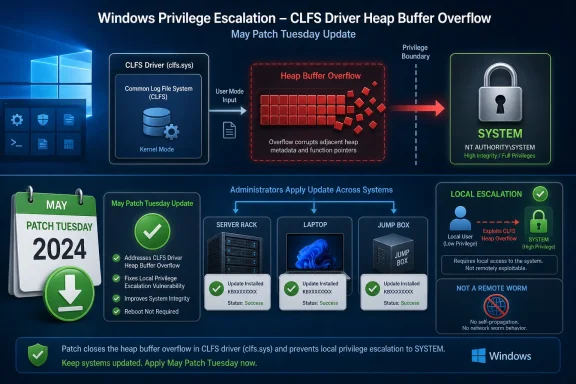
Microsoft disclosed CVE-2026-40407 on May 12, 2026 as an Important Windows Common Log File System Driver elevation-of-privilege vulnerability, caused by a heap-based buffer overflow and affecting supported Windows client and server releases with updates available through the May Patch Tuesday release. The short version is that this is not a remote worm, not a panic button, and not something administrators should leave to drift. It is a local privilege escalation bug in a historically sensitive Windows kernel-adjacent component, and Microsoft says a successful attacker could gain SYSTEM privileges. That combination makes it the kind of flaw that matters most after an attacker has already found a foothold.
The Common Log File System driver is not a household Windows component, but it has become familiar territory to defenders who track local privilege escalation. CLFS sits in the plumbing of Windows, providing log-file services used by system and application components. When a vulnerability appears there, the question is rarely whether a random internet scan can hit it directly; the more practical question is what it does for an attacker who has already landed code on the box.
CVE-2026-40407 answers that question plainly. Microsoft describes the issue as a heap-based buffer overflow in the Windows Common Log File System Driver that allows an authorized attacker to elevate privileges locally. The advisory’s FAQ says successful exploitation could yield SYSTEM privileges, the level of authority that turns an ordinary compromise into near-total control of a Windows installation.
That distinction is important because “local” can be misleadingly reassuring. Local exploitation does not mean an attacker needs to be physically seated at the keyboard. It means the exploit path is not directly through the network stack; a phished user session, malware dropped by another vulnerability, abuse of exposed remote access, or a compromised low-privilege account can all provide the starting point.
Microsoft’s own CVSS vector captures that shape: local attack vector, low attack complexity, low privileges required, and no user interaction. The base score is 7.8, with a temporal score of 6.8 after accounting for Microsoft’s assessment that exploit code is unproven and an official fix is available. In other words, the bug is not rated Critical, but the mechanics are exactly what red teams and ransomware operators like to pair with initial access.
But the score also tells a less comforting story. Low attack complexity means Microsoft does not believe exploitation depends on exotic timing, improbable system state, or a highly unusual configuration. Low privileges required means a basic authenticated attacker may be enough. No user interaction means the attacker does not need to trick a second user into clicking a file or approving a prompt once the attacker is already in position.
The impact metrics are the part administrators should not skim past. Microsoft rates confidentiality, integrity, and availability impact as high. That is consistent with a privilege-escalation flaw that can move an attacker into SYSTEM context, where credential theft, defense tampering, persistence, data access, and destructive activity become far easier.
The temporal metrics add nuance rather than comfort. Microsoft lists exploit code maturity as unproven, says the vulnerability was not publicly disclosed before release, and says it was not known to be exploited at the time of original publication. That lowers urgency compared with an actively exploited zero-day, but it does not lower the value of the vulnerability to attackers once patch diffing begins.
That matters because vulnerability triage is usually an exercise in rationing doubt. Security teams routinely face vague advisories, disputed proof-of-concept claims, speculative exploit chatter, and scanner findings that need validation. “Confirmed” removes one layer of ambiguity: Microsoft is acknowledging the presence of the vulnerability in affected code.
It does not mean a public exploit exists. It does not mean attackers are already using it. It does mean defenders should treat the flaw as real, reproducible enough for the vendor to patch, and technically concrete enough to deserve normal Patch Tuesday handling rather than indefinite deferral.
There is a second-order effect as well. Once a Windows update ships, attackers can compare vulnerable and fixed binaries to infer what changed. CLFS bugs are especially attractive in that setting because a local privilege escalation exploit does not need to break into the perimeter by itself; it only needs to upgrade an existing foothold.
That history does not prove that this specific CVE is easy to weaponize. It does, however, explain why defenders notice the component. CLFS is a kernel-mode driver with a role in managing log files; mistakes in its memory handling can have consequences well beyond an application crash.
Microsoft identifies the weakness here as CWE-122, a heap-based buffer overflow. That classification is useful because it tells us more than the marketing name of the bug. Heap corruption issues can be difficult to exploit reliably on modern Windows because of mitigations, but when they are exploitable in privileged code, they can become powerful building blocks for privilege escalation.
The advisory’s “Exploitation Unlikely” assessment should therefore be read as a point-in-time judgment, not a lifetime guarantee. Microsoft is saying that, at publication, exploitation is not expected to be straightforward or likely in the near term. Attackers and researchers now have the patch, the affected component, the weakness class, and the privilege outcome.
That range is a reminder that CLFS is not a niche feature enabled only by a particular role. It is Windows infrastructure. If your organization runs supported Windows endpoints and servers, this is probably in your May patch universe unless a specific edition is outside support or handled through a separate servicing channel.
The update table also shows the complexity of modern Windows servicing. Some platforms receive conventional security updates, while newer server and client servicing paths may show hotpatch entries alongside cumulative updates. Windows Server 2025 and some Windows 11 24H2 or 25H2 entries, for example, appear with both standard security update and security hotpatch options.
For administrators, that means the operative question is not “Do we have CLFS?” but “Which servicing mechanism gets every affected build to the fixed version?” In a mixed estate, the answer may differ by operating system generation, architecture, and whether hotpatching is in use.
But hotpatching does not eliminate the need for inventory discipline. A hotpatch is only useful for machines enrolled in the right servicing model and eligible for that update path. Older Server Core deployments, long-lived Windows 10 builds, and conventional Windows Server systems still depend on the familiar cumulative update process.
The danger in mixed estates is false confidence. A dashboard may show that the newest Windows Server 2025 systems received a hotpatch while older domain members, application servers, or VDI images remain exposed. Attackers do not need the newest machines to be vulnerable; they need one reachable, useful host with a low-privilege foothold and an escalation path.
The operational answer is dull but necessary: confirm fixed build numbers, not just update intent. Microsoft’s advisory lists build numbers for affected products after the fix. Those numbers are the ground truth administrators should compare against endpoint management, vulnerability scanning, and configuration management data.
Local privilege escalation bugs are especially relevant on endpoints because the first foothold is often a user context. Phishing, malicious attachments, browser exploitation, drive-by malware, or credential abuse may land an attacker with limited privileges. A kernel or driver EoP bug is the bridge from “compromised user” to “compromised machine.”
That makes endpoint patch timing more important than the severity label alone suggests. A low-privilege local bug may not be the first link in the chain, but it can be the link that makes the rest of the chain painful. Once SYSTEM is available, tampering with security tools, dumping credentials, disabling recovery mechanisms, and staging lateral movement all become more feasible.
For home users, the prescription is simpler: install the May 2026 Windows security update when offered. For businesses, the work is more procedural: validate update rings, watch for deployment failures, and ensure remote and rarely connected endpoints do not fall behind.
A phishing attachment gives code execution as the user. A stolen VPN credential gives an authenticated position in the environment. A misconfigured service gives a low-privilege shell. A browser bug gives sandboxed or user-level execution. A CLFS elevation-of-privilege exploit, if weaponized, can turn any of those into SYSTEM.
This is why “Exploitation Unlikely” should not become “No action required.” Microsoft’s exploitability assessment is valuable, but adversaries make their own calculations. A bug with low privileges required, no user interaction, and SYSTEM impact has obvious utility if exploit development proves viable.
The practical priority should be based on exposure to compromise chains. Internet-facing servers may not be directly vulnerable to remote exploitation through this CVE, but if they host applications that could be compromised through other flaws, local escalation becomes relevant. Endpoints used by administrators, developers, finance teams, and help desk staff deserve particular attention because a local SYSTEM foothold there can have outsized consequences.
But Patch Tuesday starts a different clock. Public patches provide defenders with fixes and attackers with clues. Security researchers and exploit developers can inspect the delta between vulnerable and fixed versions, identify the patched code path, and test whether the bug can be turned into a reliable primitive.
This does not happen instantly for every vulnerability. Modern Windows mitigations are meaningful, and heap-based kernel exploitation is not a trivial exercise. Still, local privilege escalation bugs often move from advisory to proof of concept faster than organizations move from “approved for testing” to “fully deployed.”
That asymmetry is the core patch-management problem. Vendors publish monthly; attackers can specialize; defenders must maintain uptime, compatibility, and change control across messy environments. The right response is not panic, but it is also not complacency.
With SYSTEM, an attacker can often access sensitive local resources, manipulate services, interfere with endpoint protection, and harvest credentials from places that are unavailable to a standard user. Depending on configuration, they may also gain the leverage needed to move laterally or establish persistence that survives reboots and user logoffs.
This is why local privilege escalation bugs routinely matter in ransomware intrusions. Initial access gets the adversary inside; privilege escalation gives them room to operate. The difference between a contained user compromise and a full host compromise is often the difference between incident cleanup and incident response.
CVE-2026-40407 should therefore be prioritized by consequence, not just entry point. A local-only bug with SYSTEM impact can be more operationally dangerous than a noisier remote flaw with limited post-exploitation value.
Start with systems where a low-privilege foothold is plausible and the prize is high. That includes administrator workstations, jump boxes, developer endpoints, shared servers, VDI hosts, Remote Desktop Session Hosts, and servers running applications with a history of upload, scripting, or service-account exposure. Domain controllers are not affected because they run Windows in some abstract sense; they matter because any local escalation on a high-trust server can have disproportionate blast radius.
For servers, normal staging still makes sense. Microsoft’s recent patch history has reminded administrators that cumulative updates can introduce regressions, especially in complex Active Directory or server-role scenarios. But staging should be measured in days, not weeks, when the vulnerability provides SYSTEM-level escalation and the affected component is broadly present.
For endpoints, broad deployment is usually the better default. The operational risk of a Windows client cumulative update is real, but the security risk of allowing local escalation paths to persist across a large endpoint population is also real. Users generate footholds; attackers look for privilege boundaries to cross.
Hardening still matters, but it is not a substitute. Least privilege, application control, attack surface reduction rules, EDR, credential protection, and removal of unnecessary local administrator rights can reduce the likelihood that an attacker reaches the point where this CVE is useful. They do not remove the vulnerable code from affected systems.
The same is true of monitoring. Security teams should watch for suspicious local privilege escalation behavior, abnormal CLFS-related crashes, unexpected service creation, tampering with security products, and post-exploitation patterns. But detection is a backstop, not a remediation plan.
The best defense is boring: patch supported systems, verify fixed builds, and investigate machines that fail to report compliance. For a vulnerability like this, boring is what works.
Windows estates are layered over years of procurement, application compatibility decisions, hardware refresh cycles, and migration delays. A vulnerability in shared OS plumbing cuts across those layers. The same CVE may require different KBs, different fixed build numbers, and different reboot expectations.
This is where vulnerability management tools can both help and mislead. A scanner that says “CVE-2026-40407 present” is useful, but only if it maps correctly to the edition, build, and servicing channel. A deployment dashboard that says “May update installed” is useful, but only if it includes systems that were offline, paused, excluded, or stuck behind failed prerequisites.
The safest approach is to reconcile three views: Microsoft’s affected-product list, your patch deployment status, and actual endpoint build inventory. Any gap between those views is where this kind of bug lingers.
The move to publish CWE information in advisories helps here. Calling this a heap-based buffer overflow gives defenders and researchers a more precise way to track patterns across Windows components. It also exposes the uncomfortable continuity: memory safety remains a central weakness class in privileged Windows code.
Microsoft’s Secure Future Initiative messaging has leaned heavily on engineering discipline, secure-by-design defaults, and systemic reduction of vulnerability classes. CVE-2026-40407 is the sort of bug that tests whether that program becomes visible in the monthly patch data. One CLFS bug does not disprove a strategy; repeated CLFS bugs over time do raise fair questions about where legacy code, fuzzing coverage, and memory-safe rewrites sit on the priority list.
For customers, that broader debate is interesting but secondary. The vulnerable code is in the field today, the fix is available today, and the risk is borne by administrators who must keep mixed Windows fleets secure while Microsoft continues the longer engineering cleanup.
That combination makes it a classic second-stage vulnerability. It is not the burglar smashing the front window; it is the master key found once the burglar is inside the building. Enterprises that think in attack chains will patch it accordingly.
The strongest signal may be the plainness of Microsoft’s description. There is no elaborate prerequisite, no special feature dependency, no requirement for the victim to open a file, and no suggestion that only obscure SKUs are affected. It is Windows, it is CLFS, and it is privilege escalation.
That is enough.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft Patches the Kind of Bug Attackers Use After the Door Is Open
Microsoft Patches the Kind of Bug Attackers Use After the Door Is Open
The Common Log File System driver is not a household Windows component, but it has become familiar territory to defenders who track local privilege escalation. CLFS sits in the plumbing of Windows, providing log-file services used by system and application components. When a vulnerability appears there, the question is rarely whether a random internet scan can hit it directly; the more practical question is what it does for an attacker who has already landed code on the box.CVE-2026-40407 answers that question plainly. Microsoft describes the issue as a heap-based buffer overflow in the Windows Common Log File System Driver that allows an authorized attacker to elevate privileges locally. The advisory’s FAQ says successful exploitation could yield SYSTEM privileges, the level of authority that turns an ordinary compromise into near-total control of a Windows installation.
That distinction is important because “local” can be misleadingly reassuring. Local exploitation does not mean an attacker needs to be physically seated at the keyboard. It means the exploit path is not directly through the network stack; a phished user session, malware dropped by another vulnerability, abuse of exposed remote access, or a compromised low-privilege account can all provide the starting point.
Microsoft’s own CVSS vector captures that shape: local attack vector, low attack complexity, low privileges required, and no user interaction. The base score is 7.8, with a temporal score of 6.8 after accounting for Microsoft’s assessment that exploit code is unproven and an official fix is available. In other words, the bug is not rated Critical, but the mechanics are exactly what red teams and ransomware operators like to pair with initial access.
The CVSS Score Says “Important,” but the Privilege Boundary Says “Pay Attention”
Microsoft’s “Important” severity label is doing a lot of work here. It correctly signals that CVE-2026-40407 is not a pre-authenticated remote-code-execution disaster. It should not be confused with the sort of server-side flaw that allows mass exploitation before anyone logs in.But the score also tells a less comforting story. Low attack complexity means Microsoft does not believe exploitation depends on exotic timing, improbable system state, or a highly unusual configuration. Low privileges required means a basic authenticated attacker may be enough. No user interaction means the attacker does not need to trick a second user into clicking a file or approving a prompt once the attacker is already in position.
The impact metrics are the part administrators should not skim past. Microsoft rates confidentiality, integrity, and availability impact as high. That is consistent with a privilege-escalation flaw that can move an attacker into SYSTEM context, where credential theft, defense tampering, persistence, data access, and destructive activity become far easier.
The temporal metrics add nuance rather than comfort. Microsoft lists exploit code maturity as unproven, says the vulnerability was not publicly disclosed before release, and says it was not known to be exploited at the time of original publication. That lowers urgency compared with an actively exploited zero-day, but it does not lower the value of the vulnerability to attackers once patch diffing begins.
“Confirmed” Is the Quiet Metric That Should Change the Conversation
The user-supplied note about Report Confidence goes to the heart of this advisory. In CVSS terms, Report Confidence measures how certain the vendor and community are that a vulnerability exists and how credible the available technical details are. For CVE-2026-40407, Microsoft marks that value as Confirmed.That matters because vulnerability triage is usually an exercise in rationing doubt. Security teams routinely face vague advisories, disputed proof-of-concept claims, speculative exploit chatter, and scanner findings that need validation. “Confirmed” removes one layer of ambiguity: Microsoft is acknowledging the presence of the vulnerability in affected code.
It does not mean a public exploit exists. It does not mean attackers are already using it. It does mean defenders should treat the flaw as real, reproducible enough for the vendor to patch, and technically concrete enough to deserve normal Patch Tuesday handling rather than indefinite deferral.
There is a second-order effect as well. Once a Windows update ships, attackers can compare vulnerable and fixed binaries to infer what changed. CLFS bugs are especially attractive in that setting because a local privilege escalation exploit does not need to break into the perimeter by itself; it only needs to upgrade an existing foothold.
CLFS Has Become a Familiar Escalation Surface
CVE-2026-40407 is not appearing in a vacuum. The Windows Common Log File System driver has repeatedly shown up in Microsoft security bulletins and modern Patch Tuesday cycles. Over the last decade, CLFS-related elevation-of-privilege issues have been a recurring theme, including multiple memory-handling bugs and several vulnerabilities that drew attention because of exploitation or post-exploitation value.That history does not prove that this specific CVE is easy to weaponize. It does, however, explain why defenders notice the component. CLFS is a kernel-mode driver with a role in managing log files; mistakes in its memory handling can have consequences well beyond an application crash.
Microsoft identifies the weakness here as CWE-122, a heap-based buffer overflow. That classification is useful because it tells us more than the marketing name of the bug. Heap corruption issues can be difficult to exploit reliably on modern Windows because of mitigations, but when they are exploitable in privileged code, they can become powerful building blocks for privilege escalation.
The advisory’s “Exploitation Unlikely” assessment should therefore be read as a point-in-time judgment, not a lifetime guarantee. Microsoft is saying that, at publication, exploitation is not expected to be straightforward or likely in the near term. Attackers and researchers now have the patch, the affected component, the weakness class, and the privilege outcome.
The Affected List Spans Old Estates and New Windows Builds
One reason this advisory deserves enterprise attention is its breadth. Microsoft lists affected updates across Windows Server 2012 and 2012 R2, Windows Server 2016, Windows Server 2019, Windows Server 2022, Windows Server 2025, Windows 10, and Windows 11 releases including 23H2, 24H2, 25H2, and 26H1 entries. Both x64 and ARM64 client builds appear where applicable, along with Server Core variants.That range is a reminder that CLFS is not a niche feature enabled only by a particular role. It is Windows infrastructure. If your organization runs supported Windows endpoints and servers, this is probably in your May patch universe unless a specific edition is outside support or handled through a separate servicing channel.
The update table also shows the complexity of modern Windows servicing. Some platforms receive conventional security updates, while newer server and client servicing paths may show hotpatch entries alongside cumulative updates. Windows Server 2025 and some Windows 11 24H2 or 25H2 entries, for example, appear with both standard security update and security hotpatch options.
For administrators, that means the operative question is not “Do we have CLFS?” but “Which servicing mechanism gets every affected build to the fixed version?” In a mixed estate, the answer may differ by operating system generation, architecture, and whether hotpatching is in use.
Hotpatching Helps, but It Does Not Absolve Inventory
The presence of security hotpatch entries is a sign of where Microsoft wants enterprise servicing to go. Hotpatching promises reduced reboot pressure, faster deployment, and less friction for security fixes. For server fleets, that is not a small operational improvement.But hotpatching does not eliminate the need for inventory discipline. A hotpatch is only useful for machines enrolled in the right servicing model and eligible for that update path. Older Server Core deployments, long-lived Windows 10 builds, and conventional Windows Server systems still depend on the familiar cumulative update process.
The danger in mixed estates is false confidence. A dashboard may show that the newest Windows Server 2025 systems received a hotpatch while older domain members, application servers, or VDI images remain exposed. Attackers do not need the newest machines to be vulnerable; they need one reachable, useful host with a low-privilege foothold and an escalation path.
The operational answer is dull but necessary: confirm fixed build numbers, not just update intent. Microsoft’s advisory lists build numbers for affected products after the fix. Those numbers are the ground truth administrators should compare against endpoint management, vulnerability scanning, and configuration management data.
Windows 10’s Long Goodbye Makes This More Than a Server Story
CVE-2026-40407 also lands in the uncomfortable final stretch of Windows 10’s mainstream enterprise life. Windows 10 Version 22H2 remains present in many fleets, and the advisory includes Windows 10 21H2 and 22H2 variants among affected products. Even organizations with Windows 11 migration projects underway still have pockets of Windows 10 machines that carry operational risk.Local privilege escalation bugs are especially relevant on endpoints because the first foothold is often a user context. Phishing, malicious attachments, browser exploitation, drive-by malware, or credential abuse may land an attacker with limited privileges. A kernel or driver EoP bug is the bridge from “compromised user” to “compromised machine.”
That makes endpoint patch timing more important than the severity label alone suggests. A low-privilege local bug may not be the first link in the chain, but it can be the link that makes the rest of the chain painful. Once SYSTEM is available, tampering with security tools, dumping credentials, disabling recovery mechanisms, and staging lateral movement all become more feasible.
For home users, the prescription is simpler: install the May 2026 Windows security update when offered. For businesses, the work is more procedural: validate update rings, watch for deployment failures, and ensure remote and rarely connected endpoints do not fall behind.
The Real Risk Is Chaining, Not Drive-By Exploitation
The most common mistake in reading an advisory like this is to ask whether CVE-2026-40407 can be exploited remotely over the internet. The better question is whether it can be chained after an attacker gets code execution by some other means. That is how many Windows privilege escalation bugs earn their keep.A phishing attachment gives code execution as the user. A stolen VPN credential gives an authenticated position in the environment. A misconfigured service gives a low-privilege shell. A browser bug gives sandboxed or user-level execution. A CLFS elevation-of-privilege exploit, if weaponized, can turn any of those into SYSTEM.
This is why “Exploitation Unlikely” should not become “No action required.” Microsoft’s exploitability assessment is valuable, but adversaries make their own calculations. A bug with low privileges required, no user interaction, and SYSTEM impact has obvious utility if exploit development proves viable.
The practical priority should be based on exposure to compromise chains. Internet-facing servers may not be directly vulnerable to remote exploitation through this CVE, but if they host applications that could be compromised through other flaws, local escalation becomes relevant. Endpoints used by administrators, developers, finance teams, and help desk staff deserve particular attention because a local SYSTEM foothold there can have outsized consequences.
The Absence of Public Exploitation Is a Window, Not a Verdict
Microsoft says CVE-2026-40407 was not publicly disclosed and not exploited at the time it was published. That is good news. It means defenders are not already racing a known campaign in the way they are when a CVE appears in active exploitation lists.But Patch Tuesday starts a different clock. Public patches provide defenders with fixes and attackers with clues. Security researchers and exploit developers can inspect the delta between vulnerable and fixed versions, identify the patched code path, and test whether the bug can be turned into a reliable primitive.
This does not happen instantly for every vulnerability. Modern Windows mitigations are meaningful, and heap-based kernel exploitation is not a trivial exercise. Still, local privilege escalation bugs often move from advisory to proof of concept faster than organizations move from “approved for testing” to “fully deployed.”
That asymmetry is the core patch-management problem. Vendors publish monthly; attackers can specialize; defenders must maintain uptime, compatibility, and change control across messy environments. The right response is not panic, but it is also not complacency.
Why SYSTEM Still Changes Everything
The advisory’s FAQ gives the key outcome in one line: an attacker who successfully exploits the vulnerability could gain SYSTEM privileges. In Windows security, SYSTEM is not merely “admin, but more.” It is the context used by the operating system and many core services, and it generally sits above ordinary administrative users in practical power.With SYSTEM, an attacker can often access sensitive local resources, manipulate services, interfere with endpoint protection, and harvest credentials from places that are unavailable to a standard user. Depending on configuration, they may also gain the leverage needed to move laterally or establish persistence that survives reboots and user logoffs.
This is why local privilege escalation bugs routinely matter in ransomware intrusions. Initial access gets the adversary inside; privilege escalation gives them room to operate. The difference between a contained user compromise and a full host compromise is often the difference between incident cleanup and incident response.
CVE-2026-40407 should therefore be prioritized by consequence, not just entry point. A local-only bug with SYSTEM impact can be more operationally dangerous than a noisier remote flaw with limited post-exploitation value.
Where Administrators Should Put This in the May Queue
Patch priority is never decided by one CVSS score. It is a negotiation between exploitability, exposure, asset value, compensating controls, and operational risk. CVE-2026-40407 belongs high enough in the May queue that it should not wait for the next quarterly maintenance window.Start with systems where a low-privilege foothold is plausible and the prize is high. That includes administrator workstations, jump boxes, developer endpoints, shared servers, VDI hosts, Remote Desktop Session Hosts, and servers running applications with a history of upload, scripting, or service-account exposure. Domain controllers are not affected because they run Windows in some abstract sense; they matter because any local escalation on a high-trust server can have disproportionate blast radius.
For servers, normal staging still makes sense. Microsoft’s recent patch history has reminded administrators that cumulative updates can introduce regressions, especially in complex Active Directory or server-role scenarios. But staging should be measured in days, not weeks, when the vulnerability provides SYSTEM-level escalation and the affected component is broadly present.
For endpoints, broad deployment is usually the better default. The operational risk of a Windows client cumulative update is real, but the security risk of allowing local escalation paths to persist across a large endpoint population is also real. Users generate footholds; attackers look for privilege boundaries to cross.
Mitigations Are Secondary Because the Fix Exists
Microsoft lists an official fix as available. That should settle the remediation hierarchy. When the vendor ships a security update for a local kernel-adjacent heap overflow, the primary mitigation is to install the update.Hardening still matters, but it is not a substitute. Least privilege, application control, attack surface reduction rules, EDR, credential protection, and removal of unnecessary local administrator rights can reduce the likelihood that an attacker reaches the point where this CVE is useful. They do not remove the vulnerable code from affected systems.
The same is true of monitoring. Security teams should watch for suspicious local privilege escalation behavior, abnormal CLFS-related crashes, unexpected service creation, tampering with security products, and post-exploitation patterns. But detection is a backstop, not a remediation plan.
The best defense is boring: patch supported systems, verify fixed builds, and investigate machines that fail to report compliance. For a vulnerability like this, boring is what works.
The Patch Table Tells a Story About Windows Fragmentation
One of the more striking parts of Microsoft’s advisory is the long list of affected product rows. It spans older extended-support server platforms, multiple Windows 10 builds, several Windows 11 generations, Server Core installations, ARM64 devices, and hotpatch-capable releases. That breadth is not unusual for Windows, but it is a useful reminder of why patch management is harder than “apply the update.”Windows estates are layered over years of procurement, application compatibility decisions, hardware refresh cycles, and migration delays. A vulnerability in shared OS plumbing cuts across those layers. The same CVE may require different KBs, different fixed build numbers, and different reboot expectations.
This is where vulnerability management tools can both help and mislead. A scanner that says “CVE-2026-40407 present” is useful, but only if it maps correctly to the edition, build, and servicing channel. A deployment dashboard that says “May update installed” is useful, but only if it includes systems that were offline, paused, excluded, or stuck behind failed prerequisites.
The safest approach is to reconcile three views: Microsoft’s affected-product list, your patch deployment status, and actual endpoint build inventory. Any gap between those views is where this kind of bug lingers.
The CLFS Lesson Microsoft Keeps Relearning
Microsoft has spent years hardening Windows, and modern Windows is significantly more resilient than the platform of a decade ago. Kernel mitigations, driver signing, virtualization-based security, memory protections, and exploit telemetry all raise the bar. Yet CLFS keeps appearing in vulnerability advisories because complex legacy-adjacent system components remain difficult to make permanently bug-free.The move to publish CWE information in advisories helps here. Calling this a heap-based buffer overflow gives defenders and researchers a more precise way to track patterns across Windows components. It also exposes the uncomfortable continuity: memory safety remains a central weakness class in privileged Windows code.
Microsoft’s Secure Future Initiative messaging has leaned heavily on engineering discipline, secure-by-design defaults, and systemic reduction of vulnerability classes. CVE-2026-40407 is the sort of bug that tests whether that program becomes visible in the monthly patch data. One CLFS bug does not disprove a strategy; repeated CLFS bugs over time do raise fair questions about where legacy code, fuzzing coverage, and memory-safe rewrites sit on the priority list.
For customers, that broader debate is interesting but secondary. The vulnerable code is in the field today, the fix is available today, and the risk is borne by administrators who must keep mixed Windows fleets secure while Microsoft continues the longer engineering cleanup.
The May Advisory Rewards Teams That Read Past the Headline
CVE-2026-40407 is easy to underestimate if the only fields you read are “Important,” “Local,” and “Exploitation Unlikely.” It looks less dramatic than a critical remote execution bug and less urgent than an actively exploited zero-day. But the rest of the advisory changes the picture: low complexity, low privileges, no user interaction, confirmed report confidence, high impact, and SYSTEM privileges.That combination makes it a classic second-stage vulnerability. It is not the burglar smashing the front window; it is the master key found once the burglar is inside the building. Enterprises that think in attack chains will patch it accordingly.
The strongest signal may be the plainness of Microsoft’s description. There is no elaborate prerequisite, no special feature dependency, no requirement for the victim to open a file, and no suggestion that only obscure SKUs are affected. It is Windows, it is CLFS, and it is privilege escalation.
That is enough.
The Patch Window Microsoft Just Opened
The useful reading of CVE-2026-40407 is neither alarmist nor dismissive. Microsoft has given defenders a fixed vulnerability before known public exploitation, which is the preferred side of the race. The task now is to use that lead.- CVE-2026-40407 was released on May 12, 2026 and affects a broad set of supported Windows client and server versions.
- Microsoft identifies the flaw as a heap-based buffer overflow in the Windows Common Log File System Driver.
- The vulnerability requires local access with low privileges, low attack complexity, and no user interaction.
- Microsoft says successful exploitation could grant SYSTEM privileges.
- Microsoft reports no public disclosure or known exploitation at original publication and assesses exploitation as unlikely.
- Administrators should prioritize patch verification on high-value endpoints, servers, jump hosts, and systems where a low-privilege foothold would be especially dangerous.
Source: MSRC Security Update Guide - Microsoft Security Response Center