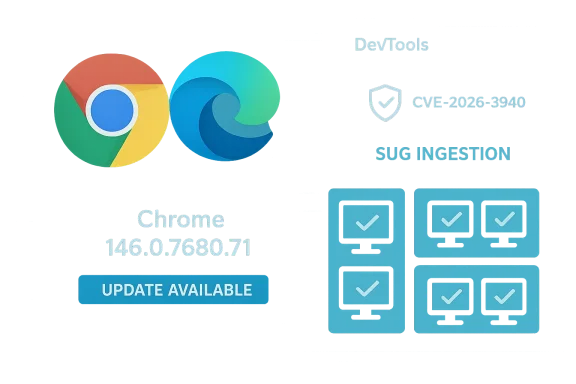
Chromium’s recently published CVE‑2026‑3940 — described as “Insufficient policy enforcement in DevTools” — has caused a small but important ripple across browser security trackers this week. Google fixed the underlying Chromium bug in the Chrome 146 stable update, and Microsoft has listed the CVE in its Security Update Guide so Microsoft Edge (Chromium‑based) customers can quickly confirm whether their Edge builds have ingested the upstream fix. This article explains exactly what CVE‑2026‑3940 is, why Microsoft documents Chrome‑assigned CVEs in its Security Update Guide, how you can verify whether your browser is affected (step‑by‑step), and what IT teams should do next to manage risk and detection at scale.
Chromium is the open‑source engine that supplies Blink, V8 and many shared components used by Google Chrome and by other Chromium‑based browsers — most notably Microsoft Edge. When a security flaw is discovered and assigned a CVE by the Chromium/Chrome security team, the upstream fix appears in Chrome release notes and Chromium bug trackers. Downstream vendors (like Microsoft) then ingest Chromium’s code into their own product releases; until that ingestion happens and a new Edge build ships, Edge remains dependent on the patched upstream code to be included and validated.
Microsoft’s Security Update Guide (SUG) lists many upstream Chromium CVEs for this reason: it’s a way to notify Edge users and administrators whether the Edge builds distributed by Microsoft include the Chromium fix and are therefore no longer vulnerable. The SUG entry for this family of Chromium CVEs explicitly states that the entry exists to announce that the latest Microsoft Edge (Chromium‑based) build has ingested the upstream remediation. nnel update for desktop on March 10, 2026 promoted Chrome 146 to the stable channel, and the published release notes list the security fixes included in that update. The Chromium security metadata for CVE‑2026‑3940 shows the affected range and the fixed Chrome baseline (Chrome prior to 146.0.7680.71 is affected).
Put another way:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Chromium is the open‑source engine that supplies Blink, V8 and many shared components used by Google Chrome and by other Chromium‑based browsers — most notably Microsoft Edge. When a security flaw is discovered and assigned a CVE by the Chromium/Chrome security team, the upstream fix appears in Chrome release notes and Chromium bug trackers. Downstream vendors (like Microsoft) then ingest Chromium’s code into their own product releases; until that ingestion happens and a new Edge build ships, Edge remains dependent on the patched upstream code to be included and validated.Microsoft’s Security Update Guide (SUG) lists many upstream Chromium CVEs for this reason: it’s a way to notify Edge users and administrators whether the Edge builds distributed by Microsoft include the Chromium fix and are therefore no longer vulnerable. The SUG entry for this family of Chromium CVEs explicitly states that the entry exists to announce that the latest Microsoft Edge (Chromium‑based) build has ingested the upstream remediation. nnel update for desktop on March 10, 2026 promoted Chrome 146 to the stable channel, and the published release notes list the security fixes included in that update. The Chromium security metadata for CVE‑2026‑3940 shows the affected range and the fixed Chrome baseline (Chrome prior to 146.0.7680.71 is affected).
What is CVE‑2026‑3940? A technical summary
- The vulnerability is described as “Insufficient policy enforcement in DevTools”. In plain terms, a piece of the DevTools code base did not correctly enforce a navigation or policy restriction, allowing a specially crafted HTML page to bypass a navigation restriction. That bypass could be used by a remote actor to influence navigation behavior in ways the policy was supposed to prevent.
- Chromium’s published record classifies the issue with a low security severity rating. That classification reflects the code path, required conditions for exploitation, and the likely impact model described by the Chromium team.
- The bug is not described as remote code execution (RCE) or an immediate privilege escalation; rather, it is a logic/policy enforcement gap in a developer‑facing component (DevTools) that could allow constrained navigation bypasses or cross‑origin information flow under particular conditions.
Why Microsoft included this Chrome CVE in the Security Update Guide
Microsoft lists Chromium‑assigned CVEs in the Security Update Guide for a simple operational reason: Microsoft Edge is built on Chromium, so upstream Chromium vulnerabilities are relevant to Edge customers until Microsoft ships an Edge build that contains the upstream repair. The SUG entry is a short, authoritative signal that the latest Edge release has ingestnd that customers running that Edge version are no longer vulnerable. This is the same pattern Microsoft has followed for earlier Chromium CVEs and continues to use for new Chromium‑origin issues.Put another way:
- The CVE owner (Google/Chromium) publishes the advisory and fixes in Chrome.
- Microsoft monitors Chromium releases and merges the upstream code into Edge’s code base.
- When Miincludes the upstream patch, Microsoft documents the CVE in the Security Update Guide to communicate the Edge version mapping and the build status to administrators and users.
Which Chrome/Chromium/Edge versions are affected or fixed?
- Chromium/Chrome: the CVE is fixed in Chrome 146.0.7680.71 (and later 146 stable builds). Users with Chrome versions prior to 146.0.7680.71 are considered vulnerable.
- Microsoft Edge (Chromium‑based): Microsoft’s SUG entry is published to indicate that the latest Microsoft Edge builds that are based on a Chromium revision which includes that fix are no longer vulnerable. The SUG entries often provide a small mapping table (Edge version / Chromium version) so administrators can confirm whether their installed Edge build contains the patched Chromium baseline. Because Edge follows a separate release and he fixed Chromium revision appears in Edge only after Microsoft produces and ships an Edge release that consumes that revision. For that reason, the SUG entry’s purpose is to confirm the ingestion status for Edge.
How to see the version of the browser (step‑by‑step)
If you want to confirm whether your browser has the patched version, here are the fastest, foolproof ways to check on desktop and mobile.Microsoft Edge (desktop — Windows / macOS / Linux)
- Open Microsoft Edge.
- Click the Options menu (three horizontal dots at the far right).
3.back → About Microsoft Edge. - The page will display the installed Edge version and automatically trigger an update check; if an update is available, Edge will offer to download and apply it.
Google Chrome (desktop)
- Open Google Chrome.
- Click the menu (three vertical dots) → Help → About Google Chrome.
- The About page displays the installed Chrome version and triggers an update check if one is available. The simple command chrome://version in the address bar also presents the version and detailed component information. These methods are standard across desktop platforms.
Chromium‑based alternative browsers (Brave, Vivaldi, Opera, etc.)
- Use the browser’s menu to locate “About” (Help → About) or visit about://version or equivalent (some browsers support about://version or chrome://version). For many Chromium forks, the underlying Chromium revision is visible on the About/version page — that number is the one you must map to the Chromium fixed baseline to determine exposure.
Mobile (Android / iOS)
- Android: Open the Play Store entry for Chrome (or Edge), or open the browser app → Menu → Settings → About (varies by browser and OS). For Chrome on Android, Settings → About Chrome shows the version.
- iOS: Open Settings in the Chrome or Edge app or check the app’s About section. App store listing pages also show the current app version the device has installed.
Quick verification checklist (for end users)
- 1.) Open your browser’s About page (Edge → Help and feedback → About Microsoft Edge; Chrome → Help → About Google Chrome).
- 2.) Note the version string (eg: 146.0.7680.71). If your installed version is the same as or later than the fixed baseline, you are patched for CVE‑2026‑3940.
- 3.) Restart the browser after any update. Many fixes only take effect once the running binary is replaced.
- 4.) If you manage many endpoints, export your inventory and search for the browser version string across devices to confirm coverage.
Enterprise considerations and recommended actions
For IT and security teams, a single user updating their browser is not sufficient — you need fleet‑wide assurance and verification.- Inventory: Ensure your endpoint inventory includes the browser vendor and full version string. Use your EDR/Vulnerability Management/Asset Management platform to query installed packages and versions. Many MDM/patch management tools report the exact browser version (including the Chromium revision).
- Policies & Auto‑update settings: Confirm that auto‑update for Edge/Chrome is enabled where acceptable; review your update ring or deployment policies to balance stability and security. Note: Chrome and Edge may require explicit configuration in managed environments to update automatically (Group Policy, Intune, or enterprise update channels). If you use Edge managed via Windows Update for Business or Intune, make sure the ingestion cadence you selected (e.g., Extended Stable vs Stable) meets your security requirements.
- Blocking controls: If you need immediate mitigation before a full roll‑out (for example, in highly regulated segments), consider blocking DevTools access via policy or extension restrictions where possible, enforce site isolation controls, and restrict which users can use developer tools (when configurable). These are compensating mitigations — the correct fix is to apply the patched browser build.
- Verification: After patch deployment, run queries to verify restart and replacement of the browser process. Many update failures are due to processes not restarting; require or orchestrate endpoint reboots/logoffs during the maintenance window if necessary.
- Communication: Inform helpdesk staff about the CVE and the simple troubleshooting steps (open About page → verify version → restart). That will reduce noise and expedite remediation.
Detection, logging and threat hunting guidance
- DevTools‑specific weaknesses typically do not trigger straightforward exploit signatures. Monitor for:
- Unexpected use or automation of developer tools (automation frameworks or scripts invoking devtool protocols).
- Unusual navigation events recorded in web proxies or browser telemetry that deviate from normal UX flows.
- If you maintain proxy/NGFW logs or web content filtering telemetry, look for patterns of crafted HTML pages served to internal clients immediately before anomalous navigation events.
- For high‑value hosts, consider enabling browser event logging (if your enterprise agent supports it) and feed those events into your SIEM. Alert on unusual sequences of DevTools protocol commands or patterns that indicate remote control of a browser instance.
- If your EDR platform supports it, create a detection rule for processes launching with developer tools flags or abnormal child process chains tied to browser processes.
Risk analysis — strengths, limitations and realistic exposure
Strengths / Why the impact is limited- The Chromium security team classified CVE‑2026‑3940 as low severity. That usually reflects exploit complexity and limited impact (no direct RCE or privilege escalation indicated in the advisory).
- DevTools features often require active user interaction or certain debugging flags to be turned on; many realistic exploitation paths require social engineering or specific debugging scenarios.
- Modern Chromium builds ship frequently; the fixed revision is already in Chrome 146 and is being back‑ported into downstream builds, so exposure windows tend to be short when vendors and operators act promptly.
- Even low‑severity DevTools issues can be used as part of multi‑stage attacks (for example, to bypass navigation restrictions that otherwise would limit data exfiltration or to create UI conditions that facilitate other exploits).
- In enterprise contexts where browsers are pinned to older builds for compatibility, a low‑severity issue can remain exploitable for a long time — long enough for well‑resourced attackers to weaponize adjunct techniques.
- Attackers sometimes chain multiple low‑ and medium‑severity issues; patching the individual components reduces the available attack surface for such chains.
Practical remediation timeline and verification plan (sample playbook)
- Triage (hours): Confirm whether any critical systems use pinned, older Chromium builds. Pull inventory and find all hosts running Chromium browser versions less than 146.0.7680.71.
- Rapid patch (24–72 hours): For unmanaged clients and developers, notify users to update Chrome/Edge immediately and restart. For managed endpoints, schedule roll‑out to the update ring that best balances coverage and stability.
- Hardening (72 hours): For sensitive groups, temporarily restrict access to developer tools where policy allows, and tighten site isolation and content security policy enforcement.
- Validation (1 week): Run verification queries against telemetry to ensure all targeted endpoints report patched version strings and have restarted since the update.
- Post‑deployment review (2 weeks): Review update failures, exceptions and any anomalies observed during or after patching.
How to map Chromium CVEs to Edge versions (practical tip)
Because Edge is a Chromium consumer, simply seeing a Chrome CVE doesn’t tell you whether Edge is vulnerable — you must map the Chromium revision to the Edge build. Microsoft’s SUG entries are designed to give precisely that mapping information and to state when Microsoft’s Edge builds no longer contain the vulnerability. Use the SUG entry as your authoritative signal for Edge ingestion status; the SUG entry will generally show which Edge version is affected or fixed. If you cannot view the SUG page (it renders as a JavaScript application in many browsers), consult Microsoft’s release notes (which include Edge release notes and mapping) or your management console which inventorieions.Final notes, caveats and verification of claims
- Chromium’s public metadata for CVE‑2026‑3940 indicates the vulnerability was fixed upstream in Chrome 146.0.7680.71. I verified the Chrome release notes promoting Chrome 146 to stable and the Chromium CVE metadata that lists the fixed baseline.
- Microsoft’s Security Update Guide lists Chrome‑assigned CVEs when the CVE affects Chromium code consumed by Edge; that listing is intended to communicate ingestion status and the Edge versions that are no longer vulnerable. The SUG FAQ specifically explains that these entries are for Chromium OSS consumed by Edge.
- If you cannot open the SUG web page because of client JavaScript restrictions, use your browser’s About page to check your Edge/Chrome version and cross‑reference Microsoft’s release notes and the Chromium release notes for mapping. Many community posts and vendor advisories repeat the same operational guidance; use the official Chrome release notes and Microsoft documentation as the authoritative sources for version and ingestion status.
Conclusion
CVE‑2026‑3940 is a DevTools policy enforcement bug fixed upstream in Chrome 146.0.7680.71. Microsoft’s inclusion of the CVE in the Security Update Guide is not an indication that Microsoft introduced the bug — it’s a practical, customer‑facing step that documents when Microsoft Edge (Chromium‑based) has consumed the upstream Chromium fix and when Edge installs are therefore no longer vulnerable. For users: check your browser’s About page and update to the latest stable build, then restart. For enterprises: inventory versions, orchestrate a managed roll‑out, verify post‑deployment restarts, and consider short‑term compensating controls for high‑risk groups until the patch is fully deployed. Following those straightforward steps will close the exposure window and make it much harder for attackers to exploit this DevTools policy bypass as part of a larger attack chain.Source: MSRC Security Update Guide - Microsoft Security Response Center