Microsoft’s CVE-2026-33186 entry for gRPC-Go points to an authorization bypass rooted in a deceptively small parsing flaw: a missing leading slash in the HTTP/2
gRPC sits at the center of modern service-to-service communication, and gRPC-Go is the Go-language implementation used across cloud services, internal APIs, and microservice backends. Microsoft’s own Security Update Guide often lists upstream open-source CVEs when those components affect Microsoft products or downstream packages, which is why a gRPC-Go flaw can matter even when Microsoft did not write the vulnerable code itself. The current advisory pattern is consistent with Microsoft’s broader transparency push around vulnerability disclosure and machine-readable CVE data.
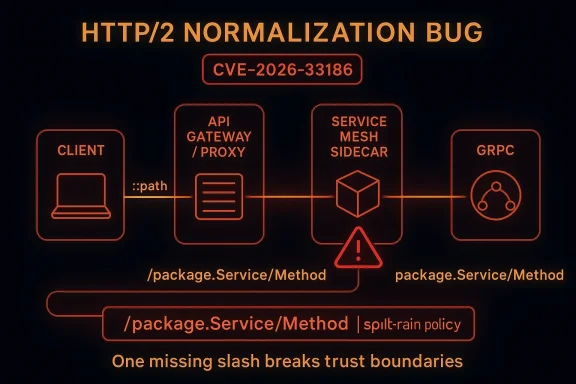
At a technical level, gRPC runs atop HTTP/2, where each request is identified by pseudo-headers like
The missing-leading-slash issue is especially important because request path handling is one of those places where implicit assumptions are dangerous. If one component treats
This vulnerability also fits a broader pattern in gRPC and HTTP/2 security: state, normalization, and validation bugs tend to surface as availability issues, auth bypasses, or both. gRPC-Go has had prior security advisories around protocol handling, including HTTP/2 rapid reset abuse, which shows the ecosystem is already familiar with the risk of malformed or adversarial transport behavior. In other words, CVE-2026-33186 is not an isolated oddity; it is part of the same hardening story.
The fact that the flaw is about authorization bypass rather than a crash changes the urgency profile. Auth bypasses are often more damaging than denial-of-service issues because they can expand attacker reach from nuisance traffic to unauthorized method invocation. In a gRPC environment, unauthorized RPC calls can expose data, trigger privileged backend behavior, or reach administrative endpoints that were assumed to be protected by routing policy.
That is especially dangerous in gRPC because many deployments use middleware chains. One interceptor may perform authentication, another may do authorization, and a third may log or transform the request. If the request path is normalized at different points in the chain, one layer may authorize a request that another layer would have rejected. That kind of split-brain policy enforcement is exactly what security reviews try to prevent, and exactly what attackers try to exploit.
This is not unique to gRPC-Go. Any RPC system with layered request processing can end up with policy drift if it accepts multiple textual representations of the same target. But gRPC’s HTTP/2 framing and pseudo-header model makes the path especially important because the route is effectively the interface contract between transport and service method.
Another concern is blast radius. A single vulnerable library version can be compiled into dozens of services, and those services may not share the same release cadence. That creates a patching problem where one backend is fixed quickly while another continues to accept risky requests for weeks. In distributed systems, inconsistency is itself a vulnerability surface.
It is also easy to underestimate the effect because the flaw does not resemble a classic exploit primitive. There is no buffer overflow, no RCE chain, and no obvious memory corruption. Yet an auth bypass can be just as serious, especially when the bypass grants access to privileged methods or internal-only APIs. In many real deployments, that is the more dangerous outcome.
For competitors in the RPC and service-mesh space, the lesson is uncomfortable but useful: users now expect explicit normalization rules, documented authorization semantics, and hardened edge-case handling. A modern transport stack is no longer judged only by throughput and latency. It is also judged by how predictably it behaves when input is just slightly off-spec.
Source: MSRC Security Update Guide - Microsoft Security Response Center
:path pseudo-header. In practice, that means a request can slip past policy logic that assumes canonical gRPC paths always begin with /, creating a gap between what the server thinks it is protecting and what it is actually matching. The problem is a reminder that in protocol security, tiny normalization mistakes can have outsized consequences.
 Background
Background
gRPC sits at the center of modern service-to-service communication, and gRPC-Go is the Go-language implementation used across cloud services, internal APIs, and microservice backends. Microsoft’s own Security Update Guide often lists upstream open-source CVEs when those components affect Microsoft products or downstream packages, which is why a gRPC-Go flaw can matter even when Microsoft did not write the vulnerable code itself. The current advisory pattern is consistent with Microsoft’s broader transparency push around vulnerability disclosure and machine-readable CVE data.At a technical level, gRPC runs atop HTTP/2, where each request is identified by pseudo-headers like
:method, :scheme, :authority, and :path. That :path value is not just decoration; it is often the key used by routers, auth middleware, interceptors, and gateways to decide which method a request maps to and whether it should be allowed at all. The official gRPC documentation emphasizes interceptors and middleware as the place where cross-cutting controls like authorization are commonly implemented.The missing-leading-slash issue is especially important because request path handling is one of those places where implicit assumptions are dangerous. If one component treats
service.Method and /service.Method as interchangeable while another does not, policy checks can diverge. That divergence is exactly the kind of subtle inconsistency attackers look for in network stacks, especially in layered deployments that combine proxies, load balancers, and service meshes.This vulnerability also fits a broader pattern in gRPC and HTTP/2 security: state, normalization, and validation bugs tend to surface as availability issues, auth bypasses, or both. gRPC-Go has had prior security advisories around protocol handling, including HTTP/2 rapid reset abuse, which shows the ecosystem is already familiar with the risk of malformed or adversarial transport behavior. In other words, CVE-2026-33186 is not an isolated oddity; it is part of the same hardening story.
What Microsoft Is Signaling
Microsoft’s inclusion of the issue in the Security Update Guide is a meaningful signal even before every downstream detail is fully enumerated. The Security Update Guide is Microsoft’s canonical place for tracking vulnerabilities that affect Microsoft-supported products, including upstream open-source components consumed by those products. Microsoft has also increasingly used the guide to improve transparency around cloud and open-source CVEs.Why the listing matters
A Microsoft-listed CVE usually means two things at once: the upstream issue is real, and Microsoft believes it matters to customers somewhere in its ecosystem. That could be in a product that embeds gRPC-Go directly, in a cloud service dependency chain, or in a packaged distribution where the vulnerable code is present by version. For defenders, that means the problem should be treated as a practical patching issue, not a theoretical bug report.The fact that the flaw is about authorization bypass rather than a crash changes the urgency profile. Auth bypasses are often more damaging than denial-of-service issues because they can expand attacker reach from nuisance traffic to unauthorized method invocation. In a gRPC environment, unauthorized RPC calls can expose data, trigger privileged backend behavior, or reach administrative endpoints that were assumed to be protected by routing policy.
What the advisory implies operationally
Even when a vulnerability is small in code terms, the operational blast radius can be large if the affected component is shared. gRPC-Go is commonly used as a library, which means a single fix may need to be rolled through many binaries, containers, and services. That makes the Microsoft listing a triage signal as much as a security notice: inventory the dependency, confirm the patched version, and verify how authorization is enforced in your service chain.- Microsoft is treating the CVE as relevant to its supported ecosystem.
- The issue affects a core request-routing field in HTTP/2.
- The likely risk is policy bypass, not just parser confusion.
- Downstream services may need independent validation even after library patching.
- Shared infrastructure increases exposure more than a single service deployment would.
How the Bypass Likely Works
The phrase “missing leading slash in:path” points to a normalization mismatch. In HTTP/2, gRPC requests are generally expected to use canonical paths like /package.Service/Method. If a server-side authorization layer strips or compares paths inconsistently, a request that omits the leading slash may evade a rule written for the canonical form. That is a classic case of parser disagreement turning into a security bug.Why a single character matters
The leading slash is tiny, but it anchors path interpretation. In a security filter, the question is not whether the string looks similar to the intended route, but whether every layer sees the exact same string after normalization. If the authorization check and the dispatch path disagree, an attacker can land in the wrong branch of the logic tree and still reach a handler they should not have accessed.That is especially dangerous in gRPC because many deployments use middleware chains. One interceptor may perform authentication, another may do authorization, and a third may log or transform the request. If the request path is normalized at different points in the chain, one layer may authorize a request that another layer would have rejected. That kind of split-brain policy enforcement is exactly what security reviews try to prevent, and exactly what attackers try to exploit.
Canonicalization as a security boundary
Normalization bugs are rarely flashy. They do not require memory corruption or complex payloads. Instead, they exploit the gap between “what the code meant” and “what the code actually compared.” In that sense, CVE-2026-33186 is more about trust boundaries than about syntax. The request is syntactically legal enough to move through the stack, but semantically different enough to defeat a naive allowlist or route match.- The bug depends on path canonicalization inconsistency.
- The attack surface is the request-routing layer, not raw transport.
- Authorization logic is only as strong as its normalization rules.
- Middleware order can amplify small validation mistakes.
- A malformed-looking path may still be accepted by one layer and rejected by another.
Why gRPC Path Handling Is Security-Critical
gRPC path handling is not just an implementation detail; it is the method identity mechanism. Because gRPC tends to expose a relatively small number of strongly typed methods, operators often assume that authorization can be simplified to “is this request for method X?” That assumption only works if the path is normalized consistently from edge proxy to application handler.The role of interceptors and middleware
The official gRPC guidance describes interceptors as the place to implement common behavior such as metadata handling and authorization. That makes interceptors powerful, but also risky: if the interceptor keys off a request path that is not normalized the same way as the downstream router, the security policy can be bypassed without ever touching application logic. In practice, that means path normalization must be treated as part of the auth boundary, not as a formatting cleanup step.This is not unique to gRPC-Go. Any RPC system with layered request processing can end up with policy drift if it accepts multiple textual representations of the same target. But gRPC’s HTTP/2 framing and pseudo-header model makes the path especially important because the route is effectively the interface contract between transport and service method.
Where enterprise systems feel it
Enterprise environments are the most exposed because they tend to stack multiple controls: ingress proxies, API gateways, auth middlewares, service mesh sidecars, and application-level ACLs. If any one of those components expects canonical/service/method formatting while another tolerates a variant without the slash, the attacker only needs one mismatch. That is why path bugs in RPC stacks often become architecture bugs, not just library bugs.- Interceptors are a common place to enforce authorization.
- Route matching must be consistent across all layers.
- Multi-tier enterprise stacks magnify normalization mistakes.
- The path is effectively the method identity in gRPC.
- Small differences in representation can defeat allowlists and RBAC rules.
Consumer and Enterprise Impact
For consumers, this type of flaw is usually invisible until an app or desktop client starts making unauthorized RPCs against a service that should have rejected them. Most users will never know gRPC-Go by name, but they may still be affected through software updates, sync clients, developer tools, or backend services that rely on Go-based RPC infrastructure. The result is usually indirect: unexpected access, broken policy enforcement, or confusing behavior from a trusted application.Enterprise impact is broader
Enterprises, by contrast, may face direct exposure in internal APIs, microservices, and platform tooling. Because gRPC is often used for internal east-west traffic, an auth bypass can open access to services that were assumed to be non-public. That can lead to data exposure, privilege escalation across services, or unauthorized triggering of business logic.Another concern is blast radius. A single vulnerable library version can be compiled into dozens of services, and those services may not share the same release cadence. That creates a patching problem where one backend is fixed quickly while another continues to accept risky requests for weeks. In distributed systems, inconsistency is itself a vulnerability surface.
What security teams should ask
Security teams should not stop at “is the package version patched?” They should also ask whether authorization decisions depend on exact path strings, whether proxies rewrite:path, and whether any custom middleware performs its own routing before or after authentication. Those are the places where a missing leading slash can quietly become a policy failure.- Consumer risk is usually indirect but still real.
- Enterprise risk is magnified by internal service trust.
- Internal APIs are often more valuable than public endpoints.
- A patch in one service does not eliminate risk in sibling services.
- Routing and auth order must be reviewed together.
Why This Kind of Bug Is Hard to Notice
Authorization bypasses built on normalization mistakes are frustrating because they often look like benign edge cases in code review. A request path without a leading slash may appear malformed enough to be rejected, but if one component silently accepts it and another canonicalizes it differently, the path can be interpreted as valid by the wrong part of the stack. The bug then hides inside the gap between components rather than inside one obvious faulty branch.Hidden complexity in “simple” strings
Strings like:path seem easy to validate, but protocol code has to reconcile RFC-level expectations, library behavior, proxy transformations, and application-specific routing rules. That combination means developers may test the obvious canonical case and still miss one alternate representation. Security bugs thrive in exactly those untested edges.It is also easy to underestimate the effect because the flaw does not resemble a classic exploit primitive. There is no buffer overflow, no RCE chain, and no obvious memory corruption. Yet an auth bypass can be just as serious, especially when the bypass grants access to privileged methods or internal-only APIs. In many real deployments, that is the more dangerous outcome.
The role of test coverage
Protocol libraries need negative tests as much as positive ones. It is not enough to check that/service/method works; you also need to prove that service/method, duplicate slashes, encoded variants, and proxy-rewritten forms do not slip through policy checks. That sort of test discipline is often what separates a robust RPC stack from a brittle one.- Edge-case strings are where policy bugs hide.
- Simple-looking validation rules can mask multi-layer disagreements.
- Auth bypasses can be more damaging than crashes.
- Testing must include malformed and alternate path forms.
- The failure mode often exists between components, not inside one function.
Competitive and Ecosystem Implications
The security implications extend beyond gRPC-Go itself. Any stack that builds on Go-based gRPC services, or that interoperates with them across gateways and proxies, now has another reason to examine path normalization rules. That matters in the cloud-native market, where gRPC is one of the default RPC choices for internal service meshes and high-throughput backend APIs.Impact on cloud-native middleware
Authentication and authorization products that sit in front of gRPC traffic will need to be sure they are not assuming canonical paths too early or too late. If an auth engine compares one representation while the upstream gateway rewrites another, attackers may be able to route around policy in precisely the way the CVE description implies. This is the sort of issue that forces vendors to audit not just their own code, but their interoperability assumptions as well.For competitors in the RPC and service-mesh space, the lesson is uncomfortable but useful: users now expect explicit normalization rules, documented authorization semantics, and hardened edge-case handling. A modern transport stack is no longer judged only by throughput and latency. It is also judged by how predictably it behaves when input is just slightly off-spec.
Why this matters for open source trust
Open-source infrastructure libraries live or die on confidence. Security incidents do not necessarily reduce adoption, but they do raise the bar for operational discipline. Projects that respond quickly, publish clear advisories, and show consistent hardening tend to retain trust better than those that leave users to infer the risk from sparse notes. Microsoft’s Security Update Guide and the upstream gRPC ecosystem both matter here because they help customers make faster remediation decisions.- Cloud-native stacks depend heavily on RPC middleware.
- Interoperability bugs can become vendor ecosystems issues.
- Security documentation is part of product trust.
- Throughput alone is no longer enough to win operator confidence.
- Clear canonicalization rules are becoming a competitive requirement.
How Teams Should Triage It
The first step is to identify where google.golang.org/grpc is used and whether the deployed version includes the fix. Because gRPC is commonly pulled in transitively, teams should inspect build graphs, container images, and vendored dependencies rather than relying on a single manifest file. The upstream repository makes clear that gRPC-Go is distributed as a standard Go module, so version tracking should be straightforward once inventories are accurate.Practical response checklist
- Inventory all Go services that import gRPC directly or indirectly.
- Confirm the exact module version in each binary or container.
- Review any custom authorization middleware that parses
:path. - Check proxies and gateways for path rewriting or normalization behavior.
- Validate that access-control decisions use the same canonical form end to end.
What to look for in logs
Logging can help confirm whether unusual paths are reaching the service, but logs are only useful if the stack preserves the original path form somewhere visible. Security teams should look for non-canonical request targets, proxy rewrites, or method names that appear to have been accepted without the expected leading slash. Those anomalies are often the first clue that a bypass has been tested in the wild.- Find every place gRPC is used, including transitive dependencies.
- Confirm module versions in shipping binaries, not just source trees.
- Audit custom auth middleware for path-string assumptions.
- Examine reverse proxies and service meshes for rewriting behavior.
- Use logs to spot non-canonical requests and suspicious route matches.
Strengths and Opportunities
The good news is that this class of issue is usually fixable without redesigning the entire stack. Because the vulnerability is tied to request normalization and authorization logic, the remediation path is often relatively direct: normalize earlier, compare canonically, and reject nonconforming forms consistently. That makes it a high-value hardening opportunity rather than a structural dead end.- The flaw is narrow enough to patch without rewriting the protocol stack.
- Better canonicalization can improve security across multiple services.
- The issue encourages cleaner separation between transport parsing and auth logic.
- Organizations can add tests that protect against future path-handling regressions.
- Middleware authors can tighten policy checks and reduce ambiguity.
- The broader ecosystem benefits from more explicit documentation of path semantics.
- Microsoft’s disclosure channel helps customers prioritize remediation.
Risks and Concerns
The main concern is that this bug class often exists in more than one layer. If the library fix is deployed but a custom gateway, interceptor, or sidecar still performs its own path interpretation, the bypass may survive in modified form. That is why these incidents are so often systemic rather than isolated.- A patched library may not fix duplicate authorization logic elsewhere.
- Reverse proxies can rewrite paths in ways developers do not expect.
- Multi-service environments make full remediation slower.
- Internal APIs may be assumed safe even when they are reachable.
- Security reviews may miss alternate path representations.
- Teams may underestimate the severity because the bug is “just” a slash issue.
- Inconsistent middleware ordering can preserve the bypass even after upgrades.
Looking Ahead
The most important next step is broader ecosystem confirmation: which gRPC-Go releases are fixed, which Microsoft products or services consumed the vulnerable version, and whether any downstream frameworks duplicated the same path-matching mistake. As with many open-source CVEs, the upstream issue may be easy to name but harder to bound in real deployments. That is why dependency inventory and runtime verification matter as much as the advisory itself.What to watch next
- Patched gRPC-Go release notes and backport status.
- Microsoft’s Update Guide entries for downstream product impact.
- Any guidance on whether a workaround exists for path normalization.
- Evidence of whether proxies or gateways need separate fixes.
- Reports of real-world exploitation or proof-of-concept bypasses.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: