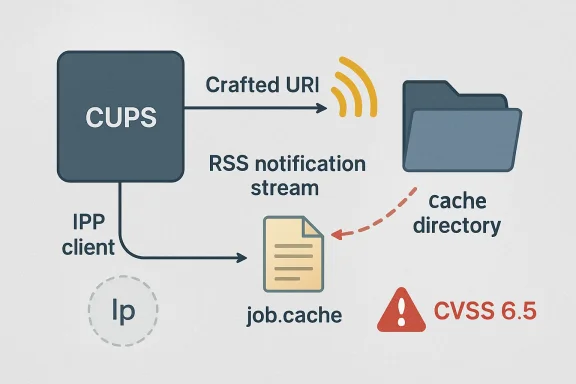
CVE-2026-34978 is a medium-severity OpenPrinting CUPS vulnerability, published in early April 2026, that lets a remote IPP client abuse the RSS notification URI field to traverse out of CUPS’ RSS cache directory and overwrite lp-writable state files such as job.cache. It is not the kind of bug that hands an attacker a shell, steals documents, or instantly turns a print server into a beachhead. But it is the kind of bug that explains why print infrastructure keeps showing up in security programs long after everyone assumed the hard lessons of spooler history had been learned. The weakness sits in the dull machinery of notifications and cache files, which is precisely why it matters.
The immediate mechanics of CVE-2026-34978 are almost painfully familiar. CUPS’ RSS notifier accepts a
That phrasing is important. This is not an arbitrary write with arbitrary attacker-selected binary payloads anywhere on the filesystem. The advisory language points to RSS XML data, lp-writable locations, and a concrete proof of concept that clobbers
Yet medium does not mean trivial.
The attacker model is also uncomfortable. The CVSS vector says network, low complexity, no privileges required, and no user interaction. Even with limited impact, that combination deserves attention on any system where CUPS is reachable by machines or users that should not be able to influence scheduler state.
That makes it a perfect example of infrastructure that feels peripheral until it fails. Printing is not glamorous, but it remains a workflow dependency in schools, hospitals, legal offices, warehouses, shipping desks, public-sector agencies, and finance departments. A bug that makes queued jobs disappear may not sound dramatic in a vulnerability database, but the help desk will experience it as a real incident.
The broader lesson is that print services are not just pipes for paper. They manage state, permissions, device discovery, job metadata, filters, queues, and sometimes surprisingly permissive network relationships. Every one of those functions creates parsing and authorization surfaces. CUPS has had years of scrutiny, but scrutiny does not eliminate the fundamental risk of complex software accepting structured input from the network.
For WindowsForum readers, the relevance is not limited to Linux shops. Mixed environments routinely include Linux print servers serving Windows clients over IPP, Samba-adjacent workflows, or vendor appliances with Unix-derived print stacks under the hood. A Windows-first organization can still depend on CUPS without thinking of itself as a “CUPS shop.”
Security teams often model exposure around headline services: the daemon, the listening port, the authentication boundary, the obvious admin API. CVE-2026-34978 sits deeper than that. It involves a notification pathway, a URI parser, a cache directory, default permissions, and a rename pattern that lets a process running as
That is the uncomfortable part. No single piece of the design needs to look outrageous for the chain to matter. A notifier writes files. A cache directory is group-writable. A URI field influences a filename. The daemon later trusts its state. Each part can look reasonable in isolation, while the combined system lets an unauthenticated client perturb scheduler behavior.
This is how many mid-tier infrastructure bugs work. They are not cinematic. They are compositional. They appear where legacy assumptions, convenience features, and file-system semantics meet.
But CVSS is a description of technical properties, not a deployment-specific risk verdict. In an enterprise where CUPS listens only on localhost, accepts jobs only from trusted hosts, and has RSS notifications disabled or patched packages deployed, CVE-2026-34978 may be a routine maintenance item. In a campus, lab, warehouse, or branch network where print services are broadly reachable, the same bug becomes more interesting.
The “no privileges required” component matters because many print deployments still treat the internal network as a soft boundary. Printers and print servers are frequently placed on shared VLANs, exposed across user segments, or exempted from aggressive filtering because printing failures generate tickets fast. That operational pressure has a habit of leaving services reachable long after the original reason has been forgotten.
The “no user interaction” component matters for another reason. Several high-profile CUPS discussions in recent years hinged on whether a user had to print, accept a printer, or otherwise participate in the exploit path. CVE-2026-34978 is less severe than those remote-code-execution narratives, but its path is cleaner: a crafted IPP subscription-related request can be the event.
State corruption bugs occupy a strange middle ground. They may not trip the same alarms as malware, but they can produce symptoms that look like software flakiness, administrative error, or mysterious service decay. Queues vanish. Jobs disappear. A scheduler fails to parse its cache. Restarting the service may not restore the expected condition because the persisted state has already been altered.
That operational ambiguity can delay response. If a print queue loses jobs after a CUPS restart, many administrators will first suspect package updates, disk issues, stale lock files, or user error. A path traversal in an RSS notifier will not be the first thought unless the vulnerability is already on the team’s radar.
This is why “availability impact: low” deserves translation. The advisory language says the attacker cannot completely deny service to legitimate users, and resources remain partially available or intermittently available. In business terms, that can still mean lost work, repeated print failures, support churn, and time spent reconstructing queues or explaining why pending jobs disappeared.
The advisory’s emphasis on default CacheDir permissions is the tell. If the cache directory is group-writable, typically owned in a root-and-lp arrangement, then a process running as
Administrators sometimes think about service accounts in binary terms: root is dangerous, non-root is safe. Real systems are messier. A non-root service user that can write scheduler state, spool files, or configuration-adjacent cache files can still cause meaningful disruption. The write does not need to land in
This is where file permissions become architecture. The exact owner, group, mode, and rename behavior of a cache directory can decide whether a malformed URI becomes a harmless failed request or a reliable way to break scheduler state. That is a deeply Unix lesson, and CUPS is a deeply Unix system.
That matters for Windows administrators because the boundary between “Microsoft estate” and “open-source dependency” is mostly fictional in day-to-day operations. Azure-hosted Linux workloads, WSL development machines, container images, build agents, appliances, and cross-platform endpoint fleets all carry packages that may never appear in a traditional Windows patch mindset. The patch Tuesday reflex is not enough.
The better interpretation is that Microsoft’s listing is a visibility cue, not a statement that every Windows desktop is directly vulnerable. If you run CUPS in a Linux VM, on a print server, inside an appliance, or as part of a managed image estate, you need to trace actual package versions and exposure. If you do not run CUPS, the CVE is still a useful reminder that infrastructure dependencies do not respect platform tribalism.
This is especially relevant in organizations that standardized on Windows endpoints but quietly rely on Linux servers for print consolidation. Those systems are easy to under-inventory because they are not glamorous and rarely receive new feature work. Vulnerability management programs that miss “boring” servers tend to discover them during incidents.
That timing matters because defenders often read CVE summaries once and never revisit them. The first version of a vulnerability record can say “no patch available,” while distributions are already preparing backports, vendor advisories, and updated packages. By the time a sysadmin is triaging the issue in late April 2026, the right question is not whether upstream ever fixed it; it is whether the organization’s distribution package includes the relevant fix.
The usual Linux caveat applies. Version strings are not always straightforward. A distribution may ship a package with an older upstream version number and backported patches, while another may ship the full 2.4.17 release. Treat “CUPS 2.4.16” as a signal to investigate, not as the only truth source.
For fleets, the most reliable approach is to check the vendor security tracker for the distribution in use, verify the installed package changelog where possible, and confirm service exposure. Patching matters, but exposure determines urgency.
Print services are often widened for convenience. A team wants mobile printing. A lab needs shared queues. A department uses older devices that behave badly unless the server accepts traffic in a permissive way. Firewall rules become exceptions, and exceptions become architecture.
This is where defenders should resist the temptation to argue only from CVSS. A medium bug reachable by every unauthenticated client on a large flat network may deserve faster action than a high bug buried behind strong authentication and segmentation. Security work is not scoreboard management; it is risk reduction.
The risk is also not limited to the public internet. Many organizations have learned to block direct internet exposure of CUPS, but internal reachability still matters. Malware, compromised laptops, unmanaged devices, guest networks, and contractor machines all turn “internal only” into a weaker statement than it used to be.
The boringness of that advice is a feature. CVE-2026-34978 should not trigger theatrical rebuilds of every print environment. It should trigger the kind of disciplined hygiene that keeps medium bugs from accumulating into brittle infrastructure: package currency, service binding review, segmentation, and feature minimization.
The more difficult work is inventory. Many organizations know where their domain controllers are and which firewalls terminate VPN traffic. Fewer can immediately answer which Linux hosts provide print services, which appliances embed CUPS, or whether a lab image has CUPS enabled by default. If a vulnerability like this forces that conversation, it has already provided value beyond its immediate patch.
Administrators should also think about monitoring. A sudden corruption of CUPS scheduler state, unexplained disappearance of queued jobs after restart, or odd RSS notifier activity should not be dismissed automatically as ordinary print weirdness. Print systems are noisy, but that is not a reason to make them invisible.
The print control plane includes queues, subscriptions, filters, drivers, discovery, authentication, spool directories, cache files, and service accounts. Every one of those pieces can become a security boundary under the right conditions. The RSS notifier bug shows how a low-glamour component can still punch above its apparent weight by writing where it should not.
This is the recurring failure mode in mature infrastructure. The dangerous assumptions are rarely written down. A component assumes a URI has been normalized. A directory assumes group write is safe. A scheduler assumes its cache is parseable. An administrator assumes the service is reachable only by friendly clients. The vulnerability appears in the gap between those assumptions.
For IT pros, the right response is not fear of printing. It is governance. Treat print servers like servers. Put them in inventory, patch them, segment them, monitor them, and retire features no one uses. That sounds obvious until the next “minor” print bug takes out a queue that a business process still depends on.
A Windows-heavy environment may still depend on CUPS in several ways. Linux print servers can front-end shared printers for Windows clients. Developers may run CUPS inside Linux VMs or WSL-adjacent environments. Containers and CI images may include printing libraries or services for document generation workflows. Network appliances and embedded systems may ship with CUPS-derived components.
The operational exposure varies widely. A dormant package installed on a sealed image is not the same as a listening print daemon on a shared subnet. But vulnerability management starts with knowing the difference. If a team cannot distinguish “installed” from “running” from “network reachable,” the CVE has revealed a process weakness.
The Microsoft angle should therefore be read as an invitation to cross-platform discipline. The modern Windows estate is not Windows-only. It is Windows endpoints, Linux servers, cloud workloads, open-source packages, vendor appliances, and identity systems stitched together by operational convenience. Attackers do not care which budget line item owns the vulnerable component.
Print jobs can contain sensitive or regulated content, but this CVE is not primarily about reading that content. It is about losing or disrupting the system’s memory of work. For some environments, that loss is minor. For others, it may affect shipping labels, prescriptions, court filings, invoices, or production paperwork.
Administrators should not overbuild a disaster recovery plan around one medium CUPS bug. They should, however, ask whether their print service state is backed up, whether queues can be reconstructed quickly, and whether business units know what to do when queued output disappears. Availability incidents are not always full outages; sometimes they are partial failures that leave users uncertain about what printed, what did not, and what needs to be resent.
That uncertainty is expensive. It leads to duplicate output, missed work, and support escalation. A vulnerability that creates ambiguity in a workflow can have an outsized operational impact even when its technical score is moderate.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 The Bug Is Small; the Boundary Failure Is Not
The Bug Is Small; the Boundary Failure Is Not
The immediate mechanics of CVE-2026-34978 are almost painfully familiar. CUPS’ RSS notifier accepts a notify-recipient-uri value, and in affected versions that value can include path traversal sequences. Instead of being confined under the scheduler’s intended RSS cache location, the notifier can be convinced to write RSS XML bytes somewhere else that the lp context can reach.That phrasing is important. This is not an arbitrary write with arbitrary attacker-selected binary payloads anywhere on the filesystem. The advisory language points to RSS XML data, lp-writable locations, and a concrete proof of concept that clobbers
job.cache. Those constraints are why the CVSS score lands in medium territory rather than the scorched-earth critical category.Yet medium does not mean trivial.
job.cache is not a decorative file. It is part of the scheduler’s view of queued work, and corrupting it can cause previously queued jobs to vanish after a restart because the scheduler cannot parse the altered state. In other words, this is a bug about trust boundaries inside the print system, and trust-boundary bugs in infrastructure are often more operationally interesting than their severity labels suggest.The attacker model is also uncomfortable. The CVSS vector says network, low complexity, no privileges required, and no user interaction. Even with limited impact, that combination deserves attention on any system where CUPS is reachable by machines or users that should not be able to influence scheduler state.
CUPS Keeps Proving That Printing Is Still Infrastructure
CUPS occupies an odd place in the modern estate. On Linux and other Unix-like systems, it is boring enough to be ignored, old enough to be deeply embedded, and important enough that outages become visible quickly. It often sits between desktops, servers, authentication systems, legacy printers, multifunction devices, and discovery protocols that administrators would rather not revisit unless something breaks.That makes it a perfect example of infrastructure that feels peripheral until it fails. Printing is not glamorous, but it remains a workflow dependency in schools, hospitals, legal offices, warehouses, shipping desks, public-sector agencies, and finance departments. A bug that makes queued jobs disappear may not sound dramatic in a vulnerability database, but the help desk will experience it as a real incident.
The broader lesson is that print services are not just pipes for paper. They manage state, permissions, device discovery, job metadata, filters, queues, and sometimes surprisingly permissive network relationships. Every one of those functions creates parsing and authorization surfaces. CUPS has had years of scrutiny, but scrutiny does not eliminate the fundamental risk of complex software accepting structured input from the network.
For WindowsForum readers, the relevance is not limited to Linux shops. Mixed environments routinely include Linux print servers serving Windows clients over IPP, Samba-adjacent workflows, or vendor appliances with Unix-derived print stacks under the hood. A Windows-first organization can still depend on CUPS without thinking of itself as a “CUPS shop.”
The RSS Notifier Is a Reminder That Optional Features Become Attack Surface
The most revealing detail in CVE-2026-34978 is not../job.cache. It is RSS. An RSS notifier in a print scheduler sounds like a feature from another era of administration, a convenience mechanism for job or printer event notifications. But optional subsystems do not stop being attack surface merely because nobody talks about them.Security teams often model exposure around headline services: the daemon, the listening port, the authentication boundary, the obvious admin API. CVE-2026-34978 sits deeper than that. It involves a notification pathway, a URI parser, a cache directory, default permissions, and a rename pattern that lets a process running as
lp affect root-managed state.That is the uncomfortable part. No single piece of the design needs to look outrageous for the chain to matter. A notifier writes files. A cache directory is group-writable. A URI field influences a filename. The daemon later trusts its state. Each part can look reasonable in isolation, while the combined system lets an unauthenticated client perturb scheduler behavior.
This is how many mid-tier infrastructure bugs work. They are not cinematic. They are compositional. They appear where legacy assumptions, convenience features, and file-system semantics meet.
Medium Severity Is the Beginning of Risk Triage, Not the End
The published CVSS 3.1 score of 6.5 is defensible. The vulnerability has low confidentiality impact because it is not described as exposing print data. It has low integrity and availability impact because the attacker’s write is constrained and the demonstrated consequence is partial denial of service rather than total system compromise. Scope remains unchanged.But CVSS is a description of technical properties, not a deployment-specific risk verdict. In an enterprise where CUPS listens only on localhost, accepts jobs only from trusted hosts, and has RSS notifications disabled or patched packages deployed, CVE-2026-34978 may be a routine maintenance item. In a campus, lab, warehouse, or branch network where print services are broadly reachable, the same bug becomes more interesting.
The “no privileges required” component matters because many print deployments still treat the internal network as a soft boundary. Printers and print servers are frequently placed on shared VLANs, exposed across user segments, or exempted from aggressive filtering because printing failures generate tickets fast. That operational pressure has a habit of leaving services reachable long after the original reason has been forgotten.
The “no user interaction” component matters for another reason. Several high-profile CUPS discussions in recent years hinged on whether a user had to print, accept a printer, or otherwise participate in the exploit path. CVE-2026-34978 is less severe than those remote-code-execution narratives, but its path is cleaner: a crafted IPP subscription-related request can be the event.
The Real Damage Is State Corruption, Not Spectacle
Security coverage tends to orbit around code execution because code execution is easy to understand. An attacker runs commands; defenders panic; vendors patch. CVE-2026-34978 is more modest and, in some environments, more annoying: it corrupts state.State corruption bugs occupy a strange middle ground. They may not trip the same alarms as malware, but they can produce symptoms that look like software flakiness, administrative error, or mysterious service decay. Queues vanish. Jobs disappear. A scheduler fails to parse its cache. Restarting the service may not restore the expected condition because the persisted state has already been altered.
That operational ambiguity can delay response. If a print queue loses jobs after a CUPS restart, many administrators will first suspect package updates, disk issues, stale lock files, or user error. A path traversal in an RSS notifier will not be the first thought unless the vulnerability is already on the team’s radar.
This is why “availability impact: low” deserves translation. The advisory language says the attacker cannot completely deny service to legitimate users, and resources remain partially available or intermittently available. In business terms, that can still mean lost work, repeated print failures, support churn, and time spent reconstructing queues or explaining why pending jobs disappeared.
The lp User Is Supposed to Contain Damage, But Containment Is Not Magic
CUPS does not run every component with unlimited power. The notifier runs aslp, and that is part of the reason this vulnerability is limited. Least privilege works; it reduces blast radius. But least privilege is not a guarantee that corrupted state will be harmless.The advisory’s emphasis on default CacheDir permissions is the tell. If the cache directory is group-writable, typically owned in a root-and-lp arrangement, then a process running as
lp can still influence files that the scheduler later treats as authoritative. That is not a failure of least privilege so much as a reminder that privilege boundaries are only as strong as the data flows crossing them.Administrators sometimes think about service accounts in binary terms: root is dangerous, non-root is safe. Real systems are messier. A non-root service user that can write scheduler state, spool files, or configuration-adjacent cache files can still cause meaningful disruption. The write does not need to land in
/etc/shadow to matter.This is where file permissions become architecture. The exact owner, group, mode, and rename behavior of a cache directory can decide whether a malformed URI becomes a harmless failed request or a reliable way to break scheduler state. That is a deeply Unix lesson, and CUPS is a deeply Unix system.
Microsoft’s Presence on the CVE Page Is a Supply-Chain Signal
The user-facing source here is Microsoft’s Security Update Guide, which may initially look odd for an OpenPrinting CUPS issue. CUPS is not Windows Print Spooler, and CVE-2026-34978 is not a native Windows vulnerability. But Microsoft’s tracking of third-party and open-source CVEs is part of a larger shift: vendors now surface vulnerabilities in components and ecosystems that intersect with their products, customers, or hosted environments.That matters for Windows administrators because the boundary between “Microsoft estate” and “open-source dependency” is mostly fictional in day-to-day operations. Azure-hosted Linux workloads, WSL development machines, container images, build agents, appliances, and cross-platform endpoint fleets all carry packages that may never appear in a traditional Windows patch mindset. The patch Tuesday reflex is not enough.
The better interpretation is that Microsoft’s listing is a visibility cue, not a statement that every Windows desktop is directly vulnerable. If you run CUPS in a Linux VM, on a print server, inside an appliance, or as part of a managed image estate, you need to trace actual package versions and exposure. If you do not run CUPS, the CVE is still a useful reminder that infrastructure dependencies do not respect platform tribalism.
This is especially relevant in organizations that standardized on Windows endpoints but quietly rely on Linux servers for print consolidation. Those systems are easy to under-inventory because they are not glamorous and rarely receive new feature work. Vulnerability management programs that miss “boring” servers tend to discover them during incidents.
The Patch Story Has Already Moved Past the Original Advisory
At publication time, the CVE record described affected OpenPrinting CUPS versions as 2.4.16 and earlier and noted that public patches were not yet available. That was a moment in time, not a permanent condition. OpenPrinting subsequently released CUPS 2.4.17 with security fixes, including a fix for the RSS notifier writing outside the scheduler’s RSS directory.That timing matters because defenders often read CVE summaries once and never revisit them. The first version of a vulnerability record can say “no patch available,” while distributions are already preparing backports, vendor advisories, and updated packages. By the time a sysadmin is triaging the issue in late April 2026, the right question is not whether upstream ever fixed it; it is whether the organization’s distribution package includes the relevant fix.
The usual Linux caveat applies. Version strings are not always straightforward. A distribution may ship a package with an older upstream version number and backported patches, while another may ship the full 2.4.17 release. Treat “CUPS 2.4.16” as a signal to investigate, not as the only truth source.
For fleets, the most reliable approach is to check the vendor security tracker for the distribution in use, verify the installed package changelog where possible, and confirm service exposure. Patching matters, but exposure determines urgency.
Exposure Is the Difference Between a Ticket and an Incident
The most practical question for CVE-2026-34978 is simple: who can reach CUPS, and can they submit the relevant IPP requests? A CUPS instance bound to localhost for a developer workstation is a different animal from a print server listening broadly on a user VLAN. A system where RSS notifications are disabled is different from one where the notifier path is active.Print services are often widened for convenience. A team wants mobile printing. A lab needs shared queues. A department uses older devices that behave badly unless the server accepts traffic in a permissive way. Firewall rules become exceptions, and exceptions become architecture.
This is where defenders should resist the temptation to argue only from CVSS. A medium bug reachable by every unauthenticated client on a large flat network may deserve faster action than a high bug buried behind strong authentication and segmentation. Security work is not scoreboard management; it is risk reduction.
The risk is also not limited to the public internet. Many organizations have learned to block direct internet exposure of CUPS, but internal reachability still matters. Malware, compromised laptops, unmanaged devices, guest networks, and contractor machines all turn “internal only” into a weaker statement than it used to be.
The Fix Is Boring, Which Is Exactly Why It Should Happen
There is no need for exotic mitigation advice here. Update CUPS through the operating system vendor or move to a fixed upstream version where appropriate. If updating immediately is not possible, reduce exposure, restrict who can reach port 631, disable unneeded notification mechanisms, and review cache directory permissions in light of vendor guidance.The boringness of that advice is a feature. CVE-2026-34978 should not trigger theatrical rebuilds of every print environment. It should trigger the kind of disciplined hygiene that keeps medium bugs from accumulating into brittle infrastructure: package currency, service binding review, segmentation, and feature minimization.
The more difficult work is inventory. Many organizations know where their domain controllers are and which firewalls terminate VPN traffic. Fewer can immediately answer which Linux hosts provide print services, which appliances embed CUPS, or whether a lab image has CUPS enabled by default. If a vulnerability like this forces that conversation, it has already provided value beyond its immediate patch.
Administrators should also think about monitoring. A sudden corruption of CUPS scheduler state, unexplained disappearance of queued jobs after restart, or odd RSS notifier activity should not be dismissed automatically as ordinary print weirdness. Print systems are noisy, but that is not a reason to make them invisible.
The 2026 CUPS Lesson Is That “Just Printing” Still Has a Control Plane
CVE-2026-34978 is not PrintNightmare, and treating it as such would be bad analysis. It does not deserve breathless claims of universal compromise. It does deserve a place in the continuing reassessment of print infrastructure as a real control plane.The print control plane includes queues, subscriptions, filters, drivers, discovery, authentication, spool directories, cache files, and service accounts. Every one of those pieces can become a security boundary under the right conditions. The RSS notifier bug shows how a low-glamour component can still punch above its apparent weight by writing where it should not.
This is the recurring failure mode in mature infrastructure. The dangerous assumptions are rarely written down. A component assumes a URI has been normalized. A directory assumes group write is safe. A scheduler assumes its cache is parseable. An administrator assumes the service is reachable only by friendly clients. The vulnerability appears in the gap between those assumptions.
For IT pros, the right response is not fear of printing. It is governance. Treat print servers like servers. Put them in inventory, patch them, segment them, monitor them, and retire features no one uses. That sounds obvious until the next “minor” print bug takes out a queue that a business process still depends on.
The Practical Reading for Windows-Heavy Shops
Windows administrators have a particular temptation with CUPS vulnerabilities: mentally file them under “Linux problem” and move on. Sometimes that is correct. Often it is incomplete.A Windows-heavy environment may still depend on CUPS in several ways. Linux print servers can front-end shared printers for Windows clients. Developers may run CUPS inside Linux VMs or WSL-adjacent environments. Containers and CI images may include printing libraries or services for document generation workflows. Network appliances and embedded systems may ship with CUPS-derived components.
The operational exposure varies widely. A dormant package installed on a sealed image is not the same as a listening print daemon on a shared subnet. But vulnerability management starts with knowing the difference. If a team cannot distinguish “installed” from “running” from “network reachable,” the CVE has revealed a process weakness.
The Microsoft angle should therefore be read as an invitation to cross-platform discipline. The modern Windows estate is not Windows-only. It is Windows endpoints, Linux servers, cloud workloads, open-source packages, vendor appliances, and identity systems stitched together by operational convenience. Attackers do not care which budget line item owns the vulnerable component.
The Cache File Clobbering Is a Warning About Recovery Plans
One underappreciated part of this vulnerability is recovery. If exploitation corruptsjob.cache, the immediate symptom may be missing queued jobs rather than a clean service-down alert. That creates a different response problem: restoring trust in scheduler state.Print jobs can contain sensitive or regulated content, but this CVE is not primarily about reading that content. It is about losing or disrupting the system’s memory of work. For some environments, that loss is minor. For others, it may affect shipping labels, prescriptions, court filings, invoices, or production paperwork.
Administrators should not overbuild a disaster recovery plan around one medium CUPS bug. They should, however, ask whether their print service state is backed up, whether queues can be reconstructed quickly, and whether business units know what to do when queued output disappears. Availability incidents are not always full outages; sometimes they are partial failures that leave users uncertain about what printed, what did not, and what needs to be resent.
That uncertainty is expensive. It leads to duplicate output, missed work, and support escalation. A vulnerability that creates ambiguity in a workflow can have an outsized operational impact even when its technical score is moderate.
The Sensible Administrator Treats This as a Print Hygiene Test
CVE-2026-34978 is best handled as a targeted hygiene exercise rather than a panic event. The facts are concrete enough to act on, and the limits are clear enough to avoid overreaction. The goal is to close the path traversal, reduce unnecessary reachability, and learn something about the print estate while doing it.- Systems running OpenPrinting CUPS 2.4.16 or earlier should be checked against distribution advisories or updated to a fixed release such as CUPS 2.4.17 where that is the appropriate vendor path.
- CUPS instances that do not need to accept network print or subscription requests should be bound to localhost or protected by host firewalls and network segmentation.
- RSS notification support and other unused CUPS features should be disabled when the business has no operational need for them.
- Administrators should verify whether CUPS cache and state directories use vendor-recommended ownership and permissions rather than locally inherited permissive settings.
- Help desks should treat unexplained queue disappearance or scheduler cache parsing failures as possible security-relevant symptoms, not merely generic print flakiness.
- Windows-centric asset inventories should still account for Linux print servers, appliances, containers, and developer systems that may carry CUPS packages or services.
Source: MSRC Security Update Guide - Microsoft Security Response Center