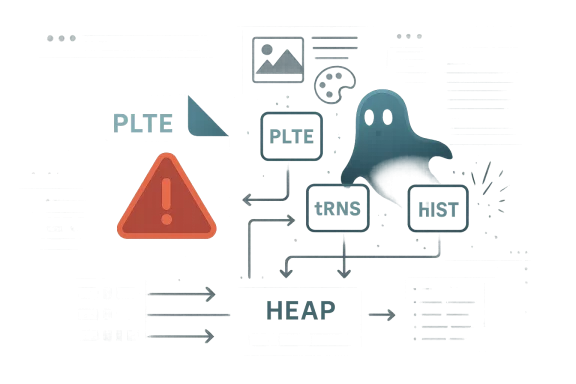
CVE-2026-34757 is the latest reminder that image parsing bugs can still punch far above their weight in modern software stacks. According to Microsoft’s Security Update Guide entry, the flaw in libpng is a use-after-free affecting
The new CVE sits in a part of libpng that many developers assume is routine: copying, updating, and reattaching PNG metadata chunks. The problem appears when data returned by a getter is fed back into a setter on the same
This is not an isolated category of flaw for libpng. The library has been through a run of recent security fixes, including several memory-safety issues disclosed across 2025 and 2026, and the project’s own security history makes clear that some of these bugs lingered for years before being found. The current issue is therefore not merely “one more CVE,” but part of a broader pattern: legacy C code, complex API behavior, and compatibility constraints combining to create attack surface that is easy to underestimate and hard to fully eliminate.
What makes the Microsoft advisory notable is that it describes the vulnerability in terms of chunk-handling routines, which are central to applications that preserve or transform PNG metadata rather than simply render pixels. That distinction matters. A viewer that only decodes and displays an image may be exposed differently than an editing tool, batch converter, thumbnail service, or asset pipeline that reads, mutates, and writes PNG information structures. Those workflows are the ones where the aliasing bug becomes dangerous.
For Windows users, the immediate practical question is not whether they install libpng directly, but whether software they rely on bundles a vulnerable copy. Many applications ship their own dependencies, and enterprise environments often contain multiple copies of the same open-source library across different products. That fragmentation is one of the reasons CVEs like this ripple widely: the library can be patched upstream while downstream consumers remain exposed until their own update cycle catches up.
The recent history of libpng is especially relevant here. Public security notices have highlighted a string of memory-safety issues in the library, including use-after-free, out-of-bounds read, and write conditions in different APIs. The libpng project’s own homepage now explicitly warns about multiple vulnerabilities fixed in recent releases, including a high-severity use-after-free in the transparency and palette-handling code and additional issues in palette expansion and simplified read paths. That backdrop matters because it shows the current CVE is not an outlier but part of an active hardening effort.
Microsoft’s Security Update Guide has increasingly become a central public-facing hub for third-party library issues that affect its ecosystem. MSRC’s broader transparency push, including publishing CWE information and machine-readable advisory data, reflects a recognition that modern vulnerability management depends on more than just CVE assignment. It depends on fast attribution, clear root-cause framing, and enough detail for defenders to map exposure across products and services. CVE-2026-34757 fits that model neatly: a third-party library flaw, a precise description, and a clear functional impact.
The technical significance of the affected functions is also worth unpacking.
At a market level, libpng bugs have implications beyond the library itself. They affect Linux distributions, package ecosystems, embedded devices, image-heavy SaaS platforms, and any application stack that values PNG as a lowest-common-denominator format. In other words, this is not just about one upstream project releasing a fix; it is about thousands of downstream maintainers deciding when and how to propagate that fix without breaking compatibility. The result is a classic patching dilemma: the more foundational the component, the slower the ecosystem often is to converge.
The underlying danger is that the library is not just crashing on bad input; it is potentially continuing to process and serialize corrupted metadata. That means the bug can alter the integrity of output as well as leak internal memory. For image-processing services, that combination is awkward: the same pipeline that ingests untrusted content may then export corrupted content to users or to another internal system.
That is one reason memory bugs in library internals often survive for years. Unit tests may cover “happy path” image loads, while the vulnerable sequence occurs only in conversion, editing, or metadata-preservation scenarios. If the buffer is freed on one path and later reused by another path, traditional functional testing can miss it unless the test harness deliberately exercises the edge cases.
The practical takeaway is that exploitability depends on more than just the presence of a malformed PNG. It depends on how the host application uses libpng, what transformations it applies, and whether the library’s internal state is reused across a setter/getter round trip. That is why advisory text for this class of bug often looks more subtle than the impact it describes: the preconditions are specific, but the consequences are not.
Applications that manipulate palettes or transparency information are particularly relevant. A photo editor might preserve PLTE and tRNS information when exporting, a converter might rebuild histogram data when flattening images, and a server-side image pipeline might round-trip PNG chunks to maintain fidelity. Those are the workflows where a heap aliasing mistake can be triggered, because the application has reason to read chunk content and feed it back into libpng.
Still, exploitability is not universal. A consumer who opens PNGs in software that never writes metadata back may be less exposed than an enterprise asset pipeline that transforms and republishes image files at scale. The same bug can be a nuisance in one context and a meaningful disclosure vector in another.
A useful way to think about the attack path is to divide it into three layers:
The disclosure angle is especially important in enterprise settings. Information leaks can reveal heap fragments, credentials accidentally placed in memory, pointers that reduce exploit mitigation entropy, or remnants of adjacent data from other requests in a multitenant service. When the vulnerable code runs in a long-lived server process, the consequences may extend beyond a single failed conversion job. A leak in an image pipeline can become a larger incident if the process holds sensitive material in memory.
Patch validation can also be harder than it sounds. Because the issue is in metadata handling rather than simple file open logic, regression testing needs to include conversion and transformation cases, not just basic image decoding. Teams that only verify that “the PNG opens” may miss the vulnerable path entirely. That is a dangerous false sense of security, especially when workflows are automated and high-volume.
Enterprises should also pay attention to service boundaries. A vulnerable internal microservice may not be internet-facing, but if it accepts uploaded assets from another internal system, the trust boundary still matters. Attackers often chain low-value footholds into higher-value target services by abusing internal file-processing jobs. In that sense, a PNG bug can be a pivot point rather than an endpoint.
Browsers are an especially interesting case. Most modern browsers have their own image handling layers, but they also depend on platform libraries in certain contexts and on many adjacent tools during upload, import, export, and preview workflows. Even when the browser engine itself is not the direct target, browser-adjacent software can still process the image and hand data to libpng. The attack surface is wider than the visible UI suggests.
The practical impact for home users is usually silent at first: a crash, a corrupted image, or a preview that fails unpredictably. But memory disclosure can expose data that is not obviously related to the image itself, and that is the more serious concern. Users rarely notice the leak; defenders often notice it only after the damage path has widened.
At a consumer support level, the best advice is simple: keep operating systems and applications updated, especially image editors, office suites, and media tools that bundle third-party codecs. If a vendor ships a patched build of libpng, the consumer may never hear the library’s name, but the risk reduction is still real. That invisible dependency is exactly why patch hygiene matters.
Microsoft’s own broader vulnerability transparency work provides useful context here. By publishing root-cause metadata and advisory information in a more structured way, MSRC is signaling that patching is not enough; defenders also need to understand categories of weakness so they can recognize patterns across products. This is especially relevant for issues like libpng aliasing bugs, where the same basic lifetime problem can recur in different functions over time.
The pattern is also visible in the release cadence. libpng’s recent security notices show a concentrated stream of fixes across adjacent versions, which suggests active maintenance but also a broad legacy surface. The upside is that upstream has identified and addressed the issue. The downside is that the wider ecosystem may still be digesting last month’s fixes while the next one arrives.
It also means paying attention to advisory language. Terms like heap disclosure, use-after-free, and chunk corruption are not interchangeable. They point to different defensive priorities: leaks increase reconnaissance, corruption can destabilize processes, and both can become stepping stones for more serious compromise depending on allocator behavior and process privileges.
A practical response plan should include the following steps:
That said, detection has limits. Use-after-free bugs can behave nondeterministically, especially under different allocators and optimization levels. The absence of crashes does not prove the absence of risk. In practice, the best detector is still the patch.
There is also a subtle reputational effect. Open-source libraries that become security headlines can trigger downstream caution, package pinning, or migration experiments even when the actual fix is straightforward. That can be healthy if it motivates better testing and stronger API design. It can also be counterproductive if teams overreact and move to newer components without a clear maintenance plan.
There is a broader lesson for platform owners and application developers as well. If your software depends on a mature C library for image parsing, you own part of the supply chain risk. It is not enough to say the library is upstream’s responsibility; if you ship the code, you ship the exposure. That reality is why coordinated disclosure and clear advisory language are so important.
The upside for the ecosystem is that these events keep memory-safety discipline in the spotlight. Better ownership rules, safer wrapper APIs, and more aggressive fuzzing all become easier to justify after a public bug. In that sense, CVE-2026-34757 is a cost, but also a forcing function for better engineering.
In the weeks ahead, watch for vendor advisories, distro backports, and application updates that quietly absorb the fix. Also watch for follow-on disclosures in neighboring code paths, because memory bugs rarely exist in splendid isolation. Once one aliasing problem is found in a mature library, reviewers often discover that adjacent APIs deserve a second look. That is the real lesson of libpng’s recent security cycle.
Source: MSRC Security Update Guide - Microsoft Security Response Center
png_set_PLTE, png_set_tRNS, and png_set_hIST, with the practical outcome being corrupted chunk data and possible heap information disclosure. The vulnerability lands in a library that sits inside browsers, desktop apps, document tools, game engines, and a long tail of server-side image pipelines, which is why even “just a PNG bug” deserves serious attention.
 Overview
Overview
The new CVE sits in a part of libpng that many developers assume is routine: copying, updating, and reattaching PNG metadata chunks. The problem appears when data returned by a getter is fed back into a setter on the same png_struct and png_info pair, creating a lifetime mismatch that can leave the library operating on freed heap memory. In plain English, the code still thinks it owns a piece of memory that has already been released, and that is exactly the kind of mistake that can turn into disclosure, corruption, or in the worst case a foothold for more serious exploitation.This is not an isolated category of flaw for libpng. The library has been through a run of recent security fixes, including several memory-safety issues disclosed across 2025 and 2026, and the project’s own security history makes clear that some of these bugs lingered for years before being found. The current issue is therefore not merely “one more CVE,” but part of a broader pattern: legacy C code, complex API behavior, and compatibility constraints combining to create attack surface that is easy to underestimate and hard to fully eliminate.
What makes the Microsoft advisory notable is that it describes the vulnerability in terms of chunk-handling routines, which are central to applications that preserve or transform PNG metadata rather than simply render pixels. That distinction matters. A viewer that only decodes and displays an image may be exposed differently than an editing tool, batch converter, thumbnail service, or asset pipeline that reads, mutates, and writes PNG information structures. Those workflows are the ones where the aliasing bug becomes dangerous.
For Windows users, the immediate practical question is not whether they install libpng directly, but whether software they rely on bundles a vulnerable copy. Many applications ship their own dependencies, and enterprise environments often contain multiple copies of the same open-source library across different products. That fragmentation is one of the reasons CVEs like this ripple widely: the library can be patched upstream while downstream consumers remain exposed until their own update cycle catches up.
Background
Libpng has long occupied a strange but important place in the software ecosystem. It is not glamorous, but it is everywhere, serving as the reference implementation for PNG support and providing both low-level and simplified APIs for reading and writing image files. The project’s history shows a recurring tension between the stability of a mature format and the instability of C memory management. The more features and compatibility layers a library accumulates, the more likely it is that an old assumption will outlive the code that depended on it.The recent history of libpng is especially relevant here. Public security notices have highlighted a string of memory-safety issues in the library, including use-after-free, out-of-bounds read, and write conditions in different APIs. The libpng project’s own homepage now explicitly warns about multiple vulnerabilities fixed in recent releases, including a high-severity use-after-free in the transparency and palette-handling code and additional issues in palette expansion and simplified read paths. That backdrop matters because it shows the current CVE is not an outlier but part of an active hardening effort.
Microsoft’s Security Update Guide has increasingly become a central public-facing hub for third-party library issues that affect its ecosystem. MSRC’s broader transparency push, including publishing CWE information and machine-readable advisory data, reflects a recognition that modern vulnerability management depends on more than just CVE assignment. It depends on fast attribution, clear root-cause framing, and enough detail for defenders to map exposure across products and services. CVE-2026-34757 fits that model neatly: a third-party library flaw, a precise description, and a clear functional impact.
The technical significance of the affected functions is also worth unpacking.
png_set_PLTE handles the palette chunk, png_set_tRNS handles transparency, and png_set_hIST handles histogram information. These chunks are often manipulated in workflows that preserve image fidelity or convert between formats, so bugs there can remain dormant in ordinary testing while still being reachable in real-world processing. That makes them especially treacherous for security teams relying on sample-file validation alone.At a market level, libpng bugs have implications beyond the library itself. They affect Linux distributions, package ecosystems, embedded devices, image-heavy SaaS platforms, and any application stack that values PNG as a lowest-common-denominator format. In other words, this is not just about one upstream project releasing a fix; it is about thousands of downstream maintainers deciding when and how to propagate that fix without breaking compatibility. The result is a classic patching dilemma: the more foundational the component, the slower the ecosystem often is to converge.
What the Vulnerability Does
The headline issue is straightforward: a use-after-free in functions that set PNG chunk data can cause libpng to work with memory that is no longer valid. Microsoft’s description says the flaw can lead to corrupted chunk data and potential heap information disclosure, and that combination immediately raises the stakes. A corruption bug can destabilize the application, while a disclosure bug can leak heap contents that may help attackers defeat mitigations or map the process layout.Why heap disclosure matters
Heap disclosure is not as flashy as remote code execution, but it is often an important precursor. If an attacker can learn allocator patterns, object contents, or adjacent heap fragments, they may be able to chain the bug into a broader compromise. In practice, information leaks can reduce the randomness and uncertainty that protect modern systems, especially when the vulnerable application runs in a long-lived process that processes many files.The underlying danger is that the library is not just crashing on bad input; it is potentially continuing to process and serialize corrupted metadata. That means the bug can alter the integrity of output as well as leak internal memory. For image-processing services, that combination is awkward: the same pipeline that ingests untrusted content may then export corrupted content to users or to another internal system.
Why metadata code is hard to secure
PNG metadata handling is deceptively complex because the library must support many combinations of chunks, transformations, and API styles. Some callers use the full low-level interface; others use simplified wrappers intended to make development easier. Each layer expands the matrix of possible object lifetimes and ownership assumptions. When a getter and setter share a buffer or a struct pointer incorrectly, the bug may not appear until a specific sequence of calls happens in just the right order.That is one reason memory bugs in library internals often survive for years. Unit tests may cover “happy path” image loads, while the vulnerable sequence occurs only in conversion, editing, or metadata-preservation scenarios. If the buffer is freed on one path and later reused by another path, traditional functional testing can miss it unless the test harness deliberately exercises the edge cases.
The practical takeaway is that exploitability depends on more than just the presence of a malformed PNG. It depends on how the host application uses libpng, what transformations it applies, and whether the library’s internal state is reused across a setter/getter round trip. That is why advisory text for this class of bug often looks more subtle than the impact it describes: the preconditions are specific, but the consequences are not.
How Attackers Might Reach It
For a vulnerability like this, the attacker’s primary lever is usually a crafted PNG file or a file with carefully arranged chunk metadata. However, because the issue lives in setter/getter interactions, the exact reachability depends on application behavior rather than on image parsing alone. In many cases, the hostile file is only the first step; the vulnerable code path is completed by the application’s own attempt to normalize, rewrite, or preserve metadata.Applications that manipulate palettes or transparency information are particularly relevant. A photo editor might preserve PLTE and tRNS information when exporting, a converter might rebuild histogram data when flattening images, and a server-side image pipeline might round-trip PNG chunks to maintain fidelity. Those are the workflows where a heap aliasing mistake can be triggered, because the application has reason to read chunk content and feed it back into libpng.
Exploitation conditions
Microsoft’s vulnerability description also includes the sort of “conditions beyond the attacker’s control” language that matters for scoring and risk modeling. In practical terms, the attacker does not need to control the victim’s environment entirely; they need the target to process the image in a vulnerable configuration. That is a very different bar from full system compromise, and it is why image codecs are so frequently treated as high-risk components in endpoint and browser security.Still, exploitability is not universal. A consumer who opens PNGs in software that never writes metadata back may be less exposed than an enterprise asset pipeline that transforms and republishes image files at scale. The same bug can be a nuisance in one context and a meaningful disclosure vector in another.
A useful way to think about the attack path is to divide it into three layers:
- The attacker supplies a malicious or specially structured PNG.
- The application parses it and invokes the relevant libpng APIs.
- The application or library reuses freed chunk memory, resulting in corrupted state or a leak.
Enterprise Impact
Enterprises should care about CVE-2026-34757 for the same reason they care about browser engine flaws and document parser bugs: the reach of image handling is broader than most asset inventories capture. PNG parsing shows up in helpdesk tools, content management systems, PDF generation, email gateways, thumbnail services, design software, and bespoke internal automation. If even one of those components carries a vulnerable libpng build, the organization may have exposure without realizing it.The disclosure angle is especially important in enterprise settings. Information leaks can reveal heap fragments, credentials accidentally placed in memory, pointers that reduce exploit mitigation entropy, or remnants of adjacent data from other requests in a multitenant service. When the vulnerable code runs in a long-lived server process, the consequences may extend beyond a single failed conversion job. A leak in an image pipeline can become a larger incident if the process holds sensitive material in memory.
Operational exposure
From an operations standpoint, the biggest challenge is dependency visibility. Many organizations track top-level packages but not the native libraries bundled inside them, and libpng is often embedded rather than directly managed. That means the fix may arrive through an application update, an OS patch, a container rebuild, or a vendor maintenance release, depending on where the library lives in the stack.Patch validation can also be harder than it sounds. Because the issue is in metadata handling rather than simple file open logic, regression testing needs to include conversion and transformation cases, not just basic image decoding. Teams that only verify that “the PNG opens” may miss the vulnerable path entirely. That is a dangerous false sense of security, especially when workflows are automated and high-volume.
Enterprises should also pay attention to service boundaries. A vulnerable internal microservice may not be internet-facing, but if it accepts uploaded assets from another internal system, the trust boundary still matters. Attackers often chain low-value footholds into higher-value target services by abusing internal file-processing jobs. In that sense, a PNG bug can be a pivot point rather than an endpoint.
Key enterprise concerns
- Hidden copies of libpng inside vendor applications
- Long-lived server processes with recoverable heap state
- Internal image pipelines that preserve metadata
- Container images that lag behind upstream fixes
- Asset repositories that accept untrusted uploads
- Limited regression testing for metadata transforms
Consumer and Desktop Impact
For consumers, the risk profile is different but still meaningful. Desktop applications that open or edit PNG files may be affected if they bundle libpng or link to a vulnerable system copy. The average user is less likely to study chunk metadata, but they are more likely to encounter files delivered through email, messaging apps, forums, or web downloads. That is why seemingly obscure codec flaws often become user-facing when bundled into popular software.Browsers are an especially interesting case. Most modern browsers have their own image handling layers, but they also depend on platform libraries in certain contexts and on many adjacent tools during upload, import, export, and preview workflows. Even when the browser engine itself is not the direct target, browser-adjacent software can still process the image and hand data to libpng. The attack surface is wider than the visible UI suggests.
User scenarios that matter
A consumer photo app that preserves metadata, for example, may be more exposed than a viewer that merely displays the image and exits. Likewise, an archive manager or messaging client that generates previews or thumbnails could invoke library code in a way that triggers the vulnerable aliasing sequence. These are everyday behaviors, which is why “just opening a file” should never be dismissed as benign.The practical impact for home users is usually silent at first: a crash, a corrupted image, or a preview that fails unpredictably. But memory disclosure can expose data that is not obviously related to the image itself, and that is the more serious concern. Users rarely notice the leak; defenders often notice it only after the damage path has widened.
At a consumer support level, the best advice is simple: keep operating systems and applications updated, especially image editors, office suites, and media tools that bundle third-party codecs. If a vendor ships a patched build of libpng, the consumer may never hear the library’s name, but the risk reduction is still real. That invisible dependency is exactly why patch hygiene matters.
The Broader Security Pattern
CVE-2026-34757 is part of a familiar and frustrating security pattern: memory safety bugs in mature C libraries that are “known good” until someone discovers a sequence the code never fully guarded against. These bugs tend to survive because the library is stable, widely trusted, and used in countless combinations that are hard to exhaustively test. The stronger the compatibility promise, the harder it becomes to refactor aggressively.Microsoft’s own broader vulnerability transparency work provides useful context here. By publishing root-cause metadata and advisory information in a more structured way, MSRC is signaling that patching is not enough; defenders also need to understand categories of weakness so they can recognize patterns across products. This is especially relevant for issues like libpng aliasing bugs, where the same basic lifetime problem can recur in different functions over time.
Why recurring bugs happen
The root cause is often not just a single coding error but a design assumption that was once safe and later became fragile. APIs that expose internal structures to callers, or that allow setters to reuse memory returned by getters, create opportunities for confusion about ownership. In a language like C, that confusion is more than semantic; it is memory corruption waiting for a trigger.The pattern is also visible in the release cadence. libpng’s recent security notices show a concentrated stream of fixes across adjacent versions, which suggests active maintenance but also a broad legacy surface. The upside is that upstream has identified and addressed the issue. The downside is that the wider ecosystem may still be digesting last month’s fixes while the next one arrives.
Why this matters to defenders
For defenders, the lesson is not to panic every time a codec CVE appears. It is to treat image libraries as first-class security dependencies, not as incidental plumbing. That means inventorying them, patching them, and testing workflows that transform or preserve metadata rather than only checking basic decode functionality.It also means paying attention to advisory language. Terms like heap disclosure, use-after-free, and chunk corruption are not interchangeable. They point to different defensive priorities: leaks increase reconnaissance, corruption can destabilize processes, and both can become stepping stones for more serious compromise depending on allocator behavior and process privileges.
Patching and Mitigation
The most effective response is to update to a version of libpng that includes the fix, or to install the vendor patch that incorporates it. Upstream has already published fixes for multiple recent issues in the libpng line, and downstream maintainers will need to republish packages for their respective platforms. If your environment uses a packaged application rather than a direct libpng dependency, that application vendor may be the real patch gate.What administrators should do
Start by identifying which products in your environment bundle libpng. That includes desktop software, command-line tools, servers, containers, embedded appliances, and developer libraries. Next, determine whether the affected copy is system-provided or vendor-supplied, because the patch path differs in each case. Finally, validate not just file opening but metadata-preserving workflows, which are more likely to hit the vulnerable code.A practical response plan should include the following steps:
- Inventory applications that process PNG files.
- Identify bundled or system-wide libpng versions.
- Apply upstream or vendor updates.
- Rebuild containers and packages that bake in old libraries.
- Test conversion, thumbnailing, and metadata-preservation workflows.
- Watch for unexplained crashes or corrupted output during PNG handling.
Detection and monitoring
Monitoring should focus on anomalies in services that accept user-supplied images. Repeated crashes, malformed outputs, or unexpected heap-related faults during image processing may indicate exposure. If your organization uses fuzzing or corpus-based testing in CI, add test cases that cover chunk-preserving transformations and round-trips through metadata APIs.That said, detection has limits. Use-after-free bugs can behave nondeterministically, especially under different allocators and optimization levels. The absence of crashes does not prove the absence of risk. In practice, the best detector is still the patch.
Competitive and Ecosystem Implications
Libpng security issues affect more than just direct users of the library; they influence the way the broader ecosystem thinks about native-code dependencies. Competing image libraries, wrappers, and platform abstractions all benefit when a widely deployed reference implementation is seen to be actively maintained, but they also inherit pressure to prove that their own memory handling is safer. The market does not reward “works on my machine” when the component sits under millions of file opens.There is also a subtle reputational effect. Open-source libraries that become security headlines can trigger downstream caution, package pinning, or migration experiments even when the actual fix is straightforward. That can be healthy if it motivates better testing and stronger API design. It can also be counterproductive if teams overreact and move to newer components without a clear maintenance plan.
Downstream behavior
Vendors often respond to this class of issue in one of three ways: they patch promptly, they backport the fix to older supported branches, or they defer until a larger maintenance window. Security teams should expect all three behaviors in the wild. The challenge is that end users only experience the last one if their vendor is slow.There is a broader lesson for platform owners and application developers as well. If your software depends on a mature C library for image parsing, you own part of the supply chain risk. It is not enough to say the library is upstream’s responsibility; if you ship the code, you ship the exposure. That reality is why coordinated disclosure and clear advisory language are so important.
The upside for the ecosystem is that these events keep memory-safety discipline in the spotlight. Better ownership rules, safer wrapper APIs, and more aggressive fuzzing all become easier to justify after a public bug. In that sense, CVE-2026-34757 is a cost, but also a forcing function for better engineering.
Strengths and Opportunities
The good news is that this is the kind of issue the ecosystem can actually fix, and upstream visibility makes that easier. Microsoft’s advisory naming, libpng’s maintenance cadence, and the availability of downstream package updates all improve the odds that defenders can close exposure quickly. The vulnerability also highlights where teams can strengthen their own processes, particularly around dependency inventory and metadata-aware testing. That makes the CVE painful, but useful.- Clear root-cause class: use-after-free
- Narrower trigger surface than a generic decoder crash
- Upstream and downstream patch paths are available
- Good opportunity to improve dependency inventory
- Strong case for metadata-aware fuzzing
- Useful reminder to sandbox image-processing services
- Encourages better ownership handling in native APIs
Risks and Concerns
The biggest concern is that many organizations still do not know where their libpng copies live, especially when they are embedded in third-party software. The second concern is that metadata-preserving workflows are often under-tested, so the vulnerable path may stay live even after superficial verification. The third is that information disclosure can be used to strengthen later attacks, turning a “mere leak” into an enabler for more serious compromise. That is why this CVE should not be treated as low drama just because it is not immediate code execution.- Hidden exposure in bundled third-party applications
- Enterprise image pipelines may preserve vulnerable paths
- Heap disclosure can aid exploit chaining
- Crashes may appear intermittent and hard to diagnose
- Patch lag across vendors can leave long tails of risk
- Test suites may miss setter/getter round-trip behavior
- Older branches may stay vulnerable longer in embedded products
Looking Ahead
The immediate next step is straightforward: confirm which products bundle libpng and get them onto fixed builds. The harder task is institutional, not technical. Organizations need better software bill of materials visibility, stronger fuzzing around nonstandard file workflows, and a willingness to treat image libraries as security-sensitive infrastructure rather than commodity utilities.In the weeks ahead, watch for vendor advisories, distro backports, and application updates that quietly absorb the fix. Also watch for follow-on disclosures in neighboring code paths, because memory bugs rarely exist in splendid isolation. Once one aliasing problem is found in a mature library, reviewers often discover that adjacent APIs deserve a second look. That is the real lesson of libpng’s recent security cycle.
- Vendor patch releases and backports
- Updated container base images
- Security scans that surface embedded libpng copies
- Fuzzing results for metadata-preserving PNG workflows
- Any follow-up advisories touching adjacent chunk APIs
Source: MSRC Security Update Guide - Microsoft Security Response Center