for a bug whose internals are not public; it is to look for the post-exploitation behavior that EoP enables.
Win32k vulnerabilities punish those habits because they live close to the everyday desktop experience. They are not isolated to a boutique server role or optional package that most organizations can remove. If an affected Windows build is in use, the bug is part of the platform unless Microsoft says otherwise.
The end of support cycles compound the problem. Unsupported Windows installations do not merely miss feature polish; they fall out of the security update stream that closes these flaws. Organizations still running old builds for industrial control, medical hardware, point-of-sale, or legacy application compatibility need compensating controls that are more serious than “it is behind the firewall.” Segmentation, application allowlisting, restricted interactive logon, and monitored jump paths become essential when timely patching is not realistic.
There is a cultural point here too. Windows administrators have learned to fear updates because updates sometimes break things. That fear is not irrational. But attackers benefit when the operational memory of a bad patch outweighs the security reality of an unpatched kernel-adjacent flaw.
Still, the best organizations use Patch Tuesday as a forcing function for broader hygiene. They do not simply ask whether the update installed; they ask why a low-privileged user could run arbitrary code on a sensitive machine in the first place. They ask whether administrators browse the web from privileged sessions. They ask whether developers have local admin by default. They ask whether RDS hosts are treated like Tier 0 assets when they effectively concentrate user execution and credentials.
Application control is one of the least glamorous but most relevant defenses. If only trusted code can run, the number of practical paths to exploit a local privilege escalation bug drops. It does not become zero, because trusted applications can be abused and signed malware exists, but the attacker's job gets harder.
Least privilege matters for the same reason. A local privilege escalation bug is more dangerous when every user already has broad local rights, because the environment has normalized privilege and made suspicious behavior harder to distinguish. Conversely, when privilege is rare, monitored, and time-bound, an unexpected jump stands out.
Virtualization-based security and modern hardware-backed protections can also raise the cost of exploitation, depending on the bug and configuration. They should not be treated as substitutes for the patch. Their value is in buying time, breaking exploit assumptions, and limiting what a successful attacker can do next.
CVE-2026-34331 belongs in that workflow. The affected component suggests broad Windows relevance. The impact suggests post-compromise escalation. The likely remediation path is the normal Windows security update channel. The absence of rich public detail means defenders should avoid overfitting their response to a guessed root cause.
This is where asset inventory becomes more than a compliance checkbox. If you cannot quickly answer which Windows builds are exposed, which devices have missed the latest cumulative update, and which endpoints are used by privileged staff, then the CVE’s severity score is almost beside the point. Your uncertainty is the risk multiplier.
Patch testing should be disciplined but not theatrical. A small ring of representative machines should catch obvious regressions. Security-sensitive cohorts should not wait weeks for perfect confidence. The longer a Win32k EoP patch sits unapplied, the more time attackers have to study the fix.
Report confidence reduces one slice of that uncertainty. Vendor acknowledgement means the vulnerability is real enough to patch. It does not reveal the exploit path, but it removes the “maybe this is theoretical” excuse.
That matters because organizations often delay patches when they cannot see a flashy exploit demo. In reality, the most useful security updates often arrive before public weaponization. Waiting for proof-of-concept code is a strategy for being late. By the time exploit details are easy to understand, they may also be easy to use.
Microsoft’s standardized language is therefore both dry and important. It gives defenders a way to reason about risk without needing every internal engineering detail. For CVE-2026-34331, the message is not that the sky is falling. It is that a confirmed privilege escalation issue in a historically sensitive Windows component has entered the patch queue, and mature defenders should treat that as enough.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 The Danger Is Not the Doorway, but What Comes After It
The Danger Is Not the Doorway, but What Comes After It
Elevation-of-privilege bugs have always suffered from a marketing problem. They do not usually let a stranger on the internet pop a server from across the world, and they do not sound as cinematic as a browser zero-click or an Exchange pre-authentication exploit. But in the post-phishing, post-token-theft, post-malware-loader world, privilege escalation is the second act of the attack — the moment when a nuisance becomes an administrator.That framing matters for CVE-2026-34331. Microsoft’s title identifies the vulnerable component as Win32k and the impact as elevation of privilege. In plain English, an attacker would first need to be able to run code or otherwise interact locally on the machine, then exploit the flaw to cross a privilege boundary. For home users, that often means malware that escapes the limits of a standard account. For enterprises, it means an intruder who has landed on one endpoint and wants to disable security tooling, dump credentials, tamper with logs, or move laterally.
The uncomfortable part is that this is how many modern Windows compromises work. The initial entry point is frequently noisy and replaceable: a malicious attachment, a stolen password, a vulnerable VPN appliance, a fake installer, a drive-by exploit, or a user persuaded to run something they should not. The privilege escalation primitive is what gives that entry point staying power.
Microsoft’s public Security Update Guide entries are deliberately sparse compared with the old bulletin era. The company now leans on CVSS, exploitability assessments, affected product tables, and revision histories rather than long narrative descriptions. That makes sense for machine-readable patch management, but it leaves defenders reading between the lines. With CVE-2026-34331, the line worth reading is Win32k.
Win32k Remains Windows’ Oldest Modern Attack Surface
Win32k is not some forgotten driver hiding in a dusty corner of the operating system. It is part of the Windows graphical subsystem, historically responsible for large pieces of the window manager and Graphics Device Interface machinery that connects user-mode applications to kernel-mode behavior. It exists because Windows has always cared about interactive performance, and interactive performance historically meant putting a lot of GUI functionality close to the kernel.That design has been hardened repeatedly, but its basic risk profile is obvious. A subsystem that accepts complex inputs from ordinary desktop processes while maintaining privileged state is a natural target for local privilege escalation. Attackers love surfaces where low-privileged code can poke at high-privileged logic, especially when that logic has accumulated compatibility constraints over decades.
The Windows security story over the past 15 years is partly the story of Microsoft trying to put guardrails around exactly this kind of component. Kernel address randomization, stronger pool mitigations, Control Flow Guard, virtualization-based security, AppContainer isolation, browser sandboxes, and driver-signing rules have all raised the bar. But raising the bar is not the same as removing the surface. Win32k has remained a recurring name in Windows patch notes because it is both powerful and unavoidable.
This is where the “local” label can mislead casual readers. Local privilege escalation does not mean physically sitting at a keyboard. It means the attacker already has a way to execute code in a lower-privileged context. In corporate environments, that condition is not rare. It is often the attacker’s opening move.
The CVSS Fine Print Is Doing More Work Than Usual
The user-supplied MSRC language about confidence in the vulnerability is the sort of paragraph many administrators skip, because it reads like standards prose rather than operational guidance. That would be a mistake. The Report Confidence metric measures how certain the industry is that the vulnerability exists and how credible the public technical details are. In practice, it helps distinguish rumor from confirmed vendor acknowledgement.For CVE-2026-34331, Microsoft’s acknowledgement is itself meaningful. Even if the public entry does not provide exploit code, root-cause analysis, or a proof-of-concept walkthrough, the presence of the CVE in Microsoft’s own guide tells defenders that this is not merely speculative chatter. The vendor is treating it as a real vulnerability requiring a security update.
That does not mean every attacker immediately has a working exploit. CVSS tries to separate several ideas that tend to blur together in headlines: severity, exploit maturity, remediation availability, and confidence. A bug can be severe but hard to exploit. A bug can be easy to exploit but unavailable to remote attackers. A bug can be fully confirmed while technical details remain private. Administrators who collapse all of that into a single score are effectively outsourcing judgment to a decimal.
The more useful question is how the vulnerability fits into an attacker’s chain. Win32k elevation-of-privilege issues tend to matter most when paired with something else. A browser sandbox escape, a malicious document, a compromised developer toolchain, or a low-privilege service account all become more dangerous when the attacker can climb into a stronger security context. The vulnerability is not necessarily the spear tip; it is the pry bar.
Microsoft’s Sparse Disclosure Is a Feature and a Friction Point
Security vendors disclose less than defenders want and more than attackers need. That tension is impossible to eliminate. If Microsoft publishes detailed root-cause analysis too early, it risks shortening the path from patch diff to weaponized exploit. If it publishes too little, administrators struggle to prioritize the update against a monthly pile of other fixes.The Security Update Guide’s current style reflects Microsoft’s answer to that tension: structured metadata first, narrative second. Product teams, vulnerability scanners, and enterprise patch platforms can ingest CVE identifiers, affected builds, severity ratings, and remediation status. Humans get just enough context to know what class of bug they are looking at.
For a Win32k elevation-of-privilege flaw, that can feel unsatisfying. Sysadmins want to know whether standard users are exposed, whether exploitation requires a GUI session, whether Server Core is affected, whether Remote Desktop changes the calculus, whether mitigations reduce exposure, and whether any public proof of concept exists. Those details are not always present on day one, and sometimes they never arrive in a form that feels complete.
But sparse disclosure should not be confused with low importance. Microsoft has been steadily moving toward more standardized vulnerability descriptions, including CWE-style weakness mapping and CVSS fields, because the industry increasingly relies on automation to triage risk. That helps large organizations, but it also puts more burden on IT teams to understand what the fields imply. A confirmed EoP in a kernel-adjacent Windows component is rarely something to defer just because the prose is thin.
The Real Patch Priority Depends on Who Can Log In
The most important operational question is not whether CVE-2026-34331 is “critical” in the headline sense. It is where low-privileged code can run in your environment. If many users can execute arbitrary applications, install browser extensions, run scripts, open Office attachments, or access shared jump hosts, then local privilege escalation bugs deserve high priority.On a locked-down kiosk, the calculus may be different. On a developer workstation, it is worse. Developers often hold credentials, signing access, cloud tokens, package-manager permissions, and administrative exceptions that turn an endpoint compromise into a supply-chain incident. A local privilege escalation bug on a developer box is not just a local problem; it may be a bridge into build systems and production secrets.
Servers sit somewhere in the middle. A traditional Windows Server that does not expose desktop sessions and runs only a narrow set of services may have less obvious Win32k exposure than a heavily used Remote Desktop Session Host. But enterprises have a habit of turning servers into admin workstations, management consoles, print servers, legacy app hosts, and troubleshooting desktops. The moment interactive logon becomes routine, GUI subsystem bugs become more interesting.
Remote Desktop deserves particular attention. A vulnerability does not need to be remotely exploitable over the network to become relevant to remote operations. If a low-privileged domain account can log into a terminal server and trigger a local privilege escalation, the attack is still remote in the attacker’s lived experience. The boundary being crossed is local, but the blast radius is organizational.
Exploitability Is a Race Against Patch Diffing
One reason Windows administrators cannot relax around Win32k bugs is patch diffing. Once Microsoft ships an update, attackers can compare old and new binaries, identify what changed, and work backward toward the vulnerable code path. That process is not magic, but it is routine enough that the window between patch release and working exploit can be short for bug classes attackers already understand.This is especially true for components with a long vulnerability lineage. Researchers and exploit developers do not begin from zero every month. They bring harnesses, debugging setups, symbol knowledge, crash triage workflows, and prior exploit techniques. Even when mitigations change, the surrounding terrain is familiar.
That does not mean CVE-2026-34331 will necessarily be exploited in the wild. Many vulnerabilities never are, at least not publicly. Some are too brittle, too version-specific, too easily detected, or too hard to weaponize reliably. But defenders do not get to know that in advance.
The practical rule is dull but effective: patch before the exploit ecosystem catches up. For home systems, that usually means allowing Windows Update to do its job and rebooting promptly. For enterprises, it means getting the update into rings quickly, watching for regression signals, and avoiding the familiar trap of letting endpoint patches drift while server patches receive all the ceremony.
The “Local Only” Comfort Blanket Has Worn Thin
There was a time when local privilege escalation bugs could be filed mentally below internet-facing vulnerabilities and left there. That hierarchy still has some truth. A wormable network service bug is an emergency in a way most EoP bugs are not. But the difference has narrowed because initial access has become cheap and abundant.Credential theft, session hijacking, malicious OAuth grants, help-desk social engineering, poisoned installers, cracked software, and browser exploitation all create low-privileged footholds. Once that foothold exists, the attacker’s next problem is control. Can they persist? Can they evade EDR? Can they steal higher-value credentials? Can they tamper with backup agents or security logs? Privilege escalation answers those questions.
Windows has also become better at containing untrusted code, which paradoxically makes EoP bugs more valuable. Sandboxes, standard-user deployments, application control, and least-privilege policies all force attackers to find a way upward. When defenders do the right thing, the attacker’s dependency on privilege escalation increases.
That is why treating CVE-2026-34331 as “only local” misses the strategic picture. The bug’s value is not in starting an intrusion. Its value is in completing one. Security teams that prioritize only the first stage of an attack chain are defending the front door while leaving the staircase unguarded.
Home Users Should Care, but Enterprises Should Care Differently
For individual Windows users, the advice is direct: install the security update, restart the machine, and do not assume that running as a standard user makes malware harmless. Standard accounts remain a good idea, but they are not a force field. An elevation-of-privilege flaw is precisely the category of bug that tries to erase the benefit of that separation.The consumer risk usually arrives bundled with something else. A trojanized game mod, fake driver updater, malicious archive, pirated application, or phishing attachment may land with ordinary user rights and then use a local bug to dig deeper. Once elevated, malware can tamper with security settings, install services, hide persistence mechanisms, and access data that should have remained outside its reach.
For enterprises, the work is more layered. Patch deployment is necessary, but so is measuring where the vulnerability would matter most if exploited. Devices used by administrators, developers, help desks, finance staff, and executives deserve closer attention than generic pooled machines. So do RDS hosts, VDI images, lab systems, and any endpoint class where users routinely run untrusted code.
There is also a telemetry angle. Security teams should watch for unusual child processes, privilege changes, suspicious driver interactions, tampering with endpoint protection, unexpected service creation, and credential-access behavior after patch release. Even without a public exploit, a Windows EoP disclosure can become a useful hunting prompt. The goal is not to invent indicators for a bug whose internals are not public; it is to look for the post-exploitation behavior that EoP enables.
Legacy Windows Habits Make Modern Bugs Worse
The hardest part of patching Windows is rarely the update itself. It is the ecosystem of exceptions built around the update process. A line-of-business application that breaks when patched. A lab image frozen for compatibility. A remote site with unreliable maintenance windows. A vendor appliance that is “Windows-based” until anyone asks who owns patching. A privileged workstation that nobody wants to reboot because it is always in use.Win32k vulnerabilities punish those habits because they live close to the everyday desktop experience. They are not isolated to a boutique server role or optional package that most organizations can remove. If an affected Windows build is in use, the bug is part of the platform unless Microsoft says otherwise.
The end of support cycles compound the problem. Unsupported Windows installations do not merely miss feature polish; they fall out of the security update stream that closes these flaws. Organizations still running old builds for industrial control, medical hardware, point-of-sale, or legacy application compatibility need compensating controls that are more serious than “it is behind the firewall.” Segmentation, application allowlisting, restricted interactive logon, and monitored jump paths become essential when timely patching is not realistic.
There is a cultural point here too. Windows administrators have learned to fear updates because updates sometimes break things. That fear is not irrational. But attackers benefit when the operational memory of a bad patch outweighs the security reality of an unpatched kernel-adjacent flaw.
The Patch Is Necessary, but It Is Not the Whole Control
The first control for CVE-2026-34331 is obvious: apply Microsoft’s security update for affected systems. Everything else is secondary. Mitigations may reduce exposure, and good architecture may reduce blast radius, but an unpatched vulnerability remains an unpatched vulnerability.Still, the best organizations use Patch Tuesday as a forcing function for broader hygiene. They do not simply ask whether the update installed; they ask why a low-privileged user could run arbitrary code on a sensitive machine in the first place. They ask whether administrators browse the web from privileged sessions. They ask whether developers have local admin by default. They ask whether RDS hosts are treated like Tier 0 assets when they effectively concentrate user execution and credentials.
Application control is one of the least glamorous but most relevant defenses. If only trusted code can run, the number of practical paths to exploit a local privilege escalation bug drops. It does not become zero, because trusted applications can be abused and signed malware exists, but the attacker's job gets harder.
Least privilege matters for the same reason. A local privilege escalation bug is more dangerous when every user already has broad local rights, because the environment has normalized privilege and made suspicious behavior harder to distinguish. Conversely, when privilege is rare, monitored, and time-bound, an unexpected jump stands out.
Virtualization-based security and modern hardware-backed protections can also raise the cost of exploitation, depending on the bug and configuration. They should not be treated as substitutes for the patch. Their value is in buying time, breaking exploit assumptions, and limiting what a successful attacker can do next.
Security Teams Should Read the CVE as a Workflow Trigger
A good vulnerability management program does not treat every CVE as an isolated ticket. It routes the CVE through context. Where are the affected assets? Who uses them? What privileges do those users have? Are they internet-facing, remotely accessible, or used for administration? Is exploitation known, likely, or merely plausible? What is the rollback plan if the patch causes trouble?CVE-2026-34331 belongs in that workflow. The affected component suggests broad Windows relevance. The impact suggests post-compromise escalation. The likely remediation path is the normal Windows security update channel. The absence of rich public detail means defenders should avoid overfitting their response to a guessed root cause.
This is where asset inventory becomes more than a compliance checkbox. If you cannot quickly answer which Windows builds are exposed, which devices have missed the latest cumulative update, and which endpoints are used by privileged staff, then the CVE’s severity score is almost beside the point. Your uncertainty is the risk multiplier.
Patch testing should be disciplined but not theatrical. A small ring of representative machines should catch obvious regressions. Security-sensitive cohorts should not wait weeks for perfect confidence. The longer a Win32k EoP patch sits unapplied, the more time attackers have to study the fix.
The Signal Hidden in Microsoft’s Confidence Language
The supplied MSRC text about confidence sounds abstract, but it points to a larger issue in vulnerability management: not all unknowns are equal. Sometimes defenders do not know whether a bug exists. Sometimes they know it exists but not how it works. Sometimes they know how it works but not whether attackers can weaponize it. Sometimes they know attackers can weaponize it but not whether anyone has done so.Report confidence reduces one slice of that uncertainty. Vendor acknowledgement means the vulnerability is real enough to patch. It does not reveal the exploit path, but it removes the “maybe this is theoretical” excuse.
That matters because organizations often delay patches when they cannot see a flashy exploit demo. In reality, the most useful security updates often arrive before public weaponization. Waiting for proof-of-concept code is a strategy for being late. By the time exploit details are easy to understand, they may also be easy to use.
Microsoft’s standardized language is therefore both dry and important. It gives defenders a way to reason about risk without needing every internal engineering detail. For CVE-2026-34331, the message is not that the sky is falling. It is that a confirmed privilege escalation issue in a historically sensitive Windows component has entered the patch queue, and mature defenders should treat that as enough.
The Admin’s Real Win Is Shortening the Exploit Window
The practical take from CVE-2026-34331 is not panic. It is speed with judgment. Patch the systems where user code and privilege intersect first, verify deployment, and use the event to clean up the habits that make local privilege escalation more damaging than it needs to be.- Apply the relevant Windows security update to affected systems as soon as testing permits, with special urgency for endpoints used by administrators, developers, and high-value business users.
- Treat Remote Desktop Session Hosts, VDI pools, and shared jump boxes as priority assets because local privilege escalation on those systems can have organization-wide consequences.
- Do not wait for public exploit code before acting, because patch diffing can turn sparse vendor details into attacker knowledge after release.
- Review where standard users can execute untrusted code, since reducing arbitrary code execution reduces the practical reach of local privilege escalation bugs.
- Monitor for post-exploitation behavior such as security-tool tampering, suspicious service creation, credential access, and unexpected privilege changes rather than trying to guess the undisclosed root cause.
- Use this patch cycle to verify inventory accuracy, reboot compliance, and exception handling for Windows systems that routinely fall behind cumulative updates.
Source: MSRC Security Update Guide - Microsoft Security Response Center