CVE-2026-43308 is a newly published Linux kernel vulnerability, recorded by NVD on May 8, 2026, covering a Btrfs fix that replaces a kernel-crashing
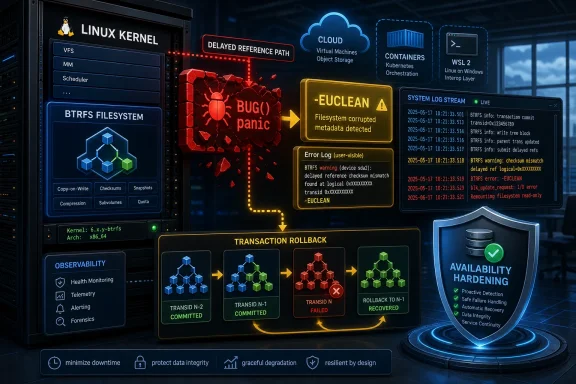
The kernel change behind CVE-2026-43308 is not a glamorous exploit write-up. There is no public proof-of-concept in the record, no dramatic privilege-escalation chain, and no NVD severity score assigned at publication time. The description is almost austere: Btrfs encountered an unexpected delayed reference type, and instead of calling
That plainness is the point. In kernel engineering, a forced crash is sometimes a useful development-time assertion, but it is a terrible production-time recovery strategy when the system has enough context to fail gracefully. A
The fix changes that contract. If the delayed-reference machinery sees a type it does not expect, Btrfs now returns
For WindowsForum readers, the Microsoft Security Response Center listing may be the strange part. This is a Linux kernel CVE, not a Windows filesystem bug. But Microsoft now ships, hosts, integrates, secures, and bills for an enormous amount of Linux through Azure, WSL, container services, Defender coverage, and customer workloads, so Linux kernel CVEs increasingly surface in Microsoft-facing security channels even when the vulnerable code lives upstream.
A filesystem is allowed to reject nonsense. It is allowed to abort a transaction if metadata invariants no longer hold. It is allowed, and sometimes required, to remount read-only or return hard errors when continuing would risk corruption. What it should not do, unless there is truly no safe alternative, is crash the entire kernel because one internal enum-like value fell outside the expected set.
That distinction matters because Btrfs delayed references are part of the filesystem’s accounting machinery. Btrfs is copy-on-write, which means metadata updates are not just in-place scribbles over old structures. The filesystem tracks references to extents, records changes, batches work, and later resolves those delayed references into durable metadata updates.
The
That is a security improvement because availability is part of security. A local user, a mounted workload, a crafted filesystem image, a hardware-induced corruption event, or a separate kernel bug that perturbs memory should not automatically get the power to panic a production host if the filesystem can instead fail the operation and keep the kernel alive.
Delayed references are one of those corner cases that reveal the cost of doing interesting things. When a filesystem can share extents between snapshots, clone data, and defer metadata work until transaction commit, it needs a sophisticated system to decide who references what and when those references are created or destroyed. That machinery is not as visible as a mount option or a snapshot command, but it is central to Btrfs’ identity.
CVE-2026-43308 does not say that Btrfs is broadly unsafe. It says that one defensive branch in a complicated metadata pipeline used a too-violent response. The difference is important. Mature codebases often become safer not only by fixing data-corruption bugs, but by replacing developer-era traps with production-grade containment.
That is also why the patch looks modest. It does not redesign delayed refs. It does not add a new validation framework. It simply treats an unexpected delayed-reference node type as filesystem damage or inconsistency, logs it, and returns an error that the broader Btrfs transaction machinery already knows how to handle.
The best filesystem fixes often look like this. They do not make the happy path faster or add a feature that appears in release notes. They make the unhappy path less catastrophic.
Linux has been steadily moving away from casual uses of
A kernel panic is sometimes defensible. If continuing would corrupt memory, expose secrets, or leave core scheduler state incoherent, halting may be the least bad option. But a filesystem-specific unexpected type in a path that can return errors is a different kind of event. It is serious, but it is not automatically a license to take down every VM, container, database, SSH session, and user process on the host.
That is especially true in cloud and virtualization environments. A kernel crash in a single-purpose test box is annoying. A kernel crash in a storage node, CI worker, container host, or developer workstation running nested workloads can become a cascading operational incident. The same local filesystem failure that might once have been “just reboot” can now interrupt pipelines, corrupt higher-level application state, and trigger automated recovery systems.
Returning
That is the mature posture. Crash when you must. Contain when you can.
Security teams should resist both extremes. It is premature to treat CVE-2026-43308 like a known remote-code-execution emergency. The record does not support that. But it is also lazy to dismiss it because no base score is present. An unscored kernel denial-of-service issue can still matter if it affects a fleet where local workloads, untrusted users, removable media, disk images, or tenant-controlled data interact with Btrfs.
The likely impact class is availability. The old behavior could turn an unexpected delayed ref type into a kernel panic. The new behavior makes Btrfs report an error and fail the transaction. That still may leave the affected filesystem in an error state, and it may still disrupt the workload using it, but it avoids the broader blast radius of a full host crash.
In practical security work, blast radius is often the whole story. If a filesystem inconsistency can be confined to one mount, one transaction, or one workload, operations teams can recover with targeted intervention. If it panics the kernel, every workload on that machine becomes collateral damage.
That is why this CVE deserves attention even without a score. Not panic, not theatrics, but attention.
Microsoft’s security ecosystem reflects that reality. A Linux kernel CVE can matter to Microsoft customers even if no Windows kernel component is affected. It may matter because of Azure images, appliance-like products, managed services, container hosts, or security products that inventory vulnerabilities across heterogeneous fleets.
WSL adds another wrinkle, though not every upstream Linux filesystem issue maps neatly to WSL exposure. Typical WSL2 distributions live inside virtual disks and use a Microsoft-provided kernel, while Btrfs is not the default filesystem path most Windows users encounter. Still, developers who attach disks, experiment with filesystems, run custom kernels, or maintain Linux-heavy workflows on Windows-adjacent systems should understand why these records appear in Microsoft channels.
For enterprise IT, the lesson is less about this single CVE than about asset classification. If your vulnerability program only maps Microsoft advisories to Windows desktops and servers, it is already behind the shape of the modern estate. The Linux kernel is part of the Microsoft customer attack surface now, not because Microsoft owns Linux, but because Microsoft’s customers run it everywhere.
That makes the boring plumbing of kernel filesystems relevant to Windows shops. The cloud made everyone a Linux administrator, whether they wanted the title or not.
The fix creates a filesystem-info local variable, sets the return value to
That matters for troubleshooting. A panic gives you a stack trace if you are lucky and configured for it. A structured filesystem error gives administrators a better chance to correlate the event with a device, mount, workload, transaction abort, or metadata problem. It also lets the system remain alive long enough for monitoring agents, logging daemons, and orchestration layers to capture useful state.
There is a quiet design principle here: when recovery is possible, diagnostics are better than drama. A crashing assertion may prove that a developer’s assumption was violated, but a logged error helps an operator decide what to do next.
The use of
Btrfs is common in places that do not always look like traditional servers. It appears on Linux desktops, developer workstations, NAS-style systems, backup hosts, container platforms, lab machines, and distributions that use snapshots heavily. It may also appear in appliance images where the administrator rarely thinks about the underlying filesystem unless something goes wrong.
The risk is highest where untrusted or semi-trusted users can influence filesystem state. Multi-user Linux systems, shared build hosts, CI runners, storage labs, and systems that mount externally supplied disk images deserve more attention than a single-user hobby machine with full-disk backups. That does not mean the latter should ignore kernel updates, only that prioritization should follow exposure.
Administrators should also avoid magical thinking about Btrfs repair commands. If a system logs delayed-reference failures or remounts a Btrfs filesystem read-only, the safest first move is usually to preserve evidence, verify backups, check hardware health, and review kernel versions before attempting invasive repair. Filesystem repair is not a ritual; it is surgery.
The patch changes a panic into an error, but it does not make underlying corruption harmless. If you hit this path, your next concern is not “great, the host stayed up.” It is “why did Btrfs see an impossible delayed-reference type in the first place?”
The kernel version is more dramatic because the process is the operating system itself. But similar mistakes occur in databases, message queues, storage controllers, authentication services, and distributed systems. Fatal assertions are seductive because they simplify reasoning. They are dangerous because production environments are where impossible states go to become tickets.
The better design is not to ignore impossible states. It is to decide what scope of failure is justified. Can the operation fail? Can the transaction abort? Can the affected tenant be isolated? Can the subsystem degrade? Can the service shed load? Each smaller containment boundary is a win.
This is why filesystem work often feels conservative. Btrfs cannot simply continue as though metadata invariants do not matter. But it can choose the narrowest safe failure mode. In this case, upstream decided the narrowest safe failure mode was an error return and log message, not a kernel panic.
That is a design lesson worth carrying into every layer of the stack.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
BUG() in run_one_delayed_ref() with ordinary error handling and logging when an unexpected delayed-reference type appears. That sounds almost comically small: one filesystem path, one defensive branch, one panic avoided. But the significance is larger than the patch size, because modern infrastructure is full of Linux kernels running under Windows-adjacent management, cloud platforms, WSL workflows, NAS appliances, and developer machines where “the kernel crashed because the filesystem saw something surprising” is no longer an acceptable failure mode.
 A Tiny Btrfs Patch Carries a Very Modern Security Lesson
A Tiny Btrfs Patch Carries a Very Modern Security Lesson
The kernel change behind CVE-2026-43308 is not a glamorous exploit write-up. There is no public proof-of-concept in the record, no dramatic privilege-escalation chain, and no NVD severity score assigned at publication time. The description is almost austere: Btrfs encountered an unexpected delayed reference type, and instead of calling BUG(), it should return an error and emit a diagnostic message.That plainness is the point. In kernel engineering, a forced crash is sometimes a useful development-time assertion, but it is a terrible production-time recovery strategy when the system has enough context to fail gracefully. A
BUG() is not a polite complaint; it is the kernel deciding the situation is unrecoverable and taking the machine down with it.The fix changes that contract. If the delayed-reference machinery sees a type it does not expect, Btrfs now returns
-EUCLEAN and logs the unexpected type, allowing the existing transaction-abort path to do the work that production systems actually need: contain the damage, preserve as much state as possible, and avoid turning a filesystem inconsistency into a whole-system outage.For WindowsForum readers, the Microsoft Security Response Center listing may be the strange part. This is a Linux kernel CVE, not a Windows filesystem bug. But Microsoft now ships, hosts, integrates, secures, and bills for an enormous amount of Linux through Azure, WSL, container services, Defender coverage, and customer workloads, so Linux kernel CVEs increasingly surface in Microsoft-facing security channels even when the vulnerable code lives upstream.
The Crash Was the Vulnerability, Not Just the Symptom
The tempting way to read CVE-2026-43308 is to shrug: an unexpected internal type reaches a defensive assertion, the kernel panics, and the patch replaces that panic with a logged error. That sounds like cleanup, not security. Yet denial-of-service vulnerabilities often live exactly in that gray zone between correctness and survivability.A filesystem is allowed to reject nonsense. It is allowed to abort a transaction if metadata invariants no longer hold. It is allowed, and sometimes required, to remount read-only or return hard errors when continuing would risk corruption. What it should not do, unless there is truly no safe alternative, is crash the entire kernel because one internal enum-like value fell outside the expected set.
That distinction matters because Btrfs delayed references are part of the filesystem’s accounting machinery. Btrfs is copy-on-write, which means metadata updates are not just in-place scribbles over old structures. The filesystem tracks references to extents, records changes, batches work, and later resolves those delayed references into durable metadata updates.
The
run_one_delayed_ref() path is therefore not decorative code. It sits in the machinery that reconciles filesystem intent with on-disk state. If that machinery hits an impossible case, the old answer was to stop everything. The new answer is to report the inconsistency and hand the failure to transaction-level error handling.That is a security improvement because availability is part of security. A local user, a mounted workload, a crafted filesystem image, a hardware-induced corruption event, or a separate kernel bug that perturbs memory should not automatically get the power to panic a production host if the filesystem can instead fail the operation and keep the kernel alive.
Btrfs Keeps Finding the Edges of Its Own Ambition
Btrfs has always been ambitious in a way that invites both admiration and scrutiny. It wants snapshots, checksumming, subvolumes, send/receive, compression, RAID-like profiles, reflinks, quotas, and copy-on-write semantics in one filesystem. That ambition is why distributions and power users keep returning to it, and also why its bug history is full of intricate corner cases.Delayed references are one of those corner cases that reveal the cost of doing interesting things. When a filesystem can share extents between snapshots, clone data, and defer metadata work until transaction commit, it needs a sophisticated system to decide who references what and when those references are created or destroyed. That machinery is not as visible as a mount option or a snapshot command, but it is central to Btrfs’ identity.
CVE-2026-43308 does not say that Btrfs is broadly unsafe. It says that one defensive branch in a complicated metadata pipeline used a too-violent response. The difference is important. Mature codebases often become safer not only by fixing data-corruption bugs, but by replacing developer-era traps with production-grade containment.
That is also why the patch looks modest. It does not redesign delayed refs. It does not add a new validation framework. It simply treats an unexpected delayed-reference node type as filesystem damage or inconsistency, logs it, and returns an error that the broader Btrfs transaction machinery already knows how to handle.
The best filesystem fixes often look like this. They do not make the happy path faster or add a feature that appears in release notes. They make the unhappy path less catastrophic.
BUG() Is a Blunt Instrument in a World of Persistent Services
Linux has been steadily moving away from casual uses of BUG() and BUG_ON() in code paths where recovery is possible. That does not mean kernel developers have gone soft on invariants. It means they have learned, often painfully, that “this should never happen” is not the same as “panic the machine if it does.”A kernel panic is sometimes defensible. If continuing would corrupt memory, expose secrets, or leave core scheduler state incoherent, halting may be the least bad option. But a filesystem-specific unexpected type in a path that can return errors is a different kind of event. It is serious, but it is not automatically a license to take down every VM, container, database, SSH session, and user process on the host.
That is especially true in cloud and virtualization environments. A kernel crash in a single-purpose test box is annoying. A kernel crash in a storage node, CI worker, container host, or developer workstation running nested workloads can become a cascading operational incident. The same local filesystem failure that might once have been “just reboot” can now interrupt pipelines, corrupt higher-level application state, and trigger automated recovery systems.
Returning
-EUCLEAN is not sweeping the problem under the rug. It is an explicit signal that the filesystem encountered a structure that should be treated as corrupt or inconsistent. The difference is that the signal travels through an error path instead of detonating the kernel.That is the mature posture. Crash when you must. Contain when you can.
The Absence of a Score Is Not the Absence of Risk
At publication, the NVD entry had not assigned CVSS 4.0, CVSS 3.x, or CVSS 2.0 scores. That is common for freshly published kernel CVEs, especially those flowing from upstream Linux security automation and stable-branch backports. It also creates a familiar problem for administrators: the vulnerability exists in feeds before the risk has been fully normalized by scoring systems.Security teams should resist both extremes. It is premature to treat CVE-2026-43308 like a known remote-code-execution emergency. The record does not support that. But it is also lazy to dismiss it because no base score is present. An unscored kernel denial-of-service issue can still matter if it affects a fleet where local workloads, untrusted users, removable media, disk images, or tenant-controlled data interact with Btrfs.
The likely impact class is availability. The old behavior could turn an unexpected delayed ref type into a kernel panic. The new behavior makes Btrfs report an error and fail the transaction. That still may leave the affected filesystem in an error state, and it may still disrupt the workload using it, but it avoids the broader blast radius of a full host crash.
In practical security work, blast radius is often the whole story. If a filesystem inconsistency can be confined to one mount, one transaction, or one workload, operations teams can recover with targeted intervention. If it panics the kernel, every workload on that machine becomes collateral damage.
That is why this CVE deserves attention even without a score. Not panic, not theatrics, but attention.
Microsoft’s Listing Is a Reminder That Linux Is Now Part of the Windows Estate
The MSRC page for CVE-2026-43308 may surprise people who still divide the world into Windows vulnerabilities over here and Linux vulnerabilities over there. That boundary has been eroding for years. Windows administrators increasingly manage Linux guests in Hyper-V, Linux containers in build systems, Linux nodes in Azure, and WSL distributions on developer endpoints.Microsoft’s security ecosystem reflects that reality. A Linux kernel CVE can matter to Microsoft customers even if no Windows kernel component is affected. It may matter because of Azure images, appliance-like products, managed services, container hosts, or security products that inventory vulnerabilities across heterogeneous fleets.
WSL adds another wrinkle, though not every upstream Linux filesystem issue maps neatly to WSL exposure. Typical WSL2 distributions live inside virtual disks and use a Microsoft-provided kernel, while Btrfs is not the default filesystem path most Windows users encounter. Still, developers who attach disks, experiment with filesystems, run custom kernels, or maintain Linux-heavy workflows on Windows-adjacent systems should understand why these records appear in Microsoft channels.
For enterprise IT, the lesson is less about this single CVE than about asset classification. If your vulnerability program only maps Microsoft advisories to Windows desktops and servers, it is already behind the shape of the modern estate. The Linux kernel is part of the Microsoft customer attack surface now, not because Microsoft owns Linux, but because Microsoft’s customers run it everywhere.
That makes the boring plumbing of kernel filesystems relevant to Windows shops. The cloud made everyone a Linux administrator, whether they wanted the title or not.
The Patch Is Small Because the Error Path Already Existed
The code change is almost surgical. The function already distinguishes known delayed-reference node types: tree block refs, shared block refs, extent data refs, shared data refs, and the owner ref case in newer kernels. The bad branch was the fallback. When the type did not match, the old code calledBUG().The fix creates a filesystem-info local variable, sets the return value to
-EUCLEAN, and logs the unexpected type. The existing post-call logic then logs the delayed-ref failure with the logical address, size, type, action, reference modification count, and return code. In other words, the filesystem now leaves breadcrumbs instead of a crater.That matters for troubleshooting. A panic gives you a stack trace if you are lucky and configured for it. A structured filesystem error gives administrators a better chance to correlate the event with a device, mount, workload, transaction abort, or metadata problem. It also lets the system remain alive long enough for monitoring agents, logging daemons, and orchestration layers to capture useful state.
There is a quiet design principle here: when recovery is possible, diagnostics are better than drama. A crashing assertion may prove that a developer’s assumption was violated, but a logged error helps an operator decide what to do next.
The use of
-EUCLEAN is also telling. That error is commonly associated with filesystem structure needing attention. It is not pretending that everything is fine. It is moving the failure from “kernel integrity emergency” to “filesystem integrity emergency,” which is the more precise category.What Administrators Should Actually Do
For most WindowsForum readers, the right response is not to go hunting for a one-off exploit. The right response is to identify where Btrfs is in use, determine whether the relevant kernels include the fix, and make sure the systems most exposed to local or tenant-controlled workloads are on a sane update path.Btrfs is common in places that do not always look like traditional servers. It appears on Linux desktops, developer workstations, NAS-style systems, backup hosts, container platforms, lab machines, and distributions that use snapshots heavily. It may also appear in appliance images where the administrator rarely thinks about the underlying filesystem unless something goes wrong.
The risk is highest where untrusted or semi-trusted users can influence filesystem state. Multi-user Linux systems, shared build hosts, CI runners, storage labs, and systems that mount externally supplied disk images deserve more attention than a single-user hobby machine with full-disk backups. That does not mean the latter should ignore kernel updates, only that prioritization should follow exposure.
Administrators should also avoid magical thinking about Btrfs repair commands. If a system logs delayed-reference failures or remounts a Btrfs filesystem read-only, the safest first move is usually to preserve evidence, verify backups, check hardware health, and review kernel versions before attempting invasive repair. Filesystem repair is not a ritual; it is surgery.
The patch changes a panic into an error, but it does not make underlying corruption harmless. If you hit this path, your next concern is not “great, the host stayed up.” It is “why did Btrfs see an impossible delayed-reference type in the first place?”
For Developers, This Is a Case Study in Killing Fatal Assertions
CVE-2026-43308 is also a useful reminder for developers working far above the kernel. The pattern is universal: a program encounters an unexpected internal state, and the original author reaches for a fatal assertion because the state “cannot happen.” Years later, that assertion becomes an outage trigger.The kernel version is more dramatic because the process is the operating system itself. But similar mistakes occur in databases, message queues, storage controllers, authentication services, and distributed systems. Fatal assertions are seductive because they simplify reasoning. They are dangerous because production environments are where impossible states go to become tickets.
The better design is not to ignore impossible states. It is to decide what scope of failure is justified. Can the operation fail? Can the transaction abort? Can the affected tenant be isolated? Can the subsystem degrade? Can the service shed load? Each smaller containment boundary is a win.
This is why filesystem work often feels conservative. Btrfs cannot simply continue as though metadata invariants do not matter. But it can choose the narrowest safe failure mode. In this case, upstream decided the narrowest safe failure mode was an error return and log message, not a kernel panic.
That is a design lesson worth carrying into every layer of the stack.
The Real Fix Is Smaller Than the Operational Work Around It
The concrete facts of CVE-2026-43308 are compact, but the operational implications spread across patch management, asset discovery, and incident response. Treat this as a kernel availability hardening issue, especially where Btrfs-backed systems host important or untrusted workloads.- CVE-2026-43308 was published on May 8, 2026, and describes a Linux kernel Btrfs fix for
run_one_delayed_ref(). - The vulnerable behavior was a
BUG()call when Btrfs encountered an unexpected delayed-reference node type. - The fixed behavior returns
-EUCLEANand logs an error, allowing Btrfs transaction error handling to proceed without panicking the whole kernel. - NVD had not assigned CVSS scores at the time the record appeared, so administrators should prioritize based on exposure rather than waiting for a number.
- The most relevant systems are Linux machines using Btrfs, especially shared hosts, CI runners, storage systems, developer machines, and cloud workloads where a local denial of service would have broader consequences.
- Microsoft’s advisory presence does not make this a Windows filesystem flaw, but it does reflect how deeply Linux kernel risk now sits inside Microsoft-managed and Windows-adjacent environments.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center