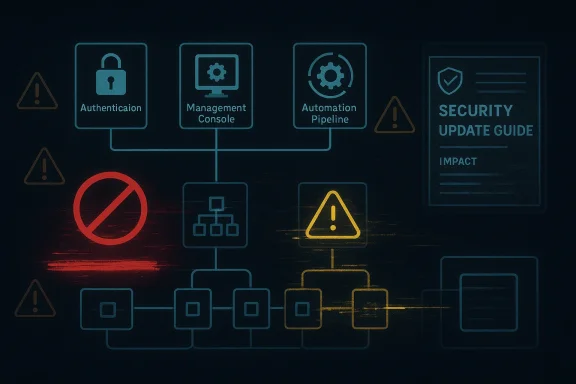
Microsoft’s description of CVE-2026-40706 points to a serious availability weakness: an attacker can either fully deny access to impacted resources for as long as the attack continues, or cause a partial but still consequential loss of service that can persist even after the attack ends. That wording matters because it places the issue in the same practical bucket as other high-impact denial-of-service bugs that do not necessarily crash everything at once, but still disrupt real workloads, workflows, and service guarantees. Microsoft’s Security Update Guide has increasingly emphasized this kind of standardized impact language for CVEs, which helps defenders understand whether a flaw is a total outage, a sustained degradation, or something in between le, but the nuance in this case is the story. “Total loss of availability” suggests a scenario where the affected component can be rendered unreachable or unusable while the attack is active, while the alternative phrasing covers situations where only part of the service is denied but the operational consequences are still severe enough to qualify as a security event. That distinction is important in enterprise environments because a partial outage can be just as disruptive as a full one if it hits authentication, automation, management planes, or customer-facing workflows.
Microsoft’s modern security disclosure model is built around giving defenders more structured data about impact, severity, and the behavior of a vulnerability, rather than relying on a vague bullet-point summary. The company has explained that the Security Update Guide now uses CVSS-style descriptions and richer metadata so administrators can sort, filter, and prioritize issues more intelligently . In practice, that means the impact state06 should be read as a strong signal that the flaw is operationally meaningful even if it is not a classic code-execution bug.
The biggest immediate takeaway is that this is not the kind of vulnerability defenders should dismiss as “just a nuisance.” Availability attacks are often underestimated because they do not always look dramatic on paper. Yet when they target a critical service component, the result can be loss of connectivity, failed retries, queue buildup, service restarts, or cascading failures in dependent systems.
The public record available here does not yet give a full technical breakdown of the root cause, affected product family, or exploit path for CVE-2026-40706. What it does give us is enough to understand the risk posture: Microsoft considers the impact serious enough to describe in direct availability terms, and that alone puts the issue on the radar for patch prioritization and change-control planning.
Microsoft’s Security Update Guide has become the company’s central public mechanism for publishing vulnerability details, mapping them to products, and giving customers machine-readable information for triage and remediation. Microsoft has steadily expanded that model, including the addition of CVE descriptions, CWE mappings, and CSAF-style publication support for richer downstream automation . That evolution matters because modern defenders rarely managaon; they manage fleets, dependencies, and layered control planes.
The result is that a short advisory line can carry a lot of weight. When Microsoft says an attacker can deny availability in a sustained or persistent way, that is not merely an abstract severity label. It is an operational warning that the component may fail in a way that survives beyond a single request, a single session, or even a single attack window.
This broader disclosure style reflects a bigger shift in the industry. Availability vulnerabilities used to be treated as lesser incidents compared with remote code execution or privilege escalation. That is no longer a safe assumption. Modern infrastructure is built on chained services, shared libraries, and persistent automation, so even a denial-of-service flaw can become a platform problem if it affects the wrong piece of plumbing. Microsoft’s own historical guidance around availability-class vulnerabilities has shown that the company treats these issues as first-class security problems when the effect is serious enough .
There is also a practical reason Microsoft and other vendors now spell these things out more clearly: now whether they are dealing with a brief interruption, an ongoing degradation, or a condition that can be repeated until the service is effectively unusable. That is the difference between an annoyance, a business continuity issue, and an incident that needs immediate containment.
CVE-2026-40706 should therefore be interpreted in the same operational context as other Microsoft availability advisories: not as a theoretical weakness, but as a vulnerability that can matter most when it lands in infrastructure that other systems depend on. In enterprise IT, those dependencies are often the highest-value targets of all.
A partial availability loss can be especially dangerous because it often looks like “flakiness” instead of a security incident. That can delay escalation, slow triage, and let attackers continue to drive disruption over time. It is the kind of problem that may not trigger panic at first, but still consumes engineering, operations, and help-desk attention.
In other words, the severity is not just about whether the service is technically alive. It is about whether the attacker can make the service unreliable enough to become unusable in practice.
Persistent availability damage is often more expensive than transient disruption because it converts a security event into an operational recovery exercise. Administrators may need to drain traffic, rebuild state, restart services, or even redeploy nodes. That means the real cost is not only the attack itself, but the cleanup.
From a defender’s perspective, persistent conditions also raise the stakes for monitoring. If the service stays degraded after the attack ends, teams need stronger telemetry and clearer rollback options so they can determine whether they are seeing an active exploit, a failed recovery, or a separate fault triggered by the initial attack.
A vulnerability that blocks access to a shared service can stall authentication, messaging, management operations, or application transactions. If that service is part of a larger distributed system, the incident may ripple outward in ways that make the original root cause hard to identify. The result is not simply “the app is down,” but “everything downstream is behaving oddly.”
That diagnostic burden is one of the reasons Microsoft’s language here is significant. By calling out direct consequences even when the denial is not total, the guidance is warning administrators that the operational harm may still be severe enough to justify urgent remediation. That is especially true for shared services, where a narrow failure can have a wide blast radius.
In practice, partial denial can also interact badly with retry logic. A service that fails just enough to cause repeated retries may consume more resources than a clean outage, because clients keep hammering the broken path instead of backing off cleanly.
That difference is why IT teams must assess the role of the impacted component, not just the CVE label. A flaw in a peripheral utility is one thing; a flaw in a service that other systems call continuously is another. Microsoft’s phrasing suggests the latter kind of risk deserves attention here.
tut the full technical detail exposed here, the impact language alone gives patch teams a credible basis for prioritization. If a vulnerability can deny access to resources in a sustained or persistent way, then the affected component deserves early review, especially if it supports business-critical services.
That is particularly useful for availability bugs because their practical severity can vary a great deal based on deployment. A flaw that looks modest in isolation can become serious if the component sits in the authentication path, the automation path, or the control path. Microsoft’s phrasing is essentially telling defenders to think systemically.
In the meantime, the right response is to map exposure, verify whether the affected component exists in your environment, and prepare for remediation. The absence of complete technical detail is not a reason to relax; it is a reason to be methodical.
That is why availability issues deserve the same disciplined handling as more dramatic vulnerabilities. They may not steal data, but they can stop a business from operating normally. In practical terms, that means downtime, interrupted automation, failed jobs, and support escalation.
This is where persistent impact matters most. If a vulnerability can leave the component in a degraded state after the attack is over, then recovery may be slow and messy. A restart may help, but if the underlying condition remains reachable, the problem can recur.
That kind of pattern is especially dangerous in automated environments, where watchdogs, load balancers, or orchestration tools may keep reintroducing the same failure in a loop. The result is a small bug with a surprisingly expensive footprint.
This is one reason Microsoft’s exact phrasing is useful. It signals that the component’s availability itself is the target, not necessarily the data or code inside it. A narrow denial in the right place can have broad consequences elsewhere.
That does not mean every availability flaw will be actively exploited in the wild. But it does mean defenders should not assume low exploit sophistication. Some denial-of-service vulnerabilities are trivial to trigger; others require conditions, timing, or repeated attempts. Microsoft’s wording here leaves room for either model, but the operational caution remains the same.
That is a meaningful distinction. Many organizations are well prepared for one outage. Fewer are prepared for a sustained pattern of disruption that comes and goes, especially if the attack can be resumed at will.
Repeated abuse can also create noise that obscures attribution. A service that keeps degrading may look like a hardware problem, a network instability, or a capacity issue before anyone suspects deliberate action. That delay is often part of the attacker’s advantage.
Persistent issues are also more likely to trigger secondary disruptions, such as failovers, resynchronization, or backlog processing. In other words, the attack can create follow-on instability even after the original trigger disappears.
It is also wise to check whether any upstream or downstream products bundle the same component. In enterprise environments, the vulnerable code may be present in software that does not obviously advertise it. That is where inventory discipline and dependency awareness pay off.
The other advantage is that Microsoft’s disclosure style gives defenders a clearer basis for urgency than older, more ambiguous advisories did. Availability language is concrete, and concrete language is easier to turn into action.
A second concern is hidden exposure. Many organizations do not have perfect visibility into every embedded component or downstream bundle. If the vulnerable piece is buried inside another product, patching can be delayed until a vendor update arrives, which stretches exposure.
A third concern is that persistent degradation can be misdiagnosed as a generic stability issue. When that happens, incident response becomes slower and patch urgency gets lost in the noise.
For defenders, the safest assumption is that any component with this kind of availability impact deserves prompt review. Even without a dramatic exploit chain, a persistent denial-of-service condition in the wrong part of the stack can become an incident very quickly. In modern enterprise IT, uptime is security, and security incidents that damage uptime are never low priority.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Microsoft’s modern security disclosure model is built around giving defenders more structured data about impact, severity, and the behavior of a vulnerability, rather than relying on a vague bullet-point summary. The company has explained that the Security Update Guide now uses CVSS-style descriptions and richer metadata so administrators can sort, filter, and prioritize issues more intelligently . In practice, that means the impact state06 should be read as a strong signal that the flaw is operationally meaningful even if it is not a classic code-execution bug.
The biggest immediate takeaway is that this is not the kind of vulnerability defenders should dismiss as “just a nuisance.” Availability attacks are often underestimated because they do not always look dramatic on paper. Yet when they target a critical service component, the result can be loss of connectivity, failed retries, queue buildup, service restarts, or cascading failures in dependent systems.
The public record available here does not yet give a full technical breakdown of the root cause, affected product family, or exploit path for CVE-2026-40706. What it does give us is enough to understand the risk posture: Microsoft considers the impact serious enough to describe in direct availability terms, and that alone puts the issue on the radar for patch prioritization and change-control planning.
 Background
Background
Microsoft’s Security Update Guide has become the company’s central public mechanism for publishing vulnerability details, mapping them to products, and giving customers machine-readable information for triage and remediation. Microsoft has steadily expanded that model, including the addition of CVE descriptions, CWE mappings, and CSAF-style publication support for richer downstream automation . That evolution matters because modern defenders rarely managaon; they manage fleets, dependencies, and layered control planes.The result is that a short advisory line can carry a lot of weight. When Microsoft says an attacker can deny availability in a sustained or persistent way, that is not merely an abstract severity label. It is an operational warning that the component may fail in a way that survives beyond a single request, a single session, or even a single attack window.
This broader disclosure style reflects a bigger shift in the industry. Availability vulnerabilities used to be treated as lesser incidents compared with remote code execution or privilege escalation. That is no longer a safe assumption. Modern infrastructure is built on chained services, shared libraries, and persistent automation, so even a denial-of-service flaw can become a platform problem if it affects the wrong piece of plumbing. Microsoft’s own historical guidance around availability-class vulnerabilities has shown that the company treats these issues as first-class security problems when the effect is serious enough .
There is also a practical reason Microsoft and other vendors now spell these things out more clearly: now whether they are dealing with a brief interruption, an ongoing degradation, or a condition that can be repeated until the service is effectively unusable. That is the difference between an annoyance, a business continuity issue, and an incident that needs immediate containment.
CVE-2026-40706 should therefore be interpreted in the same operational context as other Microsoft availability advisories: not as a theoretical weakness, but as a vulnerability that can matter most when it lands in infrastructure that other systems depend on. In enterprise IT, those dependencies are often the highest-value targets of all.
What the Impact Language Really Means
The wording attached to CVE-2026-40706 is unusually explicit, and that helps defenders think beyond the label. If an attacker can fully deny access to resources in the impacted component, then the component is effectively down from the perspective of the systems or users that depend on it. If the attacker can only partially deny availability, Microsoft is still signaling that the outcome is serious enough to matter because the reduced availability has a direct and harmful operational effect.Total denial versus partial denial
A total denial-of-service scenario is straightforward: the component stops serving its purpose altogether while the attack is active or until recovery occurs. A partial denial is more subtle, but it can still be worse in practice if the affected resource sits in a control plane or in a shared dependency. One broken workflow in a management layer can block many downstream tasks, especially in environments that rely on automation and retries.A partial availability loss can be especially dangerous because it often looks like “flakiness” instead of a security incident. That can delay escalation, slow triage, and let attackers continue to drive disruption over time. It is the kind of problem that may not trigger panic at first, but still consumes engineering, operations, and help-desk attention.
In other words, the severity is not just about whether the service is technically alive. It is about whether the attacker can make the service unreliable enough to become unusable in practice.
Why persistence matters
Microsoft’s wording also notes that the loss may be persistent even after the attack ends. That is a major clue. It suggests the vulnerability may not be a temporary packet-level disturbance that clears as soon as traffic stops, but something that changes the state of the component enough to require a restart, reset, or deeper remediation.Persistent availability damage is often more expensive than transient disruption because it converts a security event into an operational recovery exercise. Administrators may need to drain traffic, rebuild state, restart services, or even redeploy nodes. That means the real cost is not only the attack itself, but the cleanup.
From a defender’s perspective, persistent conditions also raise the stakes for monitoring. If the service stays degraded after the attack ends, teams need stronger telemetry and clearer rollback options so they can determine whether they are seeing an active exploit, a failed recovery, or a separate fault triggered by the initial attack.
Short list of practical implications
- The issue should be treated as more than a nuisance outage.
- Partial disruption can still create serious downstream failures.
- Persistent effects imply recovery may require manual intervention.
- Monitoring should look for both active attack patterns and post-attack degradation.
- Control-plane and automation dependencies deserve special attention.
Why Availability Bugs Still Matter
Availability flaws are often underrated because they do not always fit the most sensational breach narratives. There is no stolen data headline, no remote shell, no obvious privilege jump. Yet infrastructure teams know that a denial-of-service vulnerability can be one of the most expensive incidents to absorb when it lands in the wrong place.A vulnerability that blocks access to a shared service can stall authentication, messaging, management operations, or application transactions. If that service is part of a larger distributed system, the incident may ripple outward in ways that make the original root cause hard to identify. The result is not simply “the app is down,” but “everything downstream is behaving oddly.”
The hidden cost of partial outages
Partial outages are often worse than hard failures because they undermine trust in the system. If a service fails intermittently, operators start chasing ghosts: DNS, network, load balancers, certificates, identity providers, application code, or storage backends. Security teams then spend valuable time separating symptoms from cause.That diagnostic burden is one of the reasons Microsoft’s language here is significant. By calling out direct consequences even when the denial is not total, the guidance is warning administrators that the operational harm may still be severe enough to justify urgent remediation. That is especially true for shared services, where a narrow failure can have a wide blast radius.
In practice, partial denial can also interact badly with retry logic. A service that fails just enough to cause repeated retries may consume more resources than a clean outage, because clients keep hammering the broken path instead of backing off cleanly.
The enterprise versus consumer split
For consumers, an availability flaw usually shows up as an app freeze, a timeout, or a service that stops responding. Frustrating, yes, but often temporary. For enterprises, the same flaw can affect ticketing systems, identity services, endpoint management, or cloud-connected workflows where even a brief interruption can create business impact.That difference is why IT teams must assess the role of the impacted component, not just the CVE label. A flaw in a peripheral utility is one thing; a flaw in a service that other systems call continuously is another. Microsoft’s phrasing suggests the latter kind of risk deserves attention here.
Core takeaways
- Availability attacks can be financially and operationally expensive.
- Partial outages can be more confusing than outright failures.
- Retry loops can magnify the load of a vulnerability.
- Enterprise impact often exceeds what the CVE title alone suggests.
- Shared services deserve higher urgency than isolated endpoints.
Microsoft’s Disclosure Model and Prioritization
Microsoft has spent years making its vulnerability reporting more structured and more useful to defenders. The Security Update Guide now serves as the primary public catalog for Microsoft CVEs, and the company has made a point of standardizing descriptions so security teams can triage more efficiently . That matters because a good advisory does more than name a flaw; it helps organizations decide how fast they need to move.tut the full technical detail exposed here, the impact language alone gives patch teams a credible basis for prioritization. If a vulnerability can deny access to resources in a sustained or persistent way, then the affected component deserves early review, especially if it supports business-critical services.
How to read Microsoft’s severity language
Microsoft’s modern descriptions are designed to tell you what kind of failure to expect. Is the problem temporary or persistent? Is the denial total or partial? Does the attacker need timing, conditions, or repeated abuse to make it matter? Those distinctions help organizations estimate whether a flaw will be a monitoring issue, an outage issue, or a broader continuity risk.That is particularly useful for availability bugs because their practical severity can vary a great deal based on deployment. A flaw that looks modest in isolation can become serious if the component sits in the authentication path, the automation path, or the control path. Microsoft’s phrasing is essentially telling defenders to think systemically.
Why the lack of low-level detail does not reduce urgency
It can be tempting to defer action when a CVE page does not immediately expose a detailed exploit chain. That is a mistake. Many real-world incidents begin with limited public detail and only later become clearer as vendors, researchers, and attackers fill in the gaps.In the meantime, the right response is to map exposure, verify whether the affected component exists in your environment, and prepare for remediation. The absence of complete technical detail is not a reason to relax; it is a reason to be methodical.
Prioritization checklist
- Confirm whether the affected component is present in your estate.
- Determine whether it is internet-facing or internally shared.
- Assess whether the component sits in a control plane or dependency chain.
- Review whether the issue can persist after the attack stops.
- Plan for staging, rollback, and service validation after patching.
Operational Risk in Real Deployments
The most important question for administrators is not simply whether the vulnerability exists, but what breaks when it is exercised. A denial-of-service flaw in a low-value utility is one thing. The same flaw in a service that supports identity, remote management, or workflow orchestration can force emergency response across a much larger environment.That is why availability issues deserve the same disciplined handling as more dramatic vulnerabilities. They may not steal data, but they can stop a business from operating normally. In practical terms, that means downtime, interrupted automation, failed jobs, and support escalation.
Where the real damage usually shows up
Availability attacks often surface first as symptoms rather than root cause. Users see timeouts. Operators see retries. Logs show intermittent failures, delayed responses, or service restarts. In some cases, the component does not crash outright but becomes sluggish enough that dependent systems treat it as unavailable anyway.This is where persistent impact matters most. If a vulnerability can leave the component in a degraded state after the attack is over, then recovery may be slow and messy. A restart may help, but if the underlying condition remains reachable, the problem can recur.
That kind of pattern is especially dangerous in automated environments, where watchdogs, load balancers, or orchestration tools may keep reintroducing the same failure in a loop. The result is a small bug with a surprisingly expensive footprint.
Control planes are the danger zone
Security teams should pay special attention when a vulnerable component supports management, authentication, or orchestration. In those environments, the attacker may not need to take down every user-facing service. They only need to interrupt the control path long enough to create a business impact.This is one reason Microsoft’s exact phrasing is useful. It signals that the component’s availability itself is the target, not necessarily the data or code inside it. A narrow denial in the right place can have broad consequences elsewhere.
Enterprise response priorities
- Identify whether the component is on a critical path.
- Check whether the flaw can be triggered repeatedly.
- Assess whether the component self-recovers or remains degraded.
- Determine whether failover can mask the issue.
- Test patches in a staging environment before broad rollout.
What This Suggests About Attackers
Attackers do not always need the most glamorous exploit class to cause damage. A reliable availability bug can be useful precisely because it is noisy, disruptive, and repeatable. If a vulnerability can deny access to resources in a sustained or persistent way, that opens the door to harassment, extortion, service degradation, or coordinated distraction.That does not mean every availability flaw will be actively exploited in the wild. But it does mean defenders should not assume low exploit sophistication. Some denial-of-service vulnerabilities are trivial to trigger; others require conditions, timing, or repeated attempts. Microsoft’s wording here leaves room for either model, but the operational caution remains the same.
Why repeated abuse is especially concerning
The phrase “the attacker being able to fully deny access” implies that the vulnerable behavior may be reproducible rather than one-and-done. If so, an attacker may not need to achieve permanent compromise to achieve a strategic effect. They may simply need to keep the component unavailable long enough to disrupt business operations.That is a meaningful distinction. Many organizations are well prepared for one outage. Fewer are prepared for a sustained pattern of disruption that comes and goes, especially if the attack can be resumed at will.
Repeated abuse can also create noise that obscures attribution. A service that keeps degrading may look like a hardware problem, a network instability, or a capacity issue before anyone suspects deliberate action. That delay is often part of the attacker’s advantage.
Why persistence expands the threat surface
If a component remains degraded after the attack ends, the attacker does not need constant presence to create ongoing pain. The consequence remains until the service is repaired, restarted, or replaced. That increases the payoff for the attacker and increases the burden on defenders.Persistent issues are also more likely to trigger secondary disruptions, such as failovers, resynchronization, or backlog processing. In other words, the attack can create follow-on instability even after the original trigger disappears.
Indicators defenders should watch
- Repeated timeouts against the same component.
- Service degradation that survives the original trigger window.
- Recovery loops involving restarts or failovers.
- Unexpected retry storms or queue buildup.
- A pattern of failures that maps to one shared dependency.
Practical Response for Administrators
Even before a full technical advisory is available, there are sensible steps organizations can take. The first is to inventory whether the impacted component exists anywhere in the environment. The second is to determine whether it is exposed to untrusted input or embedded in a service that other systems depend on. The third is to prepare for patching and validation rather than waiting for a problem to surface in production.Immediate steps
- Identify affected systems, applications, and services.
- Verify whether the vulnerable component is internet-facing or internally accessible.
- Check whether the service has failover or resilience controls.
- Review logs for unexplained timeouts, restarts, or availability anomalies.
- Plan patch deployment with rollback and testing in mind.
What to validate after patching
Post-patch validation should not stop at “the update installed successfully.” Teams should confirm that the service starts cleanly, stays stable under normal load, and does not exhibit unusual retry or timeout behavior. If the component is exposed to clients, test realistic traffic patterns rather than only a synthetic health check.It is also wise to check whether any upstream or downstream products bundle the same component. In enterprise environments, the vulnerable code may be present in software that does not obviously advertise it. That is where inventory discipline and dependency awareness pay off.
Communications to stakeholders
Stakeholders care less about the CVE number than about whether the service stays reliable. The message should be simple: this vulnerability can deny access to important resources, and the operational impact may persist. That framing helps justify patch windows, coordination, and temporary service constraints if needed.Strengths and Opportunities
This vulnerability also creates an opportunity for stronger operational hygiene. Because the issue is framed around availability, it can be used as a forcing function for inventory review, dependency mapping, and more rigorous resilience planning. The best security responses often leave the environment better documented than before.The other advantage is that Microsoft’s disclosure style gives defenders a clearer basis for urgency than older, more ambiguous advisories did. Availability language is concrete, and concrete language is easier to turn into action.
- The impact statement is clear enough to support prioritization.
- The issue encourages better dependency inventory.
- Availability problems are easier to communicate to operations teams than abstract exploit classes.
- The event can drive improved resilience testing.
- Patch planning can be tied to business continuity, not just security.
- The advisory model helps standardize triage across teams.
- Security and ops can align on a shared definition of “availability risk.”
Risks and Concerns
The biggest danger is underreaction. Teams often downgrade availability bugs because they do not sound as severe as code execution or credential theft. That is a mistake if the component sits in a critical path, because denial of access can be enough to disrupt core business services.A second concern is hidden exposure. Many organizations do not have perfect visibility into every embedded component or downstream bundle. If the vulnerable piece is buried inside another product, patching can be delayed until a vendor update arrives, which stretches exposure.
A third concern is that persistent degradation can be misdiagnosed as a generic stability issue. When that happens, incident response becomes slower and patch urgency gets lost in the noise.
- The issue may be underestimated because it is “only” availability-related.
- Hidden dependencies can make exposure hard to find.
- Persistent degradation can be mistaken for ordinary instability.
- Recovery may require more than a simple restart.
- Retry storms can magnify the original impact.
- Shared control-plane components can turn a narrow bug into a broad outage.
- Delayed remediation can prolong operational disruption.
Looking Ahead
What matters next is whether Microsoft follows this impact language with a fuller product mapping, exploitability detail, and concrete remediation guidance. That will determine how quickly organizations can separate theoretical exposure from actual risk. The other key question is whether downstream vendors confirm that they ship the impacted component and, if so, when they publish fixed builds.For defenders, the safest assumption is that any component with this kind of availability impact deserves prompt review. Even without a dramatic exploit chain, a persistent denial-of-service condition in the wrong part of the stack can become an incident very quickly. In modern enterprise IT, uptime is security, and security incidents that damage uptime are never low priority.
What to watch next
- Microsoft’s full advisory details for product scope and fix guidance.
- Downstream vendor confirmations and patched package versions.
- Evidence of whether the issue is triggerable remotely or requires conditions.
- Any signs of repeatable exploitation patterns in affected environments.
- Clarification on whether the impact is transient, persistent, or both.
Source: MSRC Security Update Guide - Microsoft Security Response Center