CVE-2026-31725, published May 1, 2026 and modified by NVD on May 7, tracks a Linux kernel USB gadget ECM flaw in which a network device can outlive its gadget parent, leaving broken sysfs topology and creating a local denial-of-service risk. The short answer to the CPE question is yes: the current affected-version metadata deserves scrutiny. The more important answer is that this CVE shows how Linux kernel vulnerability tracking can look precise while still leaving administrators with a messy translation problem.
At first glance, CVE-2026-31725 is not the sort of vulnerability that sends incident responders sprinting. NVD scores it as CVSS 3.1 5.5, with local attack vector, low complexity, low privileges required, no user interaction, unchanged scope, no confidentiality or integrity impact, and high availability impact. In plain English, this is not a remote code execution bug and not an obvious privilege-escalation story.
But kernel bugs rarely live only inside their CVSS boxes. This one sits in the USB gadget ECM function, the part of Linux that lets a device present itself as a USB Ethernet adapter to a host. That makes it most relevant to embedded boards, Android-derived systems, appliances, development kits, industrial devices, and lab hardware that expose USB gadget networking.
The bug is not glamorous. A
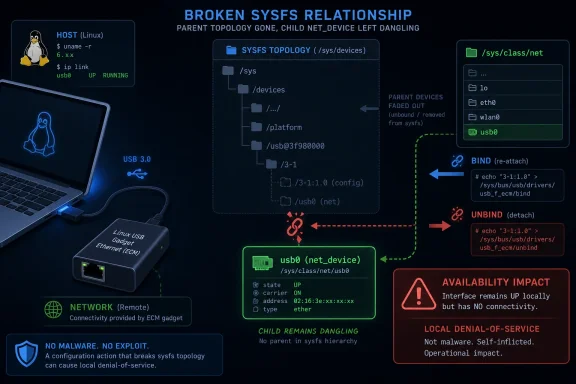
That sounds like housekeeping until you remember that sysfs is not merely a diagnostic convenience. It is a kernel-exported object model used by system services, device managers, monitoring agents, udev rules, scripts, and power-management paths. A dangling sysfs relationship is exactly the kind of kernel state mismatch that can turn a narrow lifecycle bug into an availability problem.
The Linux kernel’s device model depends heavily on parent-child relationships. Those relationships determine how devices appear in sysfs, how teardown ordering works, and how power management understands the hardware graph. If an object survives after its parent is gone, the kernel has not merely lost a label; it has exported a stale topology to userspace.
The fix uses
That is a subtle repair because the code must also preserve compatibility with older composite drivers. The description specifically calls out legacy drivers such as
This is the kind of bug that kernel maintainers fix with a diagram in their heads. The vulnerable state is not a single bad pointer in isolation. It is a timing window between bind, unbind, parent destruction, and userspace observation of the network interface.
USB gadget mode is especially common in devices that want a simple management channel. Plug the device into a PC and it appears as a virtual Ethernet adapter. Sometimes that interface hosts a web UI, a debugging shell, a provisioning service, or a firmware-update endpoint. The Windows machine is the host; the Linux device is pretending to be the network card.
That matters because the vulnerable component is on the device side, not the Windows host side. A Windows laptop is not “vulnerable” merely because it can connect to USB Ethernet gadgets. But a Linux gadget plugged into that laptop may carry the bug, and the operational failure may surface as a flaky network interface, broken enumeration, failed reconfiguration, or a device that needs a reboot after bind/unbind churn.
In enterprise environments, this is where vulnerability management gets uncomfortable. The CVE lands in the Linux kernel, but the asset may be recorded as a badge printer, a kiosk controller, a development board, a conferencing appliance, or a “USB device” attached to a Windows workstation. If the scanner only thinks in server distributions, it may miss the affected hardware entirely.
There are two separate issues here. The first is whether the version ranges correctly reflect every stable branch to which the fix was applied. The second is whether the CPE model is expressive enough to describe a kernel subsystem bug that matters only when a particular driver and configuration path are present.
The NVD entry itself reportedly asks, “Are we missing a CPE here?” That boilerplate appears on many NVD pages, but in this case it captures the real concern. Linux kernel CVEs often begin as upstream commits, then get backported across stable trees. The resulting affected ranges can be correct in broad outline but still misleading for distribution users because Ubuntu, Debian, Red Hat, SUSE, Android vendors, appliance builders, and cloud images do not ship “vanilla kernel 6.12.80” in the same way kernel.org labels it.
The version ranges also need timeline sanity checks. Kernel version numbering after 6.x has become more difficult to interpret when advisory data includes future-looking or release-candidate labels. A CPE that says
So, are we missing a CPE? Possibly. More precisely, we may be missing the right product-level mapping. The vulnerable code is in mainline Linux, but the exploitable population depends on whether a shipped kernel includes the ECM gadget function, whether it is enabled, whether USB gadget functionality is exposed, and whether the affected lifecycle path can be reached by local users or device-management workflows.
Still, “local” can be a slippery word on embedded systems. Many gadgets expose management interfaces, scripting hooks, debugging services, or update mechanisms that allow some level of authenticated local control. A low-privileged local account on an appliance is not always as hard to obtain as a shell on a hardened server.
The impact is availability. The description does not claim data theft, privilege escalation, or arbitrary code execution. It describes broken sysfs symlinks and a topology mismatch that the fix addresses by moving the network device to a safe parent before the gadget device is destroyed.
That makes this a patching priority for reliability-sensitive systems rather than a panic-grade emergency. If your device depends on repeatedly reconfiguring USB gadget functions, hotplugging composite modes, or keeping a virtual Ethernet management link alive through lifecycle transitions, the bug matters. If your Linux hosts never use USB gadget mode, it is probably background noise.
This distinction is where CVSS is useful but insufficient. A medium score can be urgent in a factory line if it bricks provisioning stations. A high score can be irrelevant to an environment with no exposed component. CVE-2026-31725 belongs in the former category for some embedded and lab deployments.
CVE-2026-31725 is a textbook example. The description is technically precise but not packaged for a general IT audience. It assumes readers understand
That is not a criticism of the kernel maintainers. Their first job is to fix the bug. But it does mean the downstream advisory ecosystem has to do translation work: which products enable this path, which branches have the fix, which distribution kernels are affected, and which users can actually trigger the bad state.
MSRC’s appearance as a source context is also a sign of the times. Microsoft’s estate now includes Linux in WSL, Azure, Defender, CBL-Mariner/Azure Linux-derived components, container hosts, appliances, and open-source dependencies. A Linux kernel CVE can show up in Microsoft-facing vulnerability workflows even when the vulnerable component is not Windows itself.
For Windows administrators, that can be confusing. The presence of an MSRC page does not automatically mean “Windows is vulnerable.” It may mean Microsoft is tracking an upstream issue because some Microsoft product, service, container image, or dependency chain includes the affected open-source component. That nuance matters when patch tickets start landing in queues owned by Windows teams.
The challenge is that those systems are often poorly represented in enterprise asset management. A server has an owner, an OS version, an update channel, and a patch window. A USB-attached appliance may have a vendor firmware version, a procurement record, and a sticky note on a lab bench.
For sysadmins, the practical question is not “Do we run Linux?” It is “Do we own devices that run Linux and expose USB gadget networking?” That is a harder query. It cuts across endpoint management, lab operations, facilities, manufacturing engineering, security testing, and vendor support.
This is also where the CPE problem becomes operationally painful. A scanner may flag every Linux kernel below a fixed version, producing noise on systems that never enable the gadget function. Or it may miss appliances because they do not advertise their kernel accurately. Both outcomes are common, and both make defenders cynical about CVE data.
The right response is narrower than a fleet-wide emergency and broader than ignoring the issue. Teams should identify devices that use USB gadget Ethernet, check whether vendor firmware includes the relevant stable fixes, and prioritize systems where unprivileged users or automation can trigger repeated gadget reconfiguration.
A link that points to a vanished parent can confuse software that assumes sysfs is coherent. Depending on timing and error handling, that can mean failed interface enumeration, repeated retries, service crashes, or inconsistent device state. The CVE’s availability impact reflects that class of failure rather than a spectacular exploit chain.
The patch’s use of
That is the quiet engineering lesson here. The kernel cannot merely make the warning go away; it must preserve ordering guarantees. Power management, sysfs topology, and lifecycle callbacks all have to agree about what still exists.
Administrators may never see the bug as “CVE-2026-31725 exploited.” They may see it as intermittent USB Ethernet disappearance, a gadget that works after reboot but not after reconfiguration, or a lab device that fails every tenth provisioning cycle. Medium-severity availability bugs often wear the mask of flakiness.
This is why the CPE question matters but should not become the only question. CPEs are useful for machine matching, but kernel security status is ultimately commit-based and vendor-build-based. If you run a distribution kernel, trust the distribution’s security advisory and changelog. If you run a vendor appliance, press the vendor for firmware status. If you build your own kernel, verify the patch is present in your tree.
For embedded teams, the action item is more direct: inspect your gadget configuration and test unbind/rebind behavior after applying the fix. A patch that changes device parentage can interact with legacy scripts that assume a fixed sysfs path. The fix is designed for compatibility, but embedded environments are where “nobody would depend on that path” becomes famous last words.
Windows-side administrators should not attempt to remediate this through Windows Update unless a Microsoft product advisory explicitly says so. The host PC is not the kernel carrying the vulnerable ECM gadget code. The remediation belongs to the Linux device, its firmware, its distribution package stream, or the product that bundles it.
That distinction is especially important in mixed teams. A vulnerability ticket generated from an MSRC link may be routed to the Windows group, but the work may belong to the appliance owner, Linux platform team, or vendor-management process. Good triage prevents the ticket from becoming a month-long game of hot potato.
That is not unusual. NVD enrichment often trails upstream nuance, and kernel CPEs are blunt instruments. They tell security tools where to start looking, not where to stop thinking.
For WindowsForum readers, the practical take is to resist both extremes. Do not panic because “Linux kernel” and “Microsoft” appear in the same vulnerability workflow. Do not ignore it because the bug is local and medium severity. Place it where it belongs: in the maintenance queue for Linux-powered USB gadget devices, especially those that use ECM networking and undergo dynamic reconfiguration.
The metadata may improve as vendors publish advisories and as NVD revises configurations. Until then, the safest interpretation is that generic CPE matching may overcount some systems and undercount products that ship patched or backported kernels under vendor-specific version strings.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Medium-Severity Bug With a Very Kernel-Shaped Blast Radius
A Medium-Severity Bug With a Very Kernel-Shaped Blast Radius
At first glance, CVE-2026-31725 is not the sort of vulnerability that sends incident responders sprinting. NVD scores it as CVSS 3.1 5.5, with local attack vector, low complexity, low privileges required, no user interaction, unchanged scope, no confidentiality or integrity impact, and high availability impact. In plain English, this is not a remote code execution bug and not an obvious privilege-escalation story.But kernel bugs rarely live only inside their CVSS boxes. This one sits in the USB gadget ECM function, the part of Linux that lets a device present itself as a USB Ethernet adapter to a host. That makes it most relevant to embedded boards, Android-derived systems, appliances, development kits, industrial devices, and lab hardware that expose USB gadget networking.
The bug is not glamorous. A
net_device is created during function-instance setup and registered during bind with the gadget device as its sysfs parent. When the gadget unbinds, the parent can be destroyed while the network device remains alive, leaving /sys/class/net/usb0 pointing at a path that no longer exists.That sounds like housekeeping until you remember that sysfs is not merely a diagnostic convenience. It is a kernel-exported object model used by system services, device managers, monitoring agents, udev rules, scripts, and power-management paths. A dangling sysfs relationship is exactly the kind of kernel state mismatch that can turn a narrow lifecycle bug into an availability problem.
The Vulnerability Is About Object Lifetime, Not USB Packets
The temptation with any USB gadget CVE is to imagine hostile USB traffic, malicious hosts, or some James Bond cable plugged into a target. CVE-2026-31725 is more mundane and, in some ways, more instructive. The failure is in lifecycle accounting.The Linux kernel’s device model depends heavily on parent-child relationships. Those relationships determine how devices appear in sysfs, how teardown ordering works, and how power management understands the hardware graph. If an object survives after its parent is gone, the kernel has not merely lost a label; it has exported a stale topology to userspace.
The fix uses
device_move() to reparent the network device between the gadget device tree and /sys/devices/virtual across bind and unbind cycles. On final unbind, calling device_move(NULL) moves the network interface into the virtual device tree before the gadget parent disappears. On rebind, it moves the device back under the new gadget.That is a subtle repair because the code must also preserve compatibility with older composite drivers. The description specifically calls out legacy drivers such as
multi.c, where a bound flag helps distinguish whether the network device is shared and pre-registered during the legacy driver’s bind phase. In other words, the patch is not just “delete the object earlier.” It is a careful attempt to keep old gadget compositions working while making sysfs truthful again.This is the kind of bug that kernel maintainers fix with a diagram in their heads. The vulnerable state is not a single bad pointer in isolation. It is a timing window between bind, unbind, parent destruction, and userspace observation of the network interface.
Why WindowsForum Readers Should Care About a Linux Gadget CVE
A Linux USB gadget flaw may sound far from the Windows desktop, but the boundary between Windows and Linux hardware has been dissolving for years. Windows developers use Linux boards over USB Ethernet. Windows administrators deploy appliances running embedded Linux. Security teams scan fleets that include Linux-based docking devices, test rigs, routers, cameras, point-of-sale gear, OT gateways, and vendor boxes nobody quite owns.USB gadget mode is especially common in devices that want a simple management channel. Plug the device into a PC and it appears as a virtual Ethernet adapter. Sometimes that interface hosts a web UI, a debugging shell, a provisioning service, or a firmware-update endpoint. The Windows machine is the host; the Linux device is pretending to be the network card.
That matters because the vulnerable component is on the device side, not the Windows host side. A Windows laptop is not “vulnerable” merely because it can connect to USB Ethernet gadgets. But a Linux gadget plugged into that laptop may carry the bug, and the operational failure may surface as a flaky network interface, broken enumeration, failed reconfiguration, or a device that needs a reboot after bind/unbind churn.
In enterprise environments, this is where vulnerability management gets uncomfortable. The CVE lands in the Linux kernel, but the asset may be recorded as a badge printer, a kiosk controller, a development board, a conferencing appliance, or a “USB device” attached to a Windows workstation. If the scanner only thinks in server distributions, it may miss the affected hardware entirely.
The CPE Metadata Looks Too Confident for the Evidence
The user-supplied NVD change record lists affected CPEs for Linux kernel 7.0 release candidates, versions from 6.13 up to but excluding 6.18.22, versions from 6.19 up to but excluding 6.19.12, and versions from 3.11 up to but excluding 6.12.81. That is the part that deserves a raised eyebrow.There are two separate issues here. The first is whether the version ranges correctly reflect every stable branch to which the fix was applied. The second is whether the CPE model is expressive enough to describe a kernel subsystem bug that matters only when a particular driver and configuration path are present.
The NVD entry itself reportedly asks, “Are we missing a CPE here?” That boilerplate appears on many NVD pages, but in this case it captures the real concern. Linux kernel CVEs often begin as upstream commits, then get backported across stable trees. The resulting affected ranges can be correct in broad outline but still misleading for distribution users because Ubuntu, Debian, Red Hat, SUSE, Android vendors, appliance builders, and cloud images do not ship “vanilla kernel 6.12.80” in the same way kernel.org labels it.
The version ranges also need timeline sanity checks. Kernel version numbering after 6.x has become more difficult to interpret when advisory data includes future-looking or release-candidate labels. A CPE that says
linux_kernel:7.0:rc1 may be meaningful in NVD’s schema, but administrators should not treat it as a substitute for vendor advisories. If a distribution says its supported kernel contains or does not contain the backport, that beats generic CPE inference.So, are we missing a CPE? Possibly. More precisely, we may be missing the right product-level mapping. The vulnerable code is in mainline Linux, but the exploitable population depends on whether a shipped kernel includes the ECM gadget function, whether it is enabled, whether USB gadget functionality is exposed, and whether the affected lifecycle path can be reached by local users or device-management workflows.
CVSS Says Local, But “Local” Is Doing a Lot of Work
NVD’s CVSS vector marks the attack vector as local and privileges required as low. That is a sensible rating if exploitation requires a user or process on the Linux device to trigger bind and unbind behavior or interact with the gadget configuration. It also avoids overstating the risk as a host-side USB attack.Still, “local” can be a slippery word on embedded systems. Many gadgets expose management interfaces, scripting hooks, debugging services, or update mechanisms that allow some level of authenticated local control. A low-privileged local account on an appliance is not always as hard to obtain as a shell on a hardened server.
The impact is availability. The description does not claim data theft, privilege escalation, or arbitrary code execution. It describes broken sysfs symlinks and a topology mismatch that the fix addresses by moving the network device to a safe parent before the gadget device is destroyed.
That makes this a patching priority for reliability-sensitive systems rather than a panic-grade emergency. If your device depends on repeatedly reconfiguring USB gadget functions, hotplugging composite modes, or keeping a virtual Ethernet management link alive through lifecycle transitions, the bug matters. If your Linux hosts never use USB gadget mode, it is probably background noise.
This distinction is where CVSS is useful but insufficient. A medium score can be urgent in a factory line if it bricks provisioning stations. A high score can be irrelevant to an environment with no exposed component. CVE-2026-31725 belongs in the former category for some embedded and lab deployments.
The Patch Tells a Larger Story About Kernel CVEs in 2026
The Linux kernel’s newer CVE process has changed the rhythm of vulnerability disclosure. More fixes are now described as vulnerabilities because the kernel project itself assigns CVEs for security-relevant bugs that land in stable trees. That has improved visibility, but it has also flooded security dashboards with kernel issues that require careful triage.CVE-2026-31725 is a textbook example. The description is technically precise but not packaged for a general IT audience. It assumes readers understand
net_device, gadget bind/unbind flows, sysfs parentage, and the difference between physical USB hosts and device-side gadget functions.That is not a criticism of the kernel maintainers. Their first job is to fix the bug. But it does mean the downstream advisory ecosystem has to do translation work: which products enable this path, which branches have the fix, which distribution kernels are affected, and which users can actually trigger the bad state.
MSRC’s appearance as a source context is also a sign of the times. Microsoft’s estate now includes Linux in WSL, Azure, Defender, CBL-Mariner/Azure Linux-derived components, container hosts, appliances, and open-source dependencies. A Linux kernel CVE can show up in Microsoft-facing vulnerability workflows even when the vulnerable component is not Windows itself.
For Windows administrators, that can be confusing. The presence of an MSRC page does not automatically mean “Windows is vulnerable.” It may mean Microsoft is tracking an upstream issue because some Microsoft product, service, container image, or dependency chain includes the affected open-source component. That nuance matters when patch tickets start landing in queues owned by Windows teams.
The Real Exposure Lives in Embedded Inventory
The most likely affected systems are not general-purpose Windows PCs or ordinary Linux servers. They are devices that can act as USB peripherals and expose Ethernet-over-USB through the ECM gadget function. That includes development boards, single-board computers, Android-adjacent devices, industrial controllers, test fixtures, and vendor hardware that uses USB as a management transport.The challenge is that those systems are often poorly represented in enterprise asset management. A server has an owner, an OS version, an update channel, and a patch window. A USB-attached appliance may have a vendor firmware version, a procurement record, and a sticky note on a lab bench.
For sysadmins, the practical question is not “Do we run Linux?” It is “Do we own devices that run Linux and expose USB gadget networking?” That is a harder query. It cuts across endpoint management, lab operations, facilities, manufacturing engineering, security testing, and vendor support.
This is also where the CPE problem becomes operationally painful. A scanner may flag every Linux kernel below a fixed version, producing noise on systems that never enable the gadget function. Or it may miss appliances because they do not advertise their kernel accurately. Both outcomes are common, and both make defenders cynical about CVE data.
The right response is narrower than a fleet-wide emergency and broader than ignoring the issue. Teams should identify devices that use USB gadget Ethernet, check whether vendor firmware includes the relevant stable fixes, and prioritize systems where unprivileged users or automation can trigger repeated gadget reconfiguration.
A Broken Symlink Can Still Break Operations
It is easy to dismiss dangling sysfs symlinks as cosmetic. They are not. In Linux, sysfs is part of the contract between the kernel and userspace. Network managers, monitoring agents, hardware inventory tools, and custom scripts routinely walk/sys/class/net to decide what exists and what to do next.A link that points to a vanished parent can confuse software that assumes sysfs is coherent. Depending on timing and error handling, that can mean failed interface enumeration, repeated retries, service crashes, or inconsistent device state. The CVE’s availability impact reflects that class of failure rather than a spectacular exploit chain.
The patch’s use of
/sys/devices/virtual is telling. When the gadget parent is not present, the network device still needs a legitimate home. Moving it into the virtual device tree keeps the object model consistent until it can be reattached under a new gadget parent.That is the quiet engineering lesson here. The kernel cannot merely make the warning go away; it must preserve ordering guarantees. Power management, sysfs topology, and lifecycle callbacks all have to agree about what still exists.
Administrators may never see the bug as “CVE-2026-31725 exploited.” They may see it as intermittent USB Ethernet disappearance, a gadget that works after reboot but not after reconfiguration, or a lab device that fails every tenth provisioning cycle. Medium-severity availability bugs often wear the mask of flakiness.
Patch Management Should Follow the Stable Tree, Not the Dashboard
The fix is referenced through multiple stable kernel commits, which implies backports across supported branches. That is normal for kernel vulnerabilities, but it complicates version-based triage. A lower version with a vendor backport may be fixed; a higher custom kernel without the patch may not be.This is why the CPE question matters but should not become the only question. CPEs are useful for machine matching, but kernel security status is ultimately commit-based and vendor-build-based. If you run a distribution kernel, trust the distribution’s security advisory and changelog. If you run a vendor appliance, press the vendor for firmware status. If you build your own kernel, verify the patch is present in your tree.
For embedded teams, the action item is more direct: inspect your gadget configuration and test unbind/rebind behavior after applying the fix. A patch that changes device parentage can interact with legacy scripts that assume a fixed sysfs path. The fix is designed for compatibility, but embedded environments are where “nobody would depend on that path” becomes famous last words.
Windows-side administrators should not attempt to remediate this through Windows Update unless a Microsoft product advisory explicitly says so. The host PC is not the kernel carrying the vulnerable ECM gadget code. The remediation belongs to the Linux device, its firmware, its distribution package stream, or the product that bundles it.
That distinction is especially important in mixed teams. A vulnerability ticket generated from an MSRC link may be routed to the Windows group, but the work may belong to the appliance owner, Linux platform team, or vendor-management process. Good triage prevents the ticket from becoming a month-long game of hot potato.
The CPE Row Is a Clue, Not the Verdict
The most concrete reading of the available data is that CVE-2026-31725 has been mapped broadly to Linux kernel versions and release candidates, but the listed CPEs should be treated as initial enrichment rather than final operational truth. The vulnerability is real, the patch is real, and the affected-systems question remains more conditional than the CPE table can express.That is not unusual. NVD enrichment often trails upstream nuance, and kernel CPEs are blunt instruments. They tell security tools where to start looking, not where to stop thinking.
For WindowsForum readers, the practical take is to resist both extremes. Do not panic because “Linux kernel” and “Microsoft” appear in the same vulnerability workflow. Do not ignore it because the bug is local and medium severity. Place it where it belongs: in the maintenance queue for Linux-powered USB gadget devices, especially those that use ECM networking and undergo dynamic reconfiguration.
The metadata may improve as vendors publish advisories and as NVD revises configurations. Until then, the safest interpretation is that generic CPE matching may overcount some systems and undercount products that ship patched or backported kernels under vendor-specific version strings.
The Signal Hidden in This Sysfs Mess
CVE-2026-31725 is small enough to triage calmly but specific enough to teach a useful lesson. It is a reminder that modern vulnerability management is no longer just about big server packages and browser zero-days. The attack surface includes object lifetimes inside kernels, USB management channels, firmware images, and devices that spend their lives plugged into Windows machines while running Linux internally.- The vulnerability affects Linux kernel USB gadget ECM behavior, not the Windows USB host stack.
- The reported impact is availability, caused by stale sysfs topology after gadget unbind operations.
- The current NVD CPE mapping should be verified against distribution, vendor, or custom-kernel patch status before it is treated as authoritative.
- Systems most worth checking are embedded or appliance-like Linux devices that expose Ethernet-over-USB through gadget mode.
- Administrators should prioritize firmware and kernel updates where gadget reconfiguration is routine or reachable by low-privileged local users.
- Security teams should route remediation to the owner of the Linux device or product image, not automatically to the Windows endpoint team.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center