Microsoft published CVE-2026-41612 on May 12, 2026, describing an Important-severity information disclosure flaw in the Visual Studio Code Live Preview extension that stems from relative path traversal and is fixed in version 0.4.19. The bug is not a dramatic remote-code-execution headline, and Microsoft says exploitation is less likely. But the vulnerability lands in exactly the kind of developer tooling that quietly handles local files, project paths, credentials, and internal application context. That makes this a reminder that the editor is no longer just an editor; it is part of the modern attack surface.
CVE-2026-41612 is, on paper, a contained flaw. Microsoft rates it Important rather than Critical, assigns it a CVSS 3.1 base score of 5.5, and classifies the impact as information disclosure. The advisory says the issue is a relative path traversal vulnerability in Visual Studio Code that could allow an unauthorized attacker to disclose information locally.
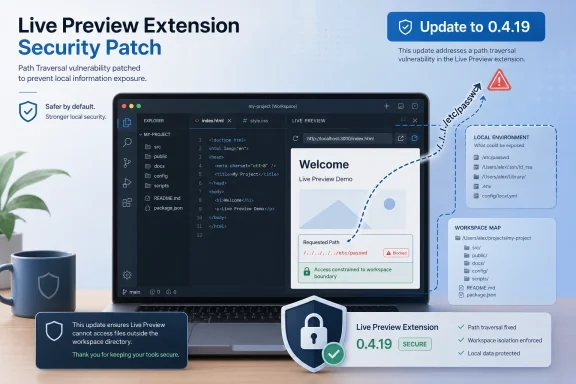
That phrasing matters. This is not Microsoft describing arbitrary code execution, privilege escalation, or a network worm. The vulnerable component is the Visual Studio Code Live Preview extension, and the fixed build is 0.4.19. The disclosed information is described specifically as unauthorized access to file-system information, including file path information.
Yet a developer workstation is not a normal endpoint. It is often a place where source code, local configuration files, environment variables, cloud credentials, test tokens, internal service names, and repository structure converge. A bug that only leaks “local” information can still matter if the local machine is a map of the organization.
The usual severity shorthand also obscures the practical risk. A CVSS 5.5 vulnerability may be reasonable to rank below the month’s exploited Windows zero-days, but that does not make it ignorable. In developer environments, information disclosure is often less about the first leak and more about what that leak enables next.
Path traversal is one of the oldest classes of application security bug because it exploits a very basic assumption: that a component can safely translate a user-controlled request into a file-system lookup. In web apps, this is the familiar problem of escaping a document root. In desktop developer tooling, the same class of mistake can become harder to reason about because the tool is intentionally designed to browse, preview, serve, and transform local project content.
Live Preview is exactly the sort of extension where the boundary can blur. Its job is to show web content from a workspace in a convenient preview loop. That workflow is useful because it shortens the distance between editing and seeing results, but the security model has to be careful about what project content can trigger and what files can be reached.
Microsoft’s advisory does not publish a step-by-step exploit, and that restraint is normal for a newly fixed vulnerability. But the CVSS vector gives useful shape to the issue. The attack vector is local, attack complexity is low, no privileges are required, and user interaction is required. In other words, the attacker does not need an account on the system, but the user has to do something that triggers the payload in the application.
That is the familiar developer-tool trap. The attacker may not need to log in if the workflow itself imports the attacker’s content. A repository, sample project, generated page, preview target, or crafted workspace can become the delivery mechanism if the vulnerable component processes it in the right way.
Developers clone repositories from strangers. They open proof-of-concept projects. They test templates, inspect bug reports, review pull requests, run local preview servers, and render documentation. The habits that make open source and rapid prototyping productive also create a large surface for “please open this” attacks.
That is why the “UI:R” part of the CVSS string should not lull teams into complacency. For a finance user, opening an unexpected attachment might be an anomaly. For a developer, opening someone else’s project is the job.
The advisory’s exploitability assessment says exploitation is less likely, and Microsoft says the vulnerability was not publicly disclosed or exploited at the time of publication. That is important. There is no need to invent panic where the vendor has not reported active attacks. But “less likely” is not the same as “irrelevant,” particularly when the fix is available and the exposed component is an extension rather than the base operating system.
The more useful question for administrators is not whether this bug is currently being exploited at scale. It is whether their fleet knows which VS Code extensions are installed, whether those extensions update automatically, and whether developer machines are managed with the same seriousness as ordinary enterprise endpoints.
That distinction is easy to miss. The same advisory also marks Exploit Code Maturity as Unproven, meaning Microsoft is not saying public exploit code exists or that exploitation is happening in the wild. The result is a common but awkward middle state: the bug is real, the fix is real, but weaponization has not been observed.
For defenders, that middle state is where patch management earns its keep. Waiting until exploit code appears is a losing strategy because the disclosure itself narrows the search space for attackers. A confirmed path traversal flaw in a specific extension, with a fixed version number and a bounded impact statement, is enough for skilled researchers and adversaries to start diffing, probing, and reproducing.
That does not mean every organization should drop everything for this CVE. It means the vulnerability should be treated as an authenticated piece of risk, not as rumor. The confirmed status answers one question: yes, there is something to fix.
The temporal score of 4.8 reflects the availability of an official fix and the unproven exploit maturity. That is exactly how scoring should work. It lowers urgency compared with an exploited zero-day but still makes delay harder to justify when remediation is straightforward.
That extension model changes the security equation. The editor is not simply reading text. It may execute tasks, host local services, parse untrusted files, render webviews, communicate with remote APIs, and interact with the local file system. Extensions often sit at the boundary between code and execution, which is exactly where security bugs become consequential.
CVE-2026-41612 affects Microsoft’s own Live Preview extension, not some abandoned third-party package with a handful of installs. That makes the advisory more significant as a signal. Even first-party developer conveniences require the same risk treatment as any other software component.
The practical challenge is that many enterprises still do not have mature extension inventory. They can tell you which Windows build is deployed, which Defender policy is active, and which Office channel a machine is on. They may not be able to say, with confidence, which VS Code extensions are installed across developer workstations or which versions are active.
That blind spot is increasingly untenable. If the editor can preview, serve, render, and manipulate local project content, then its extensions belong in asset management and vulnerability management. Treating them as personal preference is a luxury that modern supply-chain risk no longer allows.
VS Code extensions can be installed per user, synced through profiles, side-loaded from VSIX files, pulled from the Marketplace, or embedded into developer images. Some developers run the stable VS Code build, others run Insiders, and many use remote development scenarios where the extension topology differs between local and remote environments. That complexity is operationally normal, but it makes vulnerability response messy.
The advisory marks customer action as required. That is a quiet but important phrase. It means administrators should not assume this is handled solely by Windows Update or the monthly cumulative update process. The relevant unit of remediation is the extension package.
This is where enterprise policy should catch up with developer reality. If an organization permits VS Code, it should have a view of extension governance. That does not require locking every developer into a sterile configuration, but it does require knowing which extensions are allowed, which are blocked, which update channel they follow, and how exceptions are audited.
The Live Preview fix is also a good test case for software inventory. If your security team cannot answer whether 0.4.19 is deployed, the problem is bigger than this one CVE. The vulnerability becomes a diagnostic: not just “are we exposed?” but “can we tell?”
A local path can reveal usernames, project names, internal repository structures, customer names embedded in directories, build layouts, technology stacks, or locations of configuration files. In targeted attacks, that context can sharpen phishing, help craft follow-on payloads, or make lateral movement more efficient. Attackers do not always need the crown jewels in the first step; sometimes they need a map.
The confidentiality impact is marked High, while integrity and availability are marked None. That combination tells the story. The vulnerability is not about changing files or crashing the application. It is about learning something the attacker should not be able to learn.
Security programs often undervalue that category because the harm is indirect. An exploit that pops calc is easy to demonstrate. An exploit that reveals paths or file-system information may look unimpressive until it is chained with social engineering, token theft, misconfigured local servers, or another bug in the development stack.
This is particularly relevant for developer endpoints because they tend to contain secrets in places organizations wish they did not. Even mature teams still find credentials in
Modern development workflows import code from the internet by design. Package managers fetch transitive dependencies. AI tools generate snippets. CI configurations are copied across repositories. Documentation previews render markup. Local servers expose development builds. Extensions glue these pieces together.
CVE-2026-41612 fits into that broader pattern because it depends on a user triggering a payload inside a trusted development application. The vulnerability’s local attack vector does not make it harmless; it reflects the fact that the attack rides through the developer’s workflow rather than around it.
The security response should not be to tell developers never to open unknown code. That is unrealistic and, frankly, useless. The better response is layered containment: isolate untrusted projects, reduce ambient credentials, keep extensions current, avoid running unnecessary preview services, and enforce sensible workspace trust settings.
Workspace Trust in VS Code was introduced to address exactly this class of problem: code should not automatically become trusted because it is opened in a powerful editor. But trust prompts and policies only work when teams understand why they exist. If developers reflexively click through them to get work done, the control becomes theater.
That shift creates friction for IT operations. Windows Update is centralized, mature, and well-instrumented. Extension updates are more fragmented. They may be governed by application settings, user behavior, network access to marketplaces, corporate images, or manual installation habits. A small extension update can fall between teams: not quite desktop engineering, not quite AppSec, not quite vulnerability management.
But attackers do not care which internal team owns the component. If a VS Code extension can expose local information, it sits on a system that may also have access to source repositories, internal services, cloud consoles, signing tools, and deployment pipelines. Developer endpoints deserve the same patch discipline as domain controllers in one respect: they are leverage points.
The fix here is not glamorous. Update Live Preview to 0.4.19. Confirm the update. Check whether the extension is broadly deployed. Review whether untrusted projects are being opened with unnecessary local preview capabilities. These are mundane tasks, but mundane tasks are where most enterprise security succeeds or fails.
The disclosure also highlights a useful triage pattern. When a vulnerability is Important, not exploited, and fixed, the right answer is not emergency mode. It is fast, documented remediation with verification. The goal is to close the window before exploit maturity changes.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 The Vulnerability Is Modest Until You Notice Where It Lives
The Vulnerability Is Modest Until You Notice Where It Lives
CVE-2026-41612 is, on paper, a contained flaw. Microsoft rates it Important rather than Critical, assigns it a CVSS 3.1 base score of 5.5, and classifies the impact as information disclosure. The advisory says the issue is a relative path traversal vulnerability in Visual Studio Code that could allow an unauthorized attacker to disclose information locally.That phrasing matters. This is not Microsoft describing arbitrary code execution, privilege escalation, or a network worm. The vulnerable component is the Visual Studio Code Live Preview extension, and the fixed build is 0.4.19. The disclosed information is described specifically as unauthorized access to file-system information, including file path information.
Yet a developer workstation is not a normal endpoint. It is often a place where source code, local configuration files, environment variables, cloud credentials, test tokens, internal service names, and repository structure converge. A bug that only leaks “local” information can still matter if the local machine is a map of the organization.
The usual severity shorthand also obscures the practical risk. A CVSS 5.5 vulnerability may be reasonable to rank below the month’s exploited Windows zero-days, but that does not make it ignorable. In developer environments, information disclosure is often less about the first leak and more about what that leak enables next.
Path Traversal Is Old, but Developer Tooling Gives It New Rooms to Explore
The weakness behind CVE-2026-41612 is path traversal, mapped by Microsoft to CWE-23 and CWE-22. In plain English, that means software may not be properly constraining a requested path to the directory it intended to expose. If an attacker can influence that path, the application may reveal files or path data outside the expected boundary.Path traversal is one of the oldest classes of application security bug because it exploits a very basic assumption: that a component can safely translate a user-controlled request into a file-system lookup. In web apps, this is the familiar problem of escaping a document root. In desktop developer tooling, the same class of mistake can become harder to reason about because the tool is intentionally designed to browse, preview, serve, and transform local project content.
Live Preview is exactly the sort of extension where the boundary can blur. Its job is to show web content from a workspace in a convenient preview loop. That workflow is useful because it shortens the distance between editing and seeing results, but the security model has to be careful about what project content can trigger and what files can be reached.
Microsoft’s advisory does not publish a step-by-step exploit, and that restraint is normal for a newly fixed vulnerability. But the CVSS vector gives useful shape to the issue. The attack vector is local, attack complexity is low, no privileges are required, and user interaction is required. In other words, the attacker does not need an account on the system, but the user has to do something that triggers the payload in the application.
That is the familiar developer-tool trap. The attacker may not need to log in if the workflow itself imports the attacker’s content. A repository, sample project, generated page, preview target, or crafted workspace can become the delivery mechanism if the vulnerable component processes it in the right way.
“User Interaction Required” Is Not Much Comfort in a Git-Clone World
Security teams sometimes treat user interaction as a meaningful brake on exploitation, and in many consumer contexts it is. A vulnerability that requires someone to open a file or click a link is different from one that can be fired unauthenticated across the network. But development culture is built around interacting with untrusted material.Developers clone repositories from strangers. They open proof-of-concept projects. They test templates, inspect bug reports, review pull requests, run local preview servers, and render documentation. The habits that make open source and rapid prototyping productive also create a large surface for “please open this” attacks.
That is why the “UI:R” part of the CVSS string should not lull teams into complacency. For a finance user, opening an unexpected attachment might be an anomaly. For a developer, opening someone else’s project is the job.
The advisory’s exploitability assessment says exploitation is less likely, and Microsoft says the vulnerability was not publicly disclosed or exploited at the time of publication. That is important. There is no need to invent panic where the vendor has not reported active attacks. But “less likely” is not the same as “irrelevant,” particularly when the fix is available and the exposed component is an extension rather than the base operating system.
The more useful question for administrators is not whether this bug is currently being exploited at scale. It is whether their fleet knows which VS Code extensions are installed, whether those extensions update automatically, and whether developer machines are managed with the same seriousness as ordinary enterprise endpoints.
The Confirmed Report Raises the Priority Above the Score
The user-supplied context highlights Microsoft’s Report Confidence metric, and that is the right lens for this vulnerability. CVE-2026-41612 is marked Confirmed. In CVSS terms, that means the vulnerability’s existence and technical credibility are not merely speculative.That distinction is easy to miss. The same advisory also marks Exploit Code Maturity as Unproven, meaning Microsoft is not saying public exploit code exists or that exploitation is happening in the wild. The result is a common but awkward middle state: the bug is real, the fix is real, but weaponization has not been observed.
For defenders, that middle state is where patch management earns its keep. Waiting until exploit code appears is a losing strategy because the disclosure itself narrows the search space for attackers. A confirmed path traversal flaw in a specific extension, with a fixed version number and a bounded impact statement, is enough for skilled researchers and adversaries to start diffing, probing, and reproducing.
That does not mean every organization should drop everything for this CVE. It means the vulnerability should be treated as an authenticated piece of risk, not as rumor. The confirmed status answers one question: yes, there is something to fix.
The temporal score of 4.8 reflects the availability of an official fix and the unproven exploit maturity. That is exactly how scoring should work. It lowers urgency compared with an exploited zero-day but still makes delay harder to justify when remediation is straightforward.
Microsoft’s Extension Model Is Both the Strength and the Weakness
Visual Studio Code became the default editor for much of the software industry because it is lightweight, cross-platform, and extensible. The same extension ecosystem that made it useful also made it sprawling. Developers rarely run a pristine editor; they run a personalized stack of language servers, preview tools, linters, formatters, AI assistants, container integrations, debuggers, and build helpers.That extension model changes the security equation. The editor is not simply reading text. It may execute tasks, host local services, parse untrusted files, render webviews, communicate with remote APIs, and interact with the local file system. Extensions often sit at the boundary between code and execution, which is exactly where security bugs become consequential.
CVE-2026-41612 affects Microsoft’s own Live Preview extension, not some abandoned third-party package with a handful of installs. That makes the advisory more significant as a signal. Even first-party developer conveniences require the same risk treatment as any other software component.
The practical challenge is that many enterprises still do not have mature extension inventory. They can tell you which Windows build is deployed, which Defender policy is active, and which Office channel a machine is on. They may not be able to say, with confidence, which VS Code extensions are installed across developer workstations or which versions are active.
That blind spot is increasingly untenable. If the editor can preview, serve, render, and manipulate local project content, then its extensions belong in asset management and vulnerability management. Treating them as personal preference is a luxury that modern supply-chain risk no longer allows.
The Patch Is Simple; Proving It Landed May Not Be
Microsoft lists the security update for the Visual Studio Code Live Preview extension and identifies 0.4.19 as the fixed build. For an individual developer, the remediation path is simple: update the extension. For a managed organization, the harder part is verifying that the update actually reached the machines that matter.VS Code extensions can be installed per user, synced through profiles, side-loaded from VSIX files, pulled from the Marketplace, or embedded into developer images. Some developers run the stable VS Code build, others run Insiders, and many use remote development scenarios where the extension topology differs between local and remote environments. That complexity is operationally normal, but it makes vulnerability response messy.
The advisory marks customer action as required. That is a quiet but important phrase. It means administrators should not assume this is handled solely by Windows Update or the monthly cumulative update process. The relevant unit of remediation is the extension package.
This is where enterprise policy should catch up with developer reality. If an organization permits VS Code, it should have a view of extension governance. That does not require locking every developer into a sterile configuration, but it does require knowing which extensions are allowed, which are blocked, which update channel they follow, and how exceptions are audited.
The Live Preview fix is also a good test case for software inventory. If your security team cannot answer whether 0.4.19 is deployed, the problem is bigger than this one CVE. The vulnerability becomes a diagnostic: not just “are we exposed?” but “can we tell?”
Information Disclosure Is Often the Opening Move, Not the Endgame
The advisory says the disclosed information includes file path information. On its face, that sounds limited. File paths are not passwords, private keys, or source code. But paths can be reconnaissance.A local path can reveal usernames, project names, internal repository structures, customer names embedded in directories, build layouts, technology stacks, or locations of configuration files. In targeted attacks, that context can sharpen phishing, help craft follow-on payloads, or make lateral movement more efficient. Attackers do not always need the crown jewels in the first step; sometimes they need a map.
The confidentiality impact is marked High, while integrity and availability are marked None. That combination tells the story. The vulnerability is not about changing files or crashing the application. It is about learning something the attacker should not be able to learn.
Security programs often undervalue that category because the harm is indirect. An exploit that pops calc is easy to demonstrate. An exploit that reveals paths or file-system information may look unimpressive until it is chained with social engineering, token theft, misconfigured local servers, or another bug in the development stack.
This is particularly relevant for developer endpoints because they tend to contain secrets in places organizations wish they did not. Even mature teams still find credentials in
.env files, test configs, shell histories, package manager caches, local certificates, and generated artifacts. A path traversal bug does not have to disclose all of those directly to matter; it only has to help an attacker understand where to look next.The Real Risk Is the Normalization of Local Trust
For years, endpoint security models treated local developer activity as inherently trusted. If the user opened the project, ran the preview, or launched the tool, the assumption was that the activity belonged to the user. That model looks increasingly brittle.Modern development workflows import code from the internet by design. Package managers fetch transitive dependencies. AI tools generate snippets. CI configurations are copied across repositories. Documentation previews render markup. Local servers expose development builds. Extensions glue these pieces together.
CVE-2026-41612 fits into that broader pattern because it depends on a user triggering a payload inside a trusted development application. The vulnerability’s local attack vector does not make it harmless; it reflects the fact that the attack rides through the developer’s workflow rather than around it.
The security response should not be to tell developers never to open unknown code. That is unrealistic and, frankly, useless. The better response is layered containment: isolate untrusted projects, reduce ambient credentials, keep extensions current, avoid running unnecessary preview services, and enforce sensible workspace trust settings.
Workspace Trust in VS Code was introduced to address exactly this class of problem: code should not automatically become trusted because it is opened in a powerful editor. But trust prompts and policies only work when teams understand why they exist. If developers reflexively click through them to get work done, the control becomes theater.
This Is a Developer Workstation Patch Tuesday Problem
Patch Tuesday is usually discussed through the lens of Windows, Office, Exchange, SQL Server, and Azure. CVE-2026-41612 is a reminder that Microsoft’s security update ecosystem now reaches into developer tooling and Marketplace-distributed components. The center of gravity has shifted from the operating system alone to the full productivity and engineering stack.That shift creates friction for IT operations. Windows Update is centralized, mature, and well-instrumented. Extension updates are more fragmented. They may be governed by application settings, user behavior, network access to marketplaces, corporate images, or manual installation habits. A small extension update can fall between teams: not quite desktop engineering, not quite AppSec, not quite vulnerability management.
But attackers do not care which internal team owns the component. If a VS Code extension can expose local information, it sits on a system that may also have access to source repositories, internal services, cloud consoles, signing tools, and deployment pipelines. Developer endpoints deserve the same patch discipline as domain controllers in one respect: they are leverage points.
The fix here is not glamorous. Update Live Preview to 0.4.19. Confirm the update. Check whether the extension is broadly deployed. Review whether untrusted projects are being opened with unnecessary local preview capabilities. These are mundane tasks, but mundane tasks are where most enterprise security succeeds or fails.
The disclosure also highlights a useful triage pattern. When a vulnerability is Important, not exploited, and fixed, the right answer is not emergency mode. It is fast, documented remediation with verification. The goal is to close the window before exploit maturity changes.
The Small VS Code Bug That Tests a Bigger Security Program
CVE-2026-41612 should be handled as a manageable vulnerability, but it should also trigger a broader look at developer tooling hygiene. If the organization cannot inventory extensions, cannot enforce updates, or cannot separate trusted and untrusted workspaces, the next advisory may be harder to absorb.- Microsoft disclosed CVE-2026-41612 on May 12, 2026, as an Important information disclosure vulnerability affecting the Visual Studio Code Live Preview extension.
- The vulnerability is tied to relative path traversal and is fixed in Live Preview version 0.4.19.
- Microsoft says exploitation was not publicly disclosed or observed at publication time, and its assessment is that exploitation is less likely.
- The CVSS vector still deserves attention because no privileges are required, attack complexity is low, user interaction is required, and confidentiality impact is high.
- Administrators should verify extension-level remediation rather than assuming the issue is resolved by ordinary Windows patching.
- Security teams should treat VS Code extensions as managed software assets, especially on machines with access to source code, credentials, and deployment infrastructure.
Source: MSRC Security Update Guide - Microsoft Security Response Center