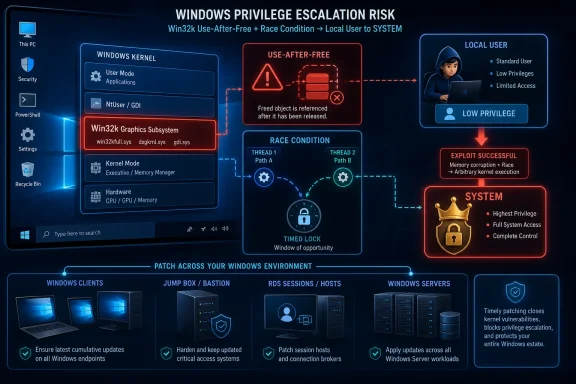
Microsoft disclosed CVE-2026-34347 on May 12, 2026, as an Important-rated Windows Win32k elevation-of-privilege vulnerability in which a local, authenticated attacker could exploit a use-after-free flaw in the Win32K graphics subsystem to gain SYSTEM privileges after winning a race condition. The useful news is that Microsoft says the flaw was not publicly disclosed or exploited when published. The uncomfortable news is that it sits in exactly the kind of local Windows attack surface that turns an initial foothold into full machine control. This is not a panic patch, but it is very much a patch-now item for administrators who understand how often “local only” becomes “the second stage of the breach.”
The headline severity for CVE-2026-34347 is “Important,” not “Critical,” and that distinction matters in Microsoft’s taxonomy. The bug is not remotely exploitable over the network, does not require a victim to click a lure, and is rated with high attack complexity. On paper, that keeps it below the worst class of Patch Tuesday emergencies.
But the privilege boundary at stake is severe. Microsoft’s advisory says a successful attacker could gain SYSTEM privileges, the highest practical level of authority on a Windows host. Once code is running as SYSTEM, many of the distinctions users care about — files, credentials, security tooling, persistence mechanisms, and local policy — become negotiable.
That is why local elevation-of-privilege bugs deserve more respect than their severity labels sometimes receive. They rarely start an intrusion by themselves. They finish the job after phishing, credential theft, malicious document execution, exposed remote access, or exploitation of a browser or application sandbox has already put code on the box.
CVE-2026-34347 is a reminder that Windows risk is often chained risk. The first bug gets the attacker in; the second bug decides whether the attacker remains a nuisance or becomes the operating system.
Microsoft describes this vulnerability as a use-after-free issue in Windows Win32K - GRFX. In plain English, that means some code path may continue to reference memory after it should no longer be trusted, creating the possibility that an attacker can manipulate what gets used in its place. That is one of the classic memory-safety failure modes, and in kernel-adjacent or graphics-related Windows components it has a long history of attracting serious exploit research.
The advisory also says successful exploitation requires winning a race condition. That phrase is doing a lot of work. It means exploitation depends on timing and state, not simply sending a cleanly formed input and receiving a predictable compromise. Race bugs can be unstable, noisy, and highly dependent on system behavior.
Yet high complexity should not be mistaken for impossibility. Attackers with enough motivation often turn unreliable primitives into reliable tools, especially when the reward is SYSTEM. Microsoft’s own “Exploitation Less Likely” assessment is reassuring only in the narrow sense that the company did not see a ready public exploit or active abuse at publication time.
The “low privileges required” part is the one defenders should linger on. An attacker does not need administrator rights before exploiting the vulnerability. A standard user context may be enough, which is precisely why these bugs are useful after an initial compromise.
The “no user interaction” metric is equally important. Once an attacker is already executing locally with low privileges, the advisory does not describe a need to trick another user into doing something. That makes the vulnerability more attractive for automated post-exploitation workflows, even if the race condition raises the engineering bar.
The high impact ratings across confidentiality, integrity, and availability reflect the consequence of successful privilege escalation. A local exploit that becomes SYSTEM is not merely about reading someone else’s files. It can enable tampering, disabling protections, installing services, dumping secrets, and establishing persistence.
That confidence changes the defender’s calculus. A vulnerability with sketchy details may remain mostly academic until researchers or attackers work out the missing pieces. A confirmed vendor advisory tells defenders and attackers alike that the bug is real, the affected surface exists, and a fix shipped because Microsoft believes the issue crosses a security boundary.
The flip side is that exploit code maturity is listed as Unproven. Microsoft says there was no public disclosure and no exploitation observed at the time of original publication. The practical message is not “ignore it”; it is “patch before exploit maturity changes.”
That distinction is where good vulnerability management separates itself from score-chasing. Waiting for exploitation to become public is a defensible strategy only if an organization has compensating controls, rapid deployment capacity, and an accurate asset inventory. Many environments have none of those things.
The affected product table also shows customer action required. In other words, this is not merely a documentation update or a cloud-side remediation invisible to administrators. Systems need the relevant cumulative update, rollup, security update, or hotpatch where applicable.
For desktop fleets, the primary concern is update compliance across roaming laptops, lightly managed endpoints, and machines that miss monthly maintenance windows. For servers, the risk discussion is more subtle. Many admins instinctively discount Win32k issues on server systems, especially Server Core installations, but Microsoft’s affected products include Server Core variants. If Microsoft lists the product as affected and action required, assume the component exposure is sufficient to warrant remediation.
Hotpatch entries for some server releases also show how Microsoft’s servicing model is changing. Hotpatching can reduce reboot pressure, but it does not remove the need for disciplined patch governance. A hotpatch that is not deployed is still an absent fix.
Local elevation bugs are force multipliers. They let malware escape the permissions of the compromised user. They help an attacker defeat endpoint protections that rely on user-mode visibility. They allow credential theft from memory or protected locations. They turn a developer workstation, help desk machine, or shared server session into something far more valuable.
The risk is especially acute in environments where users retain broad local rights or where endpoint isolation is weak. Ironically, organizations that have done the right thing by restricting administrator privileges may find standard-user-to-SYSTEM bugs more consequential because they bypass a core control. Least privilege still matters, but it is not a replacement for patching kernel and graphics subsystem flaws.
There is also the matter of timing. Microsoft released the advisory and fixes on May 12, 2026, Patch Tuesday. That means attackers can begin comparing patched and unpatched binaries almost immediately. For bugs in widely deployed Windows components, reverse engineering the patch is often the first step toward understanding the exploit path.
The gap between “hard to exploit” and “usable in an intrusion” can close quickly when a vulnerability offers a valuable privilege gain. Attackers do not need an exploit to work perfectly on every machine. They need it to work often enough against the subset of targets where the payoff justifies the engineering effort.
There is another wrinkle: local attackers can often shape the local environment. They may be able to spawn processes, influence timing, consume resources, retry repeatedly, and tailor their exploit to the exact Windows build. That does not erase the complexity rating, but it changes the practical meaning of “high.”
The correct operational interpretation is that CVE-2026-34347 is less likely to be the first vulnerability exploited at scale and more likely to become part of a selective chain if exploit details mature. That is still enough reason to prioritize it inside normal Patch Tuesday windows.
The advisory’s chronology supports that boring-but-good story. Version 1.0 was published on May 12, 2026, with no public disclosure and no observed exploitation listed. For defenders, that is the window in which patch management is supposed to work.
The problem is that many organizations are no longer operating with a comfortable monthly window. Attackers study Patch Tuesday, security vendors summarize it within hours, and proof-of-concept development can follow quickly when the bug class is familiar. A confirmed use-after-free in a Windows graphics path with SYSTEM as the reward is exactly the sort of item that will be watched.
That does not mean every Windows shop should declare an emergency change freeze exception. It does mean that treating this as just another “Important” entry in a long spreadsheet misses the value attackers place on privilege escalation.
Organizations with mature patch rings should push the relevant cumulative updates through pilot groups quickly, watch for known issues, and expand deployment without waiting for exploit chatter. Those using Windows Server hotpatching should verify that the hotpatch path actually lands on the affected machines and does not leave a parallel group waiting for the next reboot-based baseline.
Security teams should also look at exposure, not just inventory. A file server with no interactive users has a different risk profile from a remote desktop host used by contractors. A developer laptop with local build tools, secrets, and browser sessions is a richer target than a locked-down single-purpose workstation. The same CVE can justify different urgency across the estate.
For detection teams, the immediate challenge is that privilege escalation attempts may not have a clean, public signature. Until more technical details emerge, monitoring should focus on suspicious local privilege transitions, unusual child processes spawned from user contexts into privileged services, tampering with endpoint protection, and post-exploitation behavior rather than a single magic indicator.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft’s “Important” Label Hides a SYSTEM-Sized Consequence
Microsoft’s “Important” Label Hides a SYSTEM-Sized Consequence
The headline severity for CVE-2026-34347 is “Important,” not “Critical,” and that distinction matters in Microsoft’s taxonomy. The bug is not remotely exploitable over the network, does not require a victim to click a lure, and is rated with high attack complexity. On paper, that keeps it below the worst class of Patch Tuesday emergencies.But the privilege boundary at stake is severe. Microsoft’s advisory says a successful attacker could gain SYSTEM privileges, the highest practical level of authority on a Windows host. Once code is running as SYSTEM, many of the distinctions users care about — files, credentials, security tooling, persistence mechanisms, and local policy — become negotiable.
That is why local elevation-of-privilege bugs deserve more respect than their severity labels sometimes receive. They rarely start an intrusion by themselves. They finish the job after phishing, credential theft, malicious document execution, exposed remote access, or exploitation of a browser or application sandbox has already put code on the box.
CVE-2026-34347 is a reminder that Windows risk is often chained risk. The first bug gets the attacker in; the second bug decides whether the attacker remains a nuisance or becomes the operating system.
Win32k Remains the Old Door Everyone Still Has to Use
Win32k is one of Windows’ most enduring compatibility bargains. It supports the user interface and graphics paths that let decades of Windows software continue to work, and that longevity gives it both value and risk. When a flaw lands in Win32k, it lands in code that is deeply embedded in the desktop experience rather than some optional component few machines run.Microsoft describes this vulnerability as a use-after-free issue in Windows Win32K - GRFX. In plain English, that means some code path may continue to reference memory after it should no longer be trusted, creating the possibility that an attacker can manipulate what gets used in its place. That is one of the classic memory-safety failure modes, and in kernel-adjacent or graphics-related Windows components it has a long history of attracting serious exploit research.
The advisory also says successful exploitation requires winning a race condition. That phrase is doing a lot of work. It means exploitation depends on timing and state, not simply sending a cleanly formed input and receiving a predictable compromise. Race bugs can be unstable, noisy, and highly dependent on system behavior.
Yet high complexity should not be mistaken for impossibility. Attackers with enough motivation often turn unreliable primitives into reliable tools, especially when the reward is SYSTEM. Microsoft’s own “Exploitation Less Likely” assessment is reassuring only in the narrow sense that the company did not see a ready public exploit or active abuse at publication time.
The CVSS Vector Tells a More Nuanced Story Than the Score
The CVSS base score for CVE-2026-34347 is 7.0, with a temporal score of 6.1. The vector tells the real story: local attack vector, high complexity, low privileges required, no user interaction, unchanged scope, and high impact to confidentiality, integrity, and availability. That is not a remote worm scenario, but it is also not a theoretical paper cut.The “low privileges required” part is the one defenders should linger on. An attacker does not need administrator rights before exploiting the vulnerability. A standard user context may be enough, which is precisely why these bugs are useful after an initial compromise.
The “no user interaction” metric is equally important. Once an attacker is already executing locally with low privileges, the advisory does not describe a need to trick another user into doing something. That makes the vulnerability more attractive for automated post-exploitation workflows, even if the race condition raises the engineering bar.
The high impact ratings across confidentiality, integrity, and availability reflect the consequence of successful privilege escalation. A local exploit that becomes SYSTEM is not merely about reading someone else’s files. It can enable tampering, disabling protections, installing services, dumping secrets, and establishing persistence.
The Confirmed Report Matters Because Attackers Read the Same Tea Leaves
The user-provided metric text is not filler; it is central to understanding this advisory. Microsoft marks report confidence as Confirmed, meaning the vulnerability’s existence is not just rumored or inferred. Either detailed reports exist, reproduction is possible, source-level confirmation exists, or the vendor has confirmed the issue.That confidence changes the defender’s calculus. A vulnerability with sketchy details may remain mostly academic until researchers or attackers work out the missing pieces. A confirmed vendor advisory tells defenders and attackers alike that the bug is real, the affected surface exists, and a fix shipped because Microsoft believes the issue crosses a security boundary.
The flip side is that exploit code maturity is listed as Unproven. Microsoft says there was no public disclosure and no exploitation observed at the time of original publication. The practical message is not “ignore it”; it is “patch before exploit maturity changes.”
That distinction is where good vulnerability management separates itself from score-chasing. Waiting for exploitation to become public is a defensible strategy only if an organization has compensating controls, rapid deployment capacity, and an accurate asset inventory. Many environments have none of those things.
The Patch Footprint Runs Across the Windows Estate
The security update list spans modern client and server versions, including Windows 10, Windows 11, Windows Server 2012 and 2012 R2 under their applicable servicing arrangements, Windows Server 2016, Windows Server 2019, Windows Server 2022, Windows Server 2025, and newer Windows 11 versions listed in the advisory. That breadth is unsurprising for a Win32k issue, but it makes the operational burden real.The affected product table also shows customer action required. In other words, this is not merely a documentation update or a cloud-side remediation invisible to administrators. Systems need the relevant cumulative update, rollup, security update, or hotpatch where applicable.
For desktop fleets, the primary concern is update compliance across roaming laptops, lightly managed endpoints, and machines that miss monthly maintenance windows. For servers, the risk discussion is more subtle. Many admins instinctively discount Win32k issues on server systems, especially Server Core installations, but Microsoft’s affected products include Server Core variants. If Microsoft lists the product as affected and action required, assume the component exposure is sufficient to warrant remediation.
Hotpatch entries for some server releases also show how Microsoft’s servicing model is changing. Hotpatching can reduce reboot pressure, but it does not remove the need for disciplined patch governance. A hotpatch that is not deployed is still an absent fix.
“Local” Does Not Mean “Low Priority” in 2026
One of the oldest mistakes in patch triage is treating local privilege escalation as a lower class of vulnerability because it cannot be reached directly from the Internet. That view made more sense when the main threat model was a single exposed service being attacked from afar. It fits poorly with modern intrusions, where identity compromise, endpoint malware, living-off-the-land tooling, and SaaS-to-device pivots are routine.Local elevation bugs are force multipliers. They let malware escape the permissions of the compromised user. They help an attacker defeat endpoint protections that rely on user-mode visibility. They allow credential theft from memory or protected locations. They turn a developer workstation, help desk machine, or shared server session into something far more valuable.
The risk is especially acute in environments where users retain broad local rights or where endpoint isolation is weak. Ironically, organizations that have done the right thing by restricting administrator privileges may find standard-user-to-SYSTEM bugs more consequential because they bypass a core control. Least privilege still matters, but it is not a replacement for patching kernel and graphics subsystem flaws.
There is also the matter of timing. Microsoft released the advisory and fixes on May 12, 2026, Patch Tuesday. That means attackers can begin comparing patched and unpatched binaries almost immediately. For bugs in widely deployed Windows components, reverse engineering the patch is often the first step toward understanding the exploit path.
Race Conditions Are Hard Until They Are Productized
Microsoft’s note that exploitation requires winning a race condition is meaningful, but it should not lull defenders. Race conditions often begin life as fragile lab curiosities. Over time, researchers learn which scheduler behaviors matter, which calls improve reliability, and which system loads make exploitation more predictable.The gap between “hard to exploit” and “usable in an intrusion” can close quickly when a vulnerability offers a valuable privilege gain. Attackers do not need an exploit to work perfectly on every machine. They need it to work often enough against the subset of targets where the payoff justifies the engineering effort.
There is another wrinkle: local attackers can often shape the local environment. They may be able to spawn processes, influence timing, consume resources, retry repeatedly, and tailor their exploit to the exact Windows build. That does not erase the complexity rating, but it changes the practical meaning of “high.”
The correct operational interpretation is that CVE-2026-34347 is less likely to be the first vulnerability exploited at scale and more likely to become part of a selective chain if exploit details mature. That is still enough reason to prioritize it inside normal Patch Tuesday windows.
The Research Credit Points to Coordinated Disclosure Doing Its Job
Microsoft credits wenqunwang with China Telecom Research Institute for reporting the issue. That matters because coordinated vulnerability disclosure is the quiet machinery behind many Patch Tuesday fixes. The best outcome for a bug like this is boring: a researcher reports it, Microsoft validates it, customers receive patches, and no public exploit race erupts before administrators have time to respond.The advisory’s chronology supports that boring-but-good story. Version 1.0 was published on May 12, 2026, with no public disclosure and no observed exploitation listed. For defenders, that is the window in which patch management is supposed to work.
The problem is that many organizations are no longer operating with a comfortable monthly window. Attackers study Patch Tuesday, security vendors summarize it within hours, and proof-of-concept development can follow quickly when the bug class is familiar. A confirmed use-after-free in a Windows graphics path with SYSTEM as the reward is exactly the sort of item that will be watched.
That does not mean every Windows shop should declare an emergency change freeze exception. It does mean that treating this as just another “Important” entry in a long spreadsheet misses the value attackers place on privilege escalation.
Where Administrators Should Put This in the Queue
The sensible response is neither panic nor procrastination. CVE-2026-34347 should sit high in the May 2026 Windows patch queue, especially for endpoints and servers where local code execution by untrusted or semi-trusted users is plausible. That includes VDI farms, jump boxes, developer machines, shared workstations, RDS environments, kiosks with weak containment, and servers where non-admin users can log on interactively or run workloads.Organizations with mature patch rings should push the relevant cumulative updates through pilot groups quickly, watch for known issues, and expand deployment without waiting for exploit chatter. Those using Windows Server hotpatching should verify that the hotpatch path actually lands on the affected machines and does not leave a parallel group waiting for the next reboot-based baseline.
Security teams should also look at exposure, not just inventory. A file server with no interactive users has a different risk profile from a remote desktop host used by contractors. A developer laptop with local build tools, secrets, and browser sessions is a richer target than a locked-down single-purpose workstation. The same CVE can justify different urgency across the estate.
For detection teams, the immediate challenge is that privilege escalation attempts may not have a clean, public signature. Until more technical details emerge, monitoring should focus on suspicious local privilege transitions, unusual child processes spawned from user contexts into privileged services, tampering with endpoint protection, and post-exploitation behavior rather than a single magic indicator.
The May Patch Triage Should Not Stop at the Score
Here is the compact version for WindowsForum readers sorting the May 2026 updates into action:- CVE-2026-34347 is a confirmed Windows Win32k use-after-free vulnerability disclosed by Microsoft on May 12, 2026.
- Microsoft rates the issue Important with a CVSS base score of 7.0 and says successful exploitation could grant SYSTEM privileges.
- The attack is local, requires low privileges, needs no user interaction, and depends on winning a race condition.
- Microsoft said the vulnerability was not publicly disclosed and not exploited at the time of original publication, with exploitation assessed as less likely.
- Affected products span Windows client and server releases, and Microsoft marks customer action as required for the listed updates.
- Administrators should prioritize systems where standard users, remote desktop users, contractors, developers, or untrusted workloads can execute code locally.
Source: MSRC Security Update Guide - Microsoft Security Response Center