CVE-2026-41096 is a Microsoft-listed Windows DNS Client remote code execution vulnerability published in the MSRC Security Update Guide, affecting the Windows component that resolves domain names for client systems and requiring administrators to assess exposure through Microsoft’s May 12, 2026 security update data.
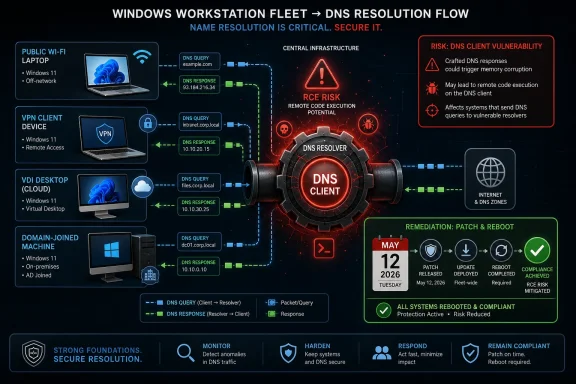
The uncomfortable part is not merely that the words “DNS Client” and “remote code execution” appear in the same advisory. It is that this class of bug sits in a component most Windows users never think about, yet every browser tab, software updater, domain join, VPN client, and line-of-business application depends on it. When name resolution becomes an attack surface, the perimeter is not a server rack; it is the workstation fleet.
The Windows DNS Client is one of those pieces of plumbing that disappears precisely because it works. It translates names into addresses, caches answers, and feeds the rest of the operating system the network coordinates it needs to function. That makes it easy to underestimate in patch triage, where administrators often sort vulnerabilities by whether a product is “internet-facing.”
That framing is too narrow here. A DNS client vulnerability does not need to live on a public server to matter. It lives on laptops that roam between hotel Wi-Fi and corporate VPNs, on VDI desktops, on developer workstations, on kiosks, on jump boxes, and on ordinary domain-joined Windows machines that ask the network hundreds or thousands of naming questions every day.
Remote code execution in such a component deserves attention because the vulnerable code path may be reachable through normal network activity rather than exotic user behavior. Microsoft’s public entry does not, by itself, hand defenders a complete exploit recipe, and that absence matters. But the affected role is so fundamental that security teams should resist treating sparse disclosure as low significance.
The key editorial point is simple: a quiet DNS client RCE can be more operationally dangerous than a noisy server bug, because it tempts organizations to wait for proof-of-concept chatter before acting. By the time public exploit details arrive, the patch window has often already closed for the defenders and opened for everyone else.
For Microsoft vulnerabilities, the presence of an MSRC entry is itself meaningful. Microsoft is not merely aggregating gossip from a mailing list; it is assigning a CVE record to a Windows component and publishing it through the company’s security response process. Even when the advisory withholds root-cause detail, the vendor acknowledgement shifts the issue out of the realm of speculation.
That matters because “not enough detail” is often misread as “not enough risk.” In security operations, those are different things. A vulnerability can be real, patched, and serious while still being intentionally under-described to slow exploit development.
This is especially true for client-side network parsers. Microsoft and other vendors routinely avoid spelling out the precise malformed packet, response field, compression edge case, or memory handling flaw that triggers exploitation. That restraint frustrates defenders who want elegant detection logic, but it also denies attackers a ready-made map.
That ambient quality is what makes DNS bugs unsettling. A vulnerability in a document parser usually needs a document. A vulnerability in a browser engine usually needs a page. A vulnerability in a DNS client may sit closer to the operating system’s reflexes, triggered as part of routine connectivity.
The practical risk depends on exploit preconditions Microsoft has not fully detailed in the provided advisory text. An attacker might need to influence a DNS response, operate a malicious DNS server, place themselves on-path, poison a lookup flow, or lure a target into resolving a domain under attacker control. Those differences matter enormously for real-world exploitability.
But from a defender’s perspective, none of those scenarios is far-fetched. Enterprise machines leave trusted networks. Users join guest networks. VPN split tunneling exists. Developers test against arbitrary domains. Malware already abuses DNS for command-and-control, staging, tunneling, and evasion. If a DNS response can also become a memory-corruption delivery vehicle, the line between “network noise” and “initial access” gets thinner.
CVE-2026-41096 points elsewhere: the client. That changes the blast pattern. Instead of asking only which servers expose port 53, organizations need to ask which endpoints process potentially hostile name-resolution data and how quickly those endpoints receive cumulative updates.
For most Windows environments, the answer is “nearly all of them.” Even machines that use internal recursive resolvers still process DNS answers. Even clients behind secure web gateways still resolve names. Even highly managed enterprise endpoints may encounter untrusted DNS paths when off-network, before VPN establishment, or during captive portal negotiation.
This is why endpoint patch latency becomes the real control. The server team may patch a handful of recursive resolvers quickly, but workstation remediation is a campaign: rings, pilot groups, reboot enforcement, help desk exceptions, application compatibility checks, and laptop availability. A DNS Client RCE punishes organizations that have beautiful server hygiene and sluggish endpoint governance.
Security teams should therefore avoid both panic and complacency. The useful stance is disciplined urgency. Treat the advisory as credible because it comes through MSRC, treat the component as broadly exposed because DNS is universal, and treat the missing root-cause detail as a reason to patch rather than a reason to defer.
The reporting-confidence metric reinforces this point. It is not an exploitability guarantee. It does not say attackers have working code. It does not say every Windows machine is trivially exploitable from the public internet. It says the vulnerability’s existence and known details have a credibility level that should inform urgency.
That distinction matters in executive communication. “Microsoft has confirmed a Windows DNS Client RCE” is a stronger and cleaner message than “there may be a DNS bug.” But “confirmed” should not be inflated into “actively exploited” unless Microsoft or credible telemetry says so. Good security writing, like good incident response, separates verified facts from plausible risk.
DNS offers several attractive places for bug hunters. Parsers must handle compressed names, record types, lengths, encodings, caching behavior, malformed responses, retry logic, and edge cases created by decades of protocol evolution. The Windows DNS Client must also integrate with modern Windows features, enterprise policy, VPN behavior, NRPT rules, DNS-over-HTTPS settings, and name-resolution fallback mechanisms.
None of that proves where CVE-2026-41096 lives. But it explains why the category is fertile. Networking clients are not passive consumers of clean data; they are parsers of adversarial input from messy networks. Every parser is a bet that hostile input will be rejected safely.
For defenders, the likely attacker workflow is enough to shape timing. Public exploit code may not exist at disclosure. But patch availability starts the reverse-engineering clock. The safer assumption is that technical understanding increases after Patch Tuesday, not before it.
Network security tools can sometimes help if exploit traffic becomes known. DNS inspection, endpoint detection telemetry, crash artifacts, suspicious child processes, and anomalous resolver behavior may all provide clues. But before public indicators emerge, defenders should not pretend they can reliably detect exploitation from standard recursive resolver logs alone.
This is where architectural controls matter. Enforcing trusted DNS resolvers, limiting arbitrary network DNS, using VPN policies that prevent unsafe resolution paths, and monitoring for clients that bypass corporate resolvers all reduce exposure. Those controls will not substitute for the Windows update, but they can reduce the number of ways a malicious response reaches a vulnerable parser.
The most practical interim control is boring: make sure clients receive the relevant cumulative update quickly and reboot. In Windows security, the reboot is often the forgotten half of remediation. A downloaded update that has not completed installation is not a patched endpoint.
Still, consumer exposure should not be dismissed. Home laptops move between routers, public Wi-Fi, school networks, travel hotspots, and ISP resolvers. A DNS Client issue is not limited to corporate intranets. If exploitation turns out to require malicious DNS responses, consumer machines can encounter those through compromised routers, hostile hotspots, or attacker-controlled domains.
The bigger challenge is communication. “DNS Client remote code execution” sounds abstract to non-specialists. The plain version is better: Windows is patching a bug in the component that handles website and service lookups, and a malicious network response could potentially be involved. Update and restart.
Microsoft’s consolidation of fixes into cumulative updates helps here. Users do not need to hunt for a standalone DNS patch. But that same consolidation can obscure urgency because one update looks much like another in the Windows Update interface.
The first question is asset coverage. Are all supported Windows client versions in the patch system? Are remote laptops checking in? Are VDI images updated? Are gold images refreshed? Are offline or intermittently connected systems visible? Are security appliances and management tools reporting installation state or merely deployment attempt state?
The second question is reboot compliance. Windows cumulative updates frequently require a restart to complete. Enterprises that celebrate deployment percentages without measuring reboot completion are measuring intent, not remediation.
The third question is exception handling. Every organization has machines that cannot patch immediately: lab systems, regulated endpoints, operational technology jump hosts, training rooms, legacy application workstations, executive laptops stuck in travel mode. A DNS Client RCE should force those exceptions into daylight, because the machines least able to patch are often the ones least able to withstand compromise.
That tension is not unique to CVE-2026-41096, but client networking bugs sharpen it. DNS is too central to ignore, and Windows endpoint fleets are too heterogeneous to patch blindly everywhere at once. The rational answer is not delay; it is controlled acceleration.
A mature organization should already have deployment rings that can move quickly: IT pilot, security-sensitive systems, broad business groups, and stragglers. If those rings cannot process a client-side RCE within days, the problem is not this CVE. The problem is that the patching model has been optimized for convenience rather than threat velocity.
There is also a transparency issue. Sparse advisories protect customers in one sense by withholding exploit clues. They frustrate customers in another by making it harder to prioritize. Microsoft’s challenge is to provide enough operational guidance for defenders without gifting attackers the missing exploit primitive.
That is why defenders should inventory DNS behavior more seriously. Which resolvers do clients use on and off VPN? Is DNS-over-HTTPS permitted, blocked, or centrally managed? Do endpoint firewalls prevent direct DNS to the internet? Are split-tunnel rules allowing unmanaged resolution? Are guest Wi-Fi and corporate Wi-Fi separated cleanly? Does endpoint telemetry flag resolver changes?
These are not glamorous questions. They rarely make the board deck. But they determine whether a DNS client vulnerability is constrained to a managed path or sprayed across every network a user visits.
The same logic applies to developers and power users. Local DNS overrides, test resolvers, container networks, WSL environments, VPN clients, and security tools can complicate resolution behavior. The more custom the stack, the more important it is to verify that the underlying Windows host is patched rather than assuming the application layer is insulated.
That combination should lead to action, not theatrics. Patch supported Windows systems. Prioritize endpoints that roam, systems used by administrators, machines on untrusted networks, and any workstation class with delayed update behavior. Confirm reboots, not just update approvals.
Security teams should also watch for later MSRC revisions. Microsoft advisories can evolve as exploitability assessment changes, affected products are clarified, or active exploitation is observed. A CVE that begins as a terse entry can become a much more urgent operational story if public proof-of-concept code appears or exploitation telemetry emerges.
The right posture is to treat the first advisory as the start of the vulnerability lifecycle, not the end of it. Patch now, monitor later, and do not wait for a catchy name before deciding that DNS client code matters.
Source: MSRC Security Update Guide - Microsoft Security Response Center
The uncomfortable part is not merely that the words “DNS Client” and “remote code execution” appear in the same advisory. It is that this class of bug sits in a component most Windows users never think about, yet every browser tab, software updater, domain join, VPN client, and line-of-business application depends on it. When name resolution becomes an attack surface, the perimeter is not a server rack; it is the workstation fleet.
 Microsoft’s Small Advisory Carries a Big Architectural Warning
Microsoft’s Small Advisory Carries a Big Architectural Warning
The Windows DNS Client is one of those pieces of plumbing that disappears precisely because it works. It translates names into addresses, caches answers, and feeds the rest of the operating system the network coordinates it needs to function. That makes it easy to underestimate in patch triage, where administrators often sort vulnerabilities by whether a product is “internet-facing.”That framing is too narrow here. A DNS client vulnerability does not need to live on a public server to matter. It lives on laptops that roam between hotel Wi-Fi and corporate VPNs, on VDI desktops, on developer workstations, on kiosks, on jump boxes, and on ordinary domain-joined Windows machines that ask the network hundreds or thousands of naming questions every day.
Remote code execution in such a component deserves attention because the vulnerable code path may be reachable through normal network activity rather than exotic user behavior. Microsoft’s public entry does not, by itself, hand defenders a complete exploit recipe, and that absence matters. But the affected role is so fundamental that security teams should resist treating sparse disclosure as low significance.
The key editorial point is simple: a quiet DNS client RCE can be more operationally dangerous than a noisy server bug, because it tempts organizations to wait for proof-of-concept chatter before acting. By the time public exploit details arrive, the patch window has often already closed for the defenders and opened for everyone else.
The Report Confidence Language Is Doing More Work Than It Seems
The user-visible language around confidence is not decorative CVSS boilerplate. It describes how much faith the scoring system places in the existence of the vulnerability and in the reliability of the known technical details. In plain English, it asks whether this is rumor, credible research, or vendor-confirmed reality.For Microsoft vulnerabilities, the presence of an MSRC entry is itself meaningful. Microsoft is not merely aggregating gossip from a mailing list; it is assigning a CVE record to a Windows component and publishing it through the company’s security response process. Even when the advisory withholds root-cause detail, the vendor acknowledgement shifts the issue out of the realm of speculation.
That matters because “not enough detail” is often misread as “not enough risk.” In security operations, those are different things. A vulnerability can be real, patched, and serious while still being intentionally under-described to slow exploit development.
This is especially true for client-side network parsers. Microsoft and other vendors routinely avoid spelling out the precise malformed packet, response field, compression edge case, or memory handling flaw that triggers exploitation. That restraint frustrates defenders who want elegant detection logic, but it also denies attackers a ready-made map.
DNS Is Not Just Infrastructure; It Is an Ambient Input Stream
Windows systems consume DNS data constantly. Users do not need to open a suspicious attachment for the DNS Client to do work. Applications, services, background tasks, telemetry agents, security tools, software distribution platforms, and authentication flows all generate name lookups.That ambient quality is what makes DNS bugs unsettling. A vulnerability in a document parser usually needs a document. A vulnerability in a browser engine usually needs a page. A vulnerability in a DNS client may sit closer to the operating system’s reflexes, triggered as part of routine connectivity.
The practical risk depends on exploit preconditions Microsoft has not fully detailed in the provided advisory text. An attacker might need to influence a DNS response, operate a malicious DNS server, place themselves on-path, poison a lookup flow, or lure a target into resolving a domain under attacker control. Those differences matter enormously for real-world exploitability.
But from a defender’s perspective, none of those scenarios is far-fetched. Enterprise machines leave trusted networks. Users join guest networks. VPN split tunneling exists. Developers test against arbitrary domains. Malware already abuses DNS for command-and-control, staging, tunneling, and evasion. If a DNS response can also become a memory-corruption delivery vehicle, the line between “network noise” and “initial access” gets thinner.
The Client-Side Angle Changes Patch Priorities
Windows DNS vulnerabilities have historically drawn the most attention when they affect DNS Server, especially domain controllers. That instinct is understandable. A compromised DNS server can become a kingdom-level problem, and the 2020 SIGRed episode trained many administrators to view DNS RCE through the server lens.CVE-2026-41096 points elsewhere: the client. That changes the blast pattern. Instead of asking only which servers expose port 53, organizations need to ask which endpoints process potentially hostile name-resolution data and how quickly those endpoints receive cumulative updates.
For most Windows environments, the answer is “nearly all of them.” Even machines that use internal recursive resolvers still process DNS answers. Even clients behind secure web gateways still resolve names. Even highly managed enterprise endpoints may encounter untrusted DNS paths when off-network, before VPN establishment, or during captive portal negotiation.
This is why endpoint patch latency becomes the real control. The server team may patch a handful of recursive resolvers quickly, but workstation remediation is a campaign: rings, pilot groups, reboot enforcement, help desk exceptions, application compatibility checks, and laptop availability. A DNS Client RCE punishes organizations that have beautiful server hygiene and sluggish endpoint governance.
Sparse Technical Detail Is a Defensive Problem, Not a Comfort Blanket
The absence of public exploit detail cuts two ways. It may mean exploitation is hard, fragile, or dependent on conditions that are not common. It may also mean the issue is dangerous enough that Microsoft is deliberately limiting technical breadcrumbs until customers have had time to patch.Security teams should therefore avoid both panic and complacency. The useful stance is disciplined urgency. Treat the advisory as credible because it comes through MSRC, treat the component as broadly exposed because DNS is universal, and treat the missing root-cause detail as a reason to patch rather than a reason to defer.
The reporting-confidence metric reinforces this point. It is not an exploitability guarantee. It does not say attackers have working code. It does not say every Windows machine is trivially exploitable from the public internet. It says the vulnerability’s existence and known details have a credibility level that should inform urgency.
That distinction matters in executive communication. “Microsoft has confirmed a Windows DNS Client RCE” is a stronger and cleaner message than “there may be a DNS bug.” But “confirmed” should not be inflated into “actively exploited” unless Microsoft or credible telemetry says so. Good security writing, like good incident response, separates verified facts from plausible risk.
Where Attackers Would Look First
If attackers decide to study CVE-2026-41096, they will likely begin where defenders do: patch diffing. Once Microsoft ships updates, researchers and adversaries can compare old and new Windows binaries to identify changed code paths. In memory-safety bugs, that comparison can reveal the vulnerable routine even when the advisory is terse.DNS offers several attractive places for bug hunters. Parsers must handle compressed names, record types, lengths, encodings, caching behavior, malformed responses, retry logic, and edge cases created by decades of protocol evolution. The Windows DNS Client must also integrate with modern Windows features, enterprise policy, VPN behavior, NRPT rules, DNS-over-HTTPS settings, and name-resolution fallback mechanisms.
None of that proves where CVE-2026-41096 lives. But it explains why the category is fertile. Networking clients are not passive consumers of clean data; they are parsers of adversarial input from messy networks. Every parser is a bet that hostile input will be rejected safely.
For defenders, the likely attacker workflow is enough to shape timing. Public exploit code may not exist at disclosure. But patch availability starts the reverse-engineering clock. The safer assumption is that technical understanding increases after Patch Tuesday, not before it.
Detection Will Be Harder Than Patching
Many organizations want a detection query for every vulnerability. For a DNS Client RCE, that desire may collide with reality. If the exploit path involves a malformed DNS answer that crashes or corrupts client memory, ordinary DNS logs may show only a lookup and response, not the internal failure condition.Network security tools can sometimes help if exploit traffic becomes known. DNS inspection, endpoint detection telemetry, crash artifacts, suspicious child processes, and anomalous resolver behavior may all provide clues. But before public indicators emerge, defenders should not pretend they can reliably detect exploitation from standard recursive resolver logs alone.
This is where architectural controls matter. Enforcing trusted DNS resolvers, limiting arbitrary network DNS, using VPN policies that prevent unsafe resolution paths, and monitoring for clients that bypass corporate resolvers all reduce exposure. Those controls will not substitute for the Windows update, but they can reduce the number of ways a malicious response reaches a vulnerable parser.
The most practical interim control is boring: make sure clients receive the relevant cumulative update quickly and reboot. In Windows security, the reboot is often the forgotten half of remediation. A downloaded update that has not completed installation is not a patched endpoint.
Home Users Are Not the Main Story, but They Are Not Exempt
For home Windows users, the guidance is straightforward: install the latest Windows security updates and restart the machine. Most consumer systems receive cumulative updates through Windows Update, and the risk calculus is simpler than in enterprise environments. The user does not need to know which DNS server they use to benefit from the fix.Still, consumer exposure should not be dismissed. Home laptops move between routers, public Wi-Fi, school networks, travel hotspots, and ISP resolvers. A DNS Client issue is not limited to corporate intranets. If exploitation turns out to require malicious DNS responses, consumer machines can encounter those through compromised routers, hostile hotspots, or attacker-controlled domains.
The bigger challenge is communication. “DNS Client remote code execution” sounds abstract to non-specialists. The plain version is better: Windows is patching a bug in the component that handles website and service lookups, and a malicious network response could potentially be involved. Update and restart.
Microsoft’s consolidation of fixes into cumulative updates helps here. Users do not need to hunt for a standalone DNS patch. But that same consolidation can obscure urgency because one update looks much like another in the Windows Update interface.
Enterprise IT Should Treat This as an Endpoint Resilience Test
For enterprises, CVE-2026-41096 is a useful test of patch maturity. Not because every DNS Client RCE becomes a worm, and not because every RCE deserves emergency change-control theater, but because the affected surface is broad enough to expose weak points in endpoint operations.The first question is asset coverage. Are all supported Windows client versions in the patch system? Are remote laptops checking in? Are VDI images updated? Are gold images refreshed? Are offline or intermittently connected systems visible? Are security appliances and management tools reporting installation state or merely deployment attempt state?
The second question is reboot compliance. Windows cumulative updates frequently require a restart to complete. Enterprises that celebrate deployment percentages without measuring reboot completion are measuring intent, not remediation.
The third question is exception handling. Every organization has machines that cannot patch immediately: lab systems, regulated endpoints, operational technology jump hosts, training rooms, legacy application workstations, executive laptops stuck in travel mode. A DNS Client RCE should force those exceptions into daylight, because the machines least able to patch are often the ones least able to withstand compromise.
The Patch Tuesday Machine Still Has a Trust Problem
Microsoft’s security update process has improved enormously since the old bulletin era, but administrators still live with an awkward bargain. They need rapid patching because attackers reverse-engineer fixes. They also need caution because Windows updates can break VPNs, authentication, printing, BitLocker workflows, domain services, and business applications.That tension is not unique to CVE-2026-41096, but client networking bugs sharpen it. DNS is too central to ignore, and Windows endpoint fleets are too heterogeneous to patch blindly everywhere at once. The rational answer is not delay; it is controlled acceleration.
A mature organization should already have deployment rings that can move quickly: IT pilot, security-sensitive systems, broad business groups, and stragglers. If those rings cannot process a client-side RCE within days, the problem is not this CVE. The problem is that the patching model has been optimized for convenience rather than threat velocity.
There is also a transparency issue. Sparse advisories protect customers in one sense by withholding exploit clues. They frustrate customers in another by making it harder to prioritize. Microsoft’s challenge is to provide enough operational guidance for defenders without gifting attackers the missing exploit primitive.
The Windows DNS Lesson Hidden in This CVE
The concrete response to CVE-2026-41096 is patching, but the broader lesson is dependency awareness. Windows security is not just about browsers, Office documents, identity providers, and exposed servers. It is also about quiet operating-system services that process untrusted input as part of ordinary life.That is why defenders should inventory DNS behavior more seriously. Which resolvers do clients use on and off VPN? Is DNS-over-HTTPS permitted, blocked, or centrally managed? Do endpoint firewalls prevent direct DNS to the internet? Are split-tunnel rules allowing unmanaged resolution? Are guest Wi-Fi and corporate Wi-Fi separated cleanly? Does endpoint telemetry flag resolver changes?
These are not glamorous questions. They rarely make the board deck. But they determine whether a DNS client vulnerability is constrained to a managed path or sprayed across every network a user visits.
The same logic applies to developers and power users. Local DNS overrides, test resolvers, container networks, WSL environments, VPN clients, and security tools can complicate resolution behavior. The more custom the stack, the more important it is to verify that the underlying Windows host is patched rather than assuming the application layer is insulated.
The Practical Read From Redmond’s Sparse Signal
For now, the facts support a measured but firm response. Microsoft has a Windows DNS Client RCE entry under CVE-2026-41096. The advisory language around confidence indicates that the credibility of the vulnerability and its technical details is part of the scoring context. The public information available to ordinary defenders does not appear to include a full root-cause narrative or exploit walkthrough.That combination should lead to action, not theatrics. Patch supported Windows systems. Prioritize endpoints that roam, systems used by administrators, machines on untrusted networks, and any workstation class with delayed update behavior. Confirm reboots, not just update approvals.
Security teams should also watch for later MSRC revisions. Microsoft advisories can evolve as exploitability assessment changes, affected products are clarified, or active exploitation is observed. A CVE that begins as a terse entry can become a much more urgent operational story if public proof-of-concept code appears or exploitation telemetry emerges.
The right posture is to treat the first advisory as the start of the vulnerability lifecycle, not the end of it. Patch now, monitor later, and do not wait for a catchy name before deciding that DNS client code matters.
The Signal Administrators Should Not Miss in CVE-2026-41096
CVE-2026-41096 is not a reason to reinvent Windows security operations overnight. It is a reason to execute the basics with unusual discipline, because the affected component is everywhere and the public detail is limited.- Organizations should deploy Microsoft’s relevant Windows security updates promptly across supported client and server editions that include the affected DNS Client component.
- Administrators should verify completed installation and reboot status rather than relying only on update approval or download metrics.
- Security teams should prioritize roaming laptops, administrator workstations, VDI base images, and systems that frequently operate on untrusted networks.
- Network teams should review whether Windows clients can bypass managed resolvers, especially off VPN or on split-tunnel configurations.
- Defenders should monitor MSRC revisions and credible security research for changes in exploitability assessment, public proof-of-concept availability, or reports of active exploitation.
- Exception lists should be treated as risk registers, because unpatched Windows endpoints with unusual DNS behavior may become the hardest systems to protect later.
Source: MSRC Security Update Guide - Microsoft Security Response Center