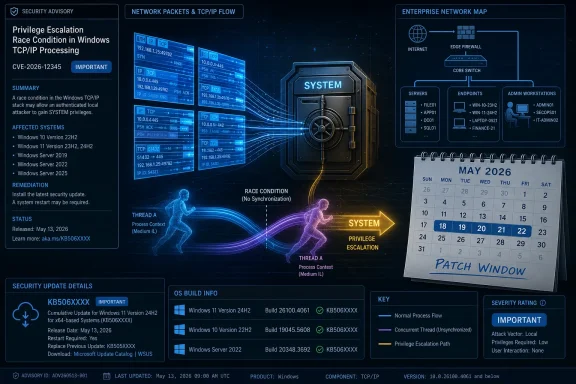
Microsoft published CVE-2026-34351 on May 12, 2026, describing an Important-rated Windows TCP/IP elevation-of-privilege flaw caused by a race condition that can let an authenticated local attacker gain SYSTEM privileges after applying the right exploit path. The vulnerability is not described as remotely exploitable, publicly disclosed, or already exploited, but its location in the Windows networking stack gives it more operational weight than an ordinary local bug. The real story is not panic; it is the familiar tension between Microsoft’s sparse advisory language and the practical risk of any flaw that crosses from low privilege to SYSTEM in code every Windows machine depends on.
CVE-2026-34351 is the kind of vulnerability that can look modest in a dashboard and serious in a fleet. Microsoft rates it Important rather than Critical, assigns it a CVSS 3.1 base score of 7.8, and marks exploitation as less likely. On paper, that keeps it below the threshold of the nightmare-class network worm, the kind of bug that can be triggered from across the internet with no credentials and no user action.
But “Windows TCP/IP” is not a niche component. It is the operating system’s network plumbing, the layer that carries everything from workstation browsing to server workloads, VPN traffic, domain connectivity, management channels, and cloud-hosted Windows instances. Even a local elevation-of-privilege vulnerability in that neighborhood deserves more than a shrug, because attackers rarely need one magic exploit when a chain will do.
Microsoft’s description is terse: a race condition in Windows TCP/IP allows an authorized attacker to elevate privileges locally. The company’s FAQ adds the key practical consequence: successful exploitation could grant SYSTEM privileges. That means the flaw is less about getting in through the front door and more about what happens after an attacker has already obtained a foothold.
That distinction matters. In modern intrusions, initial access and privilege escalation are often separate phases. A phishing payload, stolen credential, exposed remote access service, malicious installer, or vulnerable third-party app can supply the first step; a Windows local privilege escalation can turn that access into full control of the machine.
Local attack vector does not mean “requires physical access.” It means the attacker must already be able to run code on the target system or otherwise operate in a local context. For home users, that may sound like the battle is already lost. For enterprise defenders, it is a daily assumption: endpoints get touched by untrusted documents, browsers execute complex code, users install software, service accounts run scheduled tasks, and exposed applications occasionally fall over.
The most important phrase in the advisory is SYSTEM privileges. On Windows, SYSTEM is not just “administrator plus.” It is the context in which core services run, with power over files, processes, registry hives, security controls, and credentials that a normal user should never reach. If an attacker can reliably move from low privilege to SYSTEM, endpoint containment becomes much harder.
That is why local privilege escalation vulnerabilities are so consistently useful to attackers. They are not always flashy, and they rarely get the same public attention as remote code execution bugs. But they are often the grease in the intrusion chain, turning a constrained compromise into durable control.
Race conditions are notoriously awkward for both attackers and defenders. For attackers, the challenge is usually reliability: winning the timing window consistently enough to exploit the bug without crashing the system or leaving obvious noise. For defenders, the challenge is visibility: the vulnerable behavior may not look like a clean signature, and exploit attempts can be buried inside normal system activity.
That is one reason Microsoft’s “exploitation less likely” assessment should be read carefully. It does not mean impossible, and it does not mean unimportant. It means Microsoft believes, based on the information available at publication, that reliable exploitation is less probable than for some other vulnerabilities.
The advisory also lists exploit code maturity as unproven. That is useful, but it is a snapshot, not a warranty. Once a patch ships, attackers and researchers can compare binaries, inspect changed code paths, and look for the mistake the update corrected. The clock starts running when the fix becomes public.
That distinction is often lost in patch discussions. A vulnerability can be real and vendor-confirmed while still lacking public proof-of-concept code. A vulnerability can also have public chatter but weak technical grounding. CVE-2026-34351 sits in the cleaner category for defenders: the vendor has acknowledged the flaw, assigned it a CVE, described the weakness class, published affected products, and shipped updates.
The confidence metric also hints at attacker knowledge. When only a vague advisory exists, would-be exploit developers have less to work with. When the vendor confirms the component, weakness type, privilege requirements, and impact, the map becomes sharper even if the exact vulnerable function is not named. That is not a reason for Microsoft to publish nothing; defenders need enough detail to prioritize. But it is a reason to treat Patch Tuesday advisories as the beginning of risk movement, not the end.
In this case, the public technical details are limited but meaningful. We know the affected component family, the weakness category, the required attacker position, the impact ceiling, and the affected Windows versions. That is enough for administrators to prioritize deployment without pretending they have a complete exploit narrative.
That breadth should not surprise anyone. TCP/IP is a shared foundation, and shared foundations age into long tails. The same conceptual bug class can affect supported releases, extended-support releases, and newer builds because the networking stack is not reinvented from scratch for every Windows generation.
The product list also reveals the practical divide in Windows servicing. Current Windows 11 and Windows Server releases receive normal cumulative updates or security updates. Older platforms such as Windows Server 2012, Server 2012 R2, and Windows 10 22H2 in ESU contexts appear in the extended servicing lane, which means organizations still running them need to verify that they are actually eligible for and receiving the relevant updates.
For Windows 10, the timing is impossible to ignore. By May 2026, many organizations and individuals are already operating in the post-mainstream Windows 10 world, where extended security coverage, migration planning, and hardware replacement all collide. A TCP/IP privilege escalation bug is exactly the sort of issue that exposes whether that plan is real or merely documented.
The presence of hotpatch entries is notable but should not be overread. Hotpatching can reduce reboot pressure for supported server scenarios, but the advisory data still flags reboot requirements in the update metadata. In real environments, the question is not whether Microsoft has an elegant servicing story; it is whether your specific edition, configuration, and management stack will actually converge to a protected build.
The fixed builds are also important for verification. Windows 11 24H2 moves to build 26100.8457 through the standard security update path, while Windows Server 2025 moves to 26100.32860. Windows 10 22H2 moves to 19045.7291, and Windows Server 2022 moves to 20348.5139. Those numbers become the audit trail when vulnerability scanners lag behind Microsoft’s metadata or when endpoint reports disagree.
This is where experienced Windows administrators have learned to distrust green dashboards that arrive too quickly. A machine may report the latest cumulative update as installed while still pending reboot. A server may be protected by one update path but not another. A disconnected or bandwidth-constrained segment may show policy compliance without payload installation. CVE-2026-34351 is not special in that regard, but it is a useful reminder that patch management is state management.
The reason is simple: local privilege escalation bugs often become more valuable after other vulnerabilities are weaponized. A browser sandbox escape, a malicious document chain, a compromised developer tool, a vulnerable VPN client, or a stolen low-privilege account can all benefit from a reliable elevation path. The TCP/IP label may not make this bug a remote network entry point, but it gives the bug a place in the post-compromise toolkit.
Security teams should also separate urgency from sequencing. A Critical remote code execution vulnerability exposed to the internet usually jumps the queue. An Important local privilege escalation vulnerability affecting every managed Windows endpoint may not beat that emergency, but it should not wait for the next quarterly maintenance cycle either.
Microsoft’s own CVSS vector helps explain the balance. Low attack complexity and no user interaction mean that once the attacker has a suitable local position, there is not much friction left in the formal model. The “privileges required: low” element is the hinge. It turns a compromised standard account from a contained problem into a potential SYSTEM-level incident.
Networking code is privileged, performance-sensitive, and full of concurrency. It must handle simultaneous connections, timers, buffers, interface changes, offload features, virtual adapters, filtering layers, tunneling, and policy enforcement. Race conditions in that world are not exotic; they are the predictable byproduct of trying to move packets quickly while preserving security invariants.
That complexity also complicates mitigations. With some vulnerabilities, administrators can disable an optional service, block a port, remove a feature, or narrow exposure with a firewall rule. For a Windows TCP/IP local elevation-of-privilege flaw, there is no obvious “turn off networking” mitigation that makes sense for a modern system. The fix is the fix.
This is why the advisory’s customer-action-required flag matters. Microsoft is not presenting this as a configuration warning or a documentation-only correction. It is a shipped security update for a core Windows component, and the practical remediation path is to install the applicable May 2026 update and confirm the resulting build.
Windows Server 2012 and 2012 R2 entries are a good example. These systems are no longer normal supported platforms in the everyday sense, yet they still appear in security update metadata because some customers remain on paid extended coverage. When a TCP/IP privilege escalation vulnerability affects those machines, the technical bug and the lifecycle problem become inseparable.
The same pattern applies to Windows 10. Organizations that delayed Windows 11 migration for hardware, application compatibility, user training, or budget reasons now have to manage the security consequences of that delay. CVE-2026-34351 does not single-handedly invalidate those decisions, but it adds another entry to the ledger.
For small businesses and home power users, the lesson is blunter. If a machine is not receiving the relevant security update, it is not meaningfully protected by the existence of the patch. Knowing the CVE name is not a defense; being on a serviced build is.
There is a defensible reason for that restraint. Publishing too much exploit detail on Patch Tuesday can accelerate weaponization before customers have time to deploy updates. But the defensive cost is real: security teams must often decide urgency without knowing whether exploit attempts would look like unusual network activity, local process behavior, kernel object manipulation, or something else entirely.
In practice, the best response is to combine vendor metadata with local risk. Domain controllers, jump boxes, build servers, RDS hosts, VPN-adjacent Windows servers, and shared administrative workstations deserve faster attention than lightly used lab machines. Endpoints that routinely process untrusted content deserve attention because they are plausible first-hop systems.
The absence of public exploitation should also shape communications. This is not a case for alarmist messaging to users about an active worm. It is a case for disciplined patch deployment, reboot tracking, and validation across the Windows versions that actually exist in the environment.
A low-privilege foothold without an elevation path is noisy and constrained. The attacker may be trapped in a user profile, blocked by endpoint controls, unable to dump credentials, unable to tamper with services, and unable to disable security tooling. Add a SYSTEM-level escalation, and the machine becomes a staging ground.
That is why CVE-2026-34351 deserves a place in May 2026 patch prioritization even though it is not marked as exploited. The upside for an attacker is high, the affected base is broad, and the required privilege level is low. Those three facts are enough to make it a meaningful enterprise risk.
At the same time, defenders should resist the temptation to overstate it. Microsoft has not said the bug is remotely exploitable. It has not said exploitation is detected in the wild. It has not described public proof-of-concept code. The correct posture is sober urgency, not theatrical dread.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft’s Quiet TCP/IP Bug Still Lands in a Loud Part of Windows
Microsoft’s Quiet TCP/IP Bug Still Lands in a Loud Part of Windows
CVE-2026-34351 is the kind of vulnerability that can look modest in a dashboard and serious in a fleet. Microsoft rates it Important rather than Critical, assigns it a CVSS 3.1 base score of 7.8, and marks exploitation as less likely. On paper, that keeps it below the threshold of the nightmare-class network worm, the kind of bug that can be triggered from across the internet with no credentials and no user action.But “Windows TCP/IP” is not a niche component. It is the operating system’s network plumbing, the layer that carries everything from workstation browsing to server workloads, VPN traffic, domain connectivity, management channels, and cloud-hosted Windows instances. Even a local elevation-of-privilege vulnerability in that neighborhood deserves more than a shrug, because attackers rarely need one magic exploit when a chain will do.
Microsoft’s description is terse: a race condition in Windows TCP/IP allows an authorized attacker to elevate privileges locally. The company’s FAQ adds the key practical consequence: successful exploitation could grant SYSTEM privileges. That means the flaw is less about getting in through the front door and more about what happens after an attacker has already obtained a foothold.
That distinction matters. In modern intrusions, initial access and privilege escalation are often separate phases. A phishing payload, stolen credential, exposed remote access service, malicious installer, or vulnerable third-party app can supply the first step; a Windows local privilege escalation can turn that access into full control of the machine.
The Word “Local” Is Reassuring Only Until You Run an Enterprise
The CVSS vector for CVE-2026-34351 tells a compact story. The attack vector is local, attack complexity is low, privileges required are low, user interaction is not required, scope is unchanged, and confidentiality, integrity, and availability impact are all high. That combination is exactly why the score lands at 7.8 rather than somewhere in the low or medium range.Local attack vector does not mean “requires physical access.” It means the attacker must already be able to run code on the target system or otherwise operate in a local context. For home users, that may sound like the battle is already lost. For enterprise defenders, it is a daily assumption: endpoints get touched by untrusted documents, browsers execute complex code, users install software, service accounts run scheduled tasks, and exposed applications occasionally fall over.
The most important phrase in the advisory is SYSTEM privileges. On Windows, SYSTEM is not just “administrator plus.” It is the context in which core services run, with power over files, processes, registry hives, security controls, and credentials that a normal user should never reach. If an attacker can reliably move from low privilege to SYSTEM, endpoint containment becomes much harder.
That is why local privilege escalation vulnerabilities are so consistently useful to attackers. They are not always flashy, and they rarely get the same public attention as remote code execution bugs. But they are often the grease in the intrusion chain, turning a constrained compromise into durable control.
Race Conditions Are Where Reliability Becomes the Battle
Microsoft identifies the underlying weakness as concurrent execution using a shared resource with improper synchronization, the class commonly known as a race condition. In plain English, two or more operations can interact with the same resource at the wrong time, and the system fails to enforce the ordering or locking needed to keep state safe. In kernel-adjacent code, those timing mistakes can become security bugs rather than mere crashes.Race conditions are notoriously awkward for both attackers and defenders. For attackers, the challenge is usually reliability: winning the timing window consistently enough to exploit the bug without crashing the system or leaving obvious noise. For defenders, the challenge is visibility: the vulnerable behavior may not look like a clean signature, and exploit attempts can be buried inside normal system activity.
That is one reason Microsoft’s “exploitation less likely” assessment should be read carefully. It does not mean impossible, and it does not mean unimportant. It means Microsoft believes, based on the information available at publication, that reliable exploitation is less probable than for some other vulnerabilities.
The advisory also lists exploit code maturity as unproven. That is useful, but it is a snapshot, not a warranty. Once a patch ships, attackers and researchers can compare binaries, inspect changed code paths, and look for the mistake the update corrected. The clock starts running when the fix becomes public.
Report Confidence Is Doing More Work Than It Usually Gets Credit For
The user-supplied note about the report confidence metric is especially relevant here because Microsoft gives CVE-2026-34351 a “confirmed” confidence signal through its own advisory data. In vulnerability scoring, report confidence measures how certain we are that the vulnerability exists and how credible the known technical details are. It is not the same as exploitability, severity, or active exploitation.That distinction is often lost in patch discussions. A vulnerability can be real and vendor-confirmed while still lacking public proof-of-concept code. A vulnerability can also have public chatter but weak technical grounding. CVE-2026-34351 sits in the cleaner category for defenders: the vendor has acknowledged the flaw, assigned it a CVE, described the weakness class, published affected products, and shipped updates.
The confidence metric also hints at attacker knowledge. When only a vague advisory exists, would-be exploit developers have less to work with. When the vendor confirms the component, weakness type, privilege requirements, and impact, the map becomes sharper even if the exact vulnerable function is not named. That is not a reason for Microsoft to publish nothing; defenders need enough detail to prioritize. But it is a reason to treat Patch Tuesday advisories as the beginning of risk movement, not the end.
In this case, the public technical details are limited but meaningful. We know the affected component family, the weakness category, the required attacker position, the impact ceiling, and the affected Windows versions. That is enough for administrators to prioritize deployment without pretending they have a complete exploit narrative.
The Affected List Is Broad Because TCP/IP Is Not Optional
The affected product set spans old and new Windows lines. Microsoft lists Windows Server 2012 and 2012 R2 under Extended Security Updates, Windows Server 2016, 2019, 2022, 2022 23H2, and 2025, as well as multiple Windows 10 and Windows 11 releases. Client platforms include Windows 10 21H2, 22H2, 1809, 1607, and Windows 11 23H2, 24H2, 25H2, and 26H1, across x64, ARM64, and in some cases 32-bit builds.That breadth should not surprise anyone. TCP/IP is a shared foundation, and shared foundations age into long tails. The same conceptual bug class can affect supported releases, extended-support releases, and newer builds because the networking stack is not reinvented from scratch for every Windows generation.
The product list also reveals the practical divide in Windows servicing. Current Windows 11 and Windows Server releases receive normal cumulative updates or security updates. Older platforms such as Windows Server 2012, Server 2012 R2, and Windows 10 22H2 in ESU contexts appear in the extended servicing lane, which means organizations still running them need to verify that they are actually eligible for and receiving the relevant updates.
For Windows 10, the timing is impossible to ignore. By May 2026, many organizations and individuals are already operating in the post-mainstream Windows 10 world, where extended security coverage, migration planning, and hardware replacement all collide. A TCP/IP privilege escalation bug is exactly the sort of issue that exposes whether that plan is real or merely documented.
Patch Numbers Matter More Than the CVE Name in the Change Window
For administrators, the operational artifact is not the CVE identifier but the update that closes it. Microsoft associates CVE-2026-34351 with a series of May 2026 updates, including KB5089549 for Windows 11 24H2 and 25H2, KB5087420 for Windows 11 23H2, KB5087544 for Windows 10 21H2 and 22H2, and KB5087545 for Windows Server 2022. Windows Server 2025 is covered by KB5087539, with a hotpatch path also listed for eligible systems.The presence of hotpatch entries is notable but should not be overread. Hotpatching can reduce reboot pressure for supported server scenarios, but the advisory data still flags reboot requirements in the update metadata. In real environments, the question is not whether Microsoft has an elegant servicing story; it is whether your specific edition, configuration, and management stack will actually converge to a protected build.
The fixed builds are also important for verification. Windows 11 24H2 moves to build 26100.8457 through the standard security update path, while Windows Server 2025 moves to 26100.32860. Windows 10 22H2 moves to 19045.7291, and Windows Server 2022 moves to 20348.5139. Those numbers become the audit trail when vulnerability scanners lag behind Microsoft’s metadata or when endpoint reports disagree.
This is where experienced Windows administrators have learned to distrust green dashboards that arrive too quickly. A machine may report the latest cumulative update as installed while still pending reboot. A server may be protected by one update path but not another. A disconnected or bandwidth-constrained segment may show policy compliance without payload installation. CVE-2026-34351 is not special in that regard, but it is a useful reminder that patch management is state management.
“Exploitation Less Likely” Is a Triage Signal, Not a Permission Slip
Microsoft’s exploitability assessment says exploitation is less likely for the latest software release, and the advisory states that the vulnerability was not publicly disclosed and not exploited at publication. Those are helpful facts. They should lower panic, not priority.The reason is simple: local privilege escalation bugs often become more valuable after other vulnerabilities are weaponized. A browser sandbox escape, a malicious document chain, a compromised developer tool, a vulnerable VPN client, or a stolen low-privilege account can all benefit from a reliable elevation path. The TCP/IP label may not make this bug a remote network entry point, but it gives the bug a place in the post-compromise toolkit.
Security teams should also separate urgency from sequencing. A Critical remote code execution vulnerability exposed to the internet usually jumps the queue. An Important local privilege escalation vulnerability affecting every managed Windows endpoint may not beat that emergency, but it should not wait for the next quarterly maintenance cycle either.
Microsoft’s own CVSS vector helps explain the balance. Low attack complexity and no user interaction mean that once the attacker has a suitable local position, there is not much friction left in the formal model. The “privileges required: low” element is the hinge. It turns a compromised standard account from a contained problem into a potential SYSTEM-level incident.
The Networking Stack Gives the Bug Strategic Weight
The Windows TCP/IP stack has a long institutional memory in security. Some of the most disruptive Windows vulnerabilities in history have lived in network-facing components, because code that parses packets and maintains protocol state is both complex and widely exposed. CVE-2026-34351 is not being described as that kind of remotely triggerable flaw, but the affected component still shapes how defenders should think about it.Networking code is privileged, performance-sensitive, and full of concurrency. It must handle simultaneous connections, timers, buffers, interface changes, offload features, virtual adapters, filtering layers, tunneling, and policy enforcement. Race conditions in that world are not exotic; they are the predictable byproduct of trying to move packets quickly while preserving security invariants.
That complexity also complicates mitigations. With some vulnerabilities, administrators can disable an optional service, block a port, remove a feature, or narrow exposure with a firewall rule. For a Windows TCP/IP local elevation-of-privilege flaw, there is no obvious “turn off networking” mitigation that makes sense for a modern system. The fix is the fix.
This is why the advisory’s customer-action-required flag matters. Microsoft is not presenting this as a configuration warning or a documentation-only correction. It is a shipped security update for a core Windows component, and the practical remediation path is to install the applicable May 2026 update and confirm the resulting build.
Old Windows Builds Make a Local Bug Feel Bigger
The wide affected set also exposes a more uncomfortable issue: many organizations still carry old Windows versions because their business systems, hardware dependencies, and certification cycles move more slowly than Microsoft’s release calendar. Extended Security Updates buy time, but they do not make legacy platforms simpler to defend. They merely keep a shrinking bridge from collapsing immediately.Windows Server 2012 and 2012 R2 entries are a good example. These systems are no longer normal supported platforms in the everyday sense, yet they still appear in security update metadata because some customers remain on paid extended coverage. When a TCP/IP privilege escalation vulnerability affects those machines, the technical bug and the lifecycle problem become inseparable.
The same pattern applies to Windows 10. Organizations that delayed Windows 11 migration for hardware, application compatibility, user training, or budget reasons now have to manage the security consequences of that delay. CVE-2026-34351 does not single-handedly invalidate those decisions, but it adds another entry to the ledger.
For small businesses and home power users, the lesson is blunter. If a machine is not receiving the relevant security update, it is not meaningfully protected by the existence of the patch. Knowing the CVE name is not a defense; being on a serviced build is.
The Advisory Says Little, but It Says Enough
Microsoft’s sparse vulnerability write-ups remain a point of frustration for defenders. CVE-2026-34351 does not disclose a vulnerable function, a detailed exploitation scenario, sample indicators, or a workaround. It tells us the component, impact, weakness class, affected products, scores, and update paths. That is enough for patching, but not enough for deep detection engineering.There is a defensible reason for that restraint. Publishing too much exploit detail on Patch Tuesday can accelerate weaponization before customers have time to deploy updates. But the defensive cost is real: security teams must often decide urgency without knowing whether exploit attempts would look like unusual network activity, local process behavior, kernel object manipulation, or something else entirely.
In practice, the best response is to combine vendor metadata with local risk. Domain controllers, jump boxes, build servers, RDS hosts, VPN-adjacent Windows servers, and shared administrative workstations deserve faster attention than lightly used lab machines. Endpoints that routinely process untrusted content deserve attention because they are plausible first-hop systems.
The absence of public exploitation should also shape communications. This is not a case for alarmist messaging to users about an active worm. It is a case for disciplined patch deployment, reboot tracking, and validation across the Windows versions that actually exist in the environment.
The SYSTEM Prize Changes the Defender’s Math
Privilege escalation vulnerabilities are sometimes treated as second-tier because they require prior access. That hierarchy makes sense in a narrow scoring model, but it can mislead in operational defense. Attackers do not experience a network as a spreadsheet of isolated CVEs; they experience it as a sequence of opportunities.A low-privilege foothold without an elevation path is noisy and constrained. The attacker may be trapped in a user profile, blocked by endpoint controls, unable to dump credentials, unable to tamper with services, and unable to disable security tooling. Add a SYSTEM-level escalation, and the machine becomes a staging ground.
That is why CVE-2026-34351 deserves a place in May 2026 patch prioritization even though it is not marked as exploited. The upside for an attacker is high, the affected base is broad, and the required privilege level is low. Those three facts are enough to make it a meaningful enterprise risk.
At the same time, defenders should resist the temptation to overstate it. Microsoft has not said the bug is remotely exploitable. It has not said exploitation is detected in the wild. It has not described public proof-of-concept code. The correct posture is sober urgency, not theatrical dread.
The May Patch Window Now Has a TCP/IP Audit Trail
This is the kind of advisory that rewards basic patch discipline more than clever compensating controls. The most useful near-term work is to identify affected Windows versions, deploy the May 2026 security updates, confirm reboots where required, and verify fixed build numbers rather than relying solely on update-install status.- CVE-2026-34351 is an Important-rated Windows TCP/IP elevation-of-privilege vulnerability published by Microsoft on May 12, 2026.
- Microsoft describes the root cause as a race condition and says successful exploitation could give an attacker SYSTEM privileges.
- The vulnerability requires local access with low privileges, has low attack complexity, and does not require user interaction once the attacker is in position.
- Microsoft says the flaw was not publicly disclosed and not exploited at publication, with exploitation assessed as less likely.
- The affected set spans major Windows client and server releases, including Windows 10, Windows 11, Windows Server 2012-era ESU systems, and current Windows Server versions.
- Administrators should validate the relevant May 2026 KB installation, reboot completion, and final build numbers across managed endpoints and servers.
Source: MSRC Security Update Guide - Microsoft Security Response Center