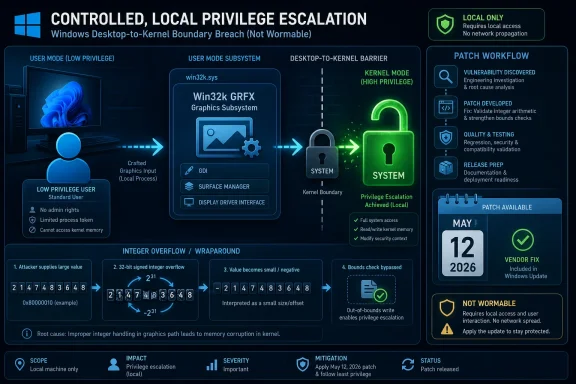
Microsoft disclosed CVE-2026-34330 on May 12, 2026, as an Important-rated Windows Win32k elevation-of-privilege flaw in the GRFX component that can let a locally authenticated attacker gain SYSTEM privileges after exploiting an integer overflow or wraparound weakness. The advisory is not screaming “wormable,” and Microsoft says exploitation is unlikely at publication. But the useful signal for defenders is not the headline severity; it is the combination of local attack, low complexity, confirmed reporting, and a completed vendor fix. This is the sort of Windows bug that rarely wins the news cycle, yet often matters deeply once an attacker already has a foothold.
CVE-2026-34330 sits in the familiar but uncomfortable category of Windows local privilege escalation. It does not give an unauthenticated attacker a path in from the internet. It does not require a user to open a poisoned document. It does, however, potentially turn a low-privileged account on a Windows machine into SYSTEM, which is the line every endpoint defense stack is trying to prevent an intruder from crossing.
Microsoft’s own scoring tells the story. The vulnerability carries a CVSS 3.1 base score of 7.8, with local attack vector, low attack complexity, low privileges required, no user interaction, and high impact to confidentiality, integrity, and availability. That profile is not exotic; it is the standard shape of a practical post-compromise escalation bug.
The advisory also identifies two weakness classes: integer overflow or wraparound and use-after-free. Microsoft’s summary specifically names integer overflow or wraparound in Windows Win32K GRFX as the route to local privilege escalation, while the weakness list includes both CWE-190 and CWE-416. That pairing suggests memory-safety territory in a subsystem whose job is old, performance-sensitive, and historically hard to make boring.
The vendor’s exploitability judgment is calmer. Microsoft marks the bug as not publicly disclosed, not exploited, and “exploitation unlikely” at original publication. For patch managers, that should lower panic, not priority. The right reading is “patch in the normal security cycle unless your environment has elevated exposure,” not “ignore until someone publishes a proof of concept.”
The GRFX label in Microsoft’s advisory points toward the graphics side of this subsystem, which is exactly where complexity tends to accumulate. Rendering paths, object lifetimes, integer calculations, and kernel/user transitions are a hostile mix. A local attacker does not need the bug to be reachable from the public internet if malware, a malicious insider, a compromised remote desktop session, or a hijacked low-privilege account can reach the vulnerable code path locally.
This is why Windows elevation-of-privilege bugs are so often underestimated by people who only look at initial access. In a real intrusion, attackers chain stages. Phishing, stolen credentials, exposed services, malicious installers, browser escapes, and supply-chain compromises are the doorways; local privilege escalation is what turns a doorway into ownership.
That distinction matters for WindowsForum readers because many of the affected systems are endpoints and servers that already face authenticated use. Developers run code. Help-desk staff remote into machines. Users install tools. Servers host scheduled tasks and service accounts. A local-only bug is still reachable in the messy, authenticated world where most Windows estates actually operate.
A confirmed report does not mean exploit code is circulating. Microsoft separately marks exploit code maturity as unproven, and the advisory says there is no known public disclosure or exploitation at the time of release. But confirmed report confidence does mean defenders should treat the underlying condition as real. It is not a theoretical class of bug in a whitepaper; Microsoft has acknowledged the vulnerability and shipped a fix.
The combination of “confirmed” and “unproven” is the classic Patch Tuesday gray zone. Attackers may not have a public recipe today, but they have a diff once updates are released. Security researchers and adversaries alike can compare patched and unpatched binaries, especially for widely deployed Windows components. That does not guarantee weaponization, but it makes delay less attractive.
This is also why Microsoft’s “exploitation unlikely” label should be read as a probability estimate, not a promise. Exploitability assessments are snapshots at publication time. They help triage a crowded month; they do not freeze attacker economics. A local privilege escalation bug that reaches SYSTEM can become more interesting if it pairs neatly with another vulnerability or a commodity malware operator finds a reliable trigger.
That breadth matters less because every one of those machines has the same risk profile and more because most mixed Windows environments contain some of them. A desktop team may see this as a Windows 11 cumulative update issue. A server team may see hotpatch entries for newer server builds. A legacy operations group may see monthly rollups for older Server 2012-era systems still hanging around under extended support arrangements.
The fixed build numbers are similarly concrete. Windows 11 24H2 systems move to fixed builds in the 26100.8457 or hotpatch 26100.8390 range, while Windows 11 25H2 systems move to corresponding 26200 builds. Windows 10 22H2 receives build 19045.7291, and Server 2025 entries include 26100.32860 or hotpatch 26100.32772 depending on update path.
For administrators, the lesson is not to memorize every build. The lesson is to verify that update compliance tools are actually distinguishing between the full cumulative security update and hotpatch channels where both appear. A dashboard that says “patched” without surfacing build numbers can hide awkward exceptions.
But hotpatching does not turn security maintenance into a passive background event. It still requires eligibility, correct servicing configuration, and validation that the machine actually received the intended build. The risk for enterprises is that hotpatching becomes a comforting noun on a roadmap rather than an observed state on each server.
CVE-2026-34330 is a good example of why that distinction matters. A local privilege escalation flaw may not force an emergency reboot across the estate, but it should still close within defined patch windows. If hotpatching helps meet that window without downtime, excellent. If hotpatching creates a second lane that asset owners do not understand, it can become another source of drift.
The practical approach is simple: treat hotpatch and cumulative update paths as different delivery mechanisms for the same security requirement. Validate by build, not by expectation. If a system is in a hotpatch cohort, confirm it landed on the hotpatch build Microsoft lists. If it is not, confirm the standard security update build.
SYSTEM access can let an attacker tamper with security tools, harvest credentials from local stores or memory-adjacent contexts, install persistence, access protected files, and move laterally with better leverage. Endpoint detection and response products are designed to resist that outcome, but they do not make it irrelevant. Any local escalation to SYSTEM should be treated as a serious post-compromise accelerant.
This is especially relevant on shared systems, jump boxes, developer workstations, and servers that host multiple roles. A low-privileged context on a normal laptop may already be bad. A low-privileged context on an administrative workstation is worse. A low-privileged context on a server with sensitive service accounts or management tooling can be the bridge to a larger compromise.
The nuance is that CVE-2026-34330 is not itself an initial access story. It is a privilege story. That means defenders should align mitigation with the kill chain: reduce initial footholds, restrict local code execution, monitor suspicious privilege transitions, and patch the kernel boundary so attackers have one fewer rung to climb.
For small businesses, the question is whether devices are actually checking in and completing updates. Laptops that sleep through maintenance windows, remote machines that live off VPN, and unmanaged contractor devices are the usual gaps. A local privilege escalation flaw becomes more dangerous when those endpoints are also the machines most likely to encounter untrusted files, browsers, and third-party tools.
For enterprises, the decision is less about whether to patch and more about sequencing. Domain controllers are not the obvious first concern for a Win32k graphics flaw unless the vulnerable component is present and reachable, but administrative workstations, RDS hosts, VDI images, developer boxes, and general-purpose servers deserve attention. Any machine where a low-privilege session coexists with sensitive credentials or admin tooling is a more attractive escalation target.
Testing remains necessary. Graphics and kernel-mode changes can trigger compatibility concerns, especially with display drivers, remote graphics stacks, security agents, and virtualization layers. But the answer to compatibility risk is staged deployment and telemetry, not indefinite deferral.
Coordinated disclosure can feel slow from the outside because users see the CVE only when the fix is ready. In this case, that timing is a strength. Microsoft published the advisory with an official fix available, no known public disclosure, no known exploitation, and confirmed confidence in the report. That is the best ordinary-case outcome for a Windows kernel-adjacent flaw.
The uncomfortable part is that defenders only enter the story at the end. Once the patch exists, the clock changes. Attackers can begin studying the fix. Security vendors can begin writing detections. Administrators can begin testing and deploying. The advisory may be calm, but the public timeline has started.
That is why confirmed report confidence is a double-edged signal. It reassures defenders that the bug is real and fixed. It also tells capable attackers that there is something concrete to investigate.
The first priority should be systems where local low-privilege access is common and privilege escalation would be especially damaging. Remote Desktop Session Hosts, VDI pools, shared engineering workstations, build servers, help-desk machines, and administrative jump boxes all fit that pattern. Those are the environments where “local only” can still mean “reachable by many.”
The second priority is systems that are hard to patch later. Older Windows Server versions, specialized workloads, and machines tied to maintenance windows should be identified early, because their friction is predictable. If they are still supported through extended programs, they need the relevant monthly rollup or security update. If they are not supported, the conversation should move from patching to isolation and retirement.
The third priority is evidence. Patch compliance should be measured by installed KB and build number, not by assumptions about update rings. CVE-driven reporting is useful only when it maps to actual assets. The existence of 31 affected rows in Microsoft’s table is a reminder that “Windows” is not one target; it is a fleet of servicing channels, architectures, and support states.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft’s Quiet Patch Still Points at a Serious Windows Boundary
Microsoft’s Quiet Patch Still Points at a Serious Windows Boundary
CVE-2026-34330 sits in the familiar but uncomfortable category of Windows local privilege escalation. It does not give an unauthenticated attacker a path in from the internet. It does not require a user to open a poisoned document. It does, however, potentially turn a low-privileged account on a Windows machine into SYSTEM, which is the line every endpoint defense stack is trying to prevent an intruder from crossing.Microsoft’s own scoring tells the story. The vulnerability carries a CVSS 3.1 base score of 7.8, with local attack vector, low attack complexity, low privileges required, no user interaction, and high impact to confidentiality, integrity, and availability. That profile is not exotic; it is the standard shape of a practical post-compromise escalation bug.
The advisory also identifies two weakness classes: integer overflow or wraparound and use-after-free. Microsoft’s summary specifically names integer overflow or wraparound in Windows Win32K GRFX as the route to local privilege escalation, while the weakness list includes both CWE-190 and CWE-416. That pairing suggests memory-safety territory in a subsystem whose job is old, performance-sensitive, and historically hard to make boring.
The vendor’s exploitability judgment is calmer. Microsoft marks the bug as not publicly disclosed, not exploited, and “exploitation unlikely” at original publication. For patch managers, that should lower panic, not priority. The right reading is “patch in the normal security cycle unless your environment has elevated exposure,” not “ignore until someone publishes a proof of concept.”
Win32k Remains the Place Where Old Windows Meets New Attack Chains
Win32k has always been one of the most consequential pieces of Windows plumbing because it lives near the junction of user interaction, graphics, window management, and kernel-mode privilege. Modern Windows has spent years trying to shrink and harden that surface, but the surface has not vanished. If anything, every Win32k CVE is a reminder that compatibility is a security inheritance.The GRFX label in Microsoft’s advisory points toward the graphics side of this subsystem, which is exactly where complexity tends to accumulate. Rendering paths, object lifetimes, integer calculations, and kernel/user transitions are a hostile mix. A local attacker does not need the bug to be reachable from the public internet if malware, a malicious insider, a compromised remote desktop session, or a hijacked low-privilege account can reach the vulnerable code path locally.
This is why Windows elevation-of-privilege bugs are so often underestimated by people who only look at initial access. In a real intrusion, attackers chain stages. Phishing, stolen credentials, exposed services, malicious installers, browser escapes, and supply-chain compromises are the doorways; local privilege escalation is what turns a doorway into ownership.
That distinction matters for WindowsForum readers because many of the affected systems are endpoints and servers that already face authenticated use. Developers run code. Help-desk staff remote into machines. Users install tools. Servers host scheduled tasks and service accounts. A local-only bug is still reachable in the messy, authenticated world where most Windows estates actually operate.
“Confirmed” Is the Metric Defenders Should Not Skip
The user-supplied text focuses on report confidence, and in this case Microsoft marks the report confidence as confirmed. That is a meaningful operational signal. It means the vulnerability is not merely rumored, vaguely inferred, or described by a third party without vendor validation.A confirmed report does not mean exploit code is circulating. Microsoft separately marks exploit code maturity as unproven, and the advisory says there is no known public disclosure or exploitation at the time of release. But confirmed report confidence does mean defenders should treat the underlying condition as real. It is not a theoretical class of bug in a whitepaper; Microsoft has acknowledged the vulnerability and shipped a fix.
The combination of “confirmed” and “unproven” is the classic Patch Tuesday gray zone. Attackers may not have a public recipe today, but they have a diff once updates are released. Security researchers and adversaries alike can compare patched and unpatched binaries, especially for widely deployed Windows components. That does not guarantee weaponization, but it makes delay less attractive.
This is also why Microsoft’s “exploitation unlikely” label should be read as a probability estimate, not a promise. Exploitability assessments are snapshots at publication time. They help triage a crowded month; they do not freeze attacker economics. A local privilege escalation bug that reaches SYSTEM can become more interesting if it pairs neatly with another vulnerability or a commodity malware operator finds a reliable trigger.
The Affected Platform List Is Broad Enough to Matter
CVE-2026-34330 affects a wide span of supported Windows client and server releases. Microsoft lists updates for Windows 11 versions 23H2, 24H2, 25H2, and 26H1 across x64 and ARM64 variants, along with Windows 10 versions including 22H2, 21H2, 1809, and 1607 where supported. On the server side, the affected list includes Windows Server 2025, Windows Server 2022, Windows Server 2019, Windows Server 2016, and extended-support Server 2012 and 2012 R2 entries.That breadth matters less because every one of those machines has the same risk profile and more because most mixed Windows environments contain some of them. A desktop team may see this as a Windows 11 cumulative update issue. A server team may see hotpatch entries for newer server builds. A legacy operations group may see monthly rollups for older Server 2012-era systems still hanging around under extended support arrangements.
The fixed build numbers are similarly concrete. Windows 11 24H2 systems move to fixed builds in the 26100.8457 or hotpatch 26100.8390 range, while Windows 11 25H2 systems move to corresponding 26200 builds. Windows 10 22H2 receives build 19045.7291, and Server 2025 entries include 26100.32860 or hotpatch 26100.32772 depending on update path.
For administrators, the lesson is not to memorize every build. The lesson is to verify that update compliance tools are actually distinguishing between the full cumulative security update and hotpatch channels where both appear. A dashboard that says “patched” without surfacing build numbers can hide awkward exceptions.
Hotpatching Changes the Workflow, Not the Obligation
Several affected server entries include both a regular security update and a security hotpatch update. That reflects Microsoft’s growing use of hotpatching to reduce reboot pressure in supported server scenarios. It is a welcome operational improvement, especially for clustered services, virtualization hosts, and maintenance-sensitive workloads.But hotpatching does not turn security maintenance into a passive background event. It still requires eligibility, correct servicing configuration, and validation that the machine actually received the intended build. The risk for enterprises is that hotpatching becomes a comforting noun on a roadmap rather than an observed state on each server.
CVE-2026-34330 is a good example of why that distinction matters. A local privilege escalation flaw may not force an emergency reboot across the estate, but it should still close within defined patch windows. If hotpatching helps meet that window without downtime, excellent. If hotpatching creates a second lane that asset owners do not understand, it can become another source of drift.
The practical approach is simple: treat hotpatch and cumulative update paths as different delivery mechanisms for the same security requirement. Validate by build, not by expectation. If a system is in a hotpatch cohort, confirm it landed on the hotpatch build Microsoft lists. If it is not, confirm the standard security update build.
SYSTEM Privileges Are the Real Headline
The advisory’s most important operational sentence is not the executive summary; it is the answer to what an attacker could gain. Microsoft says successful exploitation could grant SYSTEM privileges. In Windows terms, that is the difference between a constrained foothold and near-total local control.SYSTEM access can let an attacker tamper with security tools, harvest credentials from local stores or memory-adjacent contexts, install persistence, access protected files, and move laterally with better leverage. Endpoint detection and response products are designed to resist that outcome, but they do not make it irrelevant. Any local escalation to SYSTEM should be treated as a serious post-compromise accelerant.
This is especially relevant on shared systems, jump boxes, developer workstations, and servers that host multiple roles. A low-privileged context on a normal laptop may already be bad. A low-privileged context on an administrative workstation is worse. A low-privileged context on a server with sensitive service accounts or management tooling can be the bridge to a larger compromise.
The nuance is that CVE-2026-34330 is not itself an initial access story. It is a privilege story. That means defenders should align mitigation with the kill chain: reduce initial footholds, restrict local code execution, monitor suspicious privilege transitions, and patch the kernel boundary so attackers have one fewer rung to climb.
Patch Tuesday’s Familiar Shape Still Creates Fresh Triage Work
For home users, the prescription is straightforward: install the May 2026 Windows security update through Windows Update and avoid delaying cumulative updates unless there is a known compatibility issue. The affected client list is broad enough that waiting for a more dramatic headline is not sensible. This is exactly the kind of fix that should disappear into routine servicing.For small businesses, the question is whether devices are actually checking in and completing updates. Laptops that sleep through maintenance windows, remote machines that live off VPN, and unmanaged contractor devices are the usual gaps. A local privilege escalation flaw becomes more dangerous when those endpoints are also the machines most likely to encounter untrusted files, browsers, and third-party tools.
For enterprises, the decision is less about whether to patch and more about sequencing. Domain controllers are not the obvious first concern for a Win32k graphics flaw unless the vulnerable component is present and reachable, but administrative workstations, RDS hosts, VDI images, developer boxes, and general-purpose servers deserve attention. Any machine where a low-privilege session coexists with sensitive credentials or admin tooling is a more attractive escalation target.
Testing remains necessary. Graphics and kernel-mode changes can trigger compatibility concerns, especially with display drivers, remote graphics stacks, security agents, and virtualization layers. But the answer to compatibility risk is staged deployment and telemetry, not indefinite deferral.
The Research Credit Shows Coordinated Disclosure Doing Its Job
Microsoft credits wenqunwang with China Telecom Research Institute for reporting the issue. That acknowledgement is not just etiquette. It is part of the ecosystem that turns private vulnerability discovery into public fixes rather than surprise exploitation.Coordinated disclosure can feel slow from the outside because users see the CVE only when the fix is ready. In this case, that timing is a strength. Microsoft published the advisory with an official fix available, no known public disclosure, no known exploitation, and confirmed confidence in the report. That is the best ordinary-case outcome for a Windows kernel-adjacent flaw.
The uncomfortable part is that defenders only enter the story at the end. Once the patch exists, the clock changes. Attackers can begin studying the fix. Security vendors can begin writing detections. Administrators can begin testing and deploying. The advisory may be calm, but the public timeline has started.
That is why confirmed report confidence is a double-edged signal. It reassures defenders that the bug is real and fixed. It also tells capable attackers that there is something concrete to investigate.
Where Windows Estates Should Spend Their Attention First
Not every system needs the same urgency, and pretending otherwise is how patch programs lose credibility. A kiosk with limited user activity is not the same as a privileged access workstation. A lab VM is not the same as a production RDS host. A legacy server under extended support is not the same as a fully managed Windows 11 fleet with rapid update rings.The first priority should be systems where local low-privilege access is common and privilege escalation would be especially damaging. Remote Desktop Session Hosts, VDI pools, shared engineering workstations, build servers, help-desk machines, and administrative jump boxes all fit that pattern. Those are the environments where “local only” can still mean “reachable by many.”
The second priority is systems that are hard to patch later. Older Windows Server versions, specialized workloads, and machines tied to maintenance windows should be identified early, because their friction is predictable. If they are still supported through extended programs, they need the relevant monthly rollup or security update. If they are not supported, the conversation should move from patching to isolation and retirement.
The third priority is evidence. Patch compliance should be measured by installed KB and build number, not by assumptions about update rings. CVE-driven reporting is useful only when it maps to actual assets. The existence of 31 affected rows in Microsoft’s table is a reminder that “Windows” is not one target; it is a fleet of servicing channels, architectures, and support states.
The Calm Advisory Still Leaves a Clear Job List
CVE-2026-34330 is not a reason to declare emergency across every Windows network, but it is also not background noise. It is a confirmed Win32k GRFX local privilege escalation flaw with an official fix, broad platform coverage, and SYSTEM-level impact if successfully exploited.- Microsoft released the advisory and fixes on May 12, 2026, with the vulnerability rated Important and scored CVSS 7.8 base.
- The flaw is local, requires low privileges, requires no user interaction, and can lead to SYSTEM privileges after successful exploitation.
- Microsoft says the bug was not publicly disclosed or exploited at original publication and assesses exploitation as unlikely.
- The report confidence is confirmed, while exploit code maturity is unproven, making this a real vulnerability without current public weaponization signals.
- Administrators should validate deployment by KB and build number, especially where hotpatch and standard cumulative update paths both exist.
- Priority should go to shared, privileged, remote-access, developer, and administrative systems where local escalation has outsized consequences.
Source: MSRC Security Update Guide - Microsoft Security Response Center