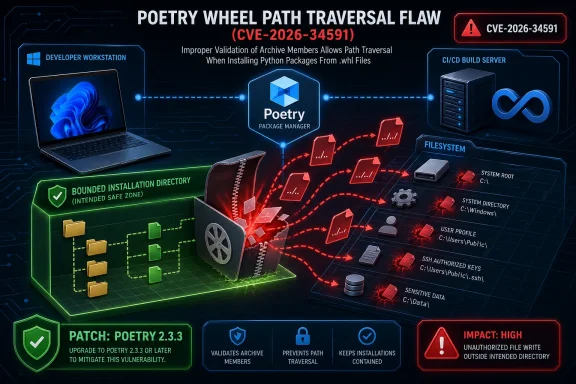
CVE-2026-34591 is a reminder that the most dangerous software supply chain bugs are not always found in operating systems, browsers, or cloud control planes. This newly disclosed Poetry wheel path traversal vulnerability affects a widely used Python dependency and packaging tool, allowing a crafted wheel file to write outside its intended installation directory when handled by vulnerable Poetry versions. The fix is already available in Poetry 2.3.3, but the real story is broader: modern developer workstations, Windows build agents, and CI/CD pipelines now depend on package installers as deeply trusted infrastructure.
Poetry has become one of the most recognizable tools in the Python ecosystem because it combines dependency management, packaging, lockfile handling, virtual environment orchestration, and publishing workflows behind a single command-line interface. For many teams, it replaced older combinations of
That convenience is exactly why a flaw in Poetry’s installation path matters. Package managers operate at a privileged point in the software lifecycle: they fetch untrusted artifacts, unpack them, place files into project environments, and often run inside developer machines or automated build systems that hold credentials. A bug in that layer may not look dramatic at first glance, but it can become a stepping stone for supply chain compromise.
CVE-2026-34591 affects Poetry versions from 1.4.0 through 2.3.2. The issue is fixed in Poetry 2.3.3, which changes how the wheel installer resolves and validates destination paths before writing files. The vulnerability is classified as a path traversal issue, specifically tied to insufficient containment checks when installing crafted wheel contents.
The key technical point is simple but serious: a malicious wheel can include file paths that attempt to escape the target install directory. If Poetry trusts those paths too much, it may write files somewhere else on disk using the permissions of the Poetry process. That makes the bug especially relevant to Windows developers, build servers, and organizations that install packages from internal indexes, mirrored repositories, or less-trusted sources.
The vulnerability sits in the gap between archive structure and filesystem reality. A file entry that appears to belong inside a package can resolve to a different location once the operating system interprets the path. That difference is why secure installers need canonicalization and containment checks before any write occurs.
A malicious wheel could attempt to overwrite or create files outside the virtual environment. On Windows, that might mean targeting project files, configuration files, script directories, or user-level automation hooks. On Linux build agents, the same class of bug could target shell profiles, cache directories, service files, or application-specific configuration paths.
Key exposure scenarios include:
The patched release, Poetry 2.3.3, changes the wheel installation logic so destination paths are resolved before writing. The installer then verifies that the resulting target remains inside the intended directory. If the resolved target escapes that boundary, installation is aborted rather than allowed to continue.
A clean upgrade plan should account for every place Poetry exists:
Secure extraction requires more than checking whether a string looks reasonable. Filesystem paths can be tricky because relative components, symbolic links, drive roots, separators, and platform-specific behavior can all affect the final destination. The safe pattern is to resolve the target path and confirm that it remains beneath the approved directory.
The Poetry fix follows the right conceptual model: determine the real target location, compare it to the resolved intended directory, and reject anything outside that boundary. That is the difference between trusting archive metadata and enforcing filesystem containment.
Important technical lessons include:
A malicious file write on Windows does not need administrator privileges to cause damage. User-writable locations can still influence future behavior. Developer profile folders, project directories, script paths, and tool configuration files are often enough to create persistence or trigger code execution later.
Potentially sensitive areas include:
Poetry is commonly used in workflows that create deployable Python applications, build wheels, run tests, and publish packages. If a malicious dependency enters that workflow, a vulnerable installer may write outside the expected environment. Even without immediate execution, that write can alter later pipeline stages.
Defenders should focus on the build graph, not only the workstation:
That difference is not unusual. CVSS 4.0 attempts to express some characteristics differently, while CVSS 3.1 remains deeply embedded in enterprise scanners and dashboards. Security teams should avoid treating the lower label as a reason to delay remediation when Poetry is used in automated build systems.
The scoring also does not fully capture environmental multipliers:
That approach matters because the installer no longer relies on the archive entry’s apparent structure. Instead, it asks the filesystem-aware question: after resolution, where would this file actually be written? That is the correct security boundary.
A good containment fix should provide:
The first step is to find all Poetry installations in developer environments, build images, CI runners, and internal scripts. The second step is to update to Poetry 2.3.3 or later. The third step is to review package provenance and caches, especially if any organization installs from internal mirrors or third-party package feeds.
Most hobbyist users are unlikely to be targeted directly through this specific CVE. However, opportunistic supply chain attacks often do not need to target individuals by name. Attackers can publish typosquatted packages, compromise maintainer accounts, or poison dependencies used by many projects.
Recommended steps include:
For Poetry’s competitors and adjacent tools, the lesson is not “Poetry is uniquely unsafe.” The lesson is that package installation is security-critical code. Pip, uv, PDM, Hatch, Conda, and internal enterprise installers all live in the same risk neighborhood when handling archives, paths, scripts, and metadata.
Tooling vendors and open-source maintainers can differentiate through:
The defensive model should assume that any package artifact may be hostile until proven otherwise. That does not mean developers should stop using package managers. It means the ecosystem needs layered controls so one malicious artifact cannot silently reshape a workstation or pipeline.
Strong controls include:
Organizations should also monitor whether related installer bugs surface in other packaging tools. The same defensive concepts apply across ecosystems: archive entries must be treated as hostile, destination paths must be resolved, and writes must be contained. Any tool that unpacks third-party artifacts into trusted environments deserves review.
Watch these areas closely:
CVE-2026-34591 will likely be remembered less as a catastrophic standalone flaw and more as another warning about the hidden trust placed in developer tooling. Poetry’s fix is available, clear, and worth deploying immediately, but the broader lesson is durable: package managers are part of the security perimeter. In 2026, protecting Windows workstations and CI/CD systems means patching not only the operating system and applications, but also the quiet build tools that decide which files land where.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Poetry has become one of the most recognizable tools in the Python ecosystem because it combines dependency management, packaging, lockfile handling, virtual environment orchestration, and publishing workflows behind a single command-line interface. For many teams, it replaced older combinations of setup.py, requirements.txt, Pipfile, and ad hoc build scripts with a more structured pyproject.toml-based workflow.That convenience is exactly why a flaw in Poetry’s installation path matters. Package managers operate at a privileged point in the software lifecycle: they fetch untrusted artifacts, unpack them, place files into project environments, and often run inside developer machines or automated build systems that hold credentials. A bug in that layer may not look dramatic at first glance, but it can become a stepping stone for supply chain compromise.
CVE-2026-34591 affects Poetry versions from 1.4.0 through 2.3.2. The issue is fixed in Poetry 2.3.3, which changes how the wheel installer resolves and validates destination paths before writing files. The vulnerability is classified as a path traversal issue, specifically tied to insufficient containment checks when installing crafted wheel contents.
The key technical point is simple but serious: a malicious wheel can include file paths that attempt to escape the target install directory. If Poetry trusts those paths too much, it may write files somewhere else on disk using the permissions of the Poetry process. That makes the bug especially relevant to Windows developers, build servers, and organizations that install packages from internal indexes, mirrored repositories, or less-trusted sources.
What CVE-2026-34591 Actually Allows
At its core, CVE-2026-34591 is an arbitrary file write vulnerability caused by wheel path traversal. A Python wheel is a ZIP-based package format, and its internal file names tell the installer where package content should land. If those names contain traversal components such as parent-directory references, a vulnerable installer must reject them rather than blindly joining them to the install location.The vulnerability sits in the gap between archive structure and filesystem reality. A file entry that appears to belong inside a package can resolve to a different location once the operating system interprets the path. That difference is why secure installers need canonicalization and containment checks before any write occurs.
Why arbitrary file write matters
An arbitrary file write is not automatically the same thing as remote code execution. However, it can become extremely powerful depending on where the attacker can place files and what happens next. In development environments, many files are later imported, executed, sourced, or read by tools with elevated trust.A malicious wheel could attempt to overwrite or create files outside the virtual environment. On Windows, that might mean targeting project files, configuration files, script directories, or user-level automation hooks. On Linux build agents, the same class of bug could target shell profiles, cache directories, service files, or application-specific configuration paths.
Key exposure scenarios include:
- Developers installing a malicious dependency during normal project setup.
- CI/CD systems restoring dependencies from a compromised package source.
- Internal package repositories serving a tampered wheel after account or pipeline compromise.
- Automated tooling installing packages without human review.
- Build images running Poetry with broader filesystem permissions than necessary.
Affected Versions and the Patch
The vulnerable range covers Poetry 1.4.0 up to, but not including, 2.3.3. In other words, anyone running Poetry 2.3.2 or older within that range should treat the update as urgent, especially if Poetry is used in automation or with packages from sources that are not fully controlled.The patched release, Poetry 2.3.3, changes the wheel installation logic so destination paths are resolved before writing. The installer then verifies that the resulting target remains inside the intended directory. If the resolved target escapes that boundary, installation is aborted rather than allowed to continue.
The practical upgrade message
For most users, the remediation is straightforward: upgrade Poetry to 2.3.3 or later. The challenge is that Poetry is often installed in several different ways. Some users install it throughpipx, others use the official installer, some pin it in a toolchain image, and others install it inside Docker layers or CI bootstrap scripts.A clean upgrade plan should account for every place Poetry exists:
- Check local developer machines for Poetry versions.
- Check CI runners and build containers.
- Check reusable workflow templates.
- Check internal developer setup scripts.
- Check base images used by Python projects.
- Rebuild cached images that may still contain vulnerable Poetry versions.
How the Wheel Path Traversal Works
A Python wheel contains package files and metadata. During installation, the installer reads entries from the archive and writes them into scheme-specific destinations such as library, scripts, headers, or data directories. The vulnerability arises when an entry path from the wheel is treated as safe input and combined with a destination directory without adequate containment validation.Secure extraction requires more than checking whether a string looks reasonable. Filesystem paths can be tricky because relative components, symbolic links, drive roots, separators, and platform-specific behavior can all affect the final destination. The safe pattern is to resolve the target path and confirm that it remains beneath the approved directory.
Why simple string checks are not enough
Path traversal bugs survive because developers often underestimate path complexity. A string prefix check can fail when paths contain symbolic links, mixed separators, encoded forms, or normalization quirks. On Windows, additional complexity comes from drive letters, UNC paths, backslashes, reserved device names, and legacy path behavior.The Poetry fix follows the right conceptual model: determine the real target location, compare it to the resolved intended directory, and reject anything outside that boundary. That is the difference between trusting archive metadata and enforcing filesystem containment.
Important technical lessons include:
- Archive entries are untrusted input, even when the archive format is familiar.
- Path joining is not validation, because the resulting path may still escape.
- Resolved paths must be checked against resolved roots.
- Symbolic links require explicit consideration.
- Tests should include malicious archive entries, not only normal package layouts.
Why Windows Developers Should Pay Attention
Windows users are not uniquely affected, but the Windows development environment creates several interesting risk paths. Many Python developers on Windows run Poetry from user-space installations, often through the Microsoft Store version of Python,pipx, PowerShell profiles, Windows Terminal sessions, or IDE-integrated shells. Those environments can contain persistent credentials and automation shortcuts.A malicious file write on Windows does not need administrator privileges to cause damage. User-writable locations can still influence future behavior. Developer profile folders, project directories, script paths, and tool configuration files are often enough to create persistence or trigger code execution later.
Windows-specific exposure points
The risk is especially relevant where Poetry runs with access to broad workspace directories. A developer might install dependencies while inside a repository that contains build scripts, test hooks, IDE configuration, or generated artifacts. If a crafted wheel writes outside the virtual environment, the attacker may try to influence the next command the developer runs.Potentially sensitive areas include:
- PowerShell profile files used to customize shell startup behavior.
- User-level script directories included in the
PATH. - Project automation files used by test runners or task launchers.
- IDE configuration files that influence debugging or build behavior.
- CI workspace files that are reused across build stages.
- Credential-adjacent configuration for package indexes or cloud tooling.
CI/CD Pipelines Are the Bigger Target
The most concerning impact is not a single hobbyist installing a suspicious package. The bigger concern is CI/CD infrastructure, where dependency installation happens automatically, repeatedly, and often with access to secrets. Build agents may hold package publishing tokens, source repository credentials, signing keys, deployment credentials, or cloud access tokens.Poetry is commonly used in workflows that create deployable Python applications, build wheels, run tests, and publish packages. If a malicious dependency enters that workflow, a vulnerable installer may write outside the expected environment. Even without immediate execution, that write can alter later pipeline stages.
Why automation amplifies the bug
Automation removes friction. That is good for productivity, but dangerous when trust assumptions fail. A CI job may install dependencies from a lockfile, a private package index, or a build artifact cache without any interactive prompt. If the underlying artifact has been poisoned, the pipeline may process it as routine input.Defenders should focus on the build graph, not only the workstation:
- Ephemeral runners reduce persistence, but they do not eliminate secret exposure during a job.
- Long-lived self-hosted runners increase risk, especially when workspaces are reused.
- Shared caches can preserve malicious artifacts after the original source is fixed.
- Private package indexes can become single points of failure.
- Build stages may trust files created by earlier stages.
Severity: Medium Score, High Operational Relevance
The public scoring around CVE-2026-34591 reflects an important tension in vulnerability management. Under CVSS 3.1, the issue has been assessed as 6.5 Medium, reflecting network attack vector, low complexity, no privileges required, user interaction required, unchanged scope, high integrity impact, and no direct confidentiality or availability impact. Under CVSS 4.0 scoring from the CNA, it lands as 7.1 High.That difference is not unusual. CVSS 4.0 attempts to express some characteristics differently, while CVSS 3.1 remains deeply embedded in enterprise scanners and dashboards. Security teams should avoid treating the lower label as a reason to delay remediation when Poetry is used in automated build systems.
Why scoring can understate supply chain risk
The vulnerability requires a malicious or compromised wheel to be installed. That requirement introduces user interaction or workflow participation, which pulls the score down. But in developer ecosystems, installing packages is exactly what the tool is designed to do.The scoring also does not fully capture environmental multipliers:
- A build server may have signing or publishing permissions.
- A developer workstation may have access to private repositories.
- A CI job may run immediately before deployment.
- A poisoned internal package may be trusted by many downstream projects.
- A lockfile may preserve a malicious artifact reference.
The Fix: Resolve, Contain, Abort
The Poetry patch is conceptually clean. Before writing wheel content to disk, Poetry resolves the destination directory and the candidate target path. It then checks whether the target remains within the intended scheme directory. If it does not, installation fails.That approach matters because the installer no longer relies on the archive entry’s apparent structure. Instead, it asks the filesystem-aware question: after resolution, where would this file actually be written? That is the correct security boundary.
What changed in defensive terms
The change also adds regression coverage around malicious wheels and symlinked targets. That matters because path traversal defenses can be brittle when tests only cover obvious../ strings. Real-world bypasses often exploit edge cases around symlinks, path normalization, platform separators, or preexisting directories.A good containment fix should provide:
- Canonical path resolution before write operations.
- Comparison against an approved root directory.
- Rejection rather than sanitization for unsafe archive entries.
- Test coverage for traversal payloads.
- Test coverage for symlinked install paths.
- Predictable failure behavior for security violations.
Enterprise Response Playbook
Enterprise teams should treat CVE-2026-34591 as a toolchain inventory exercise. The question is not simply “Do we use Poetry?” The better question is “Where does Poetry run, what version is installed there, and what trust boundary does it cross?”The first step is to find all Poetry installations in developer environments, build images, CI runners, and internal scripts. The second step is to update to Poetry 2.3.3 or later. The third step is to review package provenance and caches, especially if any organization installs from internal mirrors or third-party package feeds.
Practical remediation sequence
A good response should be structured and repeatable. Security teams can adapt the following sequence for Windows, Linux, and containerized environments:- Inventory Poetry versions across workstations, build agents, and containers.
- Upgrade Poetry to 2.3.3 or newer using the same installation method originally used.
- Invalidate dependency caches that may contain untrusted or stale wheel files.
- Rebuild base images used by Python CI jobs.
- Re-run dependency scanning against repositories and lockfiles.
- Review package index logs for suspicious wheel uploads or replacements.
- Confirm builds use the patched Poetry binary rather than an older cached copy.
Consumer and Hobbyist Impact
For individual Python developers, the advice is simpler but still important. If you use Poetry, update it. If you recently installed dependencies from an unfamiliar package source while running a vulnerable version, consider recreating the affected virtual environment and checking the surrounding project directory for unexpected file changes.Most hobbyist users are unlikely to be targeted directly through this specific CVE. However, opportunistic supply chain attacks often do not need to target individuals by name. Attackers can publish typosquatted packages, compromise maintainer accounts, or poison dependencies used by many projects.
What individual users should do
A practical personal response does not need to be dramatic. It should focus on reducing stale tooling and avoiding unnecessary trust in package artifacts.Recommended steps include:
- Upgrade Poetry immediately if it is below 2.3.3.
- Prefer official package sources and known internal indexes.
- Review recent dependency changes before running new projects.
- Delete and recreate virtual environments after suspicious installs.
- Avoid running dependency installers with elevated privileges.
- Keep PowerShell and shell profiles under version control or monitored backups.
Competitive and Ecosystem Implications
The Python packaging ecosystem has spent years improving standards, metadata, reproducibility, and build isolation. Yet CVE-2026-34591 shows that the installer remains one of the most sensitive parts of the chain. Every package manager must safely interpret untrusted archives, and any mistake becomes a trust boundary failure.For Poetry’s competitors and adjacent tools, the lesson is not “Poetry is uniquely unsafe.” The lesson is that package installation is security-critical code. Pip, uv, PDM, Hatch, Conda, and internal enterprise installers all live in the same risk neighborhood when handling archives, paths, scripts, and metadata.
Market pressure on developer tooling
The competitive impact may be subtle but real. Developers increasingly choose tools not only for speed and ergonomics but also for security posture. Fast dependency resolution, reproducible locks, and polished commands matter, but enterprises now ask harder questions about provenance, isolation, and patch responsiveness.Tooling vendors and open-source maintainers can differentiate through:
- Faster security releases with clear upgrade guidance.
- Safer defaults for archive handling and script execution.
- Better integration with dependency scanning.
- Transparent advisories and changelogs.
- Hardening tests for malicious package artifacts.
- Support for trusted publishing and artifact verification.
Lessons for Secure Package Management
CVE-2026-34591 is a textbook example of why dependency management must be viewed as part of the attack surface. Package installation is not a passive file copy operation. It is a sequence of trust decisions involving network sources, archive formats, metadata, lockfiles, caches, filesystem writes, and later code execution.The defensive model should assume that any package artifact may be hostile until proven otherwise. That does not mean developers should stop using package managers. It means the ecosystem needs layered controls so one malicious artifact cannot silently reshape a workstation or pipeline.
Controls that reduce blast radius
Security teams should combine patched tooling with operational controls. No single fix eliminates supply chain risk, but each layer makes exploitation harder and detection easier.Strong controls include:
- Pinning dependencies with hashes where workflows support it.
- Using private indexes with strict publishing controls.
- Scanning artifacts before promotion into internal repositories.
- Running builds in disposable environments.
- Restricting write access for build users.
- Separating build, test, signing, and deployment credentials.
- Monitoring unexpected file creation during dependency installation.
Strengths and Opportunities
The disclosure around CVE-2026-34591 also highlights several encouraging signs. The issue has a clear affected range, a fixed release, an understandable root cause, and a concrete patch strategy. That gives defenders a manageable path forward, provided they move beyond dashboard acknowledgment and actually update the places where Poetry runs.- The fix is available now in Poetry 2.3.3 and later.
- The vulnerability has a clear technical boundary, making remediation easier to validate.
- The patch uses a sound containment model based on resolved paths.
- Regression tests improve future resilience against similar bugs.
- The advisory gives teams actionable version information.
- The incident reinforces supply chain security awareness without requiring speculation.
- Enterprises can use this as a trigger to inventory developer tooling more broadly.
Risks and Concerns
The main concern is not that every vulnerable Poetry user is immediately compromised. The concern is that vulnerable versions may remain embedded in build images, self-hosted runners, onboarding scripts, and developer machines long after the patch is available. Toolchain vulnerabilities often linger because they are not part of the application dependency graph that teams scan every day.- Cached CI images may keep vulnerable Poetry versions alive.
- Self-hosted runners may preserve malicious filesystem changes.
- Package mirrors may retain compromised wheel artifacts.
- Developers may update project dependencies but forget global tools.
- CVSS severity labels may cause under-prioritization.
- Windows user-profile persistence paths may be overlooked.
- Multiple Poetry installation methods can complicate verification.
What to Watch Next
The next phase is about adoption and detection. Security teams should watch whether scanners, software composition analysis platforms, and CI providers reliably flag vulnerable Poetry installations. Because Poetry is often a tool rather than an application dependency, it may not appear in the same inventory systems that track Python libraries inside deployed products.Organizations should also monitor whether related installer bugs surface in other packaging tools. The same defensive concepts apply across ecosystems: archive entries must be treated as hostile, destination paths must be resolved, and writes must be contained. Any tool that unpacks third-party artifacts into trusted environments deserves review.
Watch these areas closely:
- Scanner coverage for developer tools, not just runtime libraries.
- Updates to base container images that include Poetry.
- CI provider guidance for Python build pipelines.
- New advisories involving wheel extraction or archive parsing.
- Evidence of malicious packages attempting traversal-style writes.
CVE-2026-34591 will likely be remembered less as a catastrophic standalone flaw and more as another warning about the hidden trust placed in developer tooling. Poetry’s fix is available, clear, and worth deploying immediately, but the broader lesson is durable: package managers are part of the security perimeter. In 2026, protecting Windows workstations and CI/CD systems means patching not only the operating system and applications, but also the quiet build tools that decide which files land where.
Source: MSRC Security Update Guide - Microsoft Security Response Center