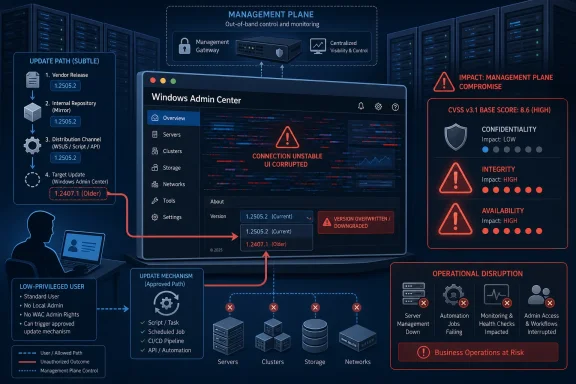
CVE-2026-35438 is a Windows Admin Center elevation-of-privilege vulnerability in which a low-privileged attacker could abuse the product’s update path to install an arbitrary available Windows Admin Center version from Microsoft’s update catalog, potentially altering or disrupting the existing deployment. That is why the CVSS line looks a little odd at first glance: low confidentiality impact, but high integrity and availability impact. This is not primarily a “steal the database” bug. It is a “change the management plane beneath the administrator” bug, and for a tool like Windows Admin Center, that distinction matters.
CVSS is often read as a severity shorthand, but in this case the useful part is not the final number. The useful part is the distribution of impact: confidentiality low, integrity high, availability high. That says the successful attacker is not being credited with broad direct access to secrets, but is being credited with meaningful power to change the state of the affected system and interfere with its normal operation.
For CVE-2026-35438, Microsoft’s own description, as reflected in the question-and-answer text, narrows the exploit effect to update manipulation. A low-privileged attacker could install an arbitrary available Windows Admin Center version from the update catalog. That is not arbitrary code execution in the classic sense, and it is not the same as dumping credentials or reading every managed server’s data.
But it is still an elevation-of-privilege issue because Windows Admin Center is not a cosmetic app. It is a browser-based administrative console used to manage Windows servers, clusters, Azure Local-style infrastructure, virtual machines, storage, networking, certificates, extensions, and other operational surfaces. A vulnerability that lets a lesser user influence which version of that console is installed crosses a boundary administrators normally rely on.
That is the heart of the scoring. The attacker’s gain is not primarily secrecy. The gain is control over software state.
Integrity impact is not limited to tampering with user documents or registry values. It includes unauthorized modification of applications, configurations, binaries, and workflows that administrators depend on. Windows Admin Center sits in a particularly sensitive category because it is itself a management layer. It is where administrators go to perform privileged actions, view infrastructure state, and operate servers that may not otherwise have interactive desktop access.
The phrase “arbitrary available Windows Admin Center version” is important. It does not mean the attacker can necessarily upload a malicious installer of their own choosing. It means the attacker can select from versions available in the update catalog. That limitation matters, but it does not make the issue harmless. A version rollback or forced version change can still defeat an organization’s intended patch state, reintroduce known weaknesses, change behavior, break extensions, or produce a configuration mismatch.
In practice, modern enterprise security depends heavily on version discipline. Admins patch because a specific version is known to fix a specific risk. If an attacker can push the management console away from that known-good state, the system’s integrity is no longer something the administrator exclusively controls.
For a home lab, that might mean a frustrating afternoon. For an IT department, it may mean losing a centralized interface during patching, incident response, cluster maintenance, certificate renewal, storage triage, or VM recovery. Management-plane outages are often more damaging than they look because they appear at exactly the point where administrators need reliable visibility.
Windows Admin Center is often deployed as a gateway. In that model, multiple administrators connect through a browser to manage multiple machines. A broken or downgraded gateway can become a choke point: the servers behind it may still be running, but the administrative path to them is impaired.
That is why availability is scored as high. The vulnerability’s effect is not merely that an icon disappears or a UI theme changes. It can interfere with the operational control plane that keeps Windows infrastructure manageable.
That distinction is easy to miss because Windows Admin Center can touch sensitive environments. The product may be used to manage domain-joined servers, Hyper-V hosts, failover clusters, storage, certificates, event logs, and security settings. A vulnerability in such a tool naturally triggers concern about data exposure.
But CVSS is attempting to score the vulnerability’s immediate security impact, not every possible consequence of living in a messy enterprise. Here, the direct action is unauthorized installation of an available Windows Admin Center version. That primarily affects what the software is and whether it keeps functioning as intended.
The confidentiality impact is still not zero. Microsoft’s explanation leaves room for indirect exposure if the attacker installs a version with weaker protections or known information-disclosure issues. That is why the metric lands at low rather than none. The exploit does not inherently disclose secrets, but it can place the environment into a state where confidentiality risks become more plausible.
That reduces the blast radius compared with a classic supply-chain compromise or arbitrary installer execution bug. If the update source is Microsoft’s catalog and the payloads are legitimate Windows Admin Center releases, the attacker’s menu is constrained. They are manipulating a trusted update mechanism rather than replacing it with an obviously foreign binary.
But constrained choices can still be dangerous. Attackers often do not need infinite freedom; they need one version with the right weakness, one downgrade that removes a fix, or one install action that breaks a service dependency. A legitimate older version can be a useful weapon if the organization had already moved past it for security or stability reasons.
This is why downgrade and rollback paths deserve more attention than they often receive. Security teams tend to think of patching as a one-way ratchet: vulnerable version, fixed version, done. CVE-2026-35438 is a reminder that the ratchet itself must be protected.
Management-plane systems are high-value not only because they hold privileges, but because administrators trust them. They are where operational truth is displayed. They are where configuration changes are initiated. They are where troubleshooting begins when something else has already gone wrong.
That makes software integrity especially important. If the management plane can be changed by someone below the intended privilege threshold, then administrators lose confidence in the tool before they even know whether the underlying servers are affected. In a crisis, that uncertainty is expensive.
Windows Admin Center is also extensible and frequently updated. That is one of its strengths, but it increases the importance of clean update governance. The more a product acts like a platform, the more its versioning, extension model, update catalog, and gateway permissions become part of the security boundary.
Elevation-of-privilege bugs are dangerous because they turn an initial foothold into something more useful. They are not usually the first move in an intrusion; they are the move that makes the first move matter. CVE-2026-35438 appears to fit that pattern, with the twist that the privilege gain is expressed through control over product installation rather than direct acquisition of SYSTEM-level execution.
That makes the vulnerability easy to understate. If a scanner reports confidentiality low, some teams may mentally demote the issue. But the attacker’s ability to alter administrative software should be treated as a serious operational control failure.
In a well-run environment, low-privileged users should not decide which administrative console version is installed. That decision belongs to patch management, change control, and administrators with explicit authority. CVE-2026-35438 matters because it appears to violate that assumption.
Hostile version drift is different. If an attacker can force Windows Admin Center into a chosen available version, the organization is no longer merely behind on updates. It may be moved deliberately into a less secure or less stable state. That is a more adversarial problem than ordinary patch lag.
The danger is not limited to known CVEs. An older version may behave differently with extensions, authentication settings, browser compatibility, certificates, logging, or Azure integrations. Even if there is no obvious public exploit chain, the attacker may use disruption itself as the goal.
For defenders, this shifts the response. The right question is not only “Are we patched against CVE-2026-35438?” It is also “Can we prove that Windows Admin Center has not been unexpectedly changed?” Integrity monitoring, installer logs, update records, and gateway change history become part of the investigation.
Security scoring systems struggle with these chains. CVSS tries to describe the vulnerability at hand, not every creative follow-on action. Attackers, however, do not operate in neat scoring boxes. They combine primitives: low privilege plus update manipulation plus a vulnerable version plus weak monitoring plus a busy administrator.
That is why confidentiality low should not become “confidentiality irrelevant.” In a management product, even indirect exposure can matter. Admin consoles often display system names, event data, configuration details, extension state, certificate information, and operational metadata that can help an attacker map an environment.
The correct reading is therefore balanced. CVE-2026-35438 is not primarily an information-disclosure vulnerability. But once an attacker can tamper with the management console’s version, defenders should not assume secrets are forever out of scope.
This vulnerability highlights the security side of rollback control. If a low-privileged user can select an older or otherwise unintended Windows Admin Center version, then patch compliance becomes reversible by an attacker. That undermines the basic promise of a fixed state.
Enterprises should therefore treat Windows Admin Center version control as a protected operation. The update channel, service account permissions, gateway administration rights, installer cache, and local administrator group membership all deserve review. The same applies to any automation that approves or stages Windows Admin Center updates.
The practical response is not exotic. Install Microsoft’s fix when available for the affected deployment, validate the installed version, restrict who can manage the gateway, and review whether any unexpected Windows Admin Center installation events occurred. The novelty is not the remediation checklist; it is the recognition that the management console’s update path is itself a security boundary.
A gateway deployment concentrates value. It gives administrators a convenient browser-based entry point into infrastructure, but it also creates a single place where authentication, authorization, extensions, updates, and logging converge. That convergence is useful for operations and attractive to attackers.
Organizations that expose Windows Admin Center more broadly should be especially careful. Even when a product is intended to be securely reachable, management interfaces should not be casually placed on wide networks. Segmentation, conditional access, strong authentication, and narrow administrative groups are not optional decorations for a management plane.
The vulnerability’s low-privilege prerequisite also means identity hygiene matters. If too many users have some degree of access to the Windows Admin Center host or gateway, the practical attacker pool grows. Least privilege is not just a slogan here; it determines who can even attempt to reach the vulnerable path.
That makes it a good candidate for prioritization in environments where Windows Admin Center is operationally important. If the product is used to manage production servers, clusters, or shared administrative workflows, treat the issue as more than a routine desktop application update. If it is installed but unused, the urgency may be lower, but cleanup or removal should still be considered.
The vulnerability also belongs in a broader conversation about administrative tooling. Many organizations harden domain controllers and production workloads while leaving the management layer less rigorously governed. That imbalance creates opportunities for attackers who understand that controlling the tool can be as useful as controlling the target.
CVE-2026-35438 is therefore less dramatic than a remote code execution headline, but more instructive. It shows how a narrow update-path flaw can become a meaningful integrity and availability problem because of where the affected software sits.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 The Score Is Telling Administrators to Look Past Data Theft
The Score Is Telling Administrators to Look Past Data Theft
CVSS is often read as a severity shorthand, but in this case the useful part is not the final number. The useful part is the distribution of impact: confidentiality low, integrity high, availability high. That says the successful attacker is not being credited with broad direct access to secrets, but is being credited with meaningful power to change the state of the affected system and interfere with its normal operation.For CVE-2026-35438, Microsoft’s own description, as reflected in the question-and-answer text, narrows the exploit effect to update manipulation. A low-privileged attacker could install an arbitrary available Windows Admin Center version from the update catalog. That is not arbitrary code execution in the classic sense, and it is not the same as dumping credentials or reading every managed server’s data.
But it is still an elevation-of-privilege issue because Windows Admin Center is not a cosmetic app. It is a browser-based administrative console used to manage Windows servers, clusters, Azure Local-style infrastructure, virtual machines, storage, networking, certificates, extensions, and other operational surfaces. A vulnerability that lets a lesser user influence which version of that console is installed crosses a boundary administrators normally rely on.
That is the heart of the scoring. The attacker’s gain is not primarily secrecy. The gain is control over software state.
Integrity Is High Because the Management Tool Itself Can Be Rewritten
The integrity rating is the easiest part to understand once the word “install” is taken seriously. If exploitation allows a low-privileged attacker to replace, downgrade, overwrite, or otherwise alter the Windows Admin Center installation, then the attacker has changed trusted administrative software without being authorized to do so. In security terms, that is a major integrity failure.Integrity impact is not limited to tampering with user documents or registry values. It includes unauthorized modification of applications, configurations, binaries, and workflows that administrators depend on. Windows Admin Center sits in a particularly sensitive category because it is itself a management layer. It is where administrators go to perform privileged actions, view infrastructure state, and operate servers that may not otherwise have interactive desktop access.
The phrase “arbitrary available Windows Admin Center version” is important. It does not mean the attacker can necessarily upload a malicious installer of their own choosing. It means the attacker can select from versions available in the update catalog. That limitation matters, but it does not make the issue harmless. A version rollback or forced version change can still defeat an organization’s intended patch state, reintroduce known weaknesses, change behavior, break extensions, or produce a configuration mismatch.
In practice, modern enterprise security depends heavily on version discipline. Admins patch because a specific version is known to fix a specific risk. If an attacker can push the management console away from that known-good state, the system’s integrity is no longer something the administrator exclusively controls.
Availability Is High Because Breaking the Console Can Break the Workday
The high availability rating follows from the same update-abuse primitive. If exploitation can overwrite or alter the existing Windows Admin Center installation, it can disrupt normal operation of the console. That disruption may not destroy the underlying servers, but it can still take away the tool administrators use to manage them.For a home lab, that might mean a frustrating afternoon. For an IT department, it may mean losing a centralized interface during patching, incident response, cluster maintenance, certificate renewal, storage triage, or VM recovery. Management-plane outages are often more damaging than they look because they appear at exactly the point where administrators need reliable visibility.
Windows Admin Center is often deployed as a gateway. In that model, multiple administrators connect through a browser to manage multiple machines. A broken or downgraded gateway can become a choke point: the servers behind it may still be running, but the administrative path to them is impaired.
That is why availability is scored as high. The vulnerability’s effect is not merely that an icon disappears or a UI theme changes. It can interfere with the operational control plane that keeps Windows infrastructure manageable.
Confidentiality Is Low Because the Bug Does Not Directly Read Secrets
The low confidentiality rating is not a promise that no sensitive information could ever be exposed. It is a narrower statement about the direct exploit consequence. Based on Microsoft’s described impact, successful exploitation does not immediately hand the attacker a list of passwords, server contents, tokens, or confidential configuration data.That distinction is easy to miss because Windows Admin Center can touch sensitive environments. The product may be used to manage domain-joined servers, Hyper-V hosts, failover clusters, storage, certificates, event logs, and security settings. A vulnerability in such a tool naturally triggers concern about data exposure.
But CVSS is attempting to score the vulnerability’s immediate security impact, not every possible consequence of living in a messy enterprise. Here, the direct action is unauthorized installation of an available Windows Admin Center version. That primarily affects what the software is and whether it keeps functioning as intended.
The confidentiality impact is still not zero. Microsoft’s explanation leaves room for indirect exposure if the attacker installs a version with weaker protections or known information-disclosure issues. That is why the metric lands at low rather than none. The exploit does not inherently disclose secrets, but it can place the environment into a state where confidentiality risks become more plausible.
The Word “Available” Does More Work Than It First Appears
The most reassuring word in the scenario is also one of the most important limiting factors: “available.” The attacker is not described as installing an arbitrary package from the internet. They are choosing an available Windows Admin Center version from the update catalog.That reduces the blast radius compared with a classic supply-chain compromise or arbitrary installer execution bug. If the update source is Microsoft’s catalog and the payloads are legitimate Windows Admin Center releases, the attacker’s menu is constrained. They are manipulating a trusted update mechanism rather than replacing it with an obviously foreign binary.
But constrained choices can still be dangerous. Attackers often do not need infinite freedom; they need one version with the right weakness, one downgrade that removes a fix, or one install action that breaks a service dependency. A legitimate older version can be a useful weapon if the organization had already moved past it for security or stability reasons.
This is why downgrade and rollback paths deserve more attention than they often receive. Security teams tend to think of patching as a one-way ratchet: vulnerable version, fixed version, done. CVE-2026-35438 is a reminder that the ratchet itself must be protected.
This Is a Management-Plane Vulnerability, Not Just an Application Bug
The practical severity of the vulnerability depends heavily on where Windows Admin Center sits in an organization. On a lightly used workstation install, the impact may be local and recoverable. On a shared gateway used by a server operations team, the same primitive becomes more serious because the tool is part of the administrative fabric.Management-plane systems are high-value not only because they hold privileges, but because administrators trust them. They are where operational truth is displayed. They are where configuration changes are initiated. They are where troubleshooting begins when something else has already gone wrong.
That makes software integrity especially important. If the management plane can be changed by someone below the intended privilege threshold, then administrators lose confidence in the tool before they even know whether the underlying servers are affected. In a crisis, that uncertainty is expensive.
Windows Admin Center is also extensible and frequently updated. That is one of its strengths, but it increases the importance of clean update governance. The more a product acts like a platform, the more its versioning, extension model, update catalog, and gateway permissions become part of the security boundary.
Low Privilege Does Not Mean Low Risk
The “low-privileged attacker” condition should not be read as a minor prerequisite. Many enterprise attacks begin with exactly that level of access. A phished user, an overbroad help-desk account, a compromised junior admin account, or a service identity with limited rights may all qualify as low privilege relative to the Windows Admin Center update path.Elevation-of-privilege bugs are dangerous because they turn an initial foothold into something more useful. They are not usually the first move in an intrusion; they are the move that makes the first move matter. CVE-2026-35438 appears to fit that pattern, with the twist that the privilege gain is expressed through control over product installation rather than direct acquisition of SYSTEM-level execution.
That makes the vulnerability easy to understate. If a scanner reports confidentiality low, some teams may mentally demote the issue. But the attacker’s ability to alter administrative software should be treated as a serious operational control failure.
In a well-run environment, low-privileged users should not decide which administrative console version is installed. That decision belongs to patch management, change control, and administrators with explicit authority. CVE-2026-35438 matters because it appears to violate that assumption.
The Real Damage Is Version Drift Under Hostile Control
Version drift is normally boring. One server has last month’s build, another has this month’s build, and a gateway is waiting for a maintenance window. Administrators dislike the mess, but it is usually seen as hygiene debt rather than an active attack surface.Hostile version drift is different. If an attacker can force Windows Admin Center into a chosen available version, the organization is no longer merely behind on updates. It may be moved deliberately into a less secure or less stable state. That is a more adversarial problem than ordinary patch lag.
The danger is not limited to known CVEs. An older version may behave differently with extensions, authentication settings, browser compatibility, certificates, logging, or Azure integrations. Even if there is no obvious public exploit chain, the attacker may use disruption itself as the goal.
For defenders, this shifts the response. The right question is not only “Are we patched against CVE-2026-35438?” It is also “Can we prove that Windows Admin Center has not been unexpectedly changed?” Integrity monitoring, installer logs, update records, and gateway change history become part of the investigation.
The Confidentiality Caveat Is Small but Not Decorative
Microsoft’s confidentiality rating makes sense, but the caveat deserves attention. If an attacker can install a version with known information-disclosure behavior, the path from integrity failure to confidentiality loss becomes plausible. That does not mean every exploit of CVE-2026-35438 leaks data. It means confidentiality risk may arrive in the second step rather than the first.Security scoring systems struggle with these chains. CVSS tries to describe the vulnerability at hand, not every creative follow-on action. Attackers, however, do not operate in neat scoring boxes. They combine primitives: low privilege plus update manipulation plus a vulnerable version plus weak monitoring plus a busy administrator.
That is why confidentiality low should not become “confidentiality irrelevant.” In a management product, even indirect exposure can matter. Admin consoles often display system names, event data, configuration details, extension state, certificate information, and operational metadata that can help an attacker map an environment.
The correct reading is therefore balanced. CVE-2026-35438 is not primarily an information-disclosure vulnerability. But once an attacker can tamper with the management console’s version, defenders should not assume secrets are forever out of scope.
Patch Management Has to Defend Against Going Backward
Most patch programs are designed around forward motion. Identify vulnerable assets, approve the update, deploy the update, verify compliance. Rollback exists, but it is usually treated as an administrator-controlled recovery mechanism.This vulnerability highlights the security side of rollback control. If a low-privileged user can select an older or otherwise unintended Windows Admin Center version, then patch compliance becomes reversible by an attacker. That undermines the basic promise of a fixed state.
Enterprises should therefore treat Windows Admin Center version control as a protected operation. The update channel, service account permissions, gateway administration rights, installer cache, and local administrator group membership all deserve review. The same applies to any automation that approves or stages Windows Admin Center updates.
The practical response is not exotic. Install Microsoft’s fix when available for the affected deployment, validate the installed version, restrict who can manage the gateway, and review whether any unexpected Windows Admin Center installation events occurred. The novelty is not the remediation checklist; it is the recognition that the management console’s update path is itself a security boundary.
Exposure Depends on Deployment Shape
Windows Admin Center can be installed in different ways, and that changes the risk profile. A single-user desktop deployment used for occasional administration is not equivalent to a server gateway published for a team. The more users can reach the console, and the more machines the console can manage, the more important this vulnerability becomes.A gateway deployment concentrates value. It gives administrators a convenient browser-based entry point into infrastructure, but it also creates a single place where authentication, authorization, extensions, updates, and logging converge. That convergence is useful for operations and attractive to attackers.
Organizations that expose Windows Admin Center more broadly should be especially careful. Even when a product is intended to be securely reachable, management interfaces should not be casually placed on wide networks. Segmentation, conditional access, strong authentication, and narrow administrative groups are not optional decorations for a management plane.
The vulnerability’s low-privilege prerequisite also means identity hygiene matters. If too many users have some degree of access to the Windows Admin Center host or gateway, the practical attacker pool grows. Least privilege is not just a slogan here; it determines who can even attempt to reach the vulnerable path.
The CVSS Triplet Gives the Best One-Sentence Risk Model
For administrators trying to explain CVE-2026-35438 internally, the confidentiality-integrity-availability split is the cleanest framing. The bug is not mainly about stealing information. It is about unauthorized control over which Windows Admin Center version is installed, with the possibility of breaking or weakening a management tool.That makes it a good candidate for prioritization in environments where Windows Admin Center is operationally important. If the product is used to manage production servers, clusters, or shared administrative workflows, treat the issue as more than a routine desktop application update. If it is installed but unused, the urgency may be lower, but cleanup or removal should still be considered.
The vulnerability also belongs in a broader conversation about administrative tooling. Many organizations harden domain controllers and production workloads while leaving the management layer less rigorously governed. That imbalance creates opportunities for attackers who understand that controlling the tool can be as useful as controlling the target.
CVE-2026-35438 is therefore less dramatic than a remote code execution headline, but more instructive. It shows how a narrow update-path flaw can become a meaningful integrity and availability problem because of where the affected software sits.
The Admin Center Lesson Is That Patch State Is Part of the Perimeter
The concrete lesson from CVE-2026-35438 is not that Windows Admin Center is uniquely fragile. It is that administrative software has to be protected from unauthorized version changes with the same seriousness applied to credentials and firewall rules. In this case, the CVSS metrics are unusually helpful because they point directly at the kind of harm defenders should expect.- Successful exploitation is best understood as unauthorized manipulation of the Windows Admin Center installation, not as direct large-scale data theft.
- The high integrity impact reflects that a low-privileged attacker could alter a trusted administrative tool by installing an unintended available version.
- The high availability impact reflects that overwriting, downgrading, or otherwise changing the installation could disrupt normal Windows Admin Center operation.
- The low confidentiality impact means the exploit does not directly expose sensitive data, though indirect exposure could follow if a weaker or vulnerable version is installed.
- The most exposed environments are likely shared gateway deployments where Windows Admin Center is part of day-to-day server, cluster, or infrastructure management.
- Defenders should verify the installed version, apply Microsoft’s remediation, restrict update authority, and review logs for unexpected Windows Admin Center installation activity.
Source: MSRC Security Update Guide - Microsoft Security Response Center