CVE-2026-31723 is a medium-severity Linux kernel flaw published on May 1, 2026, involving the USB gadget
The headline fact is almost modest: local access, low attack complexity, low privileges, no user interaction, no confidentiality or integrity impact, and a high availability impact under CVSS 3.1. That combination produces the familiar “medium” rating, which is easy to ignore if your patch queue is already filled with remote code execution bugs and privilege escalations.
But kernel CVEs rarely map cleanly to enterprise intuition. A local denial-of-service in a desktop application is one thing; a local crash or device-tree inconsistency inside the kernel’s USB gadget stack is another. The latter lives in the substrate that routers, test rigs, Android-derived devices, industrial controllers, single-board computers, lab equipment, and custom USB peripherals use to present themselves to a host machine.
The bug sits in Linux’s USB gadget world, not the more familiar side where a PC consumes USB devices. Gadget mode is the mode that lets a Linux system become the USB device: a network adapter, serial interface, storage function, composite device, or some combination of those identities. That makes the affected code more relevant to embedded builders and hardware-adjacent administrators than to the average laptop user.
This is also why the vulnerability can look small in a scanner and still deserve attention. The failure mode is not a clean “attacker gets root” story. It is a lifecycle bug: an object in the kernel’s networking layer remains alive after the device tree it was attached to has been torn down, leaving sysfs pointing at a target that no longer exists.
That leaves
In ordinary admin language, that sounds like a stale file-system artifact. In kernel language, it is a sign that the object lifetime model is wrong. Sysfs is not just decorative metadata for command-line tools; it is the user-space projection of the kernel’s device model, and it is heavily relied on by udev rules, network managers, inventory agents, power-management logic, container runtimes, and scripts that assume the kernel will not lie about object ancestry.
The fix uses
That distinction matters. The kernel is full of code that survives because the common path works. Bugs like this are found when the uncommon path — bind, unbind, rebind, legacy composite behavior, repeated teardown — exposes assumptions that were never made explicit enough.
The
That is why the parent-child relationship in sysfs is not trivia. If the network interface is part of a gadget, the kernel’s device hierarchy should reflect that. If the gadget disappears, the network interface must either go away or be moved somewhere sane. Leaving it attached to the ghost of a destroyed gadget is the kernel equivalent of keeping an employee badge active after the building has been demolished.
The patch’s use of
There are several overlapping reasons. Windows Subsystem for Linux uses a Microsoft-shipped Linux kernel. Azure hosts countless Linux workloads. Defender, Intune, cloud security posture tools, container registries, vulnerability management platforms, and software bills of materials all need to reason about Linux packages. Microsoft’s security ecosystem can therefore become a visibility layer for vulnerabilities that are not “Windows bugs” in the traditional sense.
That does not mean every Linux kernel CVE listed near Microsoft tooling affects Windows clients. It means Microsoft’s customers increasingly manage estates where the boundary between Windows, Linux, cloud, and embedded infrastructure is administrative rather than physical. A Windows administrator may never compile a gadget driver, but the organization may still own Linux-based devices that do.
For WSL users, the practical exposure should be treated cautiously. WSL is not a generic embedded USB gadget environment, and the presence of a Linux kernel CVE does not automatically imply exploitable impact inside WSL. The more plausible Microsoft-world relevance is in asset inventory, Azure Linux workloads, container hosts, IoT fleets, and third-party appliances that appear in vulnerability dashboards consumed by Windows-centric teams.
This is where vulnerability management often goes wrong. A scanner sees “Linux kernel” and a CVSS score; an administrator sees “medium”; nobody asks whether the affected kernel configuration includes USB gadget networking, whether the vulnerable function is built, whether untrusted local users can exercise bind and unbind paths, or whether the device is an appliance where a crash equals a field outage.
Kernel version ranges in CVE databases need to be read with care. Mainline, stable, distribution kernels, vendor kernels, and downstream long-term-support trees do not map neatly to a single version string. A fix can be present in a distribution kernel with an older upstream version number, while a nominally newer custom kernel can remain vulnerable if it lacks the backport.
Ubuntu’s tracker listed the issue as medium priority and, at the time of publication, many package lines were still marked as needing evaluation. It also identified the issue as introduced by an older kernel commit and fixed by the mainline patch associated with Linux 7.0-rc7. That combination is typical for kernel CVEs in the modern era: the public CVE record lands, stable patches exist, and distribution-specific status takes time to settle.
The NVD entry’s “Are we missing a CPE?” prompt is also telling. CPE data is often the weakest part of vulnerability metadata for Linux. Kernel code is built into distributions, vendor appliances, Android branches, Yocto images, cloud kernels, live-patched offerings, and custom products. The clean CPE model wants named products and versions; the Linux ecosystem supplies patch streams and configuration options.
For administrators, the sane answer is not to obsess over the CPE list. The sane answer is to map exposure by kernel provenance. If a system gets its kernel from a distribution, follow that distribution’s advisory and package status. If it gets its kernel from a vendor appliance, wait for or request the vendor’s firmware guidance. If your organization builds kernels, check whether the relevant gadget networking code is enabled and whether the
The absence of confidentiality and integrity impact matters. There is no claim here that an attacker can steal data, rewrite files, or jump privilege boundaries. The stated impact is availability, which in kernel space usually means a crash, hang, broken device state, or service disruption.
But availability is contextual. On a developer workstation, a broken USB gadget test may be an annoyance. On a headless field device whose only management path is USB networking, the same class of failure can become a truck roll. On a manufacturing line where boards are provisioned over USB gadget Ethernet, it can stop production.
The local-access requirement also narrows the threat model but does not erase it. “Local” can mean an authenticated shell user, a container escape prerequisite, a compromised management agent, a malicious workload on a development board, or an automated test process that can manipulate configfs gadget state. The relevant question is not whether the internet can hit the bug directly. It is whether anything you do not fully trust can drive the gadget bind and unbind lifecycle.
This is why medium kernel CVEs are so often operationally misunderstood. Security teams rank by score. Platform teams rank by blast radius. Embedded teams rank by how painful recovery is when a device falls off the bus. CVE-2026-31723 sits at the intersection of those mental models.
Kernel subsystems accumulate compatibility obligations. A cleaner fix might be obvious in a world where every driver follows the same modern allocation and registration pattern. The actual kernel has old composite drivers, shared device instances, pre-registration behavior, and user-space expectations that cannot simply be broken because a lifecycle model looks untidy.
This is where the Linux kernel’s strength becomes its maintenance burden. It supports obscure hardware and long-lived patterns precisely because people depend on them. But the price of that compatibility is that a change in object ownership must respect paths that are no longer fashionable but still used.
The
That is also why the fix is more subtle than “delete the interface on unbind.” The
When
The CVE description explicitly calls out power management ordering, which is a sign that the bug is not just cosmetic. Device hierarchy controls more than directory layout. It participates in the order in which devices are suspended, resumed, probed, removed, and accounted for.
This is one reason kernel maintainers take sysfs topology seriously. Broken topology is often the first visible crack in a deeper lifetime issue. If the user-space projection is stale, the in-kernel references may be only one unusual path away from becoming a crash.
For Windows administrators used to Device Manager, the closest analogy is a phantom network adapter whose backing device has already been removed, except the kernel’s internal device graph is part of the failure rather than just the UI. You may be able to ignore it in a lab once. You should not build fleet automation around ignoring it repeatedly.
Repeated lifecycle transitions are exactly where this kind of bug becomes reproducible. A one-time boot bind may never show the problem in a way that matters. A lab script that cycles gadget modes hundreds of times a day can turn a stale-parent bug into a recurring reliability failure.
The risk also rises when local users or services can influence gadget configuration. Many embedded systems expose configfs controls only to privileged code, which reduces the attacker population. But in development and test environments, permissions are often relaxed for convenience. A process that can trigger gadget unbinds may be able to drive the affected path.
That makes CVE-2026-31723 a good example of why “local” should not be read as “irrelevant.” Local-only bugs are often chained with other mistakes, used by already-present malware to destabilize systems, or exploited in shared lab environments where users have more access than production policy would allow.
For appliance vendors, the customer-facing impact may never mention CVE-2026-31723 by name. It may show up as a firmware release note about USB networking stability, gadget rebinding, or sysfs cleanup. The vulnerability database gives security teams the handle; the product team may experience it as a reliability fix.
The second question is where the kernel came from. Distribution kernels should be patched through the distribution’s normal update channel. Vendor appliances should be patched through firmware or BSP updates. Custom kernels need direct review of the relevant stable commits or an upgrade to a fixed tree.
The third question is whether the device’s role makes availability especially important. A kiosk, router, lab controller, phone-derived device, or single-board computer that depends on USB Ethernet for management deserves more urgency than a general-purpose VM whose kernel happens to share ancestry with the affected source.
The fourth question is whether local access is tightly controlled. If gadget configuration is only reachable by root on a locked-down embedded device, the residual risk is lower. If multiple developers, containers, services, or automation jobs can manipulate gadget state, the bug deserves more attention.
This is also a case where reboot discipline matters. Kernel updates do not protect running kernels until the fixed kernel is booted, unless a live-patching mechanism covers the specific change. In embedded estates, a staged reboot plan can be harder than installing the package, especially when devices are remote or physically hard to recover.
CVE-2026-31723 is not a Windows vulnerability in the classic Patch Tuesday sense. It is still the kind of item that lands in the inbox of Windows-heavy IT teams because the estate they defend is no longer Windows-only. The administrative center of gravity may be Microsoft, while the risk object is a Linux kernel embedded in a device, cloud image, or vendor product.
That creates a translation problem. Security dashboards flatten the world into CVE rows. Real remediation requires knowing whether a Linux kernel feature is compiled, whether a device can act as a USB gadget, whether sysfs is exposed to relevant automation, and whether a vendor’s firmware lineage includes the fix.
The best Windows administrators already do this kind of translation for OpenSSL, curl, container base images, Java runtimes, and browser engines. Linux kernel subsystems are simply the next layer down. The trick is to avoid both extremes: do not ignore a kernel CVE because it is not Windows, and do not page the incident team for a USB gadget bug on systems that cannot present themselves as USB devices.
In practical terms, this is a CMDB and ownership problem. If nobody knows which business unit owns the embedded Linux box on the lab bench, nobody will know whether CVE-2026-31723 matters until something breaks. Vulnerability management begins to look a lot like asset management because, at this layer, they are the same discipline.
This is also a reminder that Linux kernel CVEs increasingly include fixes that older security taxonomies struggle to describe. NVD’s weakness entry is “insufficient information,” which is not surprising. The bug is not neatly a classic use-after-free in the public description, nor a simple null pointer dereference, nor an authorization bypass. It is a lifecycle mismatch in a particular subsystem.
That ambiguity does not make the CVE meaningless. It means the vulnerability label is carrying an engineering story rather than a Hollywood exploit story. For the people responsible for resilient systems, that may be more useful.
The affected stable ranges and release-candidate references also show the continuing importance of tracking the kernel as a living product rather than a static version number. A device on an old branch may be patched. A device on a newer branch may not be. A vendor tree may carry the fix under a different package version. The only reliable answer is in the patch lineage.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
f_subset driver, where a network device can outlive its sysfs parent during bind and unbind cycles and leave broken kernel device links behind. It is not the kind of bug that should send Windows desktop users scrambling, but it is exactly the kind of quiet kernel hygiene problem that matters in appliances, embedded systems, developer boards, and Linux-backed infrastructure. The vulnerability’s practical lesson is less about USB networking as a dramatic attack surface and more about how fragile device lifetimes become when the kernel is asked to impersonate hardware on demand.
 A Medium CVE With a Very Kernel-Shaped Warning Label
A Medium CVE With a Very Kernel-Shaped Warning Label
The headline fact is almost modest: local access, low attack complexity, low privileges, no user interaction, no confidentiality or integrity impact, and a high availability impact under CVSS 3.1. That combination produces the familiar “medium” rating, which is easy to ignore if your patch queue is already filled with remote code execution bugs and privilege escalations.But kernel CVEs rarely map cleanly to enterprise intuition. A local denial-of-service in a desktop application is one thing; a local crash or device-tree inconsistency inside the kernel’s USB gadget stack is another. The latter lives in the substrate that routers, test rigs, Android-derived devices, industrial controllers, single-board computers, lab equipment, and custom USB peripherals use to present themselves to a host machine.
The bug sits in Linux’s USB gadget world, not the more familiar side where a PC consumes USB devices. Gadget mode is the mode that lets a Linux system become the USB device: a network adapter, serial interface, storage function, composite device, or some combination of those identities. That makes the affected code more relevant to embedded builders and hardware-adjacent administrators than to the average laptop user.
This is also why the vulnerability can look small in a scanner and still deserve attention. The failure mode is not a clean “attacker gets root” story. It is a lifecycle bug: an object in the kernel’s networking layer remains alive after the device tree it was attached to has been torn down, leaving sysfs pointing at a target that no longer exists.
The Broken Symlink Is the Symptom, Not the Disease
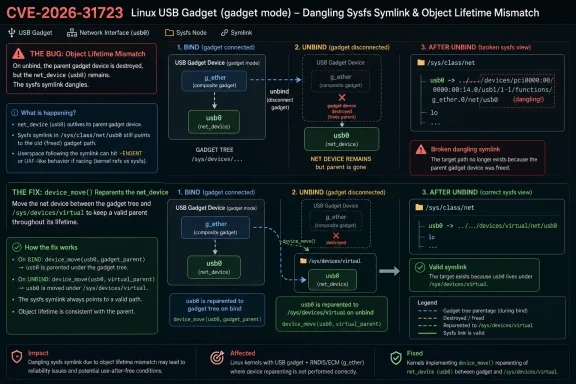
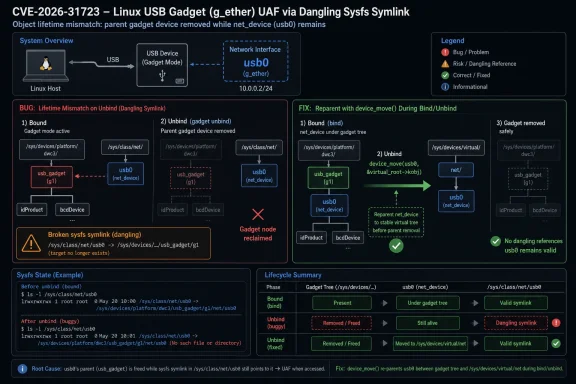
The detail that makes CVE-2026-31723 worth reading is the dangling sysfs path. The network device is allocated when the function instance is created and then registered during the bind phase with the gadget device as its sysfs parent. When the function unbinds, the gadget parent disappears, but thenet_device persists.That leaves
/sys/class/net/usb0 pointing into a device hierarchy that has already been destroyed. A user or management process can see the network interface class entry, follow the symlink, and land on nothing. The system has not merely hidden a device; it has failed to maintain a coherent story about where that device lives.In ordinary admin language, that sounds like a stale file-system artifact. In kernel language, it is a sign that the object lifetime model is wrong. Sysfs is not just decorative metadata for command-line tools; it is the user-space projection of the kernel’s device model, and it is heavily relied on by udev rules, network managers, inventory agents, power-management logic, container runtimes, and scripts that assume the kernel will not lie about object ancestry.
The fix uses
device_move() to reparent the network device between the real gadget device tree and /sys/devices/virtual. On unbind, the device is moved back into the virtual tree before the gadget parent is destroyed. On bind, it is moved under the new gadget. In other words, the patch does not simply hide the broken link; it restores a defensible ownership model.That distinction matters. The kernel is full of code that survives because the common path works. Bugs like this are found when the uncommon path — bind, unbind, rebind, legacy composite behavior, repeated teardown — exposes assumptions that were never made explicit enough.
USB Gadget Mode Is Where Linux Pretends to Be Hardware
For many WindowsForum readers, “USB gadget” may sound like a peripheral feature. In practice, it is one of Linux’s most useful tricks in embedded and development environments. A Raspberry Pi Zero can present itself as a USB Ethernet adapter. Android devices can expose composite interfaces. Test appliances can enumerate as network devices. Boards on a factory bench can be controlled over a USB cable without requiring a separate Ethernet port.The
f_subset function belongs to that broader family of USB network gadget functions. These components help a Linux device present a network interface over USB, often using older or simpler compatibility modes where hosts expect a particular kind of USB Ethernet behavior. The name is obscure, but the model is straightforward: the Linux target becomes the thing the host sees.That is why the parent-child relationship in sysfs is not trivia. If the network interface is part of a gadget, the kernel’s device hierarchy should reflect that. If the gadget disappears, the network interface must either go away or be moved somewhere sane. Leaving it attached to the ghost of a destroyed gadget is the kernel equivalent of keeping an employee badge active after the building has been demolished.
The patch’s use of
/sys/devices/virtual is a clue to the intended design. A net_device can exist independently of a physical device parent, but the system must be explicit about that state. The device is virtual when it is not bound to a live gadget. It is under the gadget when the gadget exists. That sounds obvious only after the patch has made it so.Why Microsoft Users Are Seeing a Linux Kernel CVE
The user-submitted source points to Microsoft’s Security Response Center, which may feel strange for a Linux kernel CVE. That strangeness is now normal. Microsoft ships, supports, scans, documents, and depends on Linux in enough places that Linux kernel vulnerabilities routinely surface in Microsoft-adjacent security workflows.There are several overlapping reasons. Windows Subsystem for Linux uses a Microsoft-shipped Linux kernel. Azure hosts countless Linux workloads. Defender, Intune, cloud security posture tools, container registries, vulnerability management platforms, and software bills of materials all need to reason about Linux packages. Microsoft’s security ecosystem can therefore become a visibility layer for vulnerabilities that are not “Windows bugs” in the traditional sense.
That does not mean every Linux kernel CVE listed near Microsoft tooling affects Windows clients. It means Microsoft’s customers increasingly manage estates where the boundary between Windows, Linux, cloud, and embedded infrastructure is administrative rather than physical. A Windows administrator may never compile a gadget driver, but the organization may still own Linux-based devices that do.
For WSL users, the practical exposure should be treated cautiously. WSL is not a generic embedded USB gadget environment, and the presence of a Linux kernel CVE does not automatically imply exploitable impact inside WSL. The more plausible Microsoft-world relevance is in asset inventory, Azure Linux workloads, container hosts, IoT fleets, and third-party appliances that appear in vulnerability dashboards consumed by Windows-centric teams.
This is where vulnerability management often goes wrong. A scanner sees “Linux kernel” and a CVSS score; an administrator sees “medium”; nobody asks whether the affected kernel configuration includes USB gadget networking, whether the vulnerable function is built, whether untrusted local users can exercise bind and unbind paths, or whether the device is an appliance where a crash equals a field outage.
The Version Range Looks Broad Because Kernel Backports Are Messy
The NVD change history supplied with the report lists affected Linux kernel configurations spanning very old and very new branches, including ranges from 3.11 up to fixed stable versions and release candidates in the 7.0 cycle. On its face, that looks alarming: more than a decade of kernel history implicated by a USB gadget lifecycle bug.Kernel version ranges in CVE databases need to be read with care. Mainline, stable, distribution kernels, vendor kernels, and downstream long-term-support trees do not map neatly to a single version string. A fix can be present in a distribution kernel with an older upstream version number, while a nominally newer custom kernel can remain vulnerable if it lacks the backport.
Ubuntu’s tracker listed the issue as medium priority and, at the time of publication, many package lines were still marked as needing evaluation. It also identified the issue as introduced by an older kernel commit and fixed by the mainline patch associated with Linux 7.0-rc7. That combination is typical for kernel CVEs in the modern era: the public CVE record lands, stable patches exist, and distribution-specific status takes time to settle.
The NVD entry’s “Are we missing a CPE?” prompt is also telling. CPE data is often the weakest part of vulnerability metadata for Linux. Kernel code is built into distributions, vendor appliances, Android branches, Yocto images, cloud kernels, live-patched offerings, and custom products. The clean CPE model wants named products and versions; the Linux ecosystem supplies patch streams and configuration options.
For administrators, the sane answer is not to obsess over the CPE list. The sane answer is to map exposure by kernel provenance. If a system gets its kernel from a distribution, follow that distribution’s advisory and package status. If it gets its kernel from a vendor appliance, wait for or request the vendor’s firmware guidance. If your organization builds kernels, check whether the relevant gadget networking code is enabled and whether the
device_move() lifecycle fix is present.The Severity Score Gets the Shape Right and the Drama Wrong
CVSS 3.1 rates this as 5.5: local attack vector, low complexity, low privileges, no user interaction, unchanged scope, no confidentiality impact, no integrity impact, and high availability impact. That is a reasonable machine-readable summary. It is also a poor substitute for deciding whether to patch now, patch later, or document as non-applicable.The absence of confidentiality and integrity impact matters. There is no claim here that an attacker can steal data, rewrite files, or jump privilege boundaries. The stated impact is availability, which in kernel space usually means a crash, hang, broken device state, or service disruption.
But availability is contextual. On a developer workstation, a broken USB gadget test may be an annoyance. On a headless field device whose only management path is USB networking, the same class of failure can become a truck roll. On a manufacturing line where boards are provisioned over USB gadget Ethernet, it can stop production.
The local-access requirement also narrows the threat model but does not erase it. “Local” can mean an authenticated shell user, a container escape prerequisite, a compromised management agent, a malicious workload on a development board, or an automated test process that can manipulate configfs gadget state. The relevant question is not whether the internet can hit the bug directly. It is whether anything you do not fully trust can drive the gadget bind and unbind lifecycle.
This is why medium kernel CVEs are so often operationally misunderstood. Security teams rank by score. Platform teams rank by blast radius. Embedded teams rank by how painful recovery is when a device falls off the bus. CVE-2026-31723 sits at the intersection of those mental models.
Legacy Composite Drivers Keep Old Assumptions Alive
One of the most interesting details in the description is the explicit mention of compatibility with legacy composite drivers, includingmulti.c. The patch uses a bound flag to indicate whether the network device is shared and pre-registered during a legacy driver’s bind phase. That is a small implementation note with a larger design story behind it.Kernel subsystems accumulate compatibility obligations. A cleaner fix might be obvious in a world where every driver follows the same modern allocation and registration pattern. The actual kernel has old composite drivers, shared device instances, pre-registration behavior, and user-space expectations that cannot simply be broken because a lifecycle model looks untidy.
This is where the Linux kernel’s strength becomes its maintenance burden. It supports obscure hardware and long-lived patterns precisely because people depend on them. But the price of that compatibility is that a change in object ownership must respect paths that are no longer fashionable but still used.
The
bound flag is not glamorous. It is the kind of state variable reviewers scrutinize because it can become another source of future confusion. In this case, it exists to distinguish ordinary lifecycle transitions from legacy sharing behavior so that the network device is moved rather than freed or incorrectly reparented.That is also why the fix is more subtle than “delete the interface on unbind.” The
net_device may be allocated at instance creation and survive across bind cycles by design. The bug is not survival itself. The bug is survival with the wrong parent.Sysfs Bugs Become User-Space Bugs by Proxy
Sysfs is sometimes treated as a read-only convenience layer for humans. In modern Linux systems, it is closer to a contract. User space watches it, walks it, names devices through it, applies policy based on it, and often treats its topology as truth.When
/sys/class/net/usb0 points to a destroyed gadget path, the immediate symptom is a broken symlink. The downstream symptoms can be stranger. A network manager may misclassify an interface. A script may fail during teardown. A test harness may assume a device still exists. A monitoring agent may spam errors. A power-management path may execute in an order the kernel did not intend.The CVE description explicitly calls out power management ordering, which is a sign that the bug is not just cosmetic. Device hierarchy controls more than directory layout. It participates in the order in which devices are suspended, resumed, probed, removed, and accounted for.
This is one reason kernel maintainers take sysfs topology seriously. Broken topology is often the first visible crack in a deeper lifetime issue. If the user-space projection is stale, the in-kernel references may be only one unusual path away from becoming a crash.
For Windows administrators used to Device Manager, the closest analogy is a phantom network adapter whose backing device has already been removed, except the kernel’s internal device graph is part of the failure rather than just the UI. You may be able to ignore it in a lab once. You should not build fleet automation around ignoring it repeatedly.
The Real Exposure Is in Devices That Rebind Often
The most exposed systems are likely not ordinary Linux servers sitting in racks with no USB gadget role enabled. They are devices and workflows that repeatedly create, bind, unbind, and rebind USB gadget functions. That includes embedded development, manufacturing provisioning, QA labs, Android-derived systems, USB Ethernet gadgets, and products that use configfs to dynamically compose USB identities.Repeated lifecycle transitions are exactly where this kind of bug becomes reproducible. A one-time boot bind may never show the problem in a way that matters. A lab script that cycles gadget modes hundreds of times a day can turn a stale-parent bug into a recurring reliability failure.
The risk also rises when local users or services can influence gadget configuration. Many embedded systems expose configfs controls only to privileged code, which reduces the attacker population. But in development and test environments, permissions are often relaxed for convenience. A process that can trigger gadget unbinds may be able to drive the affected path.
That makes CVE-2026-31723 a good example of why “local” should not be read as “irrelevant.” Local-only bugs are often chained with other mistakes, used by already-present malware to destabilize systems, or exploited in shared lab environments where users have more access than production policy would allow.
For appliance vendors, the customer-facing impact may never mention CVE-2026-31723 by name. It may show up as a firmware release note about USB networking stability, gadget rebinding, or sysfs cleanup. The vulnerability database gives security teams the handle; the product team may experience it as a reliability fix.
Patch Management Has to Start With Configuration, Not Panic
The first operational question is whether the affected code is present and reachable. Many kernels do not build every USB gadget function. Many servers do not expose gadget mode at all. Many cloud workloads have no practical path to exercise this code, even if their kernel source package contains the vulnerable file.The second question is where the kernel came from. Distribution kernels should be patched through the distribution’s normal update channel. Vendor appliances should be patched through firmware or BSP updates. Custom kernels need direct review of the relevant stable commits or an upgrade to a fixed tree.
The third question is whether the device’s role makes availability especially important. A kiosk, router, lab controller, phone-derived device, or single-board computer that depends on USB Ethernet for management deserves more urgency than a general-purpose VM whose kernel happens to share ancestry with the affected source.
The fourth question is whether local access is tightly controlled. If gadget configuration is only reachable by root on a locked-down embedded device, the residual risk is lower. If multiple developers, containers, services, or automation jobs can manipulate gadget state, the bug deserves more attention.
This is also a case where reboot discipline matters. Kernel updates do not protect running kernels until the fixed kernel is booted, unless a live-patching mechanism covers the specific change. In embedded estates, a staged reboot plan can be harder than installing the package, especially when devices are remote or physically hard to recover.
The Windows Admin’s Kernel Problem Is Now Cross-Platform
WindowsForum readers have lived through a decade in which Microsoft’s platform perimeter has dissolved. Hyper-V hosts Linux guests. Windows developers use WSL. Azure fleets run Linux at massive scale. Defender watches non-Windows endpoints. DevOps pipelines build containers that may carry kernel assumptions even when they do not ship a kernel themselves.CVE-2026-31723 is not a Windows vulnerability in the classic Patch Tuesday sense. It is still the kind of item that lands in the inbox of Windows-heavy IT teams because the estate they defend is no longer Windows-only. The administrative center of gravity may be Microsoft, while the risk object is a Linux kernel embedded in a device, cloud image, or vendor product.
That creates a translation problem. Security dashboards flatten the world into CVE rows. Real remediation requires knowing whether a Linux kernel feature is compiled, whether a device can act as a USB gadget, whether sysfs is exposed to relevant automation, and whether a vendor’s firmware lineage includes the fix.
The best Windows administrators already do this kind of translation for OpenSSL, curl, container base images, Java runtimes, and browser engines. Linux kernel subsystems are simply the next layer down. The trick is to avoid both extremes: do not ignore a kernel CVE because it is not Windows, and do not page the incident team for a USB gadget bug on systems that cannot present themselves as USB devices.
In practical terms, this is a CMDB and ownership problem. If nobody knows which business unit owns the embedded Linux box on the lab bench, nobody will know whether CVE-2026-31723 matters until something breaks. Vulnerability management begins to look a lot like asset management because, at this layer, they are the same discipline.
The Small USB Fix That Teaches a Larger Maintenance Lesson
The concrete fix is narrow: usedevice_move() to put the network device under the correct parent as gadget binding state changes. The broader lesson is that device lifetime is security-relevant even when no attacker-controlled buffer overflow is in sight. An object that survives longer than its parent can produce inconsistent state, and inconsistent state is where denial-of-service bugs breed.This is also a reminder that Linux kernel CVEs increasingly include fixes that older security taxonomies struggle to describe. NVD’s weakness entry is “insufficient information,” which is not surprising. The bug is not neatly a classic use-after-free in the public description, nor a simple null pointer dereference, nor an authorization bypass. It is a lifecycle mismatch in a particular subsystem.
That ambiguity does not make the CVE meaningless. It means the vulnerability label is carrying an engineering story rather than a Hollywood exploit story. For the people responsible for resilient systems, that may be more useful.
The affected stable ranges and release-candidate references also show the continuing importance of tracking the kernel as a living product rather than a static version number. A device on an old branch may be patched. A device on a newer branch may not be. A vendor tree may carry the fix under a different package version. The only reliable answer is in the patch lineage.
The Practical Reading for CVE-2026-31723
CVE-2026-31723 should be treated as a targeted kernel availability issue for Linux systems that use USB gadget networking, not as a general emergency for every Windows or Linux machine in the building. The useful response is to classify exposure, patch through trusted channels, and verify that gadget-heavy systems are not left relying on stale kernel object relationships.- Systems that do not build or use the affected USB gadget networking function are unlikely to have practical exposure, even if a scanner flags the broader Linux kernel version.
- Embedded devices, development boards, Android-derived systems, lab rigs, and appliances that present USB Ethernet interfaces deserve the closest review.
- Distribution kernels should be remediated through vendor packages rather than ad hoc cherry-picking unless your organization already owns kernel integration and testing.
- Custom kernel teams should confirm that the
net_deviceis reparented correctly across bind and unbind cycles and that legacy composite-driver behavior remains intact. - Windows-focused administrators should treat this as an asset-inventory prompt: determine where Linux gadget-capable devices exist before deciding whether the CVE is urgent.
usb0 symlink that explains it. But the fix captures a larger truth about today’s mixed estates: reliability, security, and device identity now meet deep inside kernel plumbing, and the teams that can trace that plumbing before the next advisory lands will patch faster, panic less, and understand their systems better.Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center