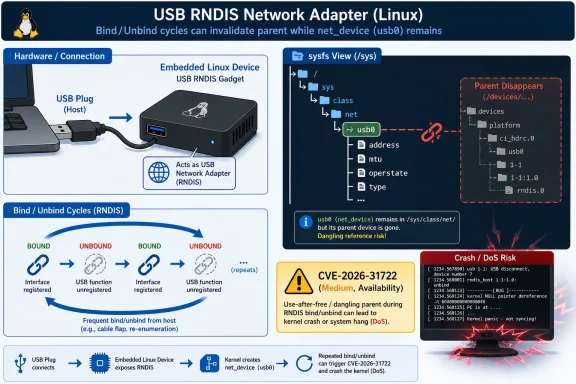
CVE-2026-31722 is a medium-severity Linux kernel vulnerability published by NVD on May 1, 2026, affecting the USB gadget RNDIS function, where repeated bind and unbind cycles can leave a surviving network device attached to a destroyed sysfs parent and crash availability. The bug is not a Windows vulnerability in the classic Patch Tuesday sense, but it is absolutely Windows-adjacent: RNDIS exists because Windows made that USB networking model matter. The interesting story is less about a single dangling symlink than about how old compatibility contracts keep showing up in modern kernel security feeds. For administrators, embedded developers, and anyone shipping Linux-powered devices that pretend to be USB network adapters, this is a reminder that boring lifecycle bugs are often the ones that make production systems brittle.
The CVSS 3.1 score assigned by NVD is 5.5, which puts CVE-2026-31722 squarely in the “medium” bucket. The vector is local, low-complexity, low-privilege, no user interaction, unchanged scope, no confidentiality impact, no integrity impact, and high availability impact. In plainer English: this is not a remote takeover bug, not a credential theft story, and not the sort of vulnerability that should cause panic across desktop fleets.
But “medium” can be a misleading word in infrastructure. A bug that merely knocks over the right embedded device, test jig, kiosk, lab appliance, phone accessory, development board, or USB-connected Linux gadget can still become a real outage. Availability bugs are often treated as second-class vulnerabilities until they occur in systems whose only job is to keep presenting a network interface every time they are plugged in.
The affected component is the Linux USB gadget RNDIS function, commonly represented in kernel code as
NVD’s affected-version data is broad and mechanically precise: Linux kernel lines from 3.11 up to, but not including, 6.12.81; 6.13 up to, but not including, 6.18.22; 6.19 up to, but not including, 6.19.12; and several 7.0 release candidates are listed. As always with kernel CVEs, distribution backports matter more than raw upstream version numbers. A vendor kernel that reports an older version may still contain the fix, while a custom kernel that tracks upstream poorly may not.
Linux supports several USB gadget networking functions, including ECM, EEM, NCM, subset variants, and RNDIS. They overlap in purpose but differ in host compatibility and historical baggage. RNDIS remains especially relevant because Windows support shaped real-world device design for years, even as cleaner standards became preferable in many environments.
That is why a Linux kernel bug can belong on a Windows-focused site without contorting the story. The vulnerable code is in Linux, but the operational context often includes a Windows host. A Windows laptop used by a field technician, a Windows workstation in a lab, or a Windows machine imaging embedded hardware may be the system that exposes the failure mode by repeatedly connecting, disconnecting, testing, or reconfiguring the gadget.
This is also why “not a Windows CVE” does not mean “not a Windows admin’s problem.” Modern Windows environments are full of Linux dependencies: WSL, Hyper-V guests, appliances, edge devices, developer boards, container hosts, NAS boxes, Android-derived equipment, and vendor-supplied gadgets with Linux inside. The vulnerability belongs to Linux, but the operational blast radius can easily cross the USB cable.
That kind of state mismatch is exactly what sysfs is good at revealing. A class link such as
The security impact follows from the kernel’s relationship with sysfs and device lifetime ordering. Kernel subsystems use the device model not merely to make pretty paths under
The fix is conceptually simple: move the network device to a safe parent when the gadget goes away, and move it back when the gadget is rebound. The kernel patch uses
This is the sort of fix that reads less like a security patch than like a correction to a long-standing ownership contract. The code was not failing because an attacker found an exotic packet shape. It was failing because the kernel object model had been asked to tolerate an object whose parent had already disappeared.
That context matters because it changes the editorial read of the CVE. CVE-2026-31722 is not evidence that RNDIS suddenly became uniquely dangerous. It is evidence that a family of related USB gadget networking functions had accumulated similar lifecycle assumptions, and that kernel developers were methodically pushing a corrected pattern through them.
The patch series also dealt with supporting details that rarely appear in vulnerability headlines. There were references to configfs concurrency, reference counting, and compatibility with legacy composite drivers such as
The
This is kernel engineering at its least glamorous and most consequential. Security advisories tend to compress the story into a CVE, a score, and a patch link. The actual work is in preserving twenty years of odd device behavior while making object lifetime rules less wrong.
For developers, this is a useful diagnostic lesson. Filesystem-shaped kernel state can make broken object ownership look deceptively harmless. A symlink that points nowhere may look like cleanup debris, but in the kernel it can also mean reference ordering, parent-child relationships, and teardown semantics no longer agree.
For administrators, the point is less academic. Monitoring systems, udev rules, network managers, provisioning scripts, and hardware test harnesses often assume that sysfs topology is coherent. When gadget devices appear and disappear under automation, stale or inconsistent sysfs state can turn into flaky behavior that is difficult to reproduce outside the lab.
The advisory frames the impact as availability, and that is the right category. A local actor with low privileges may be able to trigger the vulnerable path, depending on how the device exposes gadget configuration and how permissions are assigned. In embedded products, the “local actor” may be a management process, a test routine, a malicious app on the device, or a user with access to a constrained shell.
The important nuance is that exploitability depends heavily on deployment. A standard Windows desktop that merely hosts USB devices is not running Linux gadget code. A Raspberry Pi Zero-style board, Android-derived device, Linux appliance, or custom gadget firmware may be.
The Windows security world has changed. Administrators are no longer managing only Windows kernels on Windows hardware. They are managing mixed estates where Windows laptops talk to Linux peripherals, Windows Server hosts Linux workloads, Azure images ship Linux kernels, and developer endpoints run WSL beside corporate EDR agents. A Linux CVE can therefore be relevant to a Windows shop without being a flaw in
RNDIS makes that relationship especially direct. Windows compatibility is one reason vendors choose RNDIS for USB networking in the first place. A Linux gadget exposing RNDIS is often doing so because it expects a Windows host to recognize it without heroic driver work. That convenience is exactly why old interface choices linger.
This is not an indictment of Windows. It is a warning about compatibility as a security surface. Every protocol kept alive for painless interoperability becomes part of the maintenance burden of both sides of the cable. Even when the vulnerability lives in Linux, the ecosystem that encouraged the interface helps keep the code path hot.
For WindowsForum readers, the practical takeaway is straightforward: do not search Windows Update for salvation. Look at the Linux kernel in the device, appliance, board, image, or distribution that implements USB gadget RNDIS. If you own the host but not the gadget, the mitigation path may involve vendor firmware, not a Microsoft patch.
That is why the right question is not simply “am I running 6.12.80?” The better question is whether the relevant patch for
The broad vulnerable range also reflects the age of the underlying code path. The lower bound reaches back to Linux 3.11, which underscores how long USB gadget networking assumptions can persist. Long-lived code in the kernel is not automatically dangerous, but it often carries compatibility decisions made under very different device-model expectations.
The listed fixed thresholds are also a reminder that multiple stable series matter simultaneously. A fix can land in several maintained branches, and organizations may be pinned to one branch for vendor certification, real-time patches, hardware enablement, or product lifecycle reasons. The existence of a fixed 6.19.x release does not help a vendor locked to a heavily modified 6.12-based tree unless the patch is backported.
For anyone maintaining a product, the cleanest evidence is not a marketing claim that the kernel is “updated.” It is a changelog, commit reference, or source diff showing that the RNDIS gadget lifecycle fix is present. Security teams should ask vendors for that level of specificity.
A gadget device may allow configuration through scripts, debug shells, local web interfaces, privileged helper processes, Android system services, factory test modes, or physical access workflows. If any of those paths can trigger repeated bind and unbind cycles for the RNDIS function, the bug becomes less theoretical. The vulnerable operation is not sending magic traffic across the network; it is exercising the device lifecycle in the wrong order.
Physical access also matters. USB gadget features often exist precisely because a device will be attached to something else by cable. If a product’s threat model includes malicious or untrusted physical users, denial-of-service bugs in USB presentation logic deserve more attention than their CVSS score might suggest.
There is also a product reliability angle that security scoring cannot capture well. A kernel crash in a development board is annoying. The same crash in a point-of-sale peripheral, service tool, medical-adjacent accessory, vehicle diagnostic adapter, or industrial control interface can become operationally expensive. Even if the attacker model is weak, the bug may still be worth fixing quickly because crashes during connection churn are the kind users remember.
This is where kernel CVEs blur into quality engineering. A vulnerability disclosure creates urgency, but the underlying failure mode is also a defect in how the device behaves under repeated attach, detach, and reconfiguration. For product teams, patching it improves both security posture and supportability.
That history leaves kernel maintainers supporting old paths long after newer alternatives exist. NCM is generally a more modern USB networking option. ECM is common in non-Windows ecosystems. But product compatibility decisions are not made in a vacuum; they are made around driver availability, customer operating systems, field support scripts, and the cost of changing manufacturing images.
The result is a layered ecosystem where modern Linux kernels still carry code designed around legacy host expectations. That is not inherently bad. Backward compatibility is one reason general-purpose operating systems are useful. But it does mean that obscure lifecycle mistakes in old compatibility plumbing remain security-relevant.
The irony is that the vulnerability here is not in RNDIS packet semantics. It is in how Linux manages the network device object backing the RNDIS function. The legacy interface keeps the path alive; the kernel device model bug supplies the failure. Compatibility opens the door, but lifecycle discipline determines whether walking through it is safe.
For IT buyers and integrators, this should influence procurement questions. If a vendor’s device exposes USB networking, ask which gadget function it uses, how firmware updates are delivered, and whether the vendor tracks upstream kernel CVEs. “It appears as a network adapter on Windows” is not a complete support story.
CVE-2026-31722 sits right in that tension. It is a real bug with a real availability impact, but it is not a universal emergency. It affects a specific subsystem under specific conditions. The right reaction is neither panic nor dismissal; it is asset-aware triage.
Security tooling, however, often lacks that nuance. A scanner may flag “Linux kernel vulnerable” based on broad CPE ranges, while the actual system may not enable USB gadget mode, may not build
This is why kernel CVEs increasingly demand collaboration between security teams and platform engineers. The security team can identify the CVE and severity. The platform engineer can say whether
The administrative work is not glamorous, but it is concrete. Inventory the systems that can act as USB gadgets. Identify whether they expose RNDIS. Check vendor firmware or kernel patches. Decide whether an update, configuration change, or feature disablement is appropriate.
Windows administrators may encounter those devices only as peripherals. A field laptop sees an RNDIS adapter appear, gets an address, runs a diagnostic tool, and moves on. The Linux kernel crash, if it happens, occurs on the other end. From the Windows side, it may look like a flaky cable, a bad driver, or a device that randomly disappears.
That misdiagnosis can persist for years. Support teams replace USB cables, reinstall host drivers, blame Windows updates, or script reconnection retries. Meanwhile the underlying gadget firmware may be carrying a known lifecycle bug. CVE-2026-31722 gives that class of problem a sharper name.
The embedded supply chain also slows remediation. Many vendors ship kernels tied to silicon vendor BSPs, out-of-tree patches, and product certification cycles. Pulling in an upstream stable fix is rarely as simple as changing a package version. The good vendors still do it; they just need time, testing, and customer pressure.
That customer pressure should be specific. Asking whether a product is “affected by CVE-2026-31722” is better than asking whether it is “secure.” Asking whether the RNDIS gadget lifecycle patch has been backported is better still. Vendors are more likely to respond usefully when the question maps to a concrete commit and code path.
The first pass should separate ordinary Linux servers from devices capable of USB gadget mode. Most rack servers, cloud VMs, and desktops are USB hosts, not USB gadgets. The affected code is relevant when the Linux system can present a USB network function to another host.
The second pass should look for RNDIS specifically. A gadget that uses NCM, ECM, EEM, or another function may have related lifecycle fixes under separate CVEs or patches, but CVE-2026-31722 is about
The third pass is vendor verification. For managed Linux distributions, consult the distribution’s kernel advisory. For appliances and embedded devices, look for firmware notes or ask the supplier. For in-house products, inspect the kernel tree and update the relevant stable branch.
The temptation will be to treat this as a niche Linux issue. That is partly right, but niche does not mean rare in the places that matter. USB gadget networking is common in exactly the sorts of devices enterprises often forget are computers.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Medium CVE With a Very Specific Blast Radius
A Medium CVE With a Very Specific Blast Radius
The CVSS 3.1 score assigned by NVD is 5.5, which puts CVE-2026-31722 squarely in the “medium” bucket. The vector is local, low-complexity, low-privilege, no user interaction, unchanged scope, no confidentiality impact, no integrity impact, and high availability impact. In plainer English: this is not a remote takeover bug, not a credential theft story, and not the sort of vulnerability that should cause panic across desktop fleets.But “medium” can be a misleading word in infrastructure. A bug that merely knocks over the right embedded device, test jig, kiosk, lab appliance, phone accessory, development board, or USB-connected Linux gadget can still become a real outage. Availability bugs are often treated as second-class vulnerabilities until they occur in systems whose only job is to keep presenting a network interface every time they are plugged in.
The affected component is the Linux USB gadget RNDIS function, commonly represented in kernel code as
f_rndis. In USB gadget mode, Linux is not acting as the USB host; it is acting as the peripheral. That distinction matters because the vulnerable system is the Linux-powered device exposing a network function over USB, not the Windows PC or other host on the far end.NVD’s affected-version data is broad and mechanically precise: Linux kernel lines from 3.11 up to, but not including, 6.12.81; 6.13 up to, but not including, 6.18.22; 6.19 up to, but not including, 6.19.12; and several 7.0 release candidates are listed. As always with kernel CVEs, distribution backports matter more than raw upstream version numbers. A vendor kernel that reports an older version may still contain the fix, while a custom kernel that tracks upstream poorly may not.
RNDIS Is a Windows Compatibility Fossil That Still Has Teeth
RNDIS, short for Remote Network Driver Interface Specification, is one of those technologies that survives because removing it would break too many things that nobody wants to rediscover. It lets a USB device present itself as a network adapter, historically with Windows compatibility as a major reason for its persistence. If you have ever plugged in an embedded board, phone, modem, diagnostic unit, industrial controller, or development platform and seen a USB Ethernet-style interface appear, you have been in this neighborhood.Linux supports several USB gadget networking functions, including ECM, EEM, NCM, subset variants, and RNDIS. They overlap in purpose but differ in host compatibility and historical baggage. RNDIS remains especially relevant because Windows support shaped real-world device design for years, even as cleaner standards became preferable in many environments.
That is why a Linux kernel bug can belong on a Windows-focused site without contorting the story. The vulnerable code is in Linux, but the operational context often includes a Windows host. A Windows laptop used by a field technician, a Windows workstation in a lab, or a Windows machine imaging embedded hardware may be the system that exposes the failure mode by repeatedly connecting, disconnecting, testing, or reconfiguring the gadget.
This is also why “not a Windows CVE” does not mean “not a Windows admin’s problem.” Modern Windows environments are full of Linux dependencies: WSL, Hyper-V guests, appliances, edge devices, developer boards, container hosts, NAS boxes, Android-derived equipment, and vendor-supplied gadgets with Linux inside. The vulnerability belongs to Linux, but the operational blast radius can easily cross the USB cable.
The Bug Is a Lifecycle Mismatch, Not a Packet Parsing Disaster
CVE-2026-31722 is refreshingly mundane in its mechanics. Thenet_device object is allocated during function instance creation and registered during the bind phase with the gadget device as its sysfs parent. When the function unbinds, the gadget parent can be destroyed while the network device survives, leaving sysfs entries that point into a device tree that no longer exists.That kind of state mismatch is exactly what sysfs is good at revealing. A class link such as
/sys/class/net/usb0 may still point toward a gadget path, while the target path itself has vanished. The symptom looks like filesystem weirdness, but the root cause is object lifetime: one object outlived the parent it was still logically attached to.The security impact follows from the kernel’s relationship with sysfs and device lifetime ordering. Kernel subsystems use the device model not merely to make pretty paths under
/sys, but to coordinate references, power management, teardown, and discovery. A stale parent relationship is not just untidy; it can become a kernel crash or other availability failure when later operations walk assumptions that are no longer true.The fix is conceptually simple: move the network device to a safe parent when the gadget goes away, and move it back when the gadget is rebound. The kernel patch uses
device_move() to reparent the net_device between the gadget’s device tree and /sys/devices/virtual across bind and unbind cycles. On final unbind, device_move(NULL) moves the network device into the virtual device tree before the gadget parent is destroyed.This is the sort of fix that reads less like a security patch than like a correction to a long-standing ownership contract. The code was not failing because an attacker found an exotic packet shape. It was failing because the kernel object model had been asked to tolerate an object whose parent had already disappeared.
The Patch Series Shows a Pattern, Not an Isolated Accident
The RNDIS fix did not arrive as a lonely one-off. It was part of a March 2026 patch series aimed at USB gadget network lifecycle and configfs race problems. The series covered dangling sysfs symlink issues across multiple gadget network functions and applied a device-move pattern that had already been used for the NCM function.That context matters because it changes the editorial read of the CVE. CVE-2026-31722 is not evidence that RNDIS suddenly became uniquely dangerous. It is evidence that a family of related USB gadget networking functions had accumulated similar lifecycle assumptions, and that kernel developers were methodically pushing a corrected pattern through them.
The patch series also dealt with supporting details that rarely appear in vulnerability headlines. There were references to configfs concurrency, reference counting, and compatibility with legacy composite drivers such as
multi.c. Those details are the difference between a fix that works in a clean modern test case and a fix that does not break old device configurations in the field.The
borrowed_net flag is a good example of the compromise. Some legacy composite drivers share or pre-register the network device during their bind path. The fix therefore needs to know whether the device is owned in the ordinary way or borrowed from a legacy path. Without that distinction, a lifecycle repair could become a regression factory.This is kernel engineering at its least glamorous and most consequential. Security advisories tend to compress the story into a CVE, a score, and a patch link. The actual work is in preserving twenty years of odd device behavior while making object lifetime rules less wrong.
Sysfs Is the Canary in the Kernel Object Mine
The dangling symlink example in the advisory is not incidental. Sysfs exposes the kernel’s device model to user space, and when sysfs paths stop making sense, it often means the underlying object graph has already gone sour. The link from/sys/class/net/usb0 to a missing gadget device path is the visible crack in a deeper lifecycle contract.For developers, this is a useful diagnostic lesson. Filesystem-shaped kernel state can make broken object ownership look deceptively harmless. A symlink that points nowhere may look like cleanup debris, but in the kernel it can also mean reference ordering, parent-child relationships, and teardown semantics no longer agree.
For administrators, the point is less academic. Monitoring systems, udev rules, network managers, provisioning scripts, and hardware test harnesses often assume that sysfs topology is coherent. When gadget devices appear and disappear under automation, stale or inconsistent sysfs state can turn into flaky behavior that is difficult to reproduce outside the lab.
The advisory frames the impact as availability, and that is the right category. A local actor with low privileges may be able to trigger the vulnerable path, depending on how the device exposes gadget configuration and how permissions are assigned. In embedded products, the “local actor” may be a management process, a test routine, a malicious app on the device, or a user with access to a constrained shell.
The important nuance is that exploitability depends heavily on deployment. A standard Windows desktop that merely hosts USB devices is not running Linux gadget code. A Raspberry Pi Zero-style board, Android-derived device, Linux appliance, or custom gadget firmware may be.
The Windows Angle Is Compatibility, Not Compromise
Microsoft’s presence in the supplied source trail is easy to misread. A CVE appearing in MSRC’s Update Guide does not automatically mean Windows itself is vulnerable. Microsoft tracks third-party vulnerabilities when they intersect with Microsoft products, ecosystems, dependencies, or customer guidance, and Linux kernel issues increasingly fall into that orbit.The Windows security world has changed. Administrators are no longer managing only Windows kernels on Windows hardware. They are managing mixed estates where Windows laptops talk to Linux peripherals, Windows Server hosts Linux workloads, Azure images ship Linux kernels, and developer endpoints run WSL beside corporate EDR agents. A Linux CVE can therefore be relevant to a Windows shop without being a flaw in
ntoskrnl.exe.RNDIS makes that relationship especially direct. Windows compatibility is one reason vendors choose RNDIS for USB networking in the first place. A Linux gadget exposing RNDIS is often doing so because it expects a Windows host to recognize it without heroic driver work. That convenience is exactly why old interface choices linger.
This is not an indictment of Windows. It is a warning about compatibility as a security surface. Every protocol kept alive for painless interoperability becomes part of the maintenance burden of both sides of the cable. Even when the vulnerability lives in Linux, the ecosystem that encouraged the interface helps keep the code path hot.
For WindowsForum readers, the practical takeaway is straightforward: do not search Windows Update for salvation. Look at the Linux kernel in the device, appliance, board, image, or distribution that implements USB gadget RNDIS. If you own the host but not the gadget, the mitigation path may involve vendor firmware, not a Microsoft patch.
Version Numbers Are a Starting Point, Not a Verdict
NVD’s CPE list is useful, but it should not be treated as a complete asset inventory rule. Kernel version ranges in vulnerability databases are often blunt instruments because Linux distributions routinely backport fixes without changing the base version in a way that maps neatly to upstream. Enterprise distributions, embedded BSPs, Android common kernels, and vendor trees may all carry patches that do not line up with upstream release numbering.That is why the right question is not simply “am I running 6.12.80?” The better question is whether the relevant patch for
f_rndis has been applied to the kernel tree that produced the running image. For general-purpose Linux distributions, the answer normally comes from the vendor’s security advisory and package changelog. For embedded devices, it may require checking the board support package, kernel source drop, or firmware release notes.The broad vulnerable range also reflects the age of the underlying code path. The lower bound reaches back to Linux 3.11, which underscores how long USB gadget networking assumptions can persist. Long-lived code in the kernel is not automatically dangerous, but it often carries compatibility decisions made under very different device-model expectations.
The listed fixed thresholds are also a reminder that multiple stable series matter simultaneously. A fix can land in several maintained branches, and organizations may be pinned to one branch for vendor certification, real-time patches, hardware enablement, or product lifecycle reasons. The existence of a fixed 6.19.x release does not help a vendor locked to a heavily modified 6.12-based tree unless the patch is backported.
For anyone maintaining a product, the cleanest evidence is not a marketing claim that the kernel is “updated.” It is a changelog, commit reference, or source diff showing that the RNDIS gadget lifecycle fix is present. Security teams should ask vendors for that level of specificity.
Embedded Linux Turns Local Bugs Into Product Bugs
The phrase “local vulnerability” often causes security teams to down-rank an issue reflexively. On a laptop or server, that can be a reasonable initial instinct. On an embedded Linux device, “local” may describe a much wider and stranger set of actors than it first appears.A gadget device may allow configuration through scripts, debug shells, local web interfaces, privileged helper processes, Android system services, factory test modes, or physical access workflows. If any of those paths can trigger repeated bind and unbind cycles for the RNDIS function, the bug becomes less theoretical. The vulnerable operation is not sending magic traffic across the network; it is exercising the device lifecycle in the wrong order.
Physical access also matters. USB gadget features often exist precisely because a device will be attached to something else by cable. If a product’s threat model includes malicious or untrusted physical users, denial-of-service bugs in USB presentation logic deserve more attention than their CVSS score might suggest.
There is also a product reliability angle that security scoring cannot capture well. A kernel crash in a development board is annoying. The same crash in a point-of-sale peripheral, service tool, medical-adjacent accessory, vehicle diagnostic adapter, or industrial control interface can become operationally expensive. Even if the attacker model is weak, the bug may still be worth fixing quickly because crashes during connection churn are the kind users remember.
This is where kernel CVEs blur into quality engineering. A vulnerability disclosure creates urgency, but the underlying failure mode is also a defect in how the device behaves under repeated attach, detach, and reconfiguration. For product teams, patching it improves both security posture and supportability.
RNDIS Keeps Winning Because “It Just Works” Is a Powerful Drug
The persistence of RNDIS is a case study in platform gravity. Standards with cleaner architecture often lose to interfaces that work with the machines customers already have. For years, “works with Windows” was not merely a convenience; it was a purchasing requirement.That history leaves kernel maintainers supporting old paths long after newer alternatives exist. NCM is generally a more modern USB networking option. ECM is common in non-Windows ecosystems. But product compatibility decisions are not made in a vacuum; they are made around driver availability, customer operating systems, field support scripts, and the cost of changing manufacturing images.
The result is a layered ecosystem where modern Linux kernels still carry code designed around legacy host expectations. That is not inherently bad. Backward compatibility is one reason general-purpose operating systems are useful. But it does mean that obscure lifecycle mistakes in old compatibility plumbing remain security-relevant.
The irony is that the vulnerability here is not in RNDIS packet semantics. It is in how Linux manages the network device object backing the RNDIS function. The legacy interface keeps the path alive; the kernel device model bug supplies the failure. Compatibility opens the door, but lifecycle discipline determines whether walking through it is safe.
For IT buyers and integrators, this should influence procurement questions. If a vendor’s device exposes USB networking, ask which gadget function it uses, how firmware updates are delivered, and whether the vendor tracks upstream kernel CVEs. “It appears as a network adapter on Windows” is not a complete support story.
The Security Feed Is Becoming a Kernel Changelog With CVE Numbers
Linux kernel CVE handling has changed the rhythm of vulnerability management. More kernel fixes now receive CVE identifiers, including issues that look to old-school administrators like stability bugs or correctness fixes. That has benefits: searchable identifiers, clearer tracking, and better pressure on vendors to backport fixes. It also creates noise.CVE-2026-31722 sits right in that tension. It is a real bug with a real availability impact, but it is not a universal emergency. It affects a specific subsystem under specific conditions. The right reaction is neither panic nor dismissal; it is asset-aware triage.
Security tooling, however, often lacks that nuance. A scanner may flag “Linux kernel vulnerable” based on broad CPE ranges, while the actual system may not enable USB gadget mode, may not build
f_rndis, may not expose configfs to untrusted users, or may already carry a vendor backport. Conversely, a custom embedded image may fall through ordinary enterprise scanning entirely.This is why kernel CVEs increasingly demand collaboration between security teams and platform engineers. The security team can identify the CVE and severity. The platform engineer can say whether
CONFIG_USB_CONFIGFS_RNDIS, related gadget functions, or legacy composite drivers are present and reachable. Without both views, organizations either overreact to irrelevant findings or miss the few devices where the issue matters.The administrative work is not glamorous, but it is concrete. Inventory the systems that can act as USB gadgets. Identify whether they expose RNDIS. Check vendor firmware or kernel patches. Decide whether an update, configuration change, or feature disablement is appropriate.
The Real Risk Is in the Devices Nobody Thinks to Patch
The most vulnerable machines in a story like this may not be servers. They may be boxes in closets, boards on benches, instruments in labs, appliances at branch offices, or customer-premises devices that are technically Linux systems but operationally treated as sealed hardware. Those are exactly the places where USB gadget functionality tends to live.Windows administrators may encounter those devices only as peripherals. A field laptop sees an RNDIS adapter appear, gets an address, runs a diagnostic tool, and moves on. The Linux kernel crash, if it happens, occurs on the other end. From the Windows side, it may look like a flaky cable, a bad driver, or a device that randomly disappears.
That misdiagnosis can persist for years. Support teams replace USB cables, reinstall host drivers, blame Windows updates, or script reconnection retries. Meanwhile the underlying gadget firmware may be carrying a known lifecycle bug. CVE-2026-31722 gives that class of problem a sharper name.
The embedded supply chain also slows remediation. Many vendors ship kernels tied to silicon vendor BSPs, out-of-tree patches, and product certification cycles. Pulling in an upstream stable fix is rarely as simple as changing a package version. The good vendors still do it; they just need time, testing, and customer pressure.
That customer pressure should be specific. Asking whether a product is “affected by CVE-2026-31722” is better than asking whether it is “secure.” Asking whether the RNDIS gadget lifecycle patch has been backported is better still. Vendors are more likely to respond usefully when the question maps to a concrete commit and code path.
The Practical Read for Windows-Centric Shops
The short version is that Windows hosts are not the vulnerable endpoint, but Windows-centric environments can still own the risk. If your estate includes Linux-powered USB devices that present themselves as network adapters, this CVE belongs in your triage queue. If it does not, it is probably noise.The first pass should separate ordinary Linux servers from devices capable of USB gadget mode. Most rack servers, cloud VMs, and desktops are USB hosts, not USB gadgets. The affected code is relevant when the Linux system can present a USB network function to another host.
The second pass should look for RNDIS specifically. A gadget that uses NCM, ECM, EEM, or another function may have related lifecycle fixes under separate CVEs or patches, but CVE-2026-31722 is about
f_rndis. The March patch series makes clear that this was part of a broader cleanup, so adjacent gadget networking functions deserve attention too.The third pass is vendor verification. For managed Linux distributions, consult the distribution’s kernel advisory. For appliances and embedded devices, look for firmware notes or ask the supplier. For in-house products, inspect the kernel tree and update the relevant stable branch.
The temptation will be to treat this as a niche Linux issue. That is partly right, but niche does not mean rare in the places that matter. USB gadget networking is common in exactly the sorts of devices enterprises often forget are computers.
The Fix Is Small, the Lesson Is Larger
CVE-2026-31722 is a patchable availability bug in Linux’s USB gadget RNDIS function, but its value as a case study is bigger than its score. It shows how compatibility paths stay alive, how kernel object lifetime mistakes surface as security issues, and how Windows ecosystems can depend on Linux code they do not directly control.- Organizations should patch or obtain firmware updates for Linux devices that expose USB gadget RNDIS and fall within affected kernel ranges.
- Windows endpoints are not the vulnerable systems, but they may be the hosts that interact with vulnerable Linux gadgets during normal operations.
- Kernel version checks should be treated as indicators rather than proof, because distribution and vendor backports can change exposure.
- Embedded and appliance vendors should confirm whether the
device_move()lifecycle fix forf_rndisis present in their shipped kernel trees. - Security teams should inventory USB gadget functionality separately from ordinary Linux server exposure, because the affected code path is specialized.
- Repeated bind, unbind, attach, detach, and configuration workflows deserve testing after patching, because this vulnerability is fundamentally about lifecycle correctness.
f_rndis.c, but the business may still depend on a Linux gadget pretending to be a friendly USB network card for a Windows machine. CVE-2026-31722 will not be remembered as a blockbuster vulnerability, and that is fine; its real warning is quieter, more durable, and more useful: the compatibility code we keep for convenience still has to obey modern lifecycle rules.Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center