CVE-2026-43421 is a newly published Linux kernel vulnerability, added to the NVD dataset on May 8, 2026, covering a USB gadget f_ncm driver bug where a network device could outlive its parent gadget device during disconnect handling. The short version sounds microscopic: a
CVE-2026-43421 sits in the Linux USB gadget subsystem, specifically the NCM function driver. NCM, or Network Control Model, is one of the ways a device can present itself over USB as a network interface rather than as storage, serial, or a simple peripheral. Plug in the right phone, development board, appliance, or embedded device, and what looks like a cable can become an Ethernet-like link.
That matters because USB gadget mode reverses the ordinary PC mental model. A Windows desktop or laptop usually acts as the USB host. A Linux-powered phone, single-board computer, lab device, router, kiosk, or recovery environment may act as the gadget, presenting services to that host. In that arrangement, the Linux side creates network interfaces that must appear, disappear, and reappear cleanly as the USB connection is configured and torn down.
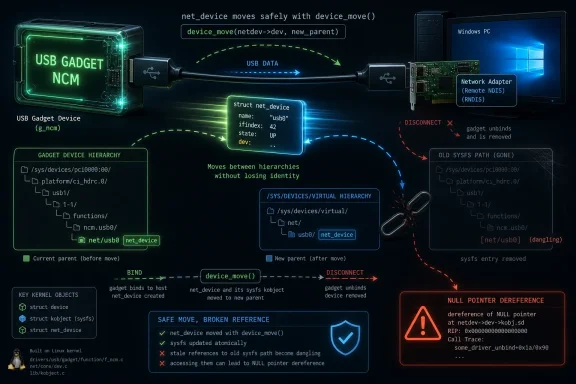
The bug described by CVE-2026-43421 is a lifecycle failure. The network device could survive longer than the gadget device that was supposed to parent it. Once the gadget disappeared, parts of sysfs could still point as if the old hierarchy existed, and code walking those relationships could hit a null pointer dereference.
That is not the cinematic kind of vulnerability. There is no public evidence in the material so far of a remote internet worm, a turnkey privilege escalation, or mass exploitation. But kernel null dereferences are still security-relevant because the kernel is the boundary between orderly failure and system instability. When object ownership goes wrong in kernel code, the blast radius depends on where the code runs, who can trigger it, and how often the affected path is exercised.
The Linux kernel is full of objects that represent hardware, pseudo-hardware, buses, interfaces, and userspace-visible names. A
The f_ncm driver’s job is not just to shovel packets through a USB endpoint. It must also cooperate with configfs, sysfs, the networking stack, power management, and userspace services that assume interface identity is stable enough to configure. The CVE notes that one attempted fix removed
Those failed repairs are the heart of the story. They show that “just free the object later” or “just allocate it later” was not sufficient. The driver had to satisfy several constituencies at once: the kernel’s device model, USB gadget teardown, network interface naming, configfs reporting, and real deployments where a DHCP server expects to keep binding to the same interface name across reconnects.
This is a subtle compromise. The driver does not simply destroy and recreate the network device every time the USB function unbinds. It also does not leave the device tied to a gadget object that has gone away. Instead, it moves the
That preserves interface continuity for userspace. The CVE description explicitly notes the DHCP regression seen in postmarketOS, where breaking the mapping made it impossible for configfs to report the resolved interface name and caused the DHCP server to fail. In other words, the bug was not only visible to kernel fuzzers or crash logs. It affected the mundane workflow of getting an IP address over a USB network connection.
The patch also introduces helper routines for attaching and detaching the gadget relationship, with cleanup behavior on bind failure and a bind counter to avoid repeated moves. Those details matter because they indicate the maintainers were not merely suppressing one crash signature. They were trying to encode the lifecycle rule so that the first bind, later unbinds, and failure paths all agree about who owns the visible network device at any given moment.
But Windows endpoints routinely sit on the other side of Linux gadget devices. Android-derived devices, embedded Linux appliances, diagnostics boards, industrial gear, development kits, portable routers, recovery images, and lab hardware can all expose USB networking to a Windows host. If a gadget-side kernel crashes or misbehaves during disconnect, the Windows operator may experience it as a flaky device, a broken provisioning run, a vanished network adapter, or a support ticket that starts with “USB networking is unreliable.”
That is why this belongs in a WindowsForum security feed. The modern Windows environment is not a sealed Microsoft-only stack. It is a workstation plugged into firmware, phones, hypervisors, Linux appliances, WSL-adjacent workflows, developer boards, and vendor hardware that may run kernels maintained through completely different channels. A Linux gadget bug can still interrupt a Windows-administered workflow.
The practical audience is narrower than the CVE label suggests. Most ordinary Windows laptops are not directly vulnerable in the sense of running the affected code. The people who should pay attention are those who build or manage Linux-based devices that connect to Windows hosts over USB networking, and those who support fleets where USB tethering, provisioning, field diagnostics, or embedded gadget mode are part of the operating procedure.
That gap matters because kernel CVEs are often misread by dashboards. A scanner may flag the CVE because a kernel package version appears in inventory. A management report may list it next to unrelated remote-code-execution issues. A product owner may ask whether it is “critical” before anyone has established whether the affected gadget function is enabled, reachable, or even compiled into the relevant build.
The better first question is not “What is the score?” but “Where do we use USB gadget NCM?” If the answer is nowhere, the exposure may be theoretical. If the answer is in a device used for provisioning, field service, tethering, or embedded network transport, the next question is whether userspace depends on stable interface naming across reconnects. In that case, this patch may fix both a vulnerability and a reliability problem.
This is where security and operations overlap. A null pointer dereference is often treated as a denial-of-service issue, but the operational symptom may be less dramatic than a panic and more annoying than a clean crash: dangling sysfs entries, unstable network identity, and services that bind to an interface that no longer behaves like the same interface.
Those are not random side effects. They are evidence that the driver sits at the intersection of subsystems with competing ideas of what “lifetime” means. The USB gadget layer cares about binding and unbinding functions as configurations change. The networking layer cares about an interface that can be named, reported, and configured. The device model cares about parent-child relationships. Power management cares about ordering. Userspace cares that its DHCP server does not suddenly lose the object it was told to manage.
A less mature fix would have optimized for one layer and broken another. That appears to be what happened in the earlier attempts. The final shape, moving the device between parents rather than destroying the interface or leaving it attached to a vanished gadget, is an admission that the interface has two lives: it is a child of a gadget when active, and a virtual device when the gadget is not bound.
That dual identity is untidy, but it matches reality. USB gadget networking is not a normal NIC plugged into a bus slot. It is a software-defined network device whose physical presentation can disappear and return. Treating it as purely physical or purely virtual misses half the problem.
For an attacker, the obvious prerequisite is some ability to influence or trigger gadget bind/unbind behavior on an affected Linux device. That is a narrower condition than a remote packet parser exposed to the internet. Physical access, local control, a malicious host scenario, or a compromised management path may be necessary depending on the deployment.
For an operator, the triggering condition may be far more ordinary. A technician unplugs a device during provisioning. A field unit reconnects. A gadget function cycles during configuration. A DHCP process expects the same interface to exist. The failure appears not as “CVE exploited,” but as a device that cannot be recovered without a reboot or manual intervention.
Security teams often underestimate bugs like this because the attacker story is constrained. Operations teams often overestimate them because every intermittent USB-networking failure becomes suspect. The disciplined position is between those poles: this is a kernel lifecycle vulnerability with plausible denial-of-service consequences in affected configurations, and it is worth patching where USB gadget NCM is part of real use.
For Windows admins, this distinction is important. MSRC is often the first stop for Microsoft product vulnerabilities, but the CVE ecosystem is broader than Microsoft. A CVE page can surface information about third-party components, cross-platform dependencies, or records that security tooling correlates in ways that are useful but easy to misread.
The relevant source of the fix is the Linux kernel stable tree. The relevant consumer action is therefore not “check Windows Update” but “check the Linux kernel version or vendor firmware for the device that exposes USB gadget NCM.” If that device is a phone-like Linux system, an appliance, a lab board, or a custom embedded image, the patch path likely runs through its OS vendor, BSP maintainer, OEM firmware update, or internal kernel build pipeline.
This is a common modern patch-management trap. The machine on the admin’s desk may be Windows, the vulnerable component may be Linux, the advisory may appear in Microsoft’s database, and the actual remediation may require a device firmware update from a third party. The CVE is the common language, not the delivery mechanism.
That is where CVE-2026-43421 becomes a long-tail problem. The upstream fix can be small and well-understood, but the affected product may sit behind an OEM update cadence, a carrier approval process, a field-service policy, or an internal firmware build that nobody wants to touch unless the device is visibly broken. USB gadget networking is common in exactly the kinds of products where kernel updates are not as routine as Windows monthly servicing.
The irony is that this bug may be easier to justify operationally than many abstract CVEs. If a device has suffered from unstable NCM behavior, broken DHCP after reconnect, or odd sysfs remnants, the patch is not just a security checkbox. It is a reliability fix with a security identifier attached.
That can help administrators argue for action. A CVE without a score may not move a procurement committee. A reproducible provisioning failure, a crash on disconnect, or a DHCP regression tied to the same code path often will.
That history is valuable because it warns downstream maintainers not to cherry-pick blindly. A vendor kernel may already carry one of the earlier attempts. A custom tree may have reverted part of it. A product team may see that “f_ncm lifecycle” was addressed once and assume the matter is closed. The CVE’s chronology says otherwise: the correct fix is not merely any patch touching f_ncm lifetime management, but the one that preserves interface identity while reparenting the device safely.
This is especially important for long-term stable branches. Backporting a kernel fix across versions is rarely a pure copy-and-paste exercise. Helper functions, cleanup macros, and surrounding subsystem behavior may differ. The CVE references multiple stable commits, suggesting that maintainers have done the work for several supported lines, but downstream trees still need verification rather than assumption.
For sysadmins, the actionable version of that warning is simple: do not accept “we patched something in USB gadget” as the final answer. Ask whether the build includes the
That distinction matters in troubleshooting. A Windows event log may show device arrival, removal, DHCP timeout, or adapter state changes. Device Manager may show a transient USB network interface. Network troubleshooting may point to address assignment. None of that proves the Windows host is broken.
In mixed environments, engineers should capture both sides. On the Linux gadget, sysfs paths under the network class, kernel logs around bind/unbind, and interface naming after reconnect are relevant. On the Windows host, USB enumeration events and DHCP behavior can establish the timeline. The bug described by CVE-2026-43421 is specifically about the gadget-side relationship between a network device and its parent, so the smoking gun is more likely in the Linux kernel log than in Windows networking policy.
This is a useful mental model for a lot of USB-C-era troubleshooting. The cable is not a passive boundary. It is a negotiation surface between operating systems, firmware, device classes, and power states. When something fails, the visible endpoint is not always the responsible endpoint.
Exploitation appears constrained by access to the affected gadget behavior. That lowers the likelihood for many traditional enterprise desktops and servers. But patch priority may still be high for device makers and labs because the affected path sits in connection management. Anything that can crash or wedge a device during connect/disconnect cycles deserves attention in products that must be recovered remotely or operated by non-experts.
There is also the matter of trust boundaries. A Linux gadget device may be plugged into an untrusted host, or a trusted Windows host may connect to a gadget device of uncertain provenance. USB has always been awkward for security because physical access and device identity blur quickly. A denial-of-service condition in the gadget stack may be sufficient to disrupt provisioning, kiosk operations, mobile workflows, or field diagnostics even if it does not hand an attacker shell access.
Administrators should therefore resist both extremes. This is not a broad Windows emergency. It is also not irrelevant simply because the affected code is in Linux. The right priority depends on whether USB NCM gadget networking is part of the environment’s operational fabric.
NCM is often chosen because it is more efficient and modern than older USB Ethernet approaches. It can be attractive for tethering, embedded management, and phone-to-host networking. But that also means it may be buried inside products that nobody labels “USB gadget devices” in procurement language.
For Linux distributions and device images under direct control, the answer is to track the kernel stable updates and confirm the specific f_ncm patch is present. For vendor devices, the answer is to press for firmware or OS release notes that mention CVE-2026-43421 or the underlying f_ncm lifecycle fix. For unsupported devices, the answer may be a compensating-control discussion: limit untrusted physical access, avoid repeated gadget reconfiguration in production workflows, and document recovery procedures if the USB network path fails.
There is no universal Windows-side mitigation that fixes a Linux gadget’s internal object lifetime. The host can sometimes avoid triggering problematic cycles by using cleaner disconnect procedures or avoiding unstable provisioning scripts, but that is a workaround at best. The fix belongs in the gadget kernel.
That is a broader design lesson for operating systems. Stability is not always achieved by destroying and recreating objects at clean lifecycle boundaries. Sometimes stability requires preserving identity while changing parentage. Userspace wants continuity; kernel internals want correctness.
Windows has its own analogues in Plug and Play, network adapter persistence, device instance IDs, and power-state transitions. Admins have seen similar classes of pain when a “new” adapter appears after a driver change, when a virtual NIC loses its profile, or when a docking station path changes enough to make Windows treat familiar hardware as unfamiliar. Different kernel, same human problem: identity is a contract, and userspace builds policy around it.
That is why CVE-2026-43421 is more than a Linux footnote. It is another example of how device identity has become a security and reliability primitive. Break the identity contract, and services fail in ways that look disproportionate to the tiny patch that eventually fixes them.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
net_device moved at the wrong time, a sysfs link left pointing at a ghost, a null pointer dereference waiting in kernel space. The longer version is more interesting, because it shows how a fix for a kernel crash can become a design argument about object lifetime, power management, and the weirdly durable reality of USB networking. For WindowsForum readers, the lesson is not that Linux suddenly became fragile; it is that modern endpoint ecosystems increasingly depend on code paths most users never know they are running.
 A Kernel Bug That Lives in the Cable, Not the Cloud
A Kernel Bug That Lives in the Cable, Not the Cloud
CVE-2026-43421 sits in the Linux USB gadget subsystem, specifically the NCM function driver. NCM, or Network Control Model, is one of the ways a device can present itself over USB as a network interface rather than as storage, serial, or a simple peripheral. Plug in the right phone, development board, appliance, or embedded device, and what looks like a cable can become an Ethernet-like link.That matters because USB gadget mode reverses the ordinary PC mental model. A Windows desktop or laptop usually acts as the USB host. A Linux-powered phone, single-board computer, lab device, router, kiosk, or recovery environment may act as the gadget, presenting services to that host. In that arrangement, the Linux side creates network interfaces that must appear, disappear, and reappear cleanly as the USB connection is configured and torn down.
The bug described by CVE-2026-43421 is a lifecycle failure. The network device could survive longer than the gadget device that was supposed to parent it. Once the gadget disappeared, parts of sysfs could still point as if the old hierarchy existed, and code walking those relationships could hit a null pointer dereference.
That is not the cinematic kind of vulnerability. There is no public evidence in the material so far of a remote internet worm, a turnkey privilege escalation, or mass exploitation. But kernel null dereferences are still security-relevant because the kernel is the boundary between orderly failure and system instability. When object ownership goes wrong in kernel code, the blast radius depends on where the code runs, who can trigger it, and how often the affected path is exercised.
The Real Story Is Object Lifetime, Not a Scary CVE Number
The most revealing phrase in the CVE description is not “null pointer dereference.” It is “network device outlived its parent gadget device.” That is the kind of sentence kernel developers write when the failure is architectural rather than cosmetic.The Linux kernel is full of objects that represent hardware, pseudo-hardware, buses, interfaces, and userspace-visible names. A
net_device is not merely a C structure with packet counters. It is also a thing userspace can see, configure, rename, monitor, and bind services to. If that object is attached to the wrong parent or removed at the wrong point in the bind/unbind cycle, the problem leaks upward into tools and daemons that were never supposed to understand USB gadget internals.The f_ncm driver’s job is not just to shovel packets through a USB endpoint. It must also cooperate with configfs, sysfs, the networking stack, power management, and userspace services that assume interface identity is stable enough to configure. The CVE notes that one attempted fix removed
SET_NETDEV_DEV entirely, but that was later reverted because it created power management ordering concerns and a NO-CARRIER regression. Another attempt moved allocation later, into bind, but broke the one-to-one mapping between a function instance and a network device.Those failed repairs are the heart of the story. They show that “just free the object later” or “just allocate it later” was not sufficient. The driver had to satisfy several constituencies at once: the kernel’s device model, USB gadget teardown, network interface naming, configfs reporting, and real deployments where a DHCP server expects to keep binding to the same interface name across reconnects.
The Fix Moves the Device Without Pretending It Was Never There
The accepted repair usesdevice_move to reparent the network device between the gadget device and /sys/devices/virtual/ across bind and unbind cycles. That sounds like kernel plumbing because it is kernel plumbing. But it is plumbing with a clear product consequence: the network interface can survive USB reconnection without pretending its dead parent still exists.This is a subtle compromise. The driver does not simply destroy and recreate the network device every time the USB function unbinds. It also does not leave the device tied to a gadget object that has gone away. Instead, it moves the
net_device out from under the physical gadget hierarchy when necessary, then attaches it back when the gadget is live again.That preserves interface continuity for userspace. The CVE description explicitly notes the DHCP regression seen in postmarketOS, where breaking the mapping made it impossible for configfs to report the resolved interface name and caused the DHCP server to fail. In other words, the bug was not only visible to kernel fuzzers or crash logs. It affected the mundane workflow of getting an IP address over a USB network connection.
The patch also introduces helper routines for attaching and detaching the gadget relationship, with cleanup behavior on bind failure and a bind counter to avoid repeated moves. Those details matter because they indicate the maintainers were not merely suppressing one crash signature. They were trying to encode the lifecycle rule so that the first bind, later unbinds, and failure paths all agree about who owns the visible network device at any given moment.
Why Windows People Should Care About a Linux Gadget Driver
At first glance, a Linux USB gadget CVE looks like someone else’s problem. Windows machines are usually USB hosts, not USB gadgets. Windows Update will not ship the Linux kernel patch for your desktop because the vulnerable code is not in Windows.But Windows endpoints routinely sit on the other side of Linux gadget devices. Android-derived devices, embedded Linux appliances, diagnostics boards, industrial gear, development kits, portable routers, recovery images, and lab hardware can all expose USB networking to a Windows host. If a gadget-side kernel crashes or misbehaves during disconnect, the Windows operator may experience it as a flaky device, a broken provisioning run, a vanished network adapter, or a support ticket that starts with “USB networking is unreliable.”
That is why this belongs in a WindowsForum security feed. The modern Windows environment is not a sealed Microsoft-only stack. It is a workstation plugged into firmware, phones, hypervisors, Linux appliances, WSL-adjacent workflows, developer boards, and vendor hardware that may run kernels maintained through completely different channels. A Linux gadget bug can still interrupt a Windows-administered workflow.
The practical audience is narrower than the CVE label suggests. Most ordinary Windows laptops are not directly vulnerable in the sense of running the affected code. The people who should pay attention are those who build or manage Linux-based devices that connect to Windows hosts over USB networking, and those who support fleets where USB tethering, provisioning, field diagnostics, or embedded gadget mode are part of the operating procedure.
NVD Has the Record, But Not Yet the Risk Shape
As of the record’s publication, NVD had received the CVE and included it in the dataset, but it had not provided CVSS scoring in the visible fields. That absence is not unusual for fresh Linux kernel CVEs, but it creates an interpretive gap. A CVE with no NVD score is neither harmless nor automatically severe; it is simply under-enriched.That gap matters because kernel CVEs are often misread by dashboards. A scanner may flag the CVE because a kernel package version appears in inventory. A management report may list it next to unrelated remote-code-execution issues. A product owner may ask whether it is “critical” before anyone has established whether the affected gadget function is enabled, reachable, or even compiled into the relevant build.
The better first question is not “What is the score?” but “Where do we use USB gadget NCM?” If the answer is nowhere, the exposure may be theoretical. If the answer is in a device used for provisioning, field service, tethering, or embedded network transport, the next question is whether userspace depends on stable interface naming across reconnects. In that case, this patch may fix both a vulnerability and a reliability problem.
This is where security and operations overlap. A null pointer dereference is often treated as a denial-of-service issue, but the operational symptom may be less dramatic than a panic and more annoying than a clean crash: dangling sysfs entries, unstable network identity, and services that bind to an interface that no longer behaves like the same interface.
The Earlier Fixes Explain Why This One Took a Detour
The CVE description reads almost like a miniature changelog of kernel engineering humility. A previous attempt removedSET_NETDEV_DEV, but that ran into power management ordering problems and a NO-CARRIER regression. Another attempt deferred allocation to bind, but that broke the relationship between the function instance and the network device.Those are not random side effects. They are evidence that the driver sits at the intersection of subsystems with competing ideas of what “lifetime” means. The USB gadget layer cares about binding and unbinding functions as configurations change. The networking layer cares about an interface that can be named, reported, and configured. The device model cares about parent-child relationships. Power management cares about ordering. Userspace cares that its DHCP server does not suddenly lose the object it was told to manage.
A less mature fix would have optimized for one layer and broken another. That appears to be what happened in the earlier attempts. The final shape, moving the device between parents rather than destroying the interface or leaving it attached to a vanished gadget, is an admission that the interface has two lives: it is a child of a gadget when active, and a virtual device when the gadget is not bound.
That dual identity is untidy, but it matches reality. USB gadget networking is not a normal NIC plugged into a bus slot. It is a software-defined network device whose physical presentation can disappear and return. Treating it as purely physical or purely virtual misses half the problem.
The Security Impact Is Local, But the Reliability Impact Is Fleet-Wide
There is a temptation to rank this CVE as boring because it does not arrive with a polished exploit narrative. That would be a mistake, though not because everyone should panic. It would be a mistake because reliability bugs in kernel device lifecycles are exactly the kind that become expensive in fleets.For an attacker, the obvious prerequisite is some ability to influence or trigger gadget bind/unbind behavior on an affected Linux device. That is a narrower condition than a remote packet parser exposed to the internet. Physical access, local control, a malicious host scenario, or a compromised management path may be necessary depending on the deployment.
For an operator, the triggering condition may be far more ordinary. A technician unplugs a device during provisioning. A field unit reconnects. A gadget function cycles during configuration. A DHCP process expects the same interface to exist. The failure appears not as “CVE exploited,” but as a device that cannot be recovered without a reboot or manual intervention.
Security teams often underestimate bugs like this because the attacker story is constrained. Operations teams often overestimate them because every intermittent USB-networking failure becomes suspect. The disciplined position is between those poles: this is a kernel lifecycle vulnerability with plausible denial-of-service consequences in affected configurations, and it is worth patching where USB gadget NCM is part of real use.
Microsoft’s Appearance in the Trail Is a Reminder About CVE Plumbing
The user-facing source here is Microsoft’s Security Update Guide entry, which may look odd for a Linux kernel CVE. But CVE records increasingly move through multiple public databases, vendor portals, aggregators, and advisory systems. The presence of an MSRC page does not mean Windows contains the vulnerable Linux driver, nor does it mean Microsoft authored the kernel patch.For Windows admins, this distinction is important. MSRC is often the first stop for Microsoft product vulnerabilities, but the CVE ecosystem is broader than Microsoft. A CVE page can surface information about third-party components, cross-platform dependencies, or records that security tooling correlates in ways that are useful but easy to misread.
The relevant source of the fix is the Linux kernel stable tree. The relevant consumer action is therefore not “check Windows Update” but “check the Linux kernel version or vendor firmware for the device that exposes USB gadget NCM.” If that device is a phone-like Linux system, an appliance, a lab board, or a custom embedded image, the patch path likely runs through its OS vendor, BSP maintainer, OEM firmware update, or internal kernel build pipeline.
This is a common modern patch-management trap. The machine on the admin’s desk may be Windows, the vulnerable component may be Linux, the advisory may appear in Microsoft’s database, and the actual remediation may require a device firmware update from a third party. The CVE is the common language, not the delivery mechanism.
Embedded Linux Turns Small Kernel Bugs Into Long-Tail Problems
Mainline and stable kernel fixes are only the beginning. Many devices that use USB gadget mode do not run a current distribution kernel with prompt package updates. They run vendor kernels, Android-derived trees, board-support packages, or heavily patched long-term branches. Some are actively maintained. Some are effectively frozen the day the product ships.That is where CVE-2026-43421 becomes a long-tail problem. The upstream fix can be small and well-understood, but the affected product may sit behind an OEM update cadence, a carrier approval process, a field-service policy, or an internal firmware build that nobody wants to touch unless the device is visibly broken. USB gadget networking is common in exactly the kinds of products where kernel updates are not as routine as Windows monthly servicing.
The irony is that this bug may be easier to justify operationally than many abstract CVEs. If a device has suffered from unstable NCM behavior, broken DHCP after reconnect, or odd sysfs remnants, the patch is not just a security checkbox. It is a reliability fix with a security identifier attached.
That can help administrators argue for action. A CVE without a score may not move a procurement committee. A reproducible provisioning failure, a crash on disconnect, or a DHCP regression tied to the same code path often will.
The Patch Also Shows Why Regression History Belongs in Advisories
One welcome feature of the CVE text is that it preserves the history of failed fixes. Too many advisories flatten a vulnerability into a one-sentence defect and a version number. Here, the record explains why two prior approaches were not acceptable: one harmed power management and link state behavior, and the other broke the stable relationship userspace needed.That history is valuable because it warns downstream maintainers not to cherry-pick blindly. A vendor kernel may already carry one of the earlier attempts. A custom tree may have reverted part of it. A product team may see that “f_ncm lifecycle” was addressed once and assume the matter is closed. The CVE’s chronology says otherwise: the correct fix is not merely any patch touching f_ncm lifetime management, but the one that preserves interface identity while reparenting the device safely.
This is especially important for long-term stable branches. Backporting a kernel fix across versions is rarely a pure copy-and-paste exercise. Helper functions, cleanup macros, and surrounding subsystem behavior may differ. The CVE references multiple stable commits, suggesting that maintainers have done the work for several supported lines, but downstream trees still need verification rather than assumption.
For sysadmins, the actionable version of that warning is simple: do not accept “we patched something in USB gadget” as the final answer. Ask whether the build includes the
device_move-based f_ncm lifecycle fix and any dependent helpers or follow-up fixes required by that branch.The Windows Host May Only See the Symptom
On a Windows PC, the most visible part of this issue may be a USB network adapter that comes and goes. Windows may enumerate the gadget, assign or retain a network profile, request DHCP, and then behave according to what the Linux side presents. If the gadget-side interface state is inconsistent, Windows is not necessarily the source of the failure even if it is where the user notices the outage.That distinction matters in troubleshooting. A Windows event log may show device arrival, removal, DHCP timeout, or adapter state changes. Device Manager may show a transient USB network interface. Network troubleshooting may point to address assignment. None of that proves the Windows host is broken.
In mixed environments, engineers should capture both sides. On the Linux gadget, sysfs paths under the network class, kernel logs around bind/unbind, and interface naming after reconnect are relevant. On the Windows host, USB enumeration events and DHCP behavior can establish the timeline. The bug described by CVE-2026-43421 is specifically about the gadget-side relationship between a network device and its parent, so the smoking gun is more likely in the Linux kernel log than in Windows networking policy.
This is a useful mental model for a lot of USB-C-era troubleshooting. The cable is not a passive boundary. It is a negotiation surface between operating systems, firmware, device classes, and power states. When something fails, the visible endpoint is not always the responsible endpoint.
The Threat Model Is Narrower Than the Patch Priority
CVE records often collapse two separate questions into one dashboard entry: how easy is exploitation, and how quickly should we apply the fix? For CVE-2026-43421, those answers may diverge.Exploitation appears constrained by access to the affected gadget behavior. That lowers the likelihood for many traditional enterprise desktops and servers. But patch priority may still be high for device makers and labs because the affected path sits in connection management. Anything that can crash or wedge a device during connect/disconnect cycles deserves attention in products that must be recovered remotely or operated by non-experts.
There is also the matter of trust boundaries. A Linux gadget device may be plugged into an untrusted host, or a trusted Windows host may connect to a gadget device of uncertain provenance. USB has always been awkward for security because physical access and device identity blur quickly. A denial-of-service condition in the gadget stack may be sufficient to disrupt provisioning, kiosk operations, mobile workflows, or field diagnostics even if it does not hand an attacker shell access.
Administrators should therefore resist both extremes. This is not a broad Windows emergency. It is also not irrelevant simply because the affected code is in Linux. The right priority depends on whether USB NCM gadget networking is part of the environment’s operational fabric.
The Practical Test Is Whether Your Devices Speak NCM
The quickest inventory question is whether any managed or supported devices expose Linux USB gadget networking using NCM. In many organizations, that question will not map cleanly to a CMDB field. It may live in engineering notes, imaging scripts, lab documentation, mobile device procedures, or the memory of the one person who built the provisioning rig.NCM is often chosen because it is more efficient and modern than older USB Ethernet approaches. It can be attractive for tethering, embedded management, and phone-to-host networking. But that also means it may be buried inside products that nobody labels “USB gadget devices” in procurement language.
For Linux distributions and device images under direct control, the answer is to track the kernel stable updates and confirm the specific f_ncm patch is present. For vendor devices, the answer is to press for firmware or OS release notes that mention CVE-2026-43421 or the underlying f_ncm lifecycle fix. For unsupported devices, the answer may be a compensating-control discussion: limit untrusted physical access, avoid repeated gadget reconfiguration in production workflows, and document recovery procedures if the USB network path fails.
There is no universal Windows-side mitigation that fixes a Linux gadget’s internal object lifetime. The host can sometimes avoid triggering problematic cycles by using cleaner disconnect procedures or avoiding unstable provisioning scripts, but that is a workaround at best. The fix belongs in the gadget kernel.
The Small Patch With the Big Architectural Lesson
The kernel community’s answer here is elegant because it does not pretend the object has only one correct home. During active binding, the network device belongs under the gadget. During unbind, it can be moved to the virtual device hierarchy. The interface remains visible and stable enough for userspace, while the kernel avoids dangling links to a device that no longer exists.That is a broader design lesson for operating systems. Stability is not always achieved by destroying and recreating objects at clean lifecycle boundaries. Sometimes stability requires preserving identity while changing parentage. Userspace wants continuity; kernel internals want correctness.
device_move is the compromise.Windows has its own analogues in Plug and Play, network adapter persistence, device instance IDs, and power-state transitions. Admins have seen similar classes of pain when a “new” adapter appears after a driver change, when a virtual NIC loses its profile, or when a docking station path changes enough to make Windows treat familiar hardware as unfamiliar. Different kernel, same human problem: identity is a contract, and userspace builds policy around it.
That is why CVE-2026-43421 is more than a Linux footnote. It is another example of how device identity has become a security and reliability primitive. Break the identity contract, and services fail in ways that look disproportionate to the tiny patch that eventually fixes them.
The Patch Queue Now Has a USB-Shaped Warning Label
For teams deciding what to do next, the concrete guidance is less dramatic than the CVE label but more specific than “patch everything.” The record points to a real kernel bug, the fix exists in stable commits, and the affected population is concentrated around Linux systems using USB gadget NCM.- Organizations should identify Linux-based devices, images, or products that expose USB networking through the f_ncm gadget driver.
- Kernel maintainers should verify that their branch carries the
device_move-based lifecycle fix, not merely an earlier attempted workaround. - Windows support teams should treat recurring USB network adapter failures during gadget reconnects as potentially gadget-side kernel issues, not automatically as Windows driver problems.
- Embedded vendors should document whether firmware updates include CVE-2026-43421, because customers cannot infer gadget-driver exposure from a product name.
- Security teams should classify the issue as environment-dependent, with higher urgency for provisioning rigs, field devices, and products that rely on stable USB NCM networking.
- Operators should watch for related follow-up fixes in the USB gadget and u_ether code paths, since lifecycle repairs often expose adjacent assumptions.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center