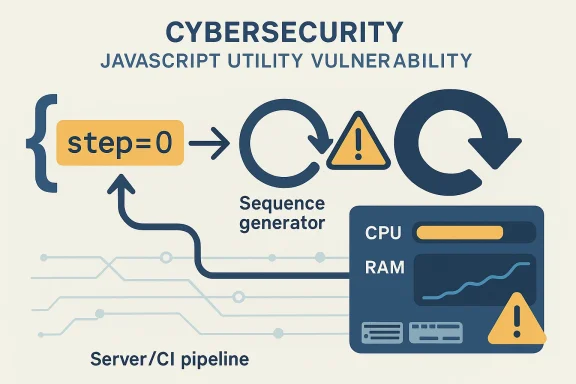
Microsoft’s CVE-2026-33750 entry describes a denial-of-service flaw in the brace-expansion package where a zero-step sequence can drive the process into a hang and memory exhaustion state. The impact language is unambiguous: an attacker can deny availability to the affected component, and in practical terms that means a crafted input can keep the process busy long enough to consume resources and stop serving legitimate work. Public trackers and third-party advisories point to the same core failure mode, with example payloads such as brace patterns using a zero step value causing the sequence generator to loop indefinitely.
The brace-expansion library sits in a deceptively ordinary part of the JavaScript ecosystem. It is not a protocol engine or a cryptography primitive; it is a utility package that expands shell-like patterns into generated sequences. That sort of helper code often seems harmless until it becomes part of a build pipeline, a CLI workflow, or a server-side parser that accepts attacker-controlled strings. Once that happens, a small logic error can become a broad operational problem.
The vulnerability described for CVE-2026-33750 is especially interesting because it is not about memory corruption in the traditional sense. Instead, it is about the algorithm accepting a zero step in a numeric sequence, which can collapse the normal progression logic and push the expansion routine into pathological behavior. In security terms, that moves the issue squarely into the availability category: the code may still be “working” in the narrowest sense, but it is no longer making forward progress in a safe or bounded way.
That distinction matters because developers and defenders often underestimate DoS bugs in parser-adjacent libraries. If a package is used in automation, the impact is not limited to a single request. A hung worker can block deployments, stall CI jobs, tie up API handlers, and trigger watchdog restarts that amplify the blast radius. The result can feel less like a crash and more like an infrastructure slowdown that keeps spreading.
The public record also suggests that the issue is not theoretical. Multiple advisory sites summarize the flaw as a reproducible hang and memory-consumption problem, and at least one notes that the vulnerable versions are older than the patched releases across several major branches. That pattern is common in JavaScript libraries: a bug in a core helper gets propagated through transitive dependencies, and the actual exposure depends on which version line downstream applications happen to carry.
In that sense, CVE-2026-33750 fits a familiar modern security pattern. The code itself is not doing anything exotic; the danger comes from untrusted input meeting a recursive or iterative expansion algorithm. That combination is fertile ground for denial-of-service issues because the attacker does not need to break memory safety to hurt availability. They only need to find an input shape that makes the program spend too much time or allocate too much state.
This is the kind of flaw that often slips through casual testing. Most tests check whether ordinary brace expansion works, not whether edge-case sequence parameters produce a degenerate path. But security bugs frequently live at the boundary where a parameter is syntactically valid yet semantically dangerous. That is exactly the kind of “valid-looking but invalid in context” input that attackers love.
The practical consequence is that an application using brace-expansion may become unresponsive even when the attack payload is tiny. That asymmetry is what makes resource-exhaustion bugs so unpleasant: the attacker sends a small string, and the server or tool burns large amounts of CPU and memory trying to interpret it. The cost imbalance is the vulnerability.
A particularly important detail is that the advisory language emphasizes availability, not confidentiality or integrity. That means defenders should treat this as a service reliability event that crosses into security territory, not as a memory-safety issue that might require a more exotic exploit chain. For many environments, especially build systems and developer infrastructure, denial of service is enough to cause serious business disruption.
This matters because late-stage mitigation often fails to solve the real issue. Once the loop is already running, the process may have consumed too much memory or become trapped in a hot path that is hard to unwind cleanly. Early validation prevents the bad state from being created at all, which is usually the best possible outcome in an expansion library.
For maintainers, the fix also has a backport advantage. A narrow input-check change is much easier to ship to older branches than a structural rewrite of the expansion engine. That lowers regression risk and increases the chance that downstream vendors can absorb the patch quickly. In security work, small and explicit is often better than clever.
That reality also explains why the same CVE can show up in many vulnerability databases with slightly different language. The core bug is the same, but the package versions, advisory phrasing, and remediation guidance can vary by source. The important point is not the wording differences; it is that the underlying exploit primitive remains a zero-step sequence that leads to resource exhaustion.
That makes the vulnerability relevant even in environments where the library is not internet-facing. Internal automation often has broad trust and fewer guardrails than public services, which means an exploit does not need to be flashy to be effective. A single malformed input inserted into a workflow can be enough to saturate resources.
The enterprise angle also matters because modern infrastructure tends to have layered orchestration. A worker hang can trigger health checks, failover, retries, and autoscaling, each of which may create additional load. What starts as a local process problem can become a cluster-level nuisance if the system keeps trying to heal itself without recognizing the input as invalid.
The lesson is broader than one CVE. Utility libraries that appear to be harmless glue often sit on the boundary between trusted and untrusted input. Once a library is used in a server, parser, or automation pipeline, availability bugs become security bugs. That is why packages like this deserve the same seriousness as more obviously dangerous components.
A useful way to think about this class of issue is that the package is doing exactly what it was asked to do, but the request is malformed in a way the code failed to reject. In practice, that means developers should not rely on downstream callers to sanitize everything perfectly. The library itself has to enforce its own invariants.
This is also where consumer impact overlaps with DevOps reality. Many “consumer” uses of JavaScript tooling happen inside package managers, bundlers, release scripts, and developer platforms. Those are not simple desktop applications; they are operational pipelines where a hang can block a team. A small parser flaw can therefore create a large workflow outage.
This is also a good example of why security teams should care about “boring” packages. The library name may not sound high-profile, but the failure mode is operationally serious. Boring software is often the software everyone depends on.
Because the condition is tied to sequence expansion, the attacker’s real leverage is in provoking pathological algorithmic behavior. That means the server may not crash immediately; it may degrade first. Those slow-burn failures are often worse operationally because they are harder to distinguish from ordinary load spikes.
The public descriptions do not suggest code execution or data theft. That does not make the issue benign. In the right place, a reliable hang is enough to interrupt service, block automation, or create cascading retry storms. In modern systems, that is a meaningful attack result.
From a defender’s perspective, this means rate limiting and input validation are complementary but not interchangeable. If the parser itself accepts a degenerate sequence, the safest fix is to remove that acceptance entirely. Rate controls may reduce the pressure, but they do not solve the root cause.
This principle is familiar across software security, but it bears repeating because developers still drift toward defensive code deeper in the call chain. That may be acceptable for handling ordinary errors, but it is weaker against resource-exhaustion bugs. In a hostile environment, fail fast is usually the right answer.
The issue also reinforces the importance of testing edge-case semantics, not just syntax. A pattern can be valid enough to parse while still being dangerous to execute. That is exactly where security bugs hide: in the gap between “can be read” and “should be processed.”
It is also a reminder that maintainers deserve credit when they ship narrow fixes across multiple release lines. Security work is often unglamorous, but the quality of the patch determines whether downstream teams can remediate quickly. A clean fix is a security control in its own right.
The second concern is behavioral. Even a fixed version can leave behind operational habits that still accept risky input shapes. If validation is not added at the application layer where appropriate, another package or another code path may reproduce the same mistake later. That is the long tail of parser bugs.
Security teams should also watch for related advisories in adjacent parsing or expansion libraries. When a bug like this appears, it is often a sign that other edge-case validators deserve a second look. The next finding may not be identical, but it will likely rhyme with this one.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
The brace-expansion library sits in a deceptively ordinary part of the JavaScript ecosystem. It is not a protocol engine or a cryptography primitive; it is a utility package that expands shell-like patterns into generated sequences. That sort of helper code often seems harmless until it becomes part of a build pipeline, a CLI workflow, or a server-side parser that accepts attacker-controlled strings. Once that happens, a small logic error can become a broad operational problem.The vulnerability described for CVE-2026-33750 is especially interesting because it is not about memory corruption in the traditional sense. Instead, it is about the algorithm accepting a zero step in a numeric sequence, which can collapse the normal progression logic and push the expansion routine into pathological behavior. In security terms, that moves the issue squarely into the availability category: the code may still be “working” in the narrowest sense, but it is no longer making forward progress in a safe or bounded way.
That distinction matters because developers and defenders often underestimate DoS bugs in parser-adjacent libraries. If a package is used in automation, the impact is not limited to a single request. A hung worker can block deployments, stall CI jobs, tie up API handlers, and trigger watchdog restarts that amplify the blast radius. The result can feel less like a crash and more like an infrastructure slowdown that keeps spreading.
The public record also suggests that the issue is not theoretical. Multiple advisory sites summarize the flaw as a reproducible hang and memory-consumption problem, and at least one notes that the vulnerable versions are older than the patched releases across several major branches. That pattern is common in JavaScript libraries: a bug in a core helper gets propagated through transitive dependencies, and the actual exposure depends on which version line downstream applications happen to carry.
In that sense, CVE-2026-33750 fits a familiar modern security pattern. The code itself is not doing anything exotic; the danger comes from untrusted input meeting a recursive or iterative expansion algorithm. That combination is fertile ground for denial-of-service issues because the attacker does not need to break memory safety to hurt availability. They only need to find an input shape that makes the program spend too much time or allocate too much state.
What the Vulnerability Does
The core issue is straightforward: a brace pattern that uses a zero step in a sequence can confuse the expansion logic into a non-terminating or excessively expensive path. The public descriptions consistently frame the bug as a process hang coupled with memory exhaustion, which suggests the routine is not merely looping forever but also accumulating enough internal state to become increasingly expensive as the loop continues.Why zero is dangerous here
A numeric step of zero is not just “small.” In a sequence generator, it is often nonsensical because it prevents progress from one value to the next. If the code fails to reject that condition early, the algorithm can end up reprocessing the same state repeatedly or generating output until some secondary limit is reached. In a worst case, the library becomes its own denial-of-service engine.This is the kind of flaw that often slips through casual testing. Most tests check whether ordinary brace expansion works, not whether edge-case sequence parameters produce a degenerate path. But security bugs frequently live at the boundary where a parameter is syntactically valid yet semantically dangerous. That is exactly the kind of “valid-looking but invalid in context” input that attackers love.
The practical consequence is that an application using brace-expansion may become unresponsive even when the attack payload is tiny. That asymmetry is what makes resource-exhaustion bugs so unpleasant: the attacker sends a small string, and the server or tool burns large amounts of CPU and memory trying to interpret it. The cost imbalance is the vulnerability.
Observable symptoms
In production, the failure mode can look like several different problems depending on where the package is used. A command-line tool may stall with no output. A long-running service may show rising memory consumption, increased latency, and eventually watchdog-triggered restarts. A containerized workload may be killed by the orchestrator after consuming too much memory. None of those outcomes are identical, but they all point back to the same underlying resource spiral.A particularly important detail is that the advisory language emphasizes availability, not confidentiality or integrity. That means defenders should treat this as a service reliability event that crosses into security territory, not as a memory-safety issue that might require a more exotic exploit chain. For many environments, especially build systems and developer infrastructure, denial of service is enough to cause serious business disruption.
Affected Versions and Fix Pattern
Third-party summaries indicate that the issue affects versions before 5.0.5, 3.0.2, 2.0.3, and 1.1.13, which implies the project maintained fixes across multiple release lines. That is typical for mature libraries with broad downstream usage, because a single dependency may be pinned to different major branches across different applications.Patch strategy
The useful thing about this kind of bug is that the correct fix is usually conceptually simple. The code needs to reject impossible sequence parameters before the expansion logic starts doing work. In other words, if a zero step is invalid, the parser or validator should stop it at the boundary instead of trying to recover deeper in the algorithm. That is the safest and most maintainable approach.This matters because late-stage mitigation often fails to solve the real issue. Once the loop is already running, the process may have consumed too much memory or become trapped in a hot path that is hard to unwind cleanly. Early validation prevents the bad state from being created at all, which is usually the best possible outcome in an expansion library.
For maintainers, the fix also has a backport advantage. A narrow input-check change is much easier to ship to older branches than a structural rewrite of the expansion engine. That lowers regression risk and increases the chance that downstream vendors can absorb the patch quickly. In security work, small and explicit is often better than clever.
Why multiple branches matter
The presence of fixes across several branch lines is a reminder that dependency ecosystems do not move in lockstep. One project may already be on a modern release, while another still uses a long-lived major version for compatibility reasons. Security teams should not assume that one fixed version number solves the problem everywhere; they need to check each branch independently.That reality also explains why the same CVE can show up in many vulnerability databases with slightly different language. The core bug is the same, but the package versions, advisory phrasing, and remediation guidance can vary by source. The important point is not the wording differences; it is that the underlying exploit primitive remains a zero-step sequence that leads to resource exhaustion.
Why This Matters for Enterprise Teams
Enterprise exposure is often bigger than it looks because utility libraries rarely live in one place. Brace expansion can be embedded in build scripts, code generators, deployment tooling, CI systems, and custom automation. If a single malicious or malformed string can wedge a shared automation worker, that becomes an operational incident, not just a coding defect.Build and deployment pipelines
In a CI/CD context, the risk is especially sharp. Many pipelines ingest user-defined parameters, repository metadata, or templated configuration strings. If one of those paths feeds into brace-expansion, an attacker may be able to stall a job runner, tie up build agents, or cause repeated retries that waste compute time. The visible impact could be failed releases rather than a clean application crash.That makes the vulnerability relevant even in environments where the library is not internet-facing. Internal automation often has broad trust and fewer guardrails than public services, which means an exploit does not need to be flashy to be effective. A single malformed input inserted into a workflow can be enough to saturate resources.
The enterprise angle also matters because modern infrastructure tends to have layered orchestration. A worker hang can trigger health checks, failover, retries, and autoscaling, each of which may create additional load. What starts as a local process problem can become a cluster-level nuisance if the system keeps trying to heal itself without recognizing the input as invalid.
Dependency risk
Another issue is transitive exposure. Many administrators do not install brace-expansion directly, but they inherit it through other packages. That makes inventory work essential. If you do not know which applications depend on the vulnerable library, you cannot determine where the hang condition might be reachable.The lesson is broader than one CVE. Utility libraries that appear to be harmless glue often sit on the boundary between trusted and untrusted input. Once a library is used in a server, parser, or automation pipeline, availability bugs become security bugs. That is why packages like this deserve the same seriousness as more obviously dangerous components.
Consumer and Developer Impact
For individual developers, this vulnerability is a reminder that seemingly innocent helper packages can still take down local tooling. A script that expands user-supplied patterns might freeze during execution, burn memory in a tight loop, or leave the shell session waiting indefinitely. That is frustrating on a laptop and damaging in an automated environment.Local tooling and scripts
Developer tooling is especially vulnerable because scripts often trust input from command arguments, config files, and environment variables. A local attacker is not the only concern; accidental misuse can trigger the same failure mode. That is one reason availability bugs in libraries deserve attention even when they are not obviously remote.A useful way to think about this class of issue is that the package is doing exactly what it was asked to do, but the request is malformed in a way the code failed to reject. In practice, that means developers should not rely on downstream callers to sanitize everything perfectly. The library itself has to enforce its own invariants.
This is also where consumer impact overlaps with DevOps reality. Many “consumer” uses of JavaScript tooling happen inside package managers, bundlers, release scripts, and developer platforms. Those are not simple desktop applications; they are operational pipelines where a hang can block a team. A small parser flaw can therefore create a large workflow outage.
What users should notice
The most obvious sign of trouble is a task that does not finish when it should. Memory growth is another clue, especially if a process gets progressively slower before terminating or being killed. When that behavior appears in tooling that accepts brace patterns, the vulnerable library becomes a plausible suspect.This is also a good example of why security teams should care about “boring” packages. The library name may not sound high-profile, but the failure mode is operationally serious. Boring software is often the software everyone depends on.
How Attackers Could Abuse It
The attack model is simple: supply a crafted brace expression that contains a zero-step sequence and let the library do the rest. Because the flaw is about how the expansion routine handles the input, the attacker does not need elevated privileges or a complex exploit chain to trigger the condition.Low-complexity, high-leverage abuse
This is the classic shape of a resource exhaustion bug. The payload is easy to construct, the effect is repeatable, and the defender may not realize what is happening until resource graphs start to climb. If the vulnerable code is reachable in a network service or shared automation layer, the attacker can force repeated stalls at low cost.Because the condition is tied to sequence expansion, the attacker’s real leverage is in provoking pathological algorithmic behavior. That means the server may not crash immediately; it may degrade first. Those slow-burn failures are often worse operationally because they are harder to distinguish from ordinary load spikes.
The public descriptions do not suggest code execution or data theft. That does not make the issue benign. In the right place, a reliable hang is enough to interrupt service, block automation, or create cascading retry storms. In modern systems, that is a meaningful attack result.
Why repeated triggering matters
A single successful trigger may only hang one worker or one process instance. But repeated exploitation can turn a partial slowdown into a sustained outage, especially where the system keeps respawning the affected task. That is why the advisory language about persistent or sustained loss of availability is so important.From a defender’s perspective, this means rate limiting and input validation are complementary but not interchangeable. If the parser itself accepts a degenerate sequence, the safest fix is to remove that acceptance entirely. Rate controls may reduce the pressure, but they do not solve the root cause.
Broader Security Lessons
CVE-2026-33750 is a good reminder that availability bugs deserve the same discipline as memory safety bugs when they affect shared infrastructure. A process that hangs or eats memory on demand can be as disruptive as a crash, especially if the component is on a critical path.Input validation must happen early
The safest place to reject a zero-step sequence is at the boundary where the input is parsed. Once the algorithm has begun expanding the pattern, the system is already spending resources on something it should have refused. Early rejection is not just cleaner; it is cheaper and more robust.This principle is familiar across software security, but it bears repeating because developers still drift toward defensive code deeper in the call chain. That may be acceptable for handling ordinary errors, but it is weaker against resource-exhaustion bugs. In a hostile environment, fail fast is usually the right answer.
The issue also reinforces the importance of testing edge-case semantics, not just syntax. A pattern can be valid enough to parse while still being dangerous to execute. That is exactly where security bugs hide: in the gap between “can be read” and “should be processed.”
Dependency hygiene matters
Another lesson is the value of dependency visibility. If your application uses brace-expansion indirectly, your vulnerability management toolchain needs to know that. Otherwise, you may think you are safe simply because you never imported the package by name. That is a dangerous assumption in a JavaScript ecosystem built on transitive modules.It is also a reminder that maintainers deserve credit when they ship narrow fixes across multiple release lines. Security work is often unglamorous, but the quality of the patch determines whether downstream teams can remediate quickly. A clean fix is a security control in its own right.
Strengths and Opportunities
The strongest part of the response to CVE-2026-33750 is that the problem appears to be technically well understood and comparatively easy to fix. That gives defenders a real chance to close exposure quickly, provided they can identify where the library is used. It also offers a useful opportunity to tighten validation practices in adjacent code.- The fix appears to be narrow and targeted, which usually lowers regression risk.
- The flaw is easy to reason about once the zero-step condition is understood.
- Multiple branch fixes suggest the maintainers addressed broad downstream compatibility needs.
- Security teams can use this CVE to audit transitive dependencies more carefully.
- The bug is a clean example of why early validation matters in parser logic.
- Operational teams can add monitoring for hangs and memory spikes in affected workflows.
- The issue may prompt broader review of algorithmic complexity in utility packages.
Operational upside
There is also an upside for defenders in the clarity of the failure mode. Unlike ambiguous instability bugs, this one has a recognizable trigger shape and a well-defined symptom cluster. That makes it easier to test, easier to monitor, and easier to verify after patching.Risks and Concerns
The main concern is that this kind of flaw can hide in places where teams are not actively watching for it. Utility packages spread quietly through the dependency graph, and a vulnerable copy can survive long after the headline CVE is published. That is especially true in older branches and pinned lockfiles.- Patch lag in downstream projects may leave systems exposed longer than expected.
- Transitive dependencies can make inventory and remediation harder.
- Build systems and automation may be hit harder than public-facing apps.
- Repeated triggering can create persistent operational disruption.
- Monitoring may misclassify the issue as a generic resource spike.
- Systems that auto-restart tasks can amplify the outage.
- Teams may underestimate a DoS bug because it is not a memory-corruption issue.
Hidden exposure
Another concern is false confidence. If an application does not directly call brace-expansion, teams may assume it is irrelevant to them. In reality, many packages arrive through helper libraries and toolchains, and those are often the very places where attacker-controlled strings first enter the system.The second concern is behavioral. Even a fixed version can leave behind operational habits that still accept risky input shapes. If validation is not added at the application layer where appropriate, another package or another code path may reproduce the same mistake later. That is the long tail of parser bugs.
Looking Ahead
What happens next will mostly depend on how quickly the ecosystem upgrades to the patched releases and whether downstream maintainers backport the fix aggressively. The technical problem is simple enough that the real challenge is distribution, not comprehension. That is often the case with library vulnerabilities: the code is easy to fix, but the fleet is hard to clean up.Security teams should also watch for related advisories in adjacent parsing or expansion libraries. When a bug like this appears, it is often a sign that other edge-case validators deserve a second look. The next finding may not be identical, but it will likely rhyme with this one.
- Confirm which products and internal tools depend on brace-expansion.
- Check whether the dependency is pinned below the fixed version lines.
- Add regression tests for zero-step and other degenerate sequence inputs.
- Monitor for unusually long-running jobs and memory growth in affected pipelines.
- Review nearby parser and expander utilities for similar input-validation gaps.
Source: MSRC Security Update Guide - Microsoft Security Response Center