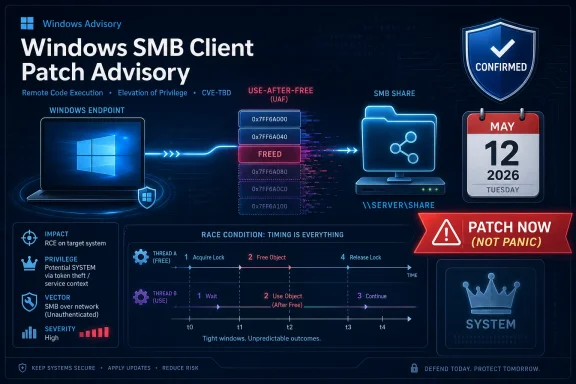
Microsoft published CVE-2026-40410 on May 12, 2026, identifying it as an Important-rated Windows SMB Client elevation-of-privilege flaw caused by use-after-free behavior, with an official fix available across supported Windows client and server releases and no public disclosure or exploitation reported at publication. That makes this a patch-now item, but not a panic item. The uncomfortable part is that Microsoft also marks the report confidence as confirmed, meaning defenders should treat the bug as real even if exploit maturity is still listed as unproven. In other words, this is not the SMB apocalypse; it is a reminder that privilege escalation inside Windows networking code remains one of the more valuable rungs on an attacker’s ladder.
The most important word in Microsoft’s entry is not “SMB,” “SYSTEM,” or even “use after free.” It is “confirmed.” Report confidence is the CVSS temporal metric that tells us whether a vulnerability is merely suspected, reasonably corroborated, or acknowledged with enough technical certainty that defenders should stop debating its existence.
For CVE-2026-40410, Microsoft’s own advisory gives that confidence level as confirmed. That is materially different from the fog that often surrounds early vulnerability chatter, where a crash, a vendor hint, or a third-party write-up can create more heat than light. Here, Microsoft is saying the bug exists, the class of flaw is known, and the patch is the remediation path.
At the same time, Microsoft’s exploitability data is deliberately calmer. The vulnerability was not publicly disclosed when published, Microsoft says it had not been exploited in the wild, and the company rates exploitation as less likely. That does not mean “ignore it.” It means defenders are dealing with a real vulnerability before it has become a known weapon.
That distinction matters because security operations teams live in the gap between certainty and urgency. A confirmed bug with no observed exploitation should move through normal emergency patching processes; it should not be treated like a wormable remote-code-execution crisis. But it also should not be buried under a pile of lower-confidence noise simply because there is not yet a flashy exploit video circulating.
The affected component here is the Windows SMB Client, not the SMB Server. That changes the mental model. A server-side SMB flaw often raises fears about exposed file shares and inbound network access; a client-side flaw suggests the vulnerable code path is exercised when a Windows machine acts as a client in SMB interactions. Microsoft scores the attack vector as local, which keeps this out of the remote-drive-by category.
Still, client-side SMB code is not obscure plumbing. Windows endpoints routinely interact with file servers, domain resources, administrative shares, mapped drives, scripts, deployment infrastructure, and countless legacy workflows that refuse to die. In enterprise networks, “local” does not necessarily mean “irrelevant”; it often means an attacker already has a foothold and is looking for a way to turn a basic user context into something more powerful.
That is why privilege escalation vulnerabilities matter so much in real intrusions. Initial access gets headlines, but escalation decides how far an attacker can go once inside. A bug that can hand SYSTEM privileges to a low-privileged attacker is the difference between nuisance malware and full local control of a Windows host.
The security significance is not that every use-after-free automatically becomes reliable code execution or privilege escalation. Many are hard to exploit, dependent on timing, heap state, race conditions, or environmental details. The significance is that this class of bug sits in the dangerous overlap between memory corruption and privilege boundary crossing.
For CVE-2026-40410, the published details point to a high-complexity attack and a race condition. That should temper expectations of easy weaponization. Race conditions can be fiddly, noisy, and dependent on winning timing windows that vary across hardware, load, configuration, and build.
But “hard” is not the same as “safe.” Attackers have repeatedly shown that complexity is a temporary obstacle when the reward is SYSTEM-level access on a broadly deployed platform. A confirmed high-impact local privilege escalation in Windows networking code is exactly the kind of bug that can graduate from “less likely” to “quietly useful” if researchers or adversaries find a repeatable primitive.
That combination is exactly why CVSS needs interpretation rather than blind sorting. The score is pulled down by local attack vector and high complexity, but the consequences of a successful exploit are severe. Microsoft’s FAQ states that a successful attacker could gain SYSTEM privileges, which is the prize for local Windows exploitation.
SYSTEM is not merely “admin, but more.” It is the operating system’s most privileged local security context, the level at which services, security products, credential-handling components, and core management functions often operate. Once an attacker reaches that level, many endpoint defenses become harder to trust, logs become easier to tamper with, and lateral movement becomes more practical.
For home users, the distinction may feel abstract. For enterprise administrators, it is concrete. A user-level compromise on a workstation is bad; a SYSTEM-level compromise on a workstation that has line-of-business access, cached credentials, VPN connectivity, or management tooling is a different class of incident.
These bugs often live in the frustrating zone between “demonstrably real” and “operationally annoying.” A researcher may be able to reproduce the issue under controlled circumstances, while an attacker may need repeated attempts, process manipulation, environmental shaping, or target-specific tuning to make it reliable enough for real operations.
That is good news, but only to a point. Reliability is a product-development problem for exploit writers. If the target population is large enough and the payoff is high enough, attackers can afford to invest in engineering. Windows SMB Client code is not a niche target surface; it is part of the platform most organizations still organize their working lives around.
The better defender’s reading is therefore narrow: this does not look like an imminent mass-exploitation scenario based on what Microsoft has published. It does look like a legitimate local escalation bug that should be removed before someone improves the exploitability story.
That breadth is part of the administrative burden. This is not a bug you can quarantine to one branch of the Windows estate or one awkward server role. If your environment still contains older supported or extended-support Windows versions, this advisory intersects with them.
The KB mapping also reflects the modern Windows servicing reality. Some releases receive traditional security updates, some include monthly rollups, and newer server and Windows 11 servicing paths may include hotpatch entries alongside regular security updates. The operational question is not “is there a patch?” but “which servicing channel does each device actually follow, and has it received the fixed build?”
For administrators, fixed build numbers are more useful than advisory prose. Windows 10 22H2 is listed with build 19045.7291; Windows 11 23H2 with 22631.7079; Windows 11 24H2 with 26100.8457 or 26100.8390 depending on the update path; Windows Server 2022 with 20348.5139 or 20348.5074; and Windows Server 2025 with 26100.32860 or 26100.32772. Those numbers are the audit trail.
This is where Windows vulnerability management becomes less about any single CVE and more about accumulated drag. Every supported legacy branch carries its own update packaging, reboot constraints, application dependencies, and political baggage. A confirmed SMB Client privilege escalation may be straightforward on a clean Windows 11 fleet and irritating on a mixed environment with old file servers, fragile vendor appliances, and remote offices that still treat reboots as a quarterly event.
The inclusion of Server Core variants also deserves attention. Server Core reduces attack surface by omitting much of the graphical shell, but it does not magically remove networking components that the server still needs. Minimal installation is a good hardening posture; it is not a patching exemption.
For organizations running older releases under extended security arrangements, this advisory should also be a reminder that paying for continued updates does not eliminate operational risk. It simply preserves the ability to receive fixes. Someone still has to deploy them, verify them, and prove that the patched build is actually running.
The vulnerability economy moves quickly after Patch Tuesday. Security researchers diff patches, compare binaries, study changed code paths, and look for the bug class Microsoft hinted at in the advisory. Attackers do the same, especially when the affected component is widely deployed and the reward is privilege escalation rather than a mere denial of service.
A confirmed report-confidence rating gives those researchers a head start of a different kind. They are not guessing whether there is a real bug behind the patch; they know Microsoft fixed one. The public advisory also tells them the component, the weakness class, the impact, and that a race condition is involved.
That does not mean a public exploit is inevitable. But the lifecycle of many Windows local privilege-escalation bugs is predictable enough: quiet publication, patch diffing, proof-of-concept attempts, security-tool detections, and eventually some incorporation into opportunistic or targeted post-exploitation chains. The fact that exploitation was “less likely” on May 12, 2026 does not answer what the threat picture will look like after administrators have had weeks or months to delay patching.
That makes CVE-2026-40410 part of a chained-risk model. On its own, it is not described as remotely exploitable over the network. In a chain, it could turn a constrained foothold into SYSTEM, after which credential access, persistence, defense evasion, and lateral movement become more plausible. This is why mature defenders prioritize privilege-escalation bugs even when help-desk metrics are screaming about more visible issues.
Endpoint detection and response tools may reduce the risk, but they are not a substitute for the patch. Memory-corruption exploitation and race-condition behavior can be difficult to distinguish from legitimate system activity, especially inside core Windows components. Once SYSTEM is obtained, the defender’s telemetry assumptions become more fragile.
The practical stance is to treat the fix as the control and monitoring as the backstop. Look for unusual SMB client activity, unexpected service creation, abnormal privilege transitions, suspicious child processes from networking-adjacent services, and endpoint behavior that suggests repeated exploitation attempts. But do not ask detection to carry a burden that patching can remove.
CVE-2026-40410 should rank above routine low-impact bugs because the successful outcome is SYSTEM privileges and Microsoft confirms the vulnerability. It should rank below actively exploited remote-code-execution vulnerabilities because Microsoft says it was not exploited or publicly disclosed at release and rates exploitation as less likely. That is the middle tier where governance discipline matters.
Organizations with aggressive patch windows should include this in the standard May deployment wave. Organizations with slower rings should make sure this does not get trapped behind feature-update politics, application testing delays, or the assumption that SMB client issues matter only to file servers. Workstations are the obvious concern, but administrative jump boxes, Remote Desktop hosts, and management servers deserve special scrutiny.
There is also a compliance angle. Because Microsoft marks customer action as required across affected rows, this is not a documentation-only advisory. The remediation path is an official security update, and the absence of exploitation does not make the vulnerability optional under most internal patch policies.
But CVE-2026-40410 is a Windows SMB Client local privilege-escalation vulnerability, and that limits the value of network-only thinking. Blocking random outbound SMB to the internet is still wise. Segmenting networks is still wise. Ensuring SMB signing and modern authentication posture is still wise. None of that should be misread as equivalent to fixing a use-after-free in the client code.
The right approach is layered. Patch first, then use SMB hardening to reduce the usefulness of future bugs and the attacker’s ability to coerce or abuse Windows machines in broader chains. In mature environments, protocol hardening is not a reaction to one CVE; it is baseline hygiene.
Home and small-business users should avoid overcomplicating the response. If Windows Update installs the May 2026 cumulative update successfully, the most important action is already done. The people who need deeper SMB policy review are the ones running domain environments, file servers, legacy line-of-business applications, or fleet management systems that depend on SMB in ways nobody has documented in years.
Security teams often overreact to exploit availability and underreact to confirmed but quiet vulnerabilities. That bias is understandable: exploited bugs create incidents, dashboards, tickets, and executive attention. But confirmed vulnerabilities with official fixes are exactly what patch management exists to eliminate before they become exploited bugs.
CVE-2026-40410’s temporal metrics tell a balanced story. Exploit code maturity is unproven. Remediation level is official fix. Report confidence is confirmed. The rational response is not fear; it is execution.
That execution includes verifying deployment by build number, not by assumption. It includes checking that devices outside the corporate network are still receiving updates. It includes making sure servers using hotpatch channels are actually on the fixed hotpatch or cumulative build. And it includes remembering that “less likely” is not the same as “not worth patching.”
That combination should put it in the first serious patch wave after any actively exploited or remotely exploitable critical issues. If an organization patches only the loudest vulnerabilities, this is the kind of bug that lingers until a future incident report asks why a known SYSTEM escalation remained available. If an organization patches everything blindly, it may miss the opportunity to explain why this one deserves timely validation.
Microsoft’s advisory also arrives at a time when Windows servicing is increasingly fragmented by release cadence, hotpatch availability, and mixed client-server estates. The patch may be “one Patch Tuesday” in public communication, but in production it is many deployment paths. The risk is not that Microsoft failed to provide a fix; the risk is that administrators assume the fix reached systems it never touched.
For WindowsForum readers, the deeper story is familiar. Windows security in 2026 is not defined only by zero-days and spectacular remote exploits. It is defined by hundreds of smaller trust-boundary failures, memory-safety defects, and privilege-escalation opportunities that attackers assemble into campaigns. CVE-2026-40410 is one piece of that puzzle, and its quietness should not be mistaken for irrelevance.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft Confirms the Bug, Even as the Exploit Story Stays Quiet
Microsoft Confirms the Bug, Even as the Exploit Story Stays Quiet
The most important word in Microsoft’s entry is not “SMB,” “SYSTEM,” or even “use after free.” It is “confirmed.” Report confidence is the CVSS temporal metric that tells us whether a vulnerability is merely suspected, reasonably corroborated, or acknowledged with enough technical certainty that defenders should stop debating its existence.For CVE-2026-40410, Microsoft’s own advisory gives that confidence level as confirmed. That is materially different from the fog that often surrounds early vulnerability chatter, where a crash, a vendor hint, or a third-party write-up can create more heat than light. Here, Microsoft is saying the bug exists, the class of flaw is known, and the patch is the remediation path.
At the same time, Microsoft’s exploitability data is deliberately calmer. The vulnerability was not publicly disclosed when published, Microsoft says it had not been exploited in the wild, and the company rates exploitation as less likely. That does not mean “ignore it.” It means defenders are dealing with a real vulnerability before it has become a known weapon.
That distinction matters because security operations teams live in the gap between certainty and urgency. A confirmed bug with no observed exploitation should move through normal emergency patching processes; it should not be treated like a wormable remote-code-execution crisis. But it also should not be buried under a pile of lower-confidence noise simply because there is not yet a flashy exploit video circulating.
The SMB Client Is the Less Glamorous Half of a Very Dangerous Story
SMB vulnerabilities carry an outsized cultural weight in Windows security because the protocol sits near the center of file sharing, authentication workflows, administrative tooling, and enterprise muscle memory. For many readers, “SMB bug” still evokes the ghosts of major wormable incidents and lateral-movement campaigns. CVE-2026-40410 is not that kind of published vulnerability, but the association is not irrational.The affected component here is the Windows SMB Client, not the SMB Server. That changes the mental model. A server-side SMB flaw often raises fears about exposed file shares and inbound network access; a client-side flaw suggests the vulnerable code path is exercised when a Windows machine acts as a client in SMB interactions. Microsoft scores the attack vector as local, which keeps this out of the remote-drive-by category.
Still, client-side SMB code is not obscure plumbing. Windows endpoints routinely interact with file servers, domain resources, administrative shares, mapped drives, scripts, deployment infrastructure, and countless legacy workflows that refuse to die. In enterprise networks, “local” does not necessarily mean “irrelevant”; it often means an attacker already has a foothold and is looking for a way to turn a basic user context into something more powerful.
That is why privilege escalation vulnerabilities matter so much in real intrusions. Initial access gets headlines, but escalation decides how far an attacker can go once inside. A bug that can hand SYSTEM privileges to a low-privileged attacker is the difference between nuisance malware and full local control of a Windows host.
A Use-After-Free in 2026 Is Boring Only Until It Is Yours
Microsoft describes the root weakness as CWE-416, use after free. That label is familiar enough to sound generic, but it remains one of the enduring failure modes in systems software. In plain terms, software continues using memory after it has already been released, creating the possibility that an attacker can influence what occupies that memory when it is referenced again.The security significance is not that every use-after-free automatically becomes reliable code execution or privilege escalation. Many are hard to exploit, dependent on timing, heap state, race conditions, or environmental details. The significance is that this class of bug sits in the dangerous overlap between memory corruption and privilege boundary crossing.
For CVE-2026-40410, the published details point to a high-complexity attack and a race condition. That should temper expectations of easy weaponization. Race conditions can be fiddly, noisy, and dependent on winning timing windows that vary across hardware, load, configuration, and build.
But “hard” is not the same as “safe.” Attackers have repeatedly shown that complexity is a temporary obstacle when the reward is SYSTEM-level access on a broadly deployed platform. A confirmed high-impact local privilege escalation in Windows networking code is exactly the kind of bug that can graduate from “less likely” to “quietly useful” if researchers or adversaries find a repeatable primitive.
The CVSS Score Is Moderate; the Impact Is Not
Microsoft gives CVE-2026-40410 a CVSS 3.1 base score of 7.0, with a temporal score of 6.1. On paper, that lands in territory many organizations classify as high but not catastrophic. The vector explains the compromise: local attack vector, high attack complexity, low privileges required, no user interaction, unchanged scope, and high impact to confidentiality, integrity, and availability.That combination is exactly why CVSS needs interpretation rather than blind sorting. The score is pulled down by local attack vector and high complexity, but the consequences of a successful exploit are severe. Microsoft’s FAQ states that a successful attacker could gain SYSTEM privileges, which is the prize for local Windows exploitation.
SYSTEM is not merely “admin, but more.” It is the operating system’s most privileged local security context, the level at which services, security products, credential-handling components, and core management functions often operate. Once an attacker reaches that level, many endpoint defenses become harder to trust, logs become easier to tamper with, and lateral movement becomes more practical.
For home users, the distinction may feel abstract. For enterprise administrators, it is concrete. A user-level compromise on a workstation is bad; a SYSTEM-level compromise on a workstation that has line-of-business access, cached credentials, VPN connectivity, or management tooling is a different class of incident.
The Race Condition Detail Explains Microsoft’s Restraint
Microsoft’s note that exploitation requires winning a race condition is one of the few pieces of technical texture in the advisory. It explains the high attack complexity rating and the “exploitation less likely” assessment. A race condition is an exploitation contest against timing, where the attacker must cause operations to occur in a particular order before the software’s state changes.These bugs often live in the frustrating zone between “demonstrably real” and “operationally annoying.” A researcher may be able to reproduce the issue under controlled circumstances, while an attacker may need repeated attempts, process manipulation, environmental shaping, or target-specific tuning to make it reliable enough for real operations.
That is good news, but only to a point. Reliability is a product-development problem for exploit writers. If the target population is large enough and the payoff is high enough, attackers can afford to invest in engineering. Windows SMB Client code is not a niche target surface; it is part of the platform most organizations still organize their working lives around.
The better defender’s reading is therefore narrow: this does not look like an imminent mass-exploitation scenario based on what Microsoft has published. It does look like a legitimate local escalation bug that should be removed before someone improves the exploitability story.
Patch Tuesday Turns a Local Bug Into a Fleet Problem
CVE-2026-40410 arrived as part of Microsoft’s May 12, 2026 security update cycle, and the affected-product list is broad in the way Windows administrators have come to expect. The advisory includes Windows 10 21H2 and 22H2, Windows 11 23H2, 24H2, 25H2, and 26H1 entries, along with Windows Server 2012 R2, 2016, 2019, 2022, 2022 23H2, and 2025 variants. Some Server Core installations are listed separately, which matters for organizations that track exposure by installation type rather than product name alone.That breadth is part of the administrative burden. This is not a bug you can quarantine to one branch of the Windows estate or one awkward server role. If your environment still contains older supported or extended-support Windows versions, this advisory intersects with them.
The KB mapping also reflects the modern Windows servicing reality. Some releases receive traditional security updates, some include monthly rollups, and newer server and Windows 11 servicing paths may include hotpatch entries alongside regular security updates. The operational question is not “is there a patch?” but “which servicing channel does each device actually follow, and has it received the fixed build?”
For administrators, fixed build numbers are more useful than advisory prose. Windows 10 22H2 is listed with build 19045.7291; Windows 11 23H2 with 22631.7079; Windows 11 24H2 with 26100.8457 or 26100.8390 depending on the update path; Windows Server 2022 with 20348.5139 or 20348.5074; and Windows Server 2025 with 26100.32860 or 26100.32772. Those numbers are the audit trail.
Older Windows Versions Keep Making New Risk Feel Familiar
One of the striking aspects of this advisory is how much old Windows still appears in a 2026 vulnerability story. Windows Server 2012 R2 and Windows 10 1607 are not exactly the face of modern computing, but they remain present in real environments through long support tails, specialized workloads, embedded systems, and institutional inertia. Attackers do not care whether a system feels old to the IT department; they care whether it is reachable, valuable, and underpatched.This is where Windows vulnerability management becomes less about any single CVE and more about accumulated drag. Every supported legacy branch carries its own update packaging, reboot constraints, application dependencies, and political baggage. A confirmed SMB Client privilege escalation may be straightforward on a clean Windows 11 fleet and irritating on a mixed environment with old file servers, fragile vendor appliances, and remote offices that still treat reboots as a quarterly event.
The inclusion of Server Core variants also deserves attention. Server Core reduces attack surface by omitting much of the graphical shell, but it does not magically remove networking components that the server still needs. Minimal installation is a good hardening posture; it is not a patching exemption.
For organizations running older releases under extended security arrangements, this advisory should also be a reminder that paying for continued updates does not eliminate operational risk. It simply preserves the ability to receive fixes. Someone still has to deploy them, verify them, and prove that the patched build is actually running.
“Not Exploited” Is a Snapshot, Not a Warranty
Microsoft’s publication-time status says CVE-2026-40410 was not publicly disclosed and not exploited. That is valuable intelligence, and it should shape prioritization. It should not become a lullaby.The vulnerability economy moves quickly after Patch Tuesday. Security researchers diff patches, compare binaries, study changed code paths, and look for the bug class Microsoft hinted at in the advisory. Attackers do the same, especially when the affected component is widely deployed and the reward is privilege escalation rather than a mere denial of service.
A confirmed report-confidence rating gives those researchers a head start of a different kind. They are not guessing whether there is a real bug behind the patch; they know Microsoft fixed one. The public advisory also tells them the component, the weakness class, the impact, and that a race condition is involved.
That does not mean a public exploit is inevitable. But the lifecycle of many Windows local privilege-escalation bugs is predictable enough: quiet publication, patch diffing, proof-of-concept attempts, security-tool detections, and eventually some incorporation into opportunistic or targeted post-exploitation chains. The fact that exploitation was “less likely” on May 12, 2026 does not answer what the threat picture will look like after administrators have had weeks or months to delay patching.
Where Endpoint Security Has to Assume Partial Failure
Local elevation-of-privilege vulnerabilities expose an awkward truth about endpoint security. They matter most after something else has already gone wrong. A phishing payload, malicious document, browser exploit, stolen credentials, rogue insider, or compromised software update may provide the initial low-privileged context; the escalation bug determines what happens next.That makes CVE-2026-40410 part of a chained-risk model. On its own, it is not described as remotely exploitable over the network. In a chain, it could turn a constrained foothold into SYSTEM, after which credential access, persistence, defense evasion, and lateral movement become more plausible. This is why mature defenders prioritize privilege-escalation bugs even when help-desk metrics are screaming about more visible issues.
Endpoint detection and response tools may reduce the risk, but they are not a substitute for the patch. Memory-corruption exploitation and race-condition behavior can be difficult to distinguish from legitimate system activity, especially inside core Windows components. Once SYSTEM is obtained, the defender’s telemetry assumptions become more fragile.
The practical stance is to treat the fix as the control and monitoring as the backstop. Look for unusual SMB client activity, unexpected service creation, abnormal privilege transitions, suspicious child processes from networking-adjacent services, and endpoint behavior that suggests repeated exploitation attempts. But do not ask detection to carry a burden that patching can remove.
The Real Audience Is the Patch Governance Team
For individual Windows users, the advice is simple: install the May 2026 security updates and keep automatic updates enabled. For businesses, the hard part is not understanding the advisory. It is turning advisory intelligence into a defensible patch decision across a messy estate.CVE-2026-40410 should rank above routine low-impact bugs because the successful outcome is SYSTEM privileges and Microsoft confirms the vulnerability. It should rank below actively exploited remote-code-execution vulnerabilities because Microsoft says it was not exploited or publicly disclosed at release and rates exploitation as less likely. That is the middle tier where governance discipline matters.
Organizations with aggressive patch windows should include this in the standard May deployment wave. Organizations with slower rings should make sure this does not get trapped behind feature-update politics, application testing delays, or the assumption that SMB client issues matter only to file servers. Workstations are the obvious concern, but administrative jump boxes, Remote Desktop hosts, and management servers deserve special scrutiny.
There is also a compliance angle. Because Microsoft marks customer action as required across affected rows, this is not a documentation-only advisory. The remediation path is an official security update, and the absence of exploitation does not make the vulnerability optional under most internal patch policies.
SMB Hardening Still Helps, But It Does Not Replace the Fix
It is tempting to reach for SMB hardening advice whenever an SMB vulnerability appears, and much of that advice remains sound. Disable obsolete SMB versions where possible, restrict outbound and inbound SMB to trusted networks, monitor unexpected SMB traffic, and reduce unnecessary file-sharing exposure. Those steps reduce blast radius across many scenarios.But CVE-2026-40410 is a Windows SMB Client local privilege-escalation vulnerability, and that limits the value of network-only thinking. Blocking random outbound SMB to the internet is still wise. Segmenting networks is still wise. Ensuring SMB signing and modern authentication posture is still wise. None of that should be misread as equivalent to fixing a use-after-free in the client code.
The right approach is layered. Patch first, then use SMB hardening to reduce the usefulness of future bugs and the attacker’s ability to coerce or abuse Windows machines in broader chains. In mature environments, protocol hardening is not a reaction to one CVE; it is baseline hygiene.
Home and small-business users should avoid overcomplicating the response. If Windows Update installs the May 2026 cumulative update successfully, the most important action is already done. The people who need deeper SMB policy review are the ones running domain environments, file servers, legacy line-of-business applications, or fleet management systems that depend on SMB in ways nobody has documented in years.
The Confidence Metric Is a Warning About Defender Psychology
The user-supplied MSRC text about report confidence is easy to skim past because it reads like CVSS boilerplate. In this case, it is the conceptual center of the advisory. Microsoft is distinguishing between exploit maturity and certainty of existence, and defenders should do the same.Security teams often overreact to exploit availability and underreact to confirmed but quiet vulnerabilities. That bias is understandable: exploited bugs create incidents, dashboards, tickets, and executive attention. But confirmed vulnerabilities with official fixes are exactly what patch management exists to eliminate before they become exploited bugs.
CVE-2026-40410’s temporal metrics tell a balanced story. Exploit code maturity is unproven. Remediation level is official fix. Report confidence is confirmed. The rational response is not fear; it is execution.
That execution includes verifying deployment by build number, not by assumption. It includes checking that devices outside the corporate network are still receiving updates. It includes making sure servers using hotpatch channels are actually on the fixed hotpatch or cumulative build. And it includes remembering that “less likely” is not the same as “not worth patching.”
The May SMB Client Fix Belongs in the Middle of the Queue, Not the Bottom
CVE-2026-40410 is the kind of vulnerability that tests whether an organization has a real risk-based patch program or merely a severity-sorting spreadsheet. It is Important, not Critical. It is local, not remote. It is high complexity, not low complexity. But it is confirmed, broadly applicable, officially fixed, and capable of yielding SYSTEM privileges.That combination should put it in the first serious patch wave after any actively exploited or remotely exploitable critical issues. If an organization patches only the loudest vulnerabilities, this is the kind of bug that lingers until a future incident report asks why a known SYSTEM escalation remained available. If an organization patches everything blindly, it may miss the opportunity to explain why this one deserves timely validation.
Microsoft’s advisory also arrives at a time when Windows servicing is increasingly fragmented by release cadence, hotpatch availability, and mixed client-server estates. The patch may be “one Patch Tuesday” in public communication, but in production it is many deployment paths. The risk is not that Microsoft failed to provide a fix; the risk is that administrators assume the fix reached systems it never touched.
For WindowsForum readers, the deeper story is familiar. Windows security in 2026 is not defined only by zero-days and spectacular remote exploits. It is defined by hundreds of smaller trust-boundary failures, memory-safety defects, and privilege-escalation opportunities that attackers assemble into campaigns. CVE-2026-40410 is one piece of that puzzle, and its quietness should not be mistaken for irrelevance.
What the May 12 SMB Client Advisory Really Demands
The practical reading is straightforward: treat CVE-2026-40410 as a confirmed Windows privilege-escalation bug with official fixes available, but do not confuse it with an actively exploited emergency. That makes it a disciplined patch-management story rather than a breaking-glass incident.- Microsoft published CVE-2026-40410 on May 12, 2026 as an Important Windows SMB Client elevation-of-privilege vulnerability.
- The bug is a use-after-free issue, and Microsoft says successful exploitation requires winning a race condition.
- The CVSS 3.1 base score is 7.0, but successful exploitation could grant SYSTEM privileges.
- Microsoft reported no public disclosure and no in-the-wild exploitation at the time of publication.
- The report confidence is confirmed, and the remediation level is official fix, so administrators should verify patched builds rather than wait for exploit chatter.
- The affected list spans Windows 10, Windows 11, and multiple Windows Server generations, including Server Core and hotpatch-serviced configurations.
Source: MSRC Security Update Guide - Microsoft Security Response Center