Microsoft disclosed CVE-2026-40415, a Windows TCP/IP remote code execution vulnerability, in its Security Update Guide on May 12, 2026, framing the issue as a network-stack flaw whose risk depends not only on severity but on how confidently defenders can trust the available technical details.
That distinction matters. A scary CVE title can make every Windows admin reach for the emergency-change lever, but Microsoft’s own framing points to a more disciplined question: how much is actually known, how much is inferred, and how quickly should organizations move when the vulnerable component is the operating system’s TCP/IP stack?
Remote code execution is the phrase that gets attention, but Windows TCP/IP is the part that should keep infrastructure teams focused. Application-layer bugs can often be boxed in by disabling a feature, blocking a URL path, or removing an exposed service. A flaw in the network stack lives closer to the floorboards.
That does not automatically make CVE-2026-40415 wormable, universally exploitable, or already weaponized. Those are separate claims, and they require separate evidence. But it does mean the blast-radius conversation begins earlier than it would for a bug in a desktop app or optional component.
The TCP/IP stack is not a boutique feature. It is the shared path through which domain controllers, file servers, jump boxes, developer workstations, laptops, VDI hosts, and cloud-based Windows workloads all communicate. When Microsoft labels a vulnerability in that layer as remote code execution, the default enterprise stance should be urgency with verification, not panic by headline.
That is especially true because many Windows estates are mixed environments. A single vulnerability page can cover client and server SKUs, supported builds with different patch baselines, and machines with very different exposure profiles. The right response is not “patch everything blindly this minute” or “wait until someone publishes exploit code.” It is to identify where TCP/IP exposure intersects with business-critical Windows roles and move those systems to the front of the queue.
That is not the same as severity. A vulnerability can be severe but poorly understood, or well understood but difficult to exploit. Report confidence tries to answer a different operational question: are defenders looking at a confirmed defect with reliable contours, or at a thinner disclosure where the details may still be evolving?
For a Windows TCP/IP RCE, that difference is not academic. If confidence is high, security teams can justify faster change windows, stronger compensating controls, and more aggressive exception handling because the vendor’s acknowledgement and technical record carry weight. If confidence is lower, teams still act, but they should be more careful about building elaborate detection logic or exposure assumptions on details that may shift.
This is where Microsoft’s role matters. MSRC disclosures are not anonymous rumors, and a CVE entry in Microsoft’s guide is itself a meaningful signal. But even with vendor acknowledgement, the public record can vary from rich technical description to deliberately sparse language designed to protect customers while patches propagate.
The result is an uncomfortable but familiar Patch Tuesday reality: the people who most need precision are often asked to move before precision is available. That is not a failure of disclosure so much as a consequence of defending a mass-market operating system. If the bug is serious enough, the patch has to arrive before the full exploit narrative does.
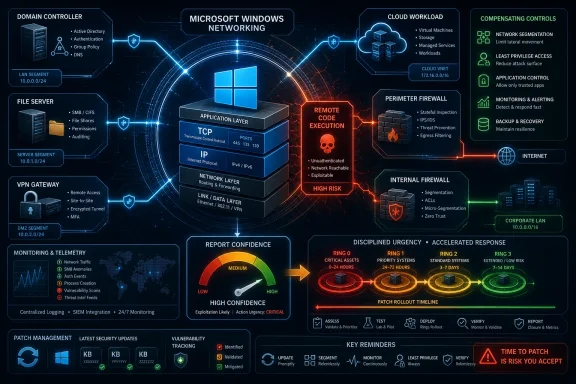
The first-order question is not only “which machines are missing the update?” It is “which machines can receive the kind of traffic that would make this bug reachable?” That pulls network segmentation, firewall policy, IPv4 and IPv6 posture, VPN exposure, and host-based filtering back into the conversation.
This is where many organizations discover that their asset inventory is less useful than they hoped. Knowing that a machine is “Windows Server 2022” is not the same as knowing whether it is internet-facing, reachable from guest Wi-Fi, exposed across site-to-site VPN tunnels, or sitting in a flat VLAN with legacy systems that cannot be patched quickly.
The practical response should begin with role and reachability. Domain controllers, edge-adjacent servers, remote access infrastructure, Hyper-V hosts, management servers, and file servers deserve faster attention than lightly used lab machines. That prioritization is not an excuse to leave the rest unpatched; it is how mature teams spend the first 24 to 72 hours when everything cannot move at once.
There is also a home-user version of this story. Consumer Windows PCs behind a NAT router are not in the same exposure category as public Windows servers, but they still process network traffic and still benefit from timely cumulative updates. The difference is not whether to patch; it is whether the update is an emergency maintenance event or a same-day normal update.
That tension is why Microsoft often keeps protocol-level RCE disclosures relatively restrained at first. The company may identify the affected component, impact, severity, exploitability assessment, and update path without spelling out the exact parsing condition or packet structure. For defenders, that can feel like trying to prioritize a fire alarm without being told which floor is burning.
The frustration is legitimate. A Windows admin responsible for thousands of systems needs more than a CVE title to decide whether to accelerate a change freeze, wake a network team, or isolate a fragile segment. A SOC analyst needs indicators that are more concrete than “watch for suspicious traffic.”
But the alternative can be worse. Overly detailed early advisories can become exploit-development briefs. In the case of network-stack flaws, the line between actionable defender guidance and attacker enablement is especially thin, because the vulnerability may be reachable before authentication and before application logs ever see anything.
The mature reading of CVE-2026-40415 is therefore cautious. Treat the vendor-confirmed existence of the vulnerability as enough to patch. Treat any highly specific exploit claims circulating outside Microsoft’s advisory as unproven unless corroborated by credible researchers, working exploit demonstrations, or observed exploitation reports.
Not every Windows RCE belongs in that lineage. The industry has a bad habit of calling anything network-adjacent “wormable” before the evidence supports it. That word should be used carefully, because it implies autonomous propagation, broad reachability, and exploit reliability across enough machines to create self-sustaining spread.
Still, the anxiety is rational. TCP/IP is the layer beneath the services that admins usually harden. If a vulnerability can be triggered by crafted packets before a request reaches IIS, SMB, RDP, or a line-of-business listener, then traditional service-level mitigations may not be enough.
That does not mean defenders are powerless. Host firewalls, perimeter filtering, segmentation, VPN scoping, IPv6 hygiene, endpoint detection telemetry, and rapid cumulative update deployment all matter. The key is to avoid the comforting fiction that “we do not run that application” is relevant when the affected component is the Windows networking stack itself.
This is also why Patch Tuesday fatigue is dangerous. Microsoft ships so many security fixes that even serious issues can blur into the monthly spreadsheet. CVE-2026-40415 deserves to be separated from the routine backlog because its affected layer changes the operational calculus.
Cumulative updates touch more than the named vulnerability. They include security fixes, quality changes, servicing-stack interactions, and sometimes regressions that only appear in certain domain, storage, printing, VPN, or application-control configurations. The more critical the server, the more likely the organization has a memory of a previous patch that broke something important.
That is why patching a TCP/IP RCE becomes a risk-balancing exercise rather than a slogan. Waiting too long increases exposure to exploit development. Moving without testing can damage availability. The job is not to pretend one risk does not exist; it is to compress testing, deploy in rings, monitor carefully, and keep rollback plans realistic.
Enterprises should avoid the two worst patterns. The first is “all at once everywhere,” which maximizes blast radius if the update misbehaves. The second is “pilot forever,” which leaves high-value systems exposed while low-risk endpoints soak for a week. A better model is accelerated rings: representative test systems first, exposed and high-value servers next, then the broader fleet.
For smaller organizations without formal rings, the guidance is less elegant but still clear. Patch a small number of representative machines, watch for obvious failures, confirm line-of-business connectivity, and then move. The absence of a perfect test lab should not become a reason to leave a network-stack RCE unaddressed.
A Windows server that is not directly exposed to the internet may still be reachable from partner VPNs, remote users, compromised laptops, guest networks, cloud peering links, or unmanaged operational-technology segments. A workstation behind NAT may still be exposed to malicious traffic on public Wi-Fi or hostile local networks. A server protected by a perimeter firewall may still accept traffic from a broad internal address range where attacker dwell time is the real concern.
That means compensating controls should be layered while patches roll out. Host-based firewalls can reduce unnecessary inbound reachability. Network ACLs can narrow who can talk to sensitive Windows roles. IDS and network telemetry can be tuned for unusual packet patterns, scanning behavior, or sudden crashes in networking components, even when exact exploit signatures are unavailable.
Administrators should also revisit IPv6 assumptions. Many Windows environments have IPv6 enabled by default, partially configured, poorly monitored, or ignored because “we do not use it.” That posture has caused trouble before. Disabling IPv6 casually is not Microsoft’s preferred broad fix and can break Windows features, but pretending it is absent because the IPv4 plan is documented is equally dangerous.
The right IPv6 question is not ideological. It is whether the organization knows where IPv6 is enabled, where it is routed, what firewalls apply, and whether monitoring sees it. A TCP/IP vulnerability is a good moment to find out.
The first useful signals may not be packet-perfect exploit signatures. They may be scans against unusual protocol surfaces, repeated connection attempts, kernel crash telemetry, unexpected service interruptions, or endpoint alerts around abnormal system behavior after inbound network traffic. None of those alone proves exploitation, but together they can steer investigation.
EDR tools also have a visibility problem here. Remote code execution in a kernel-adjacent or networking component may not look like a familiar user-mode exploit chain at first. By the time a payload spawns a process, the most interesting part of the exploit may already have happened.
That does not make detection futile. It makes patch status, exposure mapping, and telemetry correlation more important than waiting for a perfect rule. If an organization cannot say which systems are patched and which are reachable, no Sigma rule will save the incident bridge from guesswork.
For WindowsForum readers running home labs, small businesses, or MSP environments, this is a good reminder to keep logs boring before the emergency. Centralized Windows event collection, firewall logging, router telemetry, and basic asset tagging are not glamorous. They are the difference between “we saw something odd” and “we have no idea where to look.”
That does not mean secrecy is better. Security through obscurity has a poor record, and defenders cannot patch what vendors do not disclose. But it does mean the period immediately after disclosure is asymmetric. Attackers can focus on one bug; defenders must patch thousands of machines without breaking payroll, identity, remote access, or clinical systems.
The metric also helps explain why “known exploited” status is not the only thing that matters. By the time a vulnerability appears in exploitation catalogs, opportunistic scanning may already be underway. For network-stack RCEs, waiting for confirmed exploitation can be a losing strategy because the window between proof-of-concept and weaponization may be short.
At the same time, administrators should resist social-media certainty. A CVE number plus a dramatic exploit name does not make a campaign real. Unless Microsoft, CISA, a reputable security vendor, or credible independent researchers confirm exploitation details, treat sensational claims as leads to investigate rather than facts to repeat.
This is the narrow path good security teams walk every month. Move quickly because the vendor-confirmed risk is real. Speak carefully because the unconfirmed details may not be.
That matters because network-stack vulnerabilities punish forgotten machines. A retired laptop in a closet is not much of a risk if it never powers on. A Windows 10 workstation running a legacy scanner, kiosk, lab instrument, or warehouse app is different. If it remains connected and unpatched, it becomes part of the attack surface whether or not anyone thinks of it as production.
Server lifecycle issues are equally important. Old Windows Server builds often survive because the application owner left, the vendor disappeared, or the replacement project keeps slipping. Those systems are exactly where emergency patching is most difficult and compensating controls matter most.
The lesson is not that every organization can modernize overnight. It is that unsupported or hard-to-patch Windows nodes need to be treated as exceptions with documented network restrictions, monitoring, and business ownership. A TCP/IP RCE is a poor time to discover that “temporary” meant “since 2017.”
For home users, the advice is simpler. If the machine still receives security updates, install them. If it does not, stop treating it as a safe daily driver on a modern network.
That combined view is what turns vulnerability management from reporting into defense. A flat list of unpatched devices does not tell you which server should be patched first. A network map without patch state does not tell you which paths matter most. The two datasets have to meet.
MSPs face a version of this problem at scale. One customer may have disciplined update rings and clean inventory; another may have unmanaged servers, vendor appliances, and executives who only remember patching when something breaks. A Windows TCP/IP RCE is precisely the kind of advisory that forces providers to standardize their escalation language.
The best message to stakeholders is concrete and boring: this is a Microsoft-confirmed remote code execution vulnerability in a core Windows networking component; we are prioritizing reachable and high-value systems; we are deploying the vendor update through accelerated rings; and we are applying temporary network restrictions where patching cannot be immediate.
That message avoids both underreaction and theater. It does not promise that the sky is falling. It does not pretend the monthly update queue is business as usual.
Microsoft’s disclosure gives defenders enough to act, but not enough to become complacent. That is the uncomfortable middle ground of modern Windows security: patch quickly, verify carefully, distrust sensational certainty, and use each network-stack vulnerability as another reason to make the next one less chaotic.
Source: MSRC Security Update Guide - Microsoft Security Response Center
That distinction matters. A scary CVE title can make every Windows admin reach for the emergency-change lever, but Microsoft’s own framing points to a more disciplined question: how much is actually known, how much is inferred, and how quickly should organizations move when the vulnerable component is the operating system’s TCP/IP stack?
 The Dangerous Part Is Not the Acronym, It Is the Layer
The Dangerous Part Is Not the Acronym, It Is the Layer
Remote code execution is the phrase that gets attention, but Windows TCP/IP is the part that should keep infrastructure teams focused. Application-layer bugs can often be boxed in by disabling a feature, blocking a URL path, or removing an exposed service. A flaw in the network stack lives closer to the floorboards.That does not automatically make CVE-2026-40415 wormable, universally exploitable, or already weaponized. Those are separate claims, and they require separate evidence. But it does mean the blast-radius conversation begins earlier than it would for a bug in a desktop app or optional component.
The TCP/IP stack is not a boutique feature. It is the shared path through which domain controllers, file servers, jump boxes, developer workstations, laptops, VDI hosts, and cloud-based Windows workloads all communicate. When Microsoft labels a vulnerability in that layer as remote code execution, the default enterprise stance should be urgency with verification, not panic by headline.
That is especially true because many Windows estates are mixed environments. A single vulnerability page can cover client and server SKUs, supported builds with different patch baselines, and machines with very different exposure profiles. The right response is not “patch everything blindly this minute” or “wait until someone publishes exploit code.” It is to identify where TCP/IP exposure intersects with business-critical Windows roles and move those systems to the front of the queue.
Report Confidence Is the Quiet Metric That Changes the Room
The text attached to this CVE highlights a metric that many patch dashboards flatten into background noise: report confidence. In plain English, it measures how certain the vendor and vulnerability ecosystem are that the bug exists and that the public technical details are credible.That is not the same as severity. A vulnerability can be severe but poorly understood, or well understood but difficult to exploit. Report confidence tries to answer a different operational question: are defenders looking at a confirmed defect with reliable contours, or at a thinner disclosure where the details may still be evolving?
For a Windows TCP/IP RCE, that difference is not academic. If confidence is high, security teams can justify faster change windows, stronger compensating controls, and more aggressive exception handling because the vendor’s acknowledgement and technical record carry weight. If confidence is lower, teams still act, but they should be more careful about building elaborate detection logic or exposure assumptions on details that may shift.
This is where Microsoft’s role matters. MSRC disclosures are not anonymous rumors, and a CVE entry in Microsoft’s guide is itself a meaningful signal. But even with vendor acknowledgement, the public record can vary from rich technical description to deliberately sparse language designed to protect customers while patches propagate.
The result is an uncomfortable but familiar Patch Tuesday reality: the people who most need precision are often asked to move before precision is available. That is not a failure of disclosure so much as a consequence of defending a mass-market operating system. If the bug is serious enough, the patch has to arrive before the full exploit narrative does.
A TCP/IP RCE Forces Admins to Think Like Network Engineers Again
For years, Windows patch management has become increasingly SaaS-like in its rhythm. Updates arrive, rings absorb them, telemetry catches regressions, and endpoint management tools turn patching into a compliance graph. A TCP/IP remote code execution vulnerability cuts through that abstraction.The first-order question is not only “which machines are missing the update?” It is “which machines can receive the kind of traffic that would make this bug reachable?” That pulls network segmentation, firewall policy, IPv4 and IPv6 posture, VPN exposure, and host-based filtering back into the conversation.
This is where many organizations discover that their asset inventory is less useful than they hoped. Knowing that a machine is “Windows Server 2022” is not the same as knowing whether it is internet-facing, reachable from guest Wi-Fi, exposed across site-to-site VPN tunnels, or sitting in a flat VLAN with legacy systems that cannot be patched quickly.
The practical response should begin with role and reachability. Domain controllers, edge-adjacent servers, remote access infrastructure, Hyper-V hosts, management servers, and file servers deserve faster attention than lightly used lab machines. That prioritization is not an excuse to leave the rest unpatched; it is how mature teams spend the first 24 to 72 hours when everything cannot move at once.
There is also a home-user version of this story. Consumer Windows PCs behind a NAT router are not in the same exposure category as public Windows servers, but they still process network traffic and still benefit from timely cumulative updates. The difference is not whether to patch; it is whether the update is an emergency maintenance event or a same-day normal update.
Microsoft’s Sparse Language Is a Feature and a Frustration
Security advisories are written for two audiences that want opposite things. Defenders want enough detail to scope risk, build detections, validate exposure, and explain urgency to leadership. Attackers want enough detail to reproduce the bug before the world patches.That tension is why Microsoft often keeps protocol-level RCE disclosures relatively restrained at first. The company may identify the affected component, impact, severity, exploitability assessment, and update path without spelling out the exact parsing condition or packet structure. For defenders, that can feel like trying to prioritize a fire alarm without being told which floor is burning.
The frustration is legitimate. A Windows admin responsible for thousands of systems needs more than a CVE title to decide whether to accelerate a change freeze, wake a network team, or isolate a fragile segment. A SOC analyst needs indicators that are more concrete than “watch for suspicious traffic.”
But the alternative can be worse. Overly detailed early advisories can become exploit-development briefs. In the case of network-stack flaws, the line between actionable defender guidance and attacker enablement is especially thin, because the vulnerability may be reachable before authentication and before application logs ever see anything.
The mature reading of CVE-2026-40415 is therefore cautious. Treat the vendor-confirmed existence of the vulnerability as enough to patch. Treat any highly specific exploit claims circulating outside Microsoft’s advisory as unproven unless corroborated by credible researchers, working exploit demonstrations, or observed exploitation reports.
The Old Ghosts of Windows Networking Still Shape the New Panic
Windows has a long memory when it comes to remotely reachable bugs. Blaster, Sasser, Conficker, EternalBlue, BlueKeep, and more recent protocol vulnerabilities all taught admins that some flaws move from advisory to incident faster than procurement teams can approve overtime.Not every Windows RCE belongs in that lineage. The industry has a bad habit of calling anything network-adjacent “wormable” before the evidence supports it. That word should be used carefully, because it implies autonomous propagation, broad reachability, and exploit reliability across enough machines to create self-sustaining spread.
Still, the anxiety is rational. TCP/IP is the layer beneath the services that admins usually harden. If a vulnerability can be triggered by crafted packets before a request reaches IIS, SMB, RDP, or a line-of-business listener, then traditional service-level mitigations may not be enough.
That does not mean defenders are powerless. Host firewalls, perimeter filtering, segmentation, VPN scoping, IPv6 hygiene, endpoint detection telemetry, and rapid cumulative update deployment all matter. The key is to avoid the comforting fiction that “we do not run that application” is relevant when the affected component is the Windows networking stack itself.
This is also why Patch Tuesday fatigue is dangerous. Microsoft ships so many security fixes that even serious issues can blur into the monthly spreadsheet. CVE-2026-40415 deserves to be separated from the routine backlog because its affected layer changes the operational calculus.
The Patch Is the Control, But the Rollout Is the Risk
For Windows administrators, the answer will almost certainly be the same as it usually is: install the relevant cumulative security update for supported Windows versions. That sentence is simple enough for an advisory and complicated enough to ruin a week.Cumulative updates touch more than the named vulnerability. They include security fixes, quality changes, servicing-stack interactions, and sometimes regressions that only appear in certain domain, storage, printing, VPN, or application-control configurations. The more critical the server, the more likely the organization has a memory of a previous patch that broke something important.
That is why patching a TCP/IP RCE becomes a risk-balancing exercise rather than a slogan. Waiting too long increases exposure to exploit development. Moving without testing can damage availability. The job is not to pretend one risk does not exist; it is to compress testing, deploy in rings, monitor carefully, and keep rollback plans realistic.
Enterprises should avoid the two worst patterns. The first is “all at once everywhere,” which maximizes blast radius if the update misbehaves. The second is “pilot forever,” which leaves high-value systems exposed while low-risk endpoints soak for a week. A better model is accelerated rings: representative test systems first, exposed and high-value servers next, then the broader fleet.
For smaller organizations without formal rings, the guidance is less elegant but still clear. Patch a small number of representative machines, watch for obvious failures, confirm line-of-business connectivity, and then move. The absence of a perfect test lab should not become a reason to leave a network-stack RCE unaddressed.
Exposure Is Not Binary, and Neither Is Mitigation
The most common mistake in vulnerability triage is treating exposure as yes or no. A machine is internet-facing or it is not. A port is open or closed. A patch is installed or missing. Real networks are messier.A Windows server that is not directly exposed to the internet may still be reachable from partner VPNs, remote users, compromised laptops, guest networks, cloud peering links, or unmanaged operational-technology segments. A workstation behind NAT may still be exposed to malicious traffic on public Wi-Fi or hostile local networks. A server protected by a perimeter firewall may still accept traffic from a broad internal address range where attacker dwell time is the real concern.
That means compensating controls should be layered while patches roll out. Host-based firewalls can reduce unnecessary inbound reachability. Network ACLs can narrow who can talk to sensitive Windows roles. IDS and network telemetry can be tuned for unusual packet patterns, scanning behavior, or sudden crashes in networking components, even when exact exploit signatures are unavailable.
Administrators should also revisit IPv6 assumptions. Many Windows environments have IPv6 enabled by default, partially configured, poorly monitored, or ignored because “we do not use it.” That posture has caused trouble before. Disabling IPv6 casually is not Microsoft’s preferred broad fix and can break Windows features, but pretending it is absent because the IPv4 plan is documented is equally dangerous.
The right IPv6 question is not ideological. It is whether the organization knows where IPv6 is enabled, where it is routed, what firewalls apply, and whether monitoring sees it. A TCP/IP vulnerability is a good moment to find out.
Detection Will Lag the Patch, and That Is Normal
SOC teams often want detection content immediately after a major CVE drops. That instinct is healthy, but for low-level network vulnerabilities it can produce a false sense of coverage. If the public details are sparse, early detections may be generic, noisy, or based on assumptions that later prove incomplete.The first useful signals may not be packet-perfect exploit signatures. They may be scans against unusual protocol surfaces, repeated connection attempts, kernel crash telemetry, unexpected service interruptions, or endpoint alerts around abnormal system behavior after inbound network traffic. None of those alone proves exploitation, but together they can steer investigation.
EDR tools also have a visibility problem here. Remote code execution in a kernel-adjacent or networking component may not look like a familiar user-mode exploit chain at first. By the time a payload spawns a process, the most interesting part of the exploit may already have happened.
That does not make detection futile. It makes patch status, exposure mapping, and telemetry correlation more important than waiting for a perfect rule. If an organization cannot say which systems are patched and which are reachable, no Sigma rule will save the incident bridge from guesswork.
For WindowsForum readers running home labs, small businesses, or MSP environments, this is a good reminder to keep logs boring before the emergency. Centralized Windows event collection, firewall logging, router telemetry, and basic asset tagging are not glamorous. They are the difference between “we saw something odd” and “we have no idea where to look.”
The Confidence Metric Cuts Both Ways
The report-confidence language attached to CVE-2026-40415 has another implication: it tells defenders how much attackers may know. A high-confidence vulnerability with credible technical detail is easier for attackers to reason about than a vague rumor. The same clarity that helps defenders prioritize also helps offensive researchers reproduce.That does not mean secrecy is better. Security through obscurity has a poor record, and defenders cannot patch what vendors do not disclose. But it does mean the period immediately after disclosure is asymmetric. Attackers can focus on one bug; defenders must patch thousands of machines without breaking payroll, identity, remote access, or clinical systems.
The metric also helps explain why “known exploited” status is not the only thing that matters. By the time a vulnerability appears in exploitation catalogs, opportunistic scanning may already be underway. For network-stack RCEs, waiting for confirmed exploitation can be a losing strategy because the window between proof-of-concept and weaponization may be short.
At the same time, administrators should resist social-media certainty. A CVE number plus a dramatic exploit name does not make a campaign real. Unless Microsoft, CISA, a reputable security vendor, or credible independent researchers confirm exploitation details, treat sensational claims as leads to investigate rather than facts to repeat.
This is the narrow path good security teams walk every month. Move quickly because the vendor-confirmed risk is real. Speak carefully because the unconfirmed details may not be.
Windows 10’s Long Goodbye Makes These Advisories Harder to Ignore
CVE-2026-40415 lands in a Windows ecosystem still dealing with the afterlife of Windows 10. Microsoft’s mainstream consumer support deadline has already changed the economics of patching older endpoints, and extended security options have turned what used to be a simple support question into a budget and inventory problem.That matters because network-stack vulnerabilities punish forgotten machines. A retired laptop in a closet is not much of a risk if it never powers on. A Windows 10 workstation running a legacy scanner, kiosk, lab instrument, or warehouse app is different. If it remains connected and unpatched, it becomes part of the attack surface whether or not anyone thinks of it as production.
Server lifecycle issues are equally important. Old Windows Server builds often survive because the application owner left, the vendor disappeared, or the replacement project keeps slipping. Those systems are exactly where emergency patching is most difficult and compensating controls matter most.
The lesson is not that every organization can modernize overnight. It is that unsupported or hard-to-patch Windows nodes need to be treated as exceptions with documented network restrictions, monitoring, and business ownership. A TCP/IP RCE is a poor time to discover that “temporary” meant “since 2017.”
For home users, the advice is simpler. If the machine still receives security updates, install them. If it does not, stop treating it as a safe daily driver on a modern network.
The Real Test Is Whether Patch Management Knows the Network
CVE-2026-40415 is a useful stress test because it exposes the gap between endpoint management and network reality. Many tools can report missing KBs. Fewer organizations can instantly combine that data with reachability, business criticality, user population, cloud exposure, and maintenance-window constraints.That combined view is what turns vulnerability management from reporting into defense. A flat list of unpatched devices does not tell you which server should be patched first. A network map without patch state does not tell you which paths matter most. The two datasets have to meet.
MSPs face a version of this problem at scale. One customer may have disciplined update rings and clean inventory; another may have unmanaged servers, vendor appliances, and executives who only remember patching when something breaks. A Windows TCP/IP RCE is precisely the kind of advisory that forces providers to standardize their escalation language.
The best message to stakeholders is concrete and boring: this is a Microsoft-confirmed remote code execution vulnerability in a core Windows networking component; we are prioritizing reachable and high-value systems; we are deploying the vendor update through accelerated rings; and we are applying temporary network restrictions where patching cannot be immediate.
That message avoids both underreaction and theater. It does not promise that the sky is falling. It does not pretend the monthly update queue is business as usual.
The Patch Queue Now Has a Network-Stack Exception
The practical lessons from CVE-2026-40415 are not exotic, but they are easy to postpone. The vulnerability should push Windows teams to treat network-stack flaws as a distinct class inside the patch-management program, not merely another row in the monthly CVE export.- Organizations should prioritize supported Windows systems that are internet-facing, broadly reachable internally, or tied to identity, remote access, virtualization, and file-service roles.
- Administrators should validate whether IPv6 is enabled, routed, filtered, and monitored rather than assuming an IPv4-centered diagram describes the real environment.
- Security teams should use Microsoft’s advisory as the authoritative baseline and treat dramatic third-party exploit claims as unverified until credible corroboration appears.
- Patch deployment should move through accelerated rings that reduce regression risk without allowing exposed systems to wait behind low-risk endpoints.
- Systems that cannot be patched promptly should receive explicit compensating controls, including narrowed inbound access, host firewall review, segmentation, and heightened monitoring.
- Asset inventory should connect patch state with network reachability, because neither dataset is sufficient on its own during a network-stack vulnerability response.
Microsoft’s disclosure gives defenders enough to act, but not enough to become complacent. That is the uncomfortable middle ground of modern Windows security: patch quickly, verify carefully, distrust sensational certainty, and use each network-stack vulnerability as another reason to make the next one less chaotic.
Source: MSRC Security Update Guide - Microsoft Security Response Center