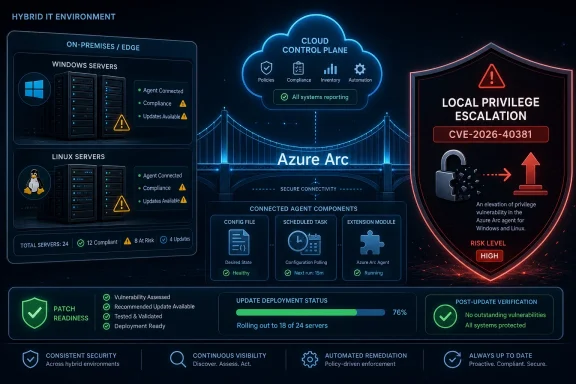
Microsoft disclosed CVE-2026-40381 on May 12, 2026, as an Important-rated elevation-of-privilege vulnerability in the Azure Connected Machine Agent, the software component that lets Windows and Linux servers outside Azure be managed through Azure Arc. The immediate story is not a flashy wormable remote-code-execution bug. It is the quieter kind of defect that matters deeply in hybrid estates: a local privilege path inside the agent that increasingly sits on servers Microsoft wants treated as cloud-managed endpoints.
The confidence signal around this vulnerability is also unusually important. Microsoft’s advisory confirms the issue exists, SANS’ May Patch Tuesday tracking lists it as not publicly disclosed and not known exploited at release, and Microsoft’s own agent release notes show a product cadence in which security fixes are being folded into routine monthly agent updates. That combination makes CVE-2026-40381 credible but not yet transparent: defenders can trust that there is a real bug, while attackers have less public technical detail than they would after a research blog, proof of concept, or patch diff narrative.
Azure Connected Machine Agent is one of those pieces of infrastructure software that quietly changes the shape of the attack surface. It is not a consumer-facing Windows feature, and it is not a traditional server role like IIS, SQL Server, or Active Directory Domain Services. Its job is to connect non-Azure machines to Azure Arc so they can be inventoried, governed, monitored, configured, and extended through Azure management planes.
That makes it strategically valuable. A server running the agent is not merely a server with another service installed; it is a server with a cloud management identity, local services, extension machinery, configuration state, and a communications path back into Azure. On Windows systems, the agent participates in the plumbing that allows administrators to bring hybrid machines under a common control plane. On Linux, it does much the same for fleets that may otherwise live in datacenters, edge sites, branch offices, hosting environments, or other clouds.
This is why an elevation-of-privilege bug in the agent deserves more attention than its “Important” label may suggest. Local privilege escalation is often treated as second-tier vulnerability news because it usually requires an attacker to already have some foothold. But in real intrusions, footholds are plentiful and administrator rights are the prize. Anything that turns a low-privilege local presence into higher privileges on a hybrid-managed server can become part of the middle act of an attack: persistence, credential access, lateral movement, and cloud identity abuse.
The uncomfortable lesson of Azure Arc is that hybrid management collapses old categories. A machine may be physically in a server room, logically governed from Azure, and operationally maintained through extensions and policies. A bug in that agent is therefore not only a local operating system concern. It is a local bug in software that helps decide how cloud control reaches into the machine.
That distinction matters. Many vulnerability write-ups blur existence, severity, exploitability, and operational risk into a single emotional reading. CVE-2026-40381 is a good reminder that those are separate judgments. A vendor-confirmed vulnerability can be very real even if the public does not yet know the root cause, the affected code path, the vulnerable versions, or the exploit preconditions.
As of publication, public reporting around Microsoft’s May 2026 Patch Tuesday identifies CVE-2026-40381 as not previously disclosed and not observed as exploited in the wild. That is meaningful. It suggests defenders are not dealing with a known exploited zero-day campaign at disclosure time, and it lowers the odds that commodity exploit kits will immediately absorb the bug based purely on public information.
But “not publicly disclosed” is not the same as “uninteresting.” Microsoft’s patches are artifacts. Attackers can compare versions, inspect installer changes, watch modified service behavior, and study how the agent’s files, scheduled tasks, named pipes, local services, extension handlers, and configuration stores have changed. A sparse advisory slows that work; it does not make it impossible.
The practical reading is therefore balanced, not complacent. CVE-2026-40381 is confirmed enough to patch with urgency, but opaque enough that public defenders should avoid pretending they know the exploit path unless Microsoft, a researcher, or a trustworthy reverse-engineering report provides more detail. In vulnerability management, that is exactly the kind of bug that gets mishandled: not dramatic enough for emergency bridges everywhere, but important enough to punish organizations that leave agents stale for months.
The catch is that CVSS is not an asset inventory. It does not know whether a particular Arc-enabled server is a domain controller, a backup server, a jump host, a build worker, a line-of-business application server, or a forgotten machine in a branch closet. It also does not know whether the same server has managed identity paths, monitoring extensions, update management dependencies, or policy enforcement roles that make local compromise more consequential.
For many WindowsForum readers, that is the real work. The question is not simply whether CVE-2026-40381 has a 7.8. The question is where the Azure Connected Machine Agent is installed, what version is running, whether automatic upgrade is enabled, whether the machine is reachable by lower-privilege users or service accounts, and whether local administrative boundaries are already under pressure.
The agent’s own release history reinforces the point. Microsoft’s Azure Connected Machine Agent release notes warn that only versions released within the last year are officially supported by the product group and recommend staying up to date whenever possible. The notes also show a steady stream of fixes around installation behavior, extension handling, local configuration, cryptography, named pipe validation, OpenSSL updates, and automatic upgrade behavior.
That pattern does not imply the agent is uniquely fragile. It implies the agent is alive, complex, and security-sensitive. A product that can install extensions, communicate with cloud services, manage local state, expose commands, and bridge policy into machines will inevitably have a larger privilege surface than a passive inventory tool.
Azure Arc is especially interesting in this respect because it gives non-Azure machines a representation inside Azure. That representation is useful to defenders. It is how organizations apply consistent governance to machines that do not live neatly inside Azure IaaS. But any technology that centralizes control also creates sharper consequences when local control is subverted.
Previous Azure Connected Machine Agent vulnerabilities underline the point. Public advisories from security researchers in early 2026 described local privilege-escalation paths involving scheduled task behavior and MSI repair functionality in older agent versions. Those were not the same vulnerability as CVE-2026-40381, and conflating them would be sloppy. But they show why researchers keep looking at this agent: it sits at an unusually rich intersection of Windows installer mechanics, scheduled execution, privileged services, update behavior, and cloud-connected identity.
This is the broader lesson for administrators. Management software is no longer background noise. The agent that helps you patch, monitor, inventory, and govern machines also needs to be patched, monitored, inventoried, and governed. If that sounds circular, welcome to modern operations.
That is the rhythm administrators should care about. The agent is not a static dependency that can be installed once and ignored until a migration project. Microsoft is shipping monthly improvements across Windows and Linux, and many of those improvements live close to the security boundary even when they are labeled as features, improvements, or bug fixes rather than CVEs.
The addition of
There is also a subtle warning in the release notes. Microsoft documents known issues around downgrading from agent version 1.61 to earlier versions on Windows, including a situation where the agent may become disconnected until permissions are changed on
The sensible posture is therefore not “install this one patch and move on.” It is to treat Connected Machine Agent lifecycle management as part of the platform baseline, with version reporting, automatic upgrade policy, exception handling, rollback testing, and monitoring for disconnected agents.
The Azure Connected Machine Agent runs on customer-managed machines. Those machines may be Windows Server boxes in a datacenter, Linux systems in another cloud, virtual machines in hosting environments, or physical servers at the edge. If the vulnerable component is local software, customer action can matter even when the advisory lives under Microsoft’s Azure umbrella.
This is where large organizations get tripped up. The cloud team may own Azure Arc policy. The server team may own Windows and Linux patching. The security team may own vulnerability scanning. The application team may own maintenance windows. The identity team may care only when managed identity or certificate authentication comes into play. A hybrid agent cuts across all of those boundaries, which means each team can assume someone else has it covered.
The fix is not organizational theater. It is asset clarity. An enterprise should be able to answer which machines are Arc-enabled, what agent version each one runs, whether the agent is healthy, whether automatic upgrades are enabled, and which business owners can approve emergency maintenance if a future Arc agent CVE is exploited in the wild.
For smaller shops, the work is simpler but still easy to miss. If you used Azure Arc to bring a few on-premises servers into Azure management and then stopped thinking about it, check the agent. If the agent was installed as part of a pilot, check whether the pilot machines are still connected. If the installer was packaged into a golden image, check whether that image is now distributing an old agent.
That is why local privilege escalation in an agent can be so useful. Once an attacker can abuse trusted management plumbing, the line between administrative activity and malicious activity becomes harder to draw. This is not unique to Microsoft. Endpoint management, backup, monitoring, EDR, configuration management, and remote support tools all carry versions of the same risk.
For Azure Connected Machine Agent, defenders should pay special attention to the places where normal behavior has sharp edges. Unexpected agent downgrades, repeated failed extension installs, unusual local users interacting with agent directories, modified scheduled tasks, changes to agent configuration files, abnormal service restarts, or unexplained disconnects from Azure Arc all deserve scrutiny.
The answer is not to distrust the agent. The answer is to understand its expected behavior well enough to spot abuse. A management plane that cannot be distinguished from an attacker’s living-off-the-land activity becomes a blind spot wrapped in a compliance dashboard.
Microsoft has been making visible improvements in this area. Recent release notes reference MSI signature verification, named pipe ownership validation, log security changes, TLS validation, OpenSSL updates, and reliability work around extension handling and configuration state. Those are the kinds of details that suggest the product team knows the local trust boundary is sensitive. They are also the kinds of details attackers notice.
For defenders, that is enough. A confirmed Microsoft CVE in a privileged hybrid-management agent should be remediated according to the exposure and importance of affected assets, even without a public proof of concept. Waiting for exploit code is not prudence; it is converting uncertainty into attacker advantage.
For attackers, the lack of detail raises the initial cost. They do not get a ready-made root cause from the advisory. They may not know whether the issue sits in Windows-only code, Linux-only code, shared agent logic, installer behavior, extension handling, IPC, configuration parsing, path validation, or some other component. They may not even know from public summaries which versions are affected unless release notes, package diffs, or later advisories reveal it.
But the metric also warns that knowledge can change. A vendor acknowledgement is a starting gun for reverse engineering. Once patched packages are available, motivated researchers and criminals can compare old and new behavior. If a later blog post explains the flaw, the public technical knowledge available to would-be attackers can jump from low to high overnight.
That is why patch timing matters. The safest window is before the exploit narrative hardens. In the first days after Patch Tuesday, defenders may have an advantage because the vulnerability is confirmed but not explained. That advantage disappears if organizations spend weeks debating whether an Important local elevation-of-privilege issue is worth touching.
For Windows administrators, the most immediate task is version discovery. Use whatever management tooling you already trust to identify installed Azure Connected Machine Agent versions, then compare them against Microsoft’s current release channel. Do not assume that Windows Update alone has handled the agent unless your environment is explicitly configured that way and reporting proves it.
For Linux administrators, the same principle applies through package inventory and agent health checks. The release notes show Linux-specific fixes and platform support changes, including extension behavior, GPG signature validation, package manager behavior, OpenSSL updates, and support for newer distributions. Linux Arc deployments are not second-class citizens in this risk model; they are part of the same hybrid control surface.
For security teams, CVE-2026-40381 belongs in the same operational conversation as local admin sprawl, service account hygiene, privileged access management, and endpoint detection coverage. If exploitation requires local access, then reducing unnecessary local access reduces exploitability. If exploitation yields elevated privileges, then monitoring privilege transitions and suspicious child processes around agent components becomes more important.
For Azure teams, the issue should trigger a review of Arc governance. Make sure disconnected agents are not silently ignored. Verify that automatic upgrade preview settings match organizational appetite. Confirm that policy assignments and extension deployments are not dependent on outdated agents. The agent is the bridge; a weak bridge undermines the promise of centralized control.
But it should not encourage deferral. The most dangerous vulnerabilities are not always the ones with the loudest headlines. They are often the ones sitting in software that organizations forgot they had standardized on. Azure Connected Machine Agent is exactly the kind of component that can become invisible once deployment succeeds.
The May disclosure also arrives after several months of visible Azure Connected Machine Agent hardening. January’s release addressed another agent CVE. February added Windows installer signature verification improvements. March introduced upgrade tooling and automatic-upgrade onboarding options. April tightened TLS checks and adjusted proxy communication with the local hybrid instance metadata service. That is a product evolving under security pressure, not a sleepy utility.
Administrators should resist the urge to treat CVE-2026-40381 as either a catastrophe or a footnote. It is a credible, vendor-confirmed local privilege-escalation vulnerability in a privileged hybrid-management agent. The correct response is disciplined urgency: identify, update, verify, and monitor.
That baseline should include agent version reporting, update mechanisms, exception review, and proof that the agent remains connected after upgrade. It should also include a plan for systems that cannot move quickly because of application dependencies, change freezes, disconnected network segments, or operating system age.
Microsoft’s release notes warning that only versions from the past year are officially supported should be read as more than housekeeping. Unsupported agents are a security debt multiplier. They miss fixes, drift from expected service behavior, and make incident response harder because administrators cannot easily distinguish old quirks from malicious anomalies.
The broader operational principle is simple: if a tool is important enough to manage your servers, it is important enough to manage carefully. Azure Arc has made hybrid management more coherent, but coherence is not the same as safety. The agent is now infrastructure.
Source: MSRC Security Update Guide - Microsoft Security Response Center
The confidence signal around this vulnerability is also unusually important. Microsoft’s advisory confirms the issue exists, SANS’ May Patch Tuesday tracking lists it as not publicly disclosed and not known exploited at release, and Microsoft’s own agent release notes show a product cadence in which security fixes are being folded into routine monthly agent updates. That combination makes CVE-2026-40381 credible but not yet transparent: defenders can trust that there is a real bug, while attackers have less public technical detail than they would after a research blog, proof of concept, or patch diff narrative.
 Azure Arc Turns the Management Agent Into a Security Boundary
Azure Arc Turns the Management Agent Into a Security Boundary
Azure Connected Machine Agent is one of those pieces of infrastructure software that quietly changes the shape of the attack surface. It is not a consumer-facing Windows feature, and it is not a traditional server role like IIS, SQL Server, or Active Directory Domain Services. Its job is to connect non-Azure machines to Azure Arc so they can be inventoried, governed, monitored, configured, and extended through Azure management planes.That makes it strategically valuable. A server running the agent is not merely a server with another service installed; it is a server with a cloud management identity, local services, extension machinery, configuration state, and a communications path back into Azure. On Windows systems, the agent participates in the plumbing that allows administrators to bring hybrid machines under a common control plane. On Linux, it does much the same for fleets that may otherwise live in datacenters, edge sites, branch offices, hosting environments, or other clouds.
This is why an elevation-of-privilege bug in the agent deserves more attention than its “Important” label may suggest. Local privilege escalation is often treated as second-tier vulnerability news because it usually requires an attacker to already have some foothold. But in real intrusions, footholds are plentiful and administrator rights are the prize. Anything that turns a low-privilege local presence into higher privileges on a hybrid-managed server can become part of the middle act of an attack: persistence, credential access, lateral movement, and cloud identity abuse.
The uncomfortable lesson of Azure Arc is that hybrid management collapses old categories. A machine may be physically in a server room, logically governed from Azure, and operationally maintained through extensions and policies. A bug in that agent is therefore not only a local operating system concern. It is a local bug in software that helps decide how cloud control reaches into the machine.
The Missing Exploit Details Are a Feature, Not a Comfort Blanket
The user-facing metric attached to CVE-2026-40381 asks a sensible question: how confident should we be that the vulnerability exists, and how much technical knowledge is available to attackers? In this case, the confidence that the vulnerability exists is high because Microsoft has assigned and published the CVE through its Security Update Guide. The confidence that the public knows how to exploit it is much lower.That distinction matters. Many vulnerability write-ups blur existence, severity, exploitability, and operational risk into a single emotional reading. CVE-2026-40381 is a good reminder that those are separate judgments. A vendor-confirmed vulnerability can be very real even if the public does not yet know the root cause, the affected code path, the vulnerable versions, or the exploit preconditions.
As of publication, public reporting around Microsoft’s May 2026 Patch Tuesday identifies CVE-2026-40381 as not previously disclosed and not observed as exploited in the wild. That is meaningful. It suggests defenders are not dealing with a known exploited zero-day campaign at disclosure time, and it lowers the odds that commodity exploit kits will immediately absorb the bug based purely on public information.
But “not publicly disclosed” is not the same as “uninteresting.” Microsoft’s patches are artifacts. Attackers can compare versions, inspect installer changes, watch modified service behavior, and study how the agent’s files, scheduled tasks, named pipes, local services, extension handlers, and configuration stores have changed. A sparse advisory slows that work; it does not make it impossible.
The practical reading is therefore balanced, not complacent. CVE-2026-40381 is confirmed enough to patch with urgency, but opaque enough that public defenders should avoid pretending they know the exploit path unless Microsoft, a researcher, or a trustworthy reverse-engineering report provides more detail. In vulnerability management, that is exactly the kind of bug that gets mishandled: not dramatic enough for emergency bridges everywhere, but important enough to punish organizations that leave agents stale for months.
The Severity Number Says “Important,” the Deployment Model Says “Check Your Estate”
The SANS Internet Storm Center’s May Patch Tuesday roundup lists CVE-2026-40381 with a CVSS base score of 7.8 and temporal score of 6.8. Microsoft classifies it as Important rather than Critical. Those numbers place it in familiar enterprise territory: serious enough to prioritize, not automatically the top item in a month that also includes critical Azure and Windows vulnerabilities.The catch is that CVSS is not an asset inventory. It does not know whether a particular Arc-enabled server is a domain controller, a backup server, a jump host, a build worker, a line-of-business application server, or a forgotten machine in a branch closet. It also does not know whether the same server has managed identity paths, monitoring extensions, update management dependencies, or policy enforcement roles that make local compromise more consequential.
For many WindowsForum readers, that is the real work. The question is not simply whether CVE-2026-40381 has a 7.8. The question is where the Azure Connected Machine Agent is installed, what version is running, whether automatic upgrade is enabled, whether the machine is reachable by lower-privilege users or service accounts, and whether local administrative boundaries are already under pressure.
The agent’s own release history reinforces the point. Microsoft’s Azure Connected Machine Agent release notes warn that only versions released within the last year are officially supported by the product group and recommend staying up to date whenever possible. The notes also show a steady stream of fixes around installation behavior, extension handling, local configuration, cryptography, named pipe validation, OpenSSL updates, and automatic upgrade behavior.
That pattern does not imply the agent is uniquely fragile. It implies the agent is alive, complex, and security-sensitive. A product that can install extensions, communicate with cloud services, manage local state, expose commands, and bridge policy into machines will inevitably have a larger privilege surface than a passive inventory tool.
Hybrid Management Has Made Local Privilege Escalation Fashionable Again
The industry spent years training people to fear remote code execution above all else. That instinct is still mostly correct when the bug is pre-authenticated, network reachable, and reliable. But cloud-managed infrastructure has made local privilege escalation fashionable again because local privilege is often the step that unlocks tokens, agents, configuration secrets, certificate material, and service identities.Azure Arc is especially interesting in this respect because it gives non-Azure machines a representation inside Azure. That representation is useful to defenders. It is how organizations apply consistent governance to machines that do not live neatly inside Azure IaaS. But any technology that centralizes control also creates sharper consequences when local control is subverted.
Previous Azure Connected Machine Agent vulnerabilities underline the point. Public advisories from security researchers in early 2026 described local privilege-escalation paths involving scheduled task behavior and MSI repair functionality in older agent versions. Those were not the same vulnerability as CVE-2026-40381, and conflating them would be sloppy. But they show why researchers keep looking at this agent: it sits at an unusually rich intersection of Windows installer mechanics, scheduled execution, privileged services, update behavior, and cloud-connected identity.
This is the broader lesson for administrators. Management software is no longer background noise. The agent that helps you patch, monitor, inventory, and govern machines also needs to be patched, monitored, inventoried, and governed. If that sounds circular, welcome to modern operations.
Microsoft’s Monthly Agent Cadence Is Doing More Work Than the Advisory
One of the stranger aspects of CVE-2026-40381 is that Microsoft’s Security Update Guide page is the official vulnerability source, while the most operationally useful context often lives elsewhere. The Azure Connected Machine Agent release notes show how the product has been moving month by month: version 1.60 in January addressed CVE-2026-21224, version 1.61 in February added MSI signature verification to the Windows installation script, version 1.62 in March added an agent upgrade command and automatic-upgrade onboarding flag, and version 1.63 in April added TLS cipher-suite validation to theazcmagent check command.That is the rhythm administrators should care about. The agent is not a static dependency that can be installed once and ignored until a migration project. Microsoft is shipping monthly improvements across Windows and Linux, and many of those improvements live close to the security boundary even when they are labeled as features, improvements, or bug fixes rather than CVEs.
The addition of
azcmagent upgrade in version 1.62 is particularly important because it gives administrators a more direct path to agent maintenance. The automatic-upgrade work matters for the same reason. Hybrid server fleets often fail at the boring part of security: keeping helper agents aligned across hundreds or thousands of machines that belong to different teams, maintenance windows, business units, or operating system baselines.There is also a subtle warning in the release notes. Microsoft documents known issues around downgrading from agent version 1.61 to earlier versions on Windows, including a situation where the agent may become disconnected until permissions are changed on
agentconfig.json. That is not directly about CVE-2026-40381, but it is operationally relevant. Agent rollback and downgrade are not risk-free escape hatches; they can create management drift precisely when administrators need visibility most.The sensible posture is therefore not “install this one patch and move on.” It is to treat Connected Machine Agent lifecycle management as part of the platform baseline, with version reporting, automatic upgrade policy, exception handling, rollback testing, and monitoring for disconnected agents.
The Cloud Label Can Hide the Machines That Actually Need Work
Patch Tuesday now routinely includes Azure vulnerabilities with the reassuring note that no customer action is required. That is reasonable for many cloud-service flaws because Microsoft owns the infrastructure and can remediate server-side components. CVE-2026-40381 should not be mentally filed in the same drawer merely because it has Azure in the product name.The Azure Connected Machine Agent runs on customer-managed machines. Those machines may be Windows Server boxes in a datacenter, Linux systems in another cloud, virtual machines in hosting environments, or physical servers at the edge. If the vulnerable component is local software, customer action can matter even when the advisory lives under Microsoft’s Azure umbrella.
This is where large organizations get tripped up. The cloud team may own Azure Arc policy. The server team may own Windows and Linux patching. The security team may own vulnerability scanning. The application team may own maintenance windows. The identity team may care only when managed identity or certificate authentication comes into play. A hybrid agent cuts across all of those boundaries, which means each team can assume someone else has it covered.
The fix is not organizational theater. It is asset clarity. An enterprise should be able to answer which machines are Arc-enabled, what agent version each one runs, whether the agent is healthy, whether automatic upgrades are enabled, and which business owners can approve emergency maintenance if a future Arc agent CVE is exploited in the wild.
For smaller shops, the work is simpler but still easy to miss. If you used Azure Arc to bring a few on-premises servers into Azure management and then stopped thinking about it, check the agent. If the agent was installed as part of a pilot, check whether the pilot machines are still connected. If the installer was packaged into a golden image, check whether that image is now distributing an old agent.
Attackers Love Agents Because Agents Already Have Permission to Be Weird
Security tools often focus on obviously suspicious behavior: unknown binaries, unusual PowerShell, unexpected outbound connections, new services, tampered registry keys, or privilege changes. Management agents complicate that model because they are supposed to do things that would look suspicious if performed by random software. They talk to cloud endpoints. They update themselves. They run scripts. They install and remove extensions. They write logs in specialized directories. They interact with privileged local services.That is why local privilege escalation in an agent can be so useful. Once an attacker can abuse trusted management plumbing, the line between administrative activity and malicious activity becomes harder to draw. This is not unique to Microsoft. Endpoint management, backup, monitoring, EDR, configuration management, and remote support tools all carry versions of the same risk.
For Azure Connected Machine Agent, defenders should pay special attention to the places where normal behavior has sharp edges. Unexpected agent downgrades, repeated failed extension installs, unusual local users interacting with agent directories, modified scheduled tasks, changes to agent configuration files, abnormal service restarts, or unexplained disconnects from Azure Arc all deserve scrutiny.
The answer is not to distrust the agent. The answer is to understand its expected behavior well enough to spot abuse. A management plane that cannot be distinguished from an attacker’s living-off-the-land activity becomes a blind spot wrapped in a compliance dashboard.
Microsoft has been making visible improvements in this area. Recent release notes reference MSI signature verification, named pipe ownership validation, log security changes, TLS validation, OpenSSL updates, and reliability work around extension handling and configuration state. Those are the kinds of details that suggest the product team knows the local trust boundary is sensitive. They are also the kinds of details attackers notice.
The Confidence Metric Cuts Both Ways
The vulnerability-confidence metric supplied with the CVE description is a useful lens because it captures a truth administrators often feel but rarely name. A vulnerability can be vendor-confirmed while its mechanics remain private. That raises confidence in existence but constrains confidence in exploit detail.For defenders, that is enough. A confirmed Microsoft CVE in a privileged hybrid-management agent should be remediated according to the exposure and importance of affected assets, even without a public proof of concept. Waiting for exploit code is not prudence; it is converting uncertainty into attacker advantage.
For attackers, the lack of detail raises the initial cost. They do not get a ready-made root cause from the advisory. They may not know whether the issue sits in Windows-only code, Linux-only code, shared agent logic, installer behavior, extension handling, IPC, configuration parsing, path validation, or some other component. They may not even know from public summaries which versions are affected unless release notes, package diffs, or later advisories reveal it.
But the metric also warns that knowledge can change. A vendor acknowledgement is a starting gun for reverse engineering. Once patched packages are available, motivated researchers and criminals can compare old and new behavior. If a later blog post explains the flaw, the public technical knowledge available to would-be attackers can jump from low to high overnight.
That is why patch timing matters. The safest window is before the exploit narrative hardens. In the first days after Patch Tuesday, defenders may have an advantage because the vulnerability is confirmed but not explained. That advantage disappears if organizations spend weeks debating whether an Important local elevation-of-privilege issue is worth touching.
Windows Admins Should Treat Arc Like a Tier-Zero Adjacent Dependency
Not every Arc-enabled server is tier zero, and it would be absurd to pretend otherwise. A lightly used test machine and a domain controller do not carry the same blast radius. But the agent should be treated as tier-zero adjacent because it participates in the management and identity story of machines that may themselves be highly privileged.For Windows administrators, the most immediate task is version discovery. Use whatever management tooling you already trust to identify installed Azure Connected Machine Agent versions, then compare them against Microsoft’s current release channel. Do not assume that Windows Update alone has handled the agent unless your environment is explicitly configured that way and reporting proves it.
For Linux administrators, the same principle applies through package inventory and agent health checks. The release notes show Linux-specific fixes and platform support changes, including extension behavior, GPG signature validation, package manager behavior, OpenSSL updates, and support for newer distributions. Linux Arc deployments are not second-class citizens in this risk model; they are part of the same hybrid control surface.
For security teams, CVE-2026-40381 belongs in the same operational conversation as local admin sprawl, service account hygiene, privileged access management, and endpoint detection coverage. If exploitation requires local access, then reducing unnecessary local access reduces exploitability. If exploitation yields elevated privileges, then monitoring privilege transitions and suspicious child processes around agent components becomes more important.
For Azure teams, the issue should trigger a review of Arc governance. Make sure disconnected agents are not silently ignored. Verify that automatic upgrade preview settings match organizational appetite. Confirm that policy assignments and extension deployments are not dependent on outdated agents. The agent is the bridge; a weak bridge undermines the promise of centralized control.
Patch Tuesday’s Real Lesson Is Inventory, Not Panic
Microsoft’s May 2026 Patch Tuesday was large, with SANS counting 137 Microsoft vulnerabilities and additional Chromium-related fixes for Edge. CVE-2026-40381 is one item in that pile. It is not the highest-scoring cloud issue of the month, and it is not reported as exploited in the wild at release. That context should prevent panic.But it should not encourage deferral. The most dangerous vulnerabilities are not always the ones with the loudest headlines. They are often the ones sitting in software that organizations forgot they had standardized on. Azure Connected Machine Agent is exactly the kind of component that can become invisible once deployment succeeds.
The May disclosure also arrives after several months of visible Azure Connected Machine Agent hardening. January’s release addressed another agent CVE. February added Windows installer signature verification improvements. March introduced upgrade tooling and automatic-upgrade onboarding options. April tightened TLS checks and adjusted proxy communication with the local hybrid instance metadata service. That is a product evolving under security pressure, not a sleepy utility.
Administrators should resist the urge to treat CVE-2026-40381 as either a catastrophe or a footnote. It is a credible, vendor-confirmed local privilege-escalation vulnerability in a privileged hybrid-management agent. The correct response is disciplined urgency: identify, update, verify, and monitor.
The Arc Agent Is Now Part of the Patch Baseline
The concrete response to CVE-2026-40381 is not complicated, but it does require ownership. Someone has to decide that the Azure Connected Machine Agent is part of the normal patch baseline, not an Azure curiosity installed outside the operating system lifecycle.That baseline should include agent version reporting, update mechanisms, exception review, and proof that the agent remains connected after upgrade. It should also include a plan for systems that cannot move quickly because of application dependencies, change freezes, disconnected network segments, or operating system age.
Microsoft’s release notes warning that only versions from the past year are officially supported should be read as more than housekeeping. Unsupported agents are a security debt multiplier. They miss fixes, drift from expected service behavior, and make incident response harder because administrators cannot easily distinguish old quirks from malicious anomalies.
The broader operational principle is simple: if a tool is important enough to manage your servers, it is important enough to manage carefully. Azure Arc has made hybrid management more coherent, but coherence is not the same as safety. The agent is now infrastructure.
A Short List for the People Who Have to Fix This by Friday
CVE-2026-40381 does not require theatrical response, but it does reward teams that already know where their hybrid management components live. The organizations that struggle will be the ones that discover during remediation that no single team owns agent currency across Windows, Linux, on-premises, edge, and cloud-adjacent machines.- Inventory every Arc-enabled machine and record the installed Azure Connected Machine Agent version before assuming the fleet is current.
- Prioritize updates on servers where local compromise would have outsized consequences, including identity infrastructure, management hosts, backup systems, build servers, and high-value application platforms.
- Confirm whether automatic agent upgrades are enabled, whether they are appropriate for the environment, and whether exceptions are documented rather than accidental.
- Watch for suspicious local interaction with agent services, configuration files, scheduled tasks, extension directories, and unexpected agent disconnects during the remediation window.
- Treat the lack of public exploit detail as a temporary defender advantage, not as evidence that the vulnerability can be ignored.
Source: MSRC Security Update Guide - Microsoft Security Response Center