Microsoft listed CVE-2026-43344 in its Security Update Guide after kernel.org published a May 8, 2026 Linux kernel fix for Intel uncore performance-monitoring code that could mishandle die identification on certain NUMA-capable Xeon platforms when CPUs are offline or NUMA is disabled. The bug is not the sort of vulnerability that sends defenders racing to block an internet-facing exploit. It is, however, a useful reminder that modern infrastructure security increasingly lives in the seam between silicon topology, operating-system assumptions, and cloud-scale telemetry. For WindowsForum readers, the story matters less because it is “a Linux CVE” and more because Windows shops now routinely operate Linux in WSL, Azure, Hyper-V, containers, appliances, monitoring stacks, and mixed server estates.
CVE-2026-43344 is, on its face, a narrow Linux kernel issue. The affected code sits under
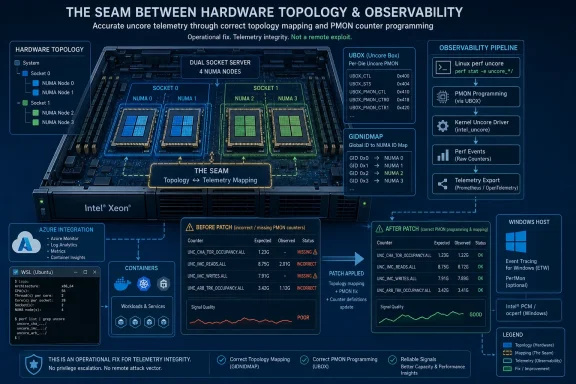
That placement alone explains why the CVE reads like a hardware engineer’s notebook rather than a conventional security advisory. The fix concerns die ID initialization and lookup paths, not a browser sandbox escape or a remote service accepting hostile packets. The kernel was making assumptions about how PCI devices, CPU locality, NUMA topology, and Intel server-platform registers lined up; under certain conditions, those assumptions broke.
The practical effect described in the CVE is that the kernel could fail to map some Intel uncore PMON units correctly. In one path, the code could stop scanning too early when a die ID lookup returned
That is a long way from “an attacker gets root.” It is also exactly the kind of bug that earns a CVE in today’s kernel process because reliability, observability, and isolation boundaries are increasingly intertwined. If the kernel gets hardware topology wrong, the consequences may be merely noisy performance data — or they may be the first domino in something more operationally painful.
Intel uncore counters are especially important on large server platforms because they reveal behavior outside the CPU cores themselves. Memory bandwidth pressure, inter-socket traffic, cache-coherency behavior, and fabric-level bottlenecks can all become visible through these units. On a workstation, bad uncore enumeration might be a curiosity. On a dense host running databases, AI preprocessing jobs, storage services, or virtualized tenant workloads, missing PMON units can distort the picture administrators rely on.
That makes CVE-2026-43344 a vulnerability in the modern sense: not necessarily a direct exploit primitive, but a flaw in a privileged component that can impair the system’s ability to represent itself accurately. Security teams have spent years learning that logs, counters, traces, and telemetry are part of the defensive surface. When they lie, vanish, or silently undercount, the blast radius is not limited to performance engineering.
The important distinction is that this CVE does not currently arrive with an NVD severity score or a public exploitation narrative. NVD had not assigned CVSS metrics at publication time, and the description from kernel.org is rooted in a resolved kernel bug rather than an adversary playbook. That should lower panic, not attention.
NUMA, or non-uniform memory access, is one of those architectural facts that administrators often meet only when something is already slow. On multi-socket and multi-die systems, not every CPU has equal-cost access to every region of memory or every device. Operating systems use NUMA information to place workloads, schedule threads, and interpret locality.
The bug arises partly because the kernel path used
For Intel Sapphire Rapids and Emerald Rapids platforms, the fix moves the relevant lookup to
This is why the CVE feels obscure but carries a lesson. Kernel code often sits atop layers of “obvious” assumptions: PCI enumeration order, online CPU state, NUMA availability, device locality, and platform register behavior. Every one of those assumptions may be violated in a real data center.
The CVE description is blunt about why that was wrong. First,
That distinction matters in kernel code because warnings have gravity. A
This is a recurring theme in mature infrastructure software. The hard part is not only detecting bad states; it is recognizing which ugly states are valid under real operating conditions. Hotplug, CPU offlining, firmware quirks, virtualization, and administrator tuning all create configurations that look abnormal until they are understood as part of the supported operating envelope.
Azure runs enormous amounts of Linux. Microsoft ships and maintains Linux components across cloud services, developer tooling, container platforms, and its own Linux distributions and images. Windows users run Linux through WSL. Enterprises that standardize on Microsoft identity, endpoint management, and cloud security still operate mixed fleets where the Linux kernel is a first-class dependency.
That means a Linux kernel CVE can be a Microsoft customer issue even when it is not a Windows kernel issue. The old mental model — Microsoft patch day over here, Linux distro advisories over there — has been obsolete for years. The more accurate model is a layered software supply chain in which kernel.org, distribution maintainers, cloud image publishers, appliance vendors, and platform operators all participate in turning an upstream fix into a customer-visible remediation.
For administrators, the key question is not “Is this a Windows vulnerability?” It is “Where in my Microsoft-adjacent estate do I consume the affected Linux kernel code?” The answer may include Azure Linux images, custom VM images, Kubernetes worker nodes, security appliances, build agents, WSL kernels, or third-party products deployed inside an otherwise Windows-centered environment.
This matters because many patch dashboards still treat CVSS as the start of triage rather than one input into it. A vulnerability with no score can disappear into exception queues, while a high-scoring bug with little relevance to the environment gets escalated. Both outcomes are bad security operations.
For this CVE, the lack of scoring should push teams toward exposure analysis rather than drama. The affected subsystem is Intel uncore performance monitoring. The described platforms include Intel Sapphire Rapids and Emerald Rapids for one part of the fix, with another path involving systems where
That is enough to separate likely-relevant environments from noise. A small ARM-based edge device is not the audience. A fleet of recent Intel Xeon servers running Linux kernels with performance monitoring enabled is much closer to the target zone. A Windows laptop that only touches Linux through occasional WSL use is somewhere else entirely, though still not exempt from normal kernel update hygiene.
The enterprise risk is subtler: configuration drift can turn “unlikely” bugs into recurring operational ghosts. One team disables NUMA to work around a scheduler issue. Another takes CPUs offline for power, licensing, troubleshooting, or cluster partitioning reasons. A third relies on uncore counters to validate workload placement or diagnose memory saturation. Suddenly, a kernel mapping bug becomes part of a production incident nobody labels as security until much later.
This is why platform bugs frustrate incident responders. They do not always present as clean crashes. Sometimes they present as missing telemetry, incomplete device trees, inconsistent metrics between hosts, or performance tools that disagree across otherwise identical systems. In security operations, that kind of inconsistency can slow investigations and erode trust in baselines.
The fix also reminds us that enumeration order is a security-adjacent concern. The advisory notes that
But dismissing that noise wholesale is a mistake. Kernel maintenance is now one of the primary ways the industry records and distributes fixes for low-level correctness bugs that may have security implications. Some will become urgent. Many will not. The only sane response is not to panic at every identifier, but to build patch processes that can absorb steady kernel churn without heroic effort.
CVE-2026-43344 sits squarely in that category. It is a correctness fix in privileged code, tied to specific hardware topology, with uncertain exploitability and real operational relevance for certain systems. It does not demand emergency weekend work for every WindowsForum reader. It does deserve to be tracked through the distributions and images that actually ship kernels into production.
That last phrase is the operational catch. Most organizations do not run “the Linux kernel” in the abstract. They run Ubuntu, Debian, Red Hat Enterprise Linux, SUSE, Oracle Linux, Azure Linux, Amazon Linux, container-optimized images, appliance kernels, and vendor-patched long-term branches. The upstream stable commits are the beginning of the remediation chain, not the end of it.
Then look for hardware relevance. This CVE’s technical description points toward Intel server platforms and uncore PMON enumeration, especially newer Xeon systems where Sapphire Rapids and Emerald Rapids appear in the affected code path. If the Linux systems in question are virtual machines without exposed uncore PMON access, the practical impact may be limited by abstraction. If they are bare-metal hosts used for performance-sensitive workloads, the issue deserves more attention.
Administrators should also examine whether they have intentionally disabled NUMA on systems that are physically NUMA-capable. That is not inherently wrong; administrators do it for reasons ranging from application behavior to legacy tuning guidance. But this CVE is a concrete example of how a kernel subsystem can still need accurate topology information even when the OS-level NUMA policy has been turned off.
Finally, treat perf permissions as part of the baseline review. Many distributions have tightened unprivileged perf access over the years because performance counters can expose sensitive information. CVE-2026-43344 is not primarily about data leakage through counters, but any review of perf-related kernel exposure is a good moment to confirm who can use those interfaces and why.
That precision matters. Performance monitoring is one of those areas where heavy-handed mitigations can hurt the very people most likely to notice: database administrators, kernel developers, performance engineers, HPC operators, and cloud infrastructure teams. Turning off counters because enumeration is hard would be technically safe but operationally crude.
The better answer is to make the topology lookup match the hardware reality. UBOX GIDNIDMAP exists to expose platform mapping. If NUMA policy is unavailable or disabled, the kernel can still derive the information it needs from the platform register. That is the difference between papering over a symptom and fixing the model.
There is also a broader lesson for anyone writing privileged systems software. Configuration options are not merely user preferences; they are fault-injection tools. If disabling NUMA breaks an uncore lookup, then the lookup was depending on the wrong layer. If offlining CPUs makes a scan abort, then the scan was treating a dynamic state as an invariant.
For most enterprises, the update path will come through the distribution or platform vendor rather than direct application of the upstream stable commits. That is especially true for systems running vendor-supported kernels with backports. Version numbers can mislead here because a distro kernel may carry the fix without matching the upstream version that first included it.
Cloud users should watch image release notes and managed-service advisories. If a host is part of a managed Kubernetes service, an appliance, or a cloud marketplace image, the remediation owner may not be the same team that owns the workload. That is where kernel CVEs turn into coordination exercises.
WSL users are likely a lower-risk population for this specific bug, particularly on ordinary client hardware, but WSL is still part of the Linux kernel supply chain. Developer machines are increasingly privileged access points into production environments. Keeping WSL current remains sensible even when a given CVE appears server-oriented.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Small Kernel Fix Lands in a Very Large Supply Chain
A Small Kernel Fix Lands in a Very Large Supply Chain
CVE-2026-43344 is, on its face, a narrow Linux kernel issue. The affected code sits under perf/x86/intel/uncore, the part of the kernel that helps expose Intel uncore performance-monitoring units — counters tied not to individual CPU cores, but to surrounding package-level hardware such as memory controllers, interconnects, and related platform fabric.That placement alone explains why the CVE reads like a hardware engineer’s notebook rather than a conventional security advisory. The fix concerns die ID initialization and lookup paths, not a browser sandbox escape or a remote service accepting hostile packets. The kernel was making assumptions about how PCI devices, CPU locality, NUMA topology, and Intel server-platform registers lined up; under certain conditions, those assumptions broke.
The practical effect described in the CVE is that the kernel could fail to map some Intel uncore PMON units correctly. In one path, the code could stop scanning too early when a die ID lookup returned
-1, even though offline CPUs could make that state expected. In another, disabling NUMA on a NUMA-capable system caused the kernel’s node lookup to return NUMA_NO_NODE, which meant Intel Sapphire Rapids and Emerald Rapids systems could ignore relevant PMON units instead of adding them to the kernel’s internal tracking tree.That is a long way from “an attacker gets root.” It is also exactly the kind of bug that earns a CVE in today’s kernel process because reliability, observability, and isolation boundaries are increasingly intertwined. If the kernel gets hardware topology wrong, the consequences may be merely noisy performance data — or they may be the first domino in something more operationally painful.
The Security Story Is Really an Observability Story
The word “perf” can lull administrators into filing this one under developer tooling. That would be too casual. Linuxperf and the broader performance-monitoring subsystem are not just conveniences for benchmarkers; they are part of how production systems are profiled, tuned, capacity-planned, and investigated when workloads behave badly.Intel uncore counters are especially important on large server platforms because they reveal behavior outside the CPU cores themselves. Memory bandwidth pressure, inter-socket traffic, cache-coherency behavior, and fabric-level bottlenecks can all become visible through these units. On a workstation, bad uncore enumeration might be a curiosity. On a dense host running databases, AI preprocessing jobs, storage services, or virtualized tenant workloads, missing PMON units can distort the picture administrators rely on.
That makes CVE-2026-43344 a vulnerability in the modern sense: not necessarily a direct exploit primitive, but a flaw in a privileged component that can impair the system’s ability to represent itself accurately. Security teams have spent years learning that logs, counters, traces, and telemetry are part of the defensive surface. When they lie, vanish, or silently undercount, the blast radius is not limited to performance engineering.
The important distinction is that this CVE does not currently arrive with an NVD severity score or a public exploitation narrative. NVD had not assigned CVSS metrics at publication time, and the description from kernel.org is rooted in a resolved kernel bug rather than an adversary playbook. That should lower panic, not attention.
NUMA Was the Assumption Hidden in the Floorboards
The most interesting part of the advisory is not theWARN_ON_ONCE() removal. It is the NUMA dependency that turns out not to be safe.NUMA, or non-uniform memory access, is one of those architectural facts that administrators often meet only when something is already slow. On multi-socket and multi-die systems, not every CPU has equal-cost access to every region of memory or every device. Operating systems use NUMA information to place workloads, schedule threads, and interpret locality.
The bug arises partly because the kernel path used
pcibus_to_node() to associate PCI buses with NUMA nodes. That can work when Linux NUMA support is enabled and topology is presented as expected. But if NUMA is disabled on a NUMA-capable machine, pcibus_to_node() can return NUMA_NO_NODE, and the old lookup chain collapses into -1 for all PCI devices.For Intel Sapphire Rapids and Emerald Rapids platforms, the fix moves the relevant lookup to
uncore_pcibus_to_dieid(), which retrieves topology from the UBOX GIDNIDMAP register instead of depending on Linux’s NUMA view. That is a more hardware-grounded answer. It says, in effect, that if the kernel needs die identity for Intel uncore devices, it should ask the platform mechanism designed to expose that relationship rather than infer it from an OS configuration that administrators may legitimately turn off.This is why the CVE feels obscure but carries a lesson. Kernel code often sits atop layers of “obvious” assumptions: PCI enumeration order, online CPU state, NUMA availability, device locality, and platform register behavior. Every one of those assumptions may be violated in a real data center.
Offline CPUs Are Not an Error Condition
The second half of the fix is more philosophical. In thenr_node_ids > 8 path, uncore_device_to_die() may return -1 when all CPUs associated with a UBOX device are offline. The previous code treated that as alarming enough to trigger a warning and break out.The CVE description is blunt about why that was wrong. First,
pci_get_device() does not guarantee iteration in domain or bus order, so breaking early could skip later UBOX devices that still needed to be scanned. Second, offline buses or devices with an unresolved die ID are not inherently erroneous in this path; they may simply reflect current CPU online state.That distinction matters in kernel code because warnings have gravity. A
WARN_ON_ONCE() is not just a message for a developer reading logs. It often reflects a belief that the system has entered a state that should not happen. Here, the corrected view is that the state can happen and should be handled without aborting the broader scan.This is a recurring theme in mature infrastructure software. The hard part is not only detecting bad states; it is recognizing which ugly states are valid under real operating conditions. Hotplug, CPU offlining, firmware quirks, virtualization, and administrator tuning all create configurations that look abnormal until they are understood as part of the supported operating envelope.
Why Microsoft Is in the Frame
At first glance, Microsoft’s presence may seem odd. CVE-2026-43344 is a Linux kernel CVE, assigned from kernel.org material, and the referenced fixes live in the Linux stable tree. Yet Microsoft’s Security Update Guide listing is not a clerical accident; it reflects how far Microsoft’s operating environment now extends into Linux.Azure runs enormous amounts of Linux. Microsoft ships and maintains Linux components across cloud services, developer tooling, container platforms, and its own Linux distributions and images. Windows users run Linux through WSL. Enterprises that standardize on Microsoft identity, endpoint management, and cloud security still operate mixed fleets where the Linux kernel is a first-class dependency.
That means a Linux kernel CVE can be a Microsoft customer issue even when it is not a Windows kernel issue. The old mental model — Microsoft patch day over here, Linux distro advisories over there — has been obsolete for years. The more accurate model is a layered software supply chain in which kernel.org, distribution maintainers, cloud image publishers, appliance vendors, and platform operators all participate in turning an upstream fix into a customer-visible remediation.
For administrators, the key question is not “Is this a Windows vulnerability?” It is “Where in my Microsoft-adjacent estate do I consume the affected Linux kernel code?” The answer may include Azure Linux images, custom VM images, Kubernetes worker nodes, security appliances, build agents, WSL kernels, or third-party products deployed inside an otherwise Windows-centered environment.
The Absence of a CVSS Score Should Not Be Misread
The NVD entry for CVE-2026-43344 arrived without a CVSS 4.0, CVSS 3.x, or CVSS 2.0 score from NIST. That does not mean the vulnerability is fake, nor does it mean it is critical. It means enrichment had not yet caught up with publication.This matters because many patch dashboards still treat CVSS as the start of triage rather than one input into it. A vulnerability with no score can disappear into exception queues, while a high-scoring bug with little relevance to the environment gets escalated. Both outcomes are bad security operations.
For this CVE, the lack of scoring should push teams toward exposure analysis rather than drama. The affected subsystem is Intel uncore performance monitoring. The described platforms include Intel Sapphire Rapids and Emerald Rapids for one part of the fix, with another path involving systems where
nr_node_ids > 8. The conditions discussed include offline CPUs and NUMA-disabled configurations on NUMA-capable hardware.That is enough to separate likely-relevant environments from noise. A small ARM-based edge device is not the audience. A fleet of recent Intel Xeon servers running Linux kernels with performance monitoring enabled is much closer to the target zone. A Windows laptop that only touches Linux through occasional WSL use is somewhere else entirely, though still not exempt from normal kernel update hygiene.
The Enterprise Risk Is Configuration Drift, Not Internet Exposure
There is no indication from the published description that CVE-2026-43344 is remotely exploitable. There is no public claim of active exploitation. There is no obvious reason to treat it like an emergency boundary-crossing flaw.The enterprise risk is subtler: configuration drift can turn “unlikely” bugs into recurring operational ghosts. One team disables NUMA to work around a scheduler issue. Another takes CPUs offline for power, licensing, troubleshooting, or cluster partitioning reasons. A third relies on uncore counters to validate workload placement or diagnose memory saturation. Suddenly, a kernel mapping bug becomes part of a production incident nobody labels as security until much later.
This is why platform bugs frustrate incident responders. They do not always present as clean crashes. Sometimes they present as missing telemetry, incomplete device trees, inconsistent metrics between hosts, or performance tools that disagree across otherwise identical systems. In security operations, that kind of inconsistency can slow investigations and erode trust in baselines.
The fix also reminds us that enumeration order is a security-adjacent concern. The advisory notes that
pci_get_device() does not guarantee domain or bus ordering. Code that assumes a friendly scan order may skip devices when a single unexpected condition appears. In complex systems, skipped devices are rarely just skipped devices; they are unobserved state.Kernel CVEs Have Become a Language for Maintenance Debt
The Linux kernel’s CVE stream can look strange to administrators accustomed to vendor advisories that focus on exploitability. Many recent kernel CVEs are generated from resolved upstream bugs, and the descriptions often read like commit messages because they essentially are commit-derived security records. That can make the feed feel noisy.But dismissing that noise wholesale is a mistake. Kernel maintenance is now one of the primary ways the industry records and distributes fixes for low-level correctness bugs that may have security implications. Some will become urgent. Many will not. The only sane response is not to panic at every identifier, but to build patch processes that can absorb steady kernel churn without heroic effort.
CVE-2026-43344 sits squarely in that category. It is a correctness fix in privileged code, tied to specific hardware topology, with uncertain exploitability and real operational relevance for certain systems. It does not demand emergency weekend work for every WindowsForum reader. It does deserve to be tracked through the distributions and images that actually ship kernels into production.
That last phrase is the operational catch. Most organizations do not run “the Linux kernel” in the abstract. They run Ubuntu, Debian, Red Hat Enterprise Linux, SUSE, Oracle Linux, Azure Linux, Amazon Linux, container-optimized images, appliance kernels, and vendor-patched long-term branches. The upstream stable commits are the beginning of the remediation chain, not the end of it.
What Windows-Centric Shops Should Actually Check
For a Windows-heavy organization, the right response is inventory-led. Start with the places where Linux is present but socially invisible: CI runners, monitoring nodes, Kubernetes workers, storage gateways, security tools, backup appliances, WSL developer machines, and Azure-hosted workloads. The boring inventory question is usually more valuable than the dramatic vulnerability question.Then look for hardware relevance. This CVE’s technical description points toward Intel server platforms and uncore PMON enumeration, especially newer Xeon systems where Sapphire Rapids and Emerald Rapids appear in the affected code path. If the Linux systems in question are virtual machines without exposed uncore PMON access, the practical impact may be limited by abstraction. If they are bare-metal hosts used for performance-sensitive workloads, the issue deserves more attention.
Administrators should also examine whether they have intentionally disabled NUMA on systems that are physically NUMA-capable. That is not inherently wrong; administrators do it for reasons ranging from application behavior to legacy tuning guidance. But this CVE is a concrete example of how a kernel subsystem can still need accurate topology information even when the OS-level NUMA policy has been turned off.
Finally, treat perf permissions as part of the baseline review. Many distributions have tightened unprivileged perf access over the years because performance counters can expose sensitive information. CVE-2026-43344 is not primarily about data leakage through counters, but any review of perf-related kernel exposure is a good moment to confirm who can use those interfaces and why.
The Fix Is Precise Because the Failure Was Conceptual
The patch approach is elegant in the way good kernel fixes often are. It does not bolt on a broad mitigation or disable a subsystem. It narrows the logic: do not treat offline CPU-associated devices as fatal in the high-node-count path, and use a die-ID source that remains valid when Linux NUMA is disabled for Sapphire Rapids and Emerald Rapids handling.That precision matters. Performance monitoring is one of those areas where heavy-handed mitigations can hurt the very people most likely to notice: database administrators, kernel developers, performance engineers, HPC operators, and cloud infrastructure teams. Turning off counters because enumeration is hard would be technically safe but operationally crude.
The better answer is to make the topology lookup match the hardware reality. UBOX GIDNIDMAP exists to expose platform mapping. If NUMA policy is unavailable or disabled, the kernel can still derive the information it needs from the platform register. That is the difference between papering over a symptom and fixing the model.
There is also a broader lesson for anyone writing privileged systems software. Configuration options are not merely user preferences; they are fault-injection tools. If disabling NUMA breaks an uncore lookup, then the lookup was depending on the wrong layer. If offlining CPUs makes a scan abort, then the scan was treating a dynamic state as an invariant.
The Patch Queue, Not the Panic Button, Is the Right Place for This One
CVE-2026-43344 should go into normal kernel update planning, with higher priority for bare-metal Intel Xeon hosts that depend on perf and uncore PMON data. It should not be ignored merely because NVD had not scored it, and it should not be marketed internally as a crisis without evidence of exploitability. The adult response is targeted remediation.For most enterprises, the update path will come through the distribution or platform vendor rather than direct application of the upstream stable commits. That is especially true for systems running vendor-supported kernels with backports. Version numbers can mislead here because a distro kernel may carry the fix without matching the upstream version that first included it.
Cloud users should watch image release notes and managed-service advisories. If a host is part of a managed Kubernetes service, an appliance, or a cloud marketplace image, the remediation owner may not be the same team that owns the workload. That is where kernel CVEs turn into coordination exercises.
WSL users are likely a lower-risk population for this specific bug, particularly on ordinary client hardware, but WSL is still part of the Linux kernel supply chain. Developer machines are increasingly privileged access points into production environments. Keeping WSL current remains sensible even when a given CVE appears server-oriented.
The Concrete Read for CVE-2026-43344
The practical read is narrower than the CVE machinery makes it look, but broader than “not my problem” allows. This is a Linux kernel topology bug in Intel uncore performance-monitoring code, and its value as a security item is that it forces a review of where low-level observability and platform assumptions intersect.- Organizations should identify Linux systems running on recent Intel Xeon server platforms, especially bare-metal hosts where uncore performance counters are used for monitoring, diagnostics, or tuning.
- Administrators should verify whether their distribution or platform vendor has shipped the stable kernel fix or a backport for CVE-2026-43344.
- Teams that disable NUMA on NUMA-capable systems should treat this CVE as a reminder to test hardware-topology-dependent tooling after kernel updates and firmware changes.
- Security teams should avoid using the missing NVD CVSS score as a reason to suppress the item without an exposure review.
- Windows-centric shops should include WSL, Azure-hosted Linux, Kubernetes nodes, appliances, and CI infrastructure in the inventory rather than limiting review to traditional Linux server teams.
- Performance engineers should re-check uncore PMON visibility on affected Intel platforms after patching, because the most visible improvement may be corrected telemetry rather than a dramatic security symptom.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center