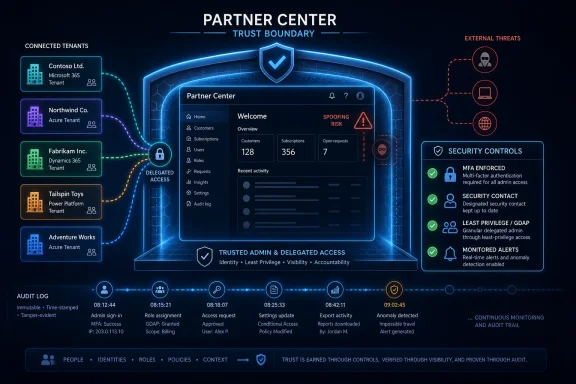
Microsoft disclosed CVE-2026-34327 as a spoofing vulnerability in Microsoft Partner Center in 2026 through the Microsoft Security Response Center, with public information centered on the vulnerability’s existence, product impact, and risk scoring rather than a detailed technical exploit narrative. That sparseness is not a footnote; it is the story. For Partner Center, where Microsoft’s channel ecosystem touches customer tenants, subscriptions, billing, support relationships, and delegated administration, even a vaguely described spoofing flaw deserves more attention than its label might suggest. The practical question for IT is not whether every admin can reverse-engineer the bug today, but whether the trust boundary around the partner channel is being treated with the seriousness it now requires.
Partner Center is not just a business portal with invoices, program enrollment, marketplace offers, and reseller dashboards. For Cloud Solution Provider partners, managed service providers, software vendors, and distributors, it is one of the front doors into a broader Microsoft commercial ecosystem. It sits near delegated relationships, customer administration workflows, security contacts, entitlement checks, offer management, and the operational machinery that lets partners sell, manage, and support Microsoft services.
That makes a Partner Center vulnerability different from a flaw in a local utility or a forgotten desktop component. The risk is not confined to one machine or even one tenant. Partner infrastructure often has a multiplier effect because a single partner may sit upstream of dozens, hundreds, or thousands of customers.
Microsoft has spent the last several years tightening this ecosystem, and not by accident. The company has pushed multifactor authentication for partner tenants, granular delegated admin privileges, security contact requirements, alert-response expectations, and Secure Application Model guidance for API integrations. The subtext is clear: partners are not merely customers of Microsoft’s cloud; they are part of the cloud’s administrative fabric.
That is why CVE-2026-34327’s “spoofing” classification should not be dismissed as low drama. Spoofing sounds softer than remote code execution, and it rarely gets the same oxygen as a wormable Windows bug. But in a portal whose job is to tell users what is authentic, authorized, billable, delegated, or approved, spoofing attacks aim at the layer where people and systems decide what to trust.
The important point is that spoofing is not merely “phishing with a CVE number.” A vulnerability classified as spoofing implies that some part of the affected product may be made to present, accept, or rely on a false assertion. The exploit path may still require user interaction, prior access, tenant context, or a crafted workflow, but the target is the trust decision itself.
That matters acutely in Partner Center because Partner Center is a place where administrative intent is translated into business and cloud action. A partner user may approve a relationship, act on an alert, configure customer access, respond to a Microsoft communication, manage marketplace material, or interact with customer-facing service records. The platform’s visual and logical signals need to be reliable because the downstream blast radius can be much larger than the screen in front of the operator.
The industry has learned this lesson the hard way. The most damaging cloud incidents rarely look like Hollywood-style exploitation after the fact. They look like abused consent, overbroad delegation, stale privileges, trusted automation gone wrong, or a user making a reasonable decision based on a compromised context. Spoofing vulnerabilities belong in that family of risk.
But the absence of exploit detail should not be confused with the absence of risk. Microsoft’s own scoring language around confidence captures the awkward middle ground defenders often inhabit. Sometimes the vendor confirms the issue exists, yet the public does not get enough detail to independently assess exploitability, affected paths, or mitigations beyond the vendor’s fix.
This is where the “confidence” metric becomes more than bureaucratic taxonomy. It is meant to describe how certain the ecosystem can be that a vulnerability exists and how credible the available technical detail is. A confirmed vendor advisory generally moves the existence question out of rumor territory, even if the exploit mechanics remain opaque.
For attackers, sparse detail can slow weaponization. For defenders, sparse detail complicates prioritization. The result is a familiar asymmetry: the people responsible for protecting systems must act with limited information, while the people looking for a way in can spend time probing the edges.
This is the recurring limitation of vulnerability management in cloud platforms. The same CVSS vector can mean different things depending on where the affected component sits. A spoofing issue in a low-value consumer page is one thing. A spoofing issue in an administrative partner portal, even if constrained, carries a different institutional meaning.
Partner Center is also not evenly important to every organization. A small internal IT team with no partner relationships may only need to know that Microsoft has handled a cloud-side issue. A managed service provider living inside Partner Center all day should treat the same CVE as a prompt to review operational assumptions: who can access the portal, which customer relationships exist, which alerts are monitored, and whether administrative workflows rely too heavily on visual trust.
Security teams have become better at asking whether a vulnerability is internet-exposed, unauthenticated, and actively exploited. They are still less disciplined at asking whether a vulnerability sits at a trust aggregation point. Partner Center is exactly that kind of point.
There is almost always something to do, but it is usually procedural rather than binary. Customers and partners should not be hunting for an MSI or waiting for WSUS approval; they should be checking whether their security model assumes Partner Center is a perfectly reliable trust oracle. They should be validating access, reducing standing privilege, reviewing delegated relationships, and making sure alerts are not routed to abandoned mailboxes.
The distinction matters because cloud vulnerability response is less about “install patch, close ticket” and more about “understand whether the vulnerability exposed a weakness in our operating model.” If a spoofing flaw could have affected what users saw or trusted, the response should include logs, sign-ins, relationship changes, consent activity, and unusual administrative behavior.
That does not mean every organization should launch a breach investigation for CVE-2026-34327. Public information does not support panic. But it does mean the advisory should be used as a forcing function to examine whether Partner Center security is owned by a real team or has drifted into the gray zone between procurement, licensing, and IT operations.
That shift is overdue. For years, partner relationships were treated as business conveniences first and security dependencies second. Delegated access made administration easier, but it also created an attractive target: compromise the operator who manages many environments rather than attacking each customer one by one.
Granular delegated admin privileges, or GDAP, is Microsoft’s answer to the old “all or nothing” partner access model. It is not glamorous, and it can be operationally annoying, but it is the sort of control that changes the economics of compromise. Time-bound, least-privileged access is far less useful to an attacker than a standing role with broad reach.
A spoofing vulnerability in Partner Center should therefore be viewed in the same frame. The bug may be Microsoft’s to fix, but the blast radius is shaped by partner hygiene. A well-run partner tenant with MFA, dedicated admin accounts, minimal GDAP roles, monitored alerts, and sane approval workflows is harder to turn into a customer-wide incident.
Spoofing thrives in precisely that environment. If an attacker can cause a user to believe an action, message, interface state, tenant identity, or relationship is legitimate, the exploit does not need to look like malware. It can look like a workflow.
This is why defenders should avoid thinking about spoofing only as a browser trick. In a mature attack chain, spoofing can be the connective tissue between identity compromise and privilege abuse. It can help move a victim from suspicion to action, or help an attacker hide inside a process that already exists.
Partner Center’s role in the Microsoft economy gives such deception extra leverage. A partner administrator is accustomed to handling customer context switches, tenant names, subscription references, reseller relationships, and Microsoft-generated notifications. The more normal complexity exists in the interface, the more valuable it becomes for an attacker to bend a trust signal.
This is a deceptively hard test. Many organizations have mature endpoint telemetry and weak SaaS administration telemetry. They can tell you which workstation launched PowerShell, but not always which partner user changed a delegated relationship or responded to a security alert.
The answer is not to create a new spreadsheet for every CVE. The answer is to treat Partner Center as a privileged administrative plane and integrate it into normal security operations. That includes ownership, logging, access review, incident runbooks, and escalation paths that do not depend on one licensing administrator remembering to forward an email.
Microsoft’s requirement for a security contact is a small but revealing example. The company has learned that sending security mail to a generic admin address is not enough. In a crisis, the difference between a live security contact and an unattended mailbox can be the difference between containment and customer harm.
For enterprise customers, the relevant question is not only whether their own tenant is patched or protected. It is whether their partner relationships are necessary, bounded, and observable. If a reseller or MSP has delegated access, that access should be justified by current work, constrained by least privilege, and reviewed regularly.
Customers should also understand which partner has which role. Too many tenants accumulate stale relationships over time: a migration partner from three years ago, a licensing reseller from a previous contract, an MSP that no longer manages the environment, or a vendor granted access during an emergency. Each relationship is a trust path.
CVE-2026-34327 does not prove those paths were abused. It does remind us that the administrative ecosystem around Microsoft 365 and Azure is part of the attack surface. If customers treat partner relationships as paperwork rather than security architecture, they are leaving risk unpriced.
That shortcut can be dangerous in identity-heavy systems. A spoofing vulnerability in an administrative workflow can be closer to privilege escalation than the label suggests, depending on what it allows the attacker to misrepresent. Likewise, an information disclosure flaw can become credential theft if the exposed information is a token, secret, or recovery path.
The right response is contextual triage. Ask where the flaw lives, what trust decision it may influence, and whether the affected system brokers access to other systems. By that standard, Partner Center deserves a careful read.
This is not an argument for treating every Microsoft cloud CVE as a five-alarm fire. It is an argument against lazy severity sorting. A vulnerability’s category is the beginning of the analysis, not the end of it.
Less mature organizations do one of two things. They either ignore the CVE because there is no patch to deploy, or they overreact because there is no exploit detail to disprove their worst-case assumptions. Both reactions miss the point.
The productive middle ground is to use the advisory to test the organization’s posture. Who owns Partner Center? Are all administrative users protected with phishing-resistant MFA where possible? Are privileged accounts separate from daily-use accounts? Are customer delegated relationships reviewed? Are Partner Center alerts routed into a monitored queue? Are API integrations using secure application patterns rather than legacy credential flows?
Those questions are more valuable than speculation about exploit internals. They are also the questions that will matter again when the next Partner Center or Microsoft cloud administration CVE arrives.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft’s Partner Channel Has Become a Security Boundary
Microsoft’s Partner Channel Has Become a Security Boundary
Partner Center is not just a business portal with invoices, program enrollment, marketplace offers, and reseller dashboards. For Cloud Solution Provider partners, managed service providers, software vendors, and distributors, it is one of the front doors into a broader Microsoft commercial ecosystem. It sits near delegated relationships, customer administration workflows, security contacts, entitlement checks, offer management, and the operational machinery that lets partners sell, manage, and support Microsoft services.That makes a Partner Center vulnerability different from a flaw in a local utility or a forgotten desktop component. The risk is not confined to one machine or even one tenant. Partner infrastructure often has a multiplier effect because a single partner may sit upstream of dozens, hundreds, or thousands of customers.
Microsoft has spent the last several years tightening this ecosystem, and not by accident. The company has pushed multifactor authentication for partner tenants, granular delegated admin privileges, security contact requirements, alert-response expectations, and Secure Application Model guidance for API integrations. The subtext is clear: partners are not merely customers of Microsoft’s cloud; they are part of the cloud’s administrative fabric.
That is why CVE-2026-34327’s “spoofing” classification should not be dismissed as low drama. Spoofing sounds softer than remote code execution, and it rarely gets the same oxygen as a wormable Windows bug. But in a portal whose job is to tell users what is authentic, authorized, billable, delegated, or approved, spoofing attacks aim at the layer where people and systems decide what to trust.
Spoofing Is the Quiet Failure Mode of Cloud Administration
In classic desktop security, spoofing often meant a fake dialog, a misleading file extension, or a visual trick that convinced a user to click the wrong thing. In cloud administration, the category can be broader and more consequential. A spoofing vulnerability may involve user-interface deception, identity confusion, token or redirect handling issues, domain or tenant misrepresentation, message authenticity problems, or a trust signal that can be made to say something it should not.The important point is that spoofing is not merely “phishing with a CVE number.” A vulnerability classified as spoofing implies that some part of the affected product may be made to present, accept, or rely on a false assertion. The exploit path may still require user interaction, prior access, tenant context, or a crafted workflow, but the target is the trust decision itself.
That matters acutely in Partner Center because Partner Center is a place where administrative intent is translated into business and cloud action. A partner user may approve a relationship, act on an alert, configure customer access, respond to a Microsoft communication, manage marketplace material, or interact with customer-facing service records. The platform’s visual and logical signals need to be reliable because the downstream blast radius can be much larger than the screen in front of the operator.
The industry has learned this lesson the hard way. The most damaging cloud incidents rarely look like Hollywood-style exploitation after the fact. They look like abused consent, overbroad delegation, stale privileges, trusted automation gone wrong, or a user making a reasonable decision based on a compromised context. Spoofing vulnerabilities belong in that family of risk.
The Sparse Advisory Is a Feature of the Disclosure System, Not a Comfort
The public entry for CVE-2026-34327 is notable for what it does not appear to provide: a full root-cause breakdown, proof-of-concept exploit, or step-by-step attacker workflow. That is common for Microsoft Security Update Guide entries, especially for cloud services or portal-side mitigations. The disclosure model is designed to inform defenders without handing attackers a recipe.But the absence of exploit detail should not be confused with the absence of risk. Microsoft’s own scoring language around confidence captures the awkward middle ground defenders often inhabit. Sometimes the vendor confirms the issue exists, yet the public does not get enough detail to independently assess exploitability, affected paths, or mitigations beyond the vendor’s fix.
This is where the “confidence” metric becomes more than bureaucratic taxonomy. It is meant to describe how certain the ecosystem can be that a vulnerability exists and how credible the available technical detail is. A confirmed vendor advisory generally moves the existence question out of rumor territory, even if the exploit mechanics remain opaque.
For attackers, sparse detail can slow weaponization. For defenders, sparse detail complicates prioritization. The result is a familiar asymmetry: the people responsible for protecting systems must act with limited information, while the people looking for a way in can spend time probing the edges.
CVSS Scores Do Not Capture Partner Blast Radius Cleanly
A CVE entry can tell you severity, attack complexity, privileges required, user interaction, scope, and impact characteristics. Those are useful dimensions, but they are not a complete model of business exposure. In the Microsoft partner ecosystem, a technically moderate flaw can become operationally serious if it intersects with delegated administration, reseller relationships, marketplace workflows, or customer trust.This is the recurring limitation of vulnerability management in cloud platforms. The same CVSS vector can mean different things depending on where the affected component sits. A spoofing issue in a low-value consumer page is one thing. A spoofing issue in an administrative partner portal, even if constrained, carries a different institutional meaning.
Partner Center is also not evenly important to every organization. A small internal IT team with no partner relationships may only need to know that Microsoft has handled a cloud-side issue. A managed service provider living inside Partner Center all day should treat the same CVE as a prompt to review operational assumptions: who can access the portal, which customer relationships exist, which alerts are monitored, and whether administrative workflows rely too heavily on visual trust.
Security teams have become better at asking whether a vulnerability is internet-exposed, unauthenticated, and actively exploited. They are still less disciplined at asking whether a vulnerability sits at a trust aggregation point. Partner Center is exactly that kind of point.
Microsoft’s Cloud Fixes Often Leave Customers With Process Work
For many Microsoft cloud vulnerabilities, the direct patching burden is lighter than it is for Windows Server, Exchange, SQL Server, or SharePoint on-premises. If the affected service is fully hosted by Microsoft, the mitigation may already be deployed server-side by the time most customers read the advisory. That can create the pleasant illusion that there is nothing to do.There is almost always something to do, but it is usually procedural rather than binary. Customers and partners should not be hunting for an MSI or waiting for WSUS approval; they should be checking whether their security model assumes Partner Center is a perfectly reliable trust oracle. They should be validating access, reducing standing privilege, reviewing delegated relationships, and making sure alerts are not routed to abandoned mailboxes.
The distinction matters because cloud vulnerability response is less about “install patch, close ticket” and more about “understand whether the vulnerability exposed a weakness in our operating model.” If a spoofing flaw could have affected what users saw or trusted, the response should include logs, sign-ins, relationship changes, consent activity, and unusual administrative behavior.
That does not mean every organization should launch a breach investigation for CVE-2026-34327. Public information does not support panic. But it does mean the advisory should be used as a forcing function to examine whether Partner Center security is owned by a real team or has drifted into the gray zone between procurement, licensing, and IT operations.
The Partner Security Baseline Is No Longer Optional Hygiene
Microsoft’s recent Partner Center security requirements are best read as a map of where the company believes the risk is concentrated. Mandatory MFA for administrative users, security contact designation, rapid alert response, Secure Application Model adoption, and least-privilege delegated administration all point in the same direction. Microsoft wants fewer permanent, high-trust partner paths into customer tenants, and it wants incidents to land in front of people who can actually respond.That shift is overdue. For years, partner relationships were treated as business conveniences first and security dependencies second. Delegated access made administration easier, but it also created an attractive target: compromise the operator who manages many environments rather than attacking each customer one by one.
Granular delegated admin privileges, or GDAP, is Microsoft’s answer to the old “all or nothing” partner access model. It is not glamorous, and it can be operationally annoying, but it is the sort of control that changes the economics of compromise. Time-bound, least-privileged access is far less useful to an attacker than a standing role with broad reach.
A spoofing vulnerability in Partner Center should therefore be viewed in the same frame. The bug may be Microsoft’s to fix, but the blast radius is shaped by partner hygiene. A well-run partner tenant with MFA, dedicated admin accounts, minimal GDAP roles, monitored alerts, and sane approval workflows is harder to turn into a customer-wide incident.
Attackers Love the Places Where Business Trust Becomes Technical Trust
The channel ecosystem is attractive because it blends business legitimacy with technical permission. Partners send real emails, operate real portals, manage real subscriptions, and have real reasons to request access. That makes malicious activity harder to distinguish from the background noise of ordinary administration.Spoofing thrives in precisely that environment. If an attacker can cause a user to believe an action, message, interface state, tenant identity, or relationship is legitimate, the exploit does not need to look like malware. It can look like a workflow.
This is why defenders should avoid thinking about spoofing only as a browser trick. In a mature attack chain, spoofing can be the connective tissue between identity compromise and privilege abuse. It can help move a victim from suspicion to action, or help an attacker hide inside a process that already exists.
Partner Center’s role in the Microsoft economy gives such deception extra leverage. A partner administrator is accustomed to handling customer context switches, tenant names, subscription references, reseller relationships, and Microsoft-generated notifications. The more normal complexity exists in the interface, the more valuable it becomes for an attacker to bend a trust signal.
The Real Test Is Whether Partners Can Reconstruct Trust After the Fact
When a vulnerability lacks public technical detail, defenders should focus on evidence they can actually gather. For Partner Center, that means asking whether the organization can reconstruct who accessed the portal, what roles they held, which customer relationships changed, what alerts were acknowledged, and whether any administrative action occurred outside normal patterns.This is a deceptively hard test. Many organizations have mature endpoint telemetry and weak SaaS administration telemetry. They can tell you which workstation launched PowerShell, but not always which partner user changed a delegated relationship or responded to a security alert.
The answer is not to create a new spreadsheet for every CVE. The answer is to treat Partner Center as a privileged administrative plane and integrate it into normal security operations. That includes ownership, logging, access review, incident runbooks, and escalation paths that do not depend on one licensing administrator remembering to forward an email.
Microsoft’s requirement for a security contact is a small but revealing example. The company has learned that sending security mail to a generic admin address is not enough. In a crisis, the difference between a live security contact and an unattended mailbox can be the difference between containment and customer harm.
Enterprise IT Should Read This as a Supply-Chain Signal
The phrase supply chain has been stretched nearly to meaninglessness, but Partner Center is one of the places where the term still has teeth. It is not a third-party library buried in an application. It is a live administrative and commercial relationship between Microsoft, partners, and customers.For enterprise customers, the relevant question is not only whether their own tenant is patched or protected. It is whether their partner relationships are necessary, bounded, and observable. If a reseller or MSP has delegated access, that access should be justified by current work, constrained by least privilege, and reviewed regularly.
Customers should also understand which partner has which role. Too many tenants accumulate stale relationships over time: a migration partner from three years ago, a licensing reseller from a previous contract, an MSP that no longer manages the environment, or a vendor granted access during an emergency. Each relationship is a trust path.
CVE-2026-34327 does not prove those paths were abused. It does remind us that the administrative ecosystem around Microsoft 365 and Azure is part of the attack surface. If customers treat partner relationships as paperwork rather than security architecture, they are leaving risk unpriced.
The Word “Spoofing” Should Not Lower the Priority by Itself
Security teams often triage by category, and that is understandable. Remote code execution and elevation of privilege tend to jump the line. Spoofing, information disclosure, and denial of service often fall behind unless there is public exploitation.That shortcut can be dangerous in identity-heavy systems. A spoofing vulnerability in an administrative workflow can be closer to privilege escalation than the label suggests, depending on what it allows the attacker to misrepresent. Likewise, an information disclosure flaw can become credential theft if the exposed information is a token, secret, or recovery path.
The right response is contextual triage. Ask where the flaw lives, what trust decision it may influence, and whether the affected system brokers access to other systems. By that standard, Partner Center deserves a careful read.
This is not an argument for treating every Microsoft cloud CVE as a five-alarm fire. It is an argument against lazy severity sorting. A vulnerability’s category is the beginning of the analysis, not the end of it.
The Disclosure Gap Is Where Security Programs Show Their Maturity
When the public record is thin, mature organizations do not freeze. They make bounded decisions. They identify affected assets and workflows, check whether the vendor has mitigated the service, look for signs of exploitation if logs are available, and adjust controls that would reduce future impact.Less mature organizations do one of two things. They either ignore the CVE because there is no patch to deploy, or they overreact because there is no exploit detail to disprove their worst-case assumptions. Both reactions miss the point.
The productive middle ground is to use the advisory to test the organization’s posture. Who owns Partner Center? Are all administrative users protected with phishing-resistant MFA where possible? Are privileged accounts separate from daily-use accounts? Are customer delegated relationships reviewed? Are Partner Center alerts routed into a monitored queue? Are API integrations using secure application patterns rather than legacy credential flows?
Those questions are more valuable than speculation about exploit internals. They are also the questions that will matter again when the next Partner Center or Microsoft cloud administration CVE arrives.
The Concrete Work Hiding Behind One Sparse CVE
CVE-2026-34327 is not a call to panic, but it is a useful pressure test for any organization that depends on Microsoft’s partner ecosystem. The advisory’s lack of public exploit detail makes the confidence and context signals more important, not less important.- Microsoft has identified CVE-2026-34327 as a spoofing vulnerability affecting Microsoft Partner Center, a platform that sits close to partner and customer trust relationships.
- The public record does not appear to provide enough technical detail for defenders to independently reconstruct the exploit path, so organizations should avoid unsupported claims about root cause or active abuse.
- Partner Center should be treated as a privileged administrative plane, not merely a licensing or commerce portal.
- Partners should verify MFA enforcement, security contact accuracy, alert response ownership, API authentication practices, and the scope of delegated customer access.
- Customers should review partner relationships and remove stale or unnecessary delegated access rather than assuming reseller links are harmless business metadata.
- Security teams should triage spoofing vulnerabilities by context, especially when the affected system influences identity, delegation, billing, or administrative trust.
Source: MSRC Security Update Guide - Microsoft Security Response Center