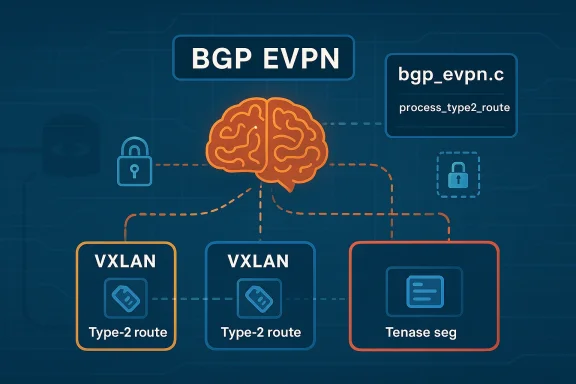
The reported CVE-2026-5107 in FRRouting’s FRR EVPN Type-2 route handling is notable because it points at a control-plane path that sits at the center of modern data-center overlays. According to the Microsoft Security Response Center entry, the issue is tied to
FRRouting, better known as FRR, is one of the most widely deployed open-source routing stacks in Linux-based network appliances, containerized routing platforms, and virtualized infrastructure. Its EVPN implementation supports the kinds of overlays that underpin modern campus, cloud, and data-center networks, especially where VXLAN and BGP EVPN are used to scale tenant separation and route distribution. FRR’s own documentation describes EVPN as the control plane for transporting Ethernet frames across bridged and routed domains, with support for both symmetric and asymmetric IRB models. (docs.frrouting.org)
The reason a defect in Type-2 route handling draws attention is that Type-2 routes carry MAC and IP reachability information, which makes them central to host mobility, ARP/ND suppression, and tenant-aware forwarding. FRR’s documentation also notes that EVPN import processing applies filtering logic for certain route types and self-originated routes, underscoring that access control and reachability policy are core to the feature. In other words, EVPN is not a passive database; it is an enforcement layer. (docs.frrouting.org)
Microsoft’s advisory naming is important because it tells us the bug is not being described in vague terms like “safety issue” or “unexpected behavior.” Instead, the vulnerable path is identified down to a source file and function, which suggests a fairly mature understanding of where the logic fails. That does not automatically mean the exploit path is public, but it does raise confidence that the issue is real and technically grounded. The fact that the advisory frames the metric around confidence and technical credibility also implies that the vendor believes the vulnerability description is specific enough to be actionable.
The timing is also worth noting. FRR continues to evolve rapidly, with recent releases showing sustained work in bgpd, EVPN, and route-processing behavior. For example, FRR 10.5.0 includes a fix stating that L3VNI should not be attached to MAC-only Type-2 routes, which reflects how subtle the Type-2 code path can be and how easily policy and route-type semantics can become intertwined. (frrouting.org)
At a practical level, the issue sits at the intersection of control-plane integrity, multi-tenant isolation, and route authorization. That is why the security community tends to treat EVPN bugs seriously even when the immediate impact is not dramatic. A route that should have been rejected, accepted, or constrained can become the seed of a much larger misconfiguration or abuse scenario.
In FRR, EVPN is built on BGP, and BGP carries the policy semantics that determine which routes are imported, maintained, or suppressed. The documentation describes how routes may remain in the global EVPN RIB while being excluded from MAC-VRF or IP-VRF import if they trip specific checks such as Site-of-Origin matching. This is a good reminder that EVPN decisions are not just about reachability; they are about who is allowed to influence whom. (docs.frrouting.org)
Why
The function name itself is revealing.
If the access-control decision in that function is incorrect, the system might apply the wrong trust model to a route. That could mean accepting a route from a peer that should have been filtered, or failing to enforce a restriction intended to keep a route local to a given tenant or VNI. Either way, the error is not cosmetic; it is foundational.
A few things make this especially important:
In vulnerability triage, specificity is a confidence multiplier. When a vendor can name the component and code path, it usually means the issue was reproduced, analyzed, and mapped to source-level behavior rather than merely suspected. That does not guarantee public exploitability, but it does suggest the underlying flaw is credible and not speculative.
At the same time, attackers benefit when a bug is tied to a protocol parser or route-import function because those are easier to reason about than memory-corruption mysteries. Even if the exact exploit steps are not public, the existence of a well-defined route-processing defect reduces the amount of guesswork needed for hostile research.
The key point is that FRR sits where control-plane policy becomes forwarding reality. If the EVPN logic accepts something it should not, the network can end up distributing incorrect host state. If it rejects something it should accept, connectivity breaks in ways that are hard to diagnose. Either outcome is expensive in production.
FRR’s own release history shows continued EVPN refinement. Recent release notes highlight EVPN-related fixes and behavior corrections, which suggests that the project is actively tightening semantics around Type-2 handling and related logic. That is typical of mature networking software: the more deployment experience it gains, the more edge cases appear. (frrouting.org)
That’s especially true in large codebases where one subsystem’s assumptions bleed into another’s. A route may be structurally valid but contextually invalid, and the security impact depends entirely on whether the code recognizes that distinction.
The impact profile is different for enterprises and service providers. An enterprise may see isolated connectivity failures or tenant leakage inside a private fabric. A carrier or cloud operator could face a wider blast radius, because one route-policy error may propagate across a more complex EVPN mesh.
For organizations, the risk is concentrated in network control planes that rely on EVPN for segmentation and scale. Those environments often assume that route policy is a trusted internal function. Once that assumption fails, the consequences may be wider than a single service outage.
The same release also includes broader BGP and EVPN maintenance, showing that the project is not treating these paths as static. That matters because a security flaw in one Type-2 code path may be adjacent to a broader class of routing semantics issues. In practical terms, administrators should not view the CVE as a one-off anomaly if they are running older FRR branches.
Such an attacker would not need to break cryptography or perform a complex memory exploit. They would only need to find the right route attributes, the right import condition, or the right topology assumption. In networking security, those are often the most practical attacks because they exploit the system’s own trust model.
The second move is to tighten your operational assumptions. Make sure EVPN peering is only enabled where it is genuinely needed, and validate that route-targets, import policies, and SoO controls are applied consistently. FRR’s documentation makes clear that import filtering and self-origin logic are part of the EVPN model, which means administrators should treat those controls as security boundaries, not optional tuning knobs. (docs.frrouting.org)
It also creates an opportunity for operators to reassess their EVPN design assumptions. Many networks grow organically, with policy exceptions layered over time. A security review prompted by a CVE is a chance to simplify those paths and reduce future exposure.
Another concern is patch lag. Infrastructure teams tend to move cautiously with routing software upgrades, especially in live EVPN fabrics, and that caution is understandable. But delays in applying a fix to the route-processing path can leave a widely trusted subsystem exposed longer than anyone intends.
There is also a broader industry lesson here. As EVPN becomes even more central to data-center design, route semantics will remain a fertile area for security bugs. The more logic we embed into the control plane, the more important it becomes to treat routing software with the same rigor traditionally reserved for operating-system privilege boundaries. That shift in mindset is overdue.
Source: MSRC Security Update Guide - Microsoft Security Response Center
bgp_evpn.c, specifically process_type2_route, and is framed as an access control problem in EVPN Type-2 processing. That combination matters: EVPN route handling is not just another parser path, but a policy-enforcement chokepoint for distributed L2/L3 segmentation. When that logic is even slightly off, the consequences can extend well beyond a single daemon crash.
 Overview
Overview
FRRouting, better known as FRR, is one of the most widely deployed open-source routing stacks in Linux-based network appliances, containerized routing platforms, and virtualized infrastructure. Its EVPN implementation supports the kinds of overlays that underpin modern campus, cloud, and data-center networks, especially where VXLAN and BGP EVPN are used to scale tenant separation and route distribution. FRR’s own documentation describes EVPN as the control plane for transporting Ethernet frames across bridged and routed domains, with support for both symmetric and asymmetric IRB models. (docs.frrouting.org)The reason a defect in Type-2 route handling draws attention is that Type-2 routes carry MAC and IP reachability information, which makes them central to host mobility, ARP/ND suppression, and tenant-aware forwarding. FRR’s documentation also notes that EVPN import processing applies filtering logic for certain route types and self-originated routes, underscoring that access control and reachability policy are core to the feature. In other words, EVPN is not a passive database; it is an enforcement layer. (docs.frrouting.org)
Microsoft’s advisory naming is important because it tells us the bug is not being described in vague terms like “safety issue” or “unexpected behavior.” Instead, the vulnerable path is identified down to a source file and function, which suggests a fairly mature understanding of where the logic fails. That does not automatically mean the exploit path is public, but it does raise confidence that the issue is real and technically grounded. The fact that the advisory frames the metric around confidence and technical credibility also implies that the vendor believes the vulnerability description is specific enough to be actionable.
The timing is also worth noting. FRR continues to evolve rapidly, with recent releases showing sustained work in bgpd, EVPN, and route-processing behavior. For example, FRR 10.5.0 includes a fix stating that L3VNI should not be attached to MAC-only Type-2 routes, which reflects how subtle the Type-2 code path can be and how easily policy and route-type semantics can become intertwined. (frrouting.org)
At a practical level, the issue sits at the intersection of control-plane integrity, multi-tenant isolation, and route authorization. That is why the security community tends to treat EVPN bugs seriously even when the immediate impact is not dramatic. A route that should have been rejected, accepted, or constrained can become the seed of a much larger misconfiguration or abuse scenario.
What EVPN Type-2 Routes Do
EVPN Type-2 routes are commonly used to advertise MAC/IP bindings for endpoints attached to an EVPN fabric. In modern VXLAN deployments, those bindings let remote VTEPs learn where a host lives without flooding the network with discovery traffic. That makes the feature essential for scaling, but it also makes the processing path sensitive to trust boundaries.In FRR, EVPN is built on BGP, and BGP carries the policy semantics that determine which routes are imported, maintained, or suppressed. The documentation describes how routes may remain in the global EVPN RIB while being excluded from MAC-VRF or IP-VRF import if they trip specific checks such as Site-of-Origin matching. This is a good reminder that EVPN decisions are not just about reachability; they are about who is allowed to influence whom. (docs.frrouting.org)
Why Type-2 Is Security-Relevant
A Type-2 route can affect forwarding, host adjacency, and tenant visibility. If access control around that route is weak, then the system may accept information that should be treated as unauthorized, stale, or self-originated. That can create route leaks, traffic steering anomalies, or in the worst case, segmentation failures.- Type-2 routes carry host identity signals.
- They influence MAC learning and neighbor resolution.
- They can interact with import policy and self-origin checks.
- They sit close to trust boundaries in EVPN fabrics.
process_type2_route is not an isolated code smell. It is a policy bug inside the routing brain of a virtualized network. In security terms, those are often the bugs that matter most because they affect the network’s decision logic, not just a peripheral helper function.Why process_type2_route Is a Sensitive Code Path
The function name itself is revealing. process_type2_route implies route classification, validation, and route-object handling before the data is admitted into the broader EVPN state machine. In a BGP daemon, that kind of function typically sits on the hot path between received protocol data and internal RIB or VRF structures.If the access-control decision in that function is incorrect, the system might apply the wrong trust model to a route. That could mean accepting a route from a peer that should have been filtered, or failing to enforce a restriction intended to keep a route local to a given tenant or VNI. Either way, the error is not cosmetic; it is foundational.
The Likely Security Failure Mode
Based on the advisory wording and FRR’s documented EVPN policy model, the defect most plausibly involves a route being evaluated against the wrong authorization condition, or a check being skipped under a particular route shape. That is an inference, not a confirmed exploit chain, but it is consistent with the file/function naming and the “access control” label. In network protocol security, subtle mismatches between route metadata and policy logic are a classic root cause.A few things make this especially important:
- EVPN control planes often rely on implicit trust relationships.
- Route-type distinctions can be deceptively subtle.
- MAC-only and MAC/IP semantics are easy to conflate.
- Import policy is only as strong as the code that enforces it.
What the Microsoft Advisory Suggests
Microsoft’s advisory entry for CVE-2026-5107 is valuable not because it explains everything, but because it identifies the vulnerability with a level of precision that usually follows real technical validation. The page ties the issue directly to FRRouting, to a specific file, and to a specific function path. That is stronger evidence than a generic “possible issue in EVPN” note.In vulnerability triage, specificity is a confidence multiplier. When a vendor can name the component and code path, it usually means the issue was reproduced, analyzed, and mapped to source-level behavior rather than merely suspected. That does not guarantee public exploitability, but it does suggest the underlying flaw is credible and not speculative.
Confidence Versus Exploitability
It is important not to overread the advisory language. A high-confidence vulnerability description does not always mean immediate exploitation in the wild. It often means the technical root cause is known with enough certainty to assign a CVE and issue guidance.At the same time, attackers benefit when a bug is tied to a protocol parser or route-import function because those are easier to reason about than memory-corruption mysteries. Even if the exact exploit steps are not public, the existence of a well-defined route-processing defect reduces the amount of guesswork needed for hostile research.
FRR’s EVPN Architecture and Why It Matters
FRR’s EVPN stack is designed to support both symmetric and asymmetric IRB, and the documentation explicitly describes its use of MAC-VRFs and BGP-EVPN control-plane behavior. This is not a niche feature used only in labs. It is a core data-center building block for operators that want vendor-neutral routing on Linux or in appliance-based fabrics. (docs.frrouting.org)The key point is that FRR sits where control-plane policy becomes forwarding reality. If the EVPN logic accepts something it should not, the network can end up distributing incorrect host state. If it rejects something it should accept, connectivity breaks in ways that are hard to diagnose. Either outcome is expensive in production.
Operational Importance
- FRR is used in production virtualization and routing environments.
- EVPN helps scale tenant networks without flooding.
- Type-2 routes are part of that core scaling model.
- A bad access-control decision can ripple across many endpoints.
Historical Context: EVPN Bugs Are Rarely Simple
This vulnerability sits in a broader historical pattern. Routing stacks tend to accumulate bugs in their most feature-rich and least frequently audited subsystems, and EVPN is a textbook example. The feature combines BGP, VXLAN, MAC learning, VRFs, route targets, and policy filters, all of which must align for the system to behave correctly.FRR’s own release history shows continued EVPN refinement. Recent release notes highlight EVPN-related fixes and behavior corrections, which suggests that the project is actively tightening semantics around Type-2 handling and related logic. That is typical of mature networking software: the more deployment experience it gains, the more edge cases appear. (frrouting.org)
Why These Bugs Persist
Protocol stacks are hard to secure because they encode both syntax and policy. A parser bug can be severe, but so can a logic bug where the parser is technically correct and the authorization decision is wrong. In EVPN, the distinction between a MAC route, a MAC/IP route, and a route that should be treated as local-only can be subtle enough to slip past ordinary testing.That’s especially true in large codebases where one subsystem’s assumptions bleed into another’s. A route may be structurally valid but contextually invalid, and the security impact depends entirely on whether the code recognizes that distinction.
Technical Impact on Operators
For operators, the immediate concern is not merely CVSS scoring or advisory language. It is whether the defect can be triggered by a peer, an adjacent fabric participant, or an internal system that is supposed to be trusted. If a route-processing flaw weakens access control, the damage can range from mis-imported routes to broader segmentation bypasses.The impact profile is different for enterprises and service providers. An enterprise may see isolated connectivity failures or tenant leakage inside a private fabric. A carrier or cloud operator could face a wider blast radius, because one route-policy error may propagate across a more complex EVPN mesh.
Possible Consequences
- Incorrect route import into a VRF or VNI.
- Host reachability appearing where it should not.
- Route suppression failing under specific conditions.
- Tenant separation becoming less reliable.
- Hard-to-debug asymmetry between control plane and data plane.
Enterprise vs. Consumer Exposure
This is primarily an enterprise and infrastructure issue, not a consumer desktop problem. FRR is used in routers, virtual switches, data-center leaf/spine nodes, network appliances, and containerized routing environments. Consumers are unlikely to interact with FRR directly, but they can absolutely be downstream victims if a provider or enterprise fabric is disrupted.For organizations, the risk is concentrated in network control planes that rely on EVPN for segmentation and scale. Those environments often assume that route policy is a trusted internal function. Once that assumption fails, the consequences may be wider than a single service outage.
Different Exposure Profiles
- Enterprises: tenant separation, campus fabrics, private cloud overlays.
- Service providers: larger EVPN meshes and higher route churn.
- Lab environments: easier to reproduce, but lower business impact.
- Consumers: mostly indirect exposure through hosted services.
What the Release Notes Reveal
FRR’s release notes provide useful background even when they do not mention the CVE directly. In 10.5.0, FRR notes a change stating that L3VNI should not be attached to MAC-only Type-2 routes, which implies active work on separating route semantics that might otherwise be conflated. That kind of change often emerges after finding logic flaws, edge cases, or policy inconsistencies in production-like testing. (frrouting.org)The same release also includes broader BGP and EVPN maintenance, showing that the project is not treating these paths as static. That matters because a security flaw in one Type-2 code path may be adjacent to a broader class of routing semantics issues. In practical terms, administrators should not view the CVE as a one-off anomaly if they are running older FRR branches.
Why Semantic Fixes Matter
When a release corrects route attachment semantics, it often signals that the internal model of what a route “means” has been sharpened. Those fixes are especially relevant in EVPN, where a route may be valid in one context and dangerous in another. The distinction between “MAC only” and “MAC/IP” is a perfect example of how a small conceptual mismatch can become a security issue.- Route semantics drive policy enforcement.
- Policy enforcement drives tenant isolation.
- Tenant isolation drives trust in the fabric.
Potential Attack Scenarios
Without confirmed exploit details, it is best to speak cautiously. Still, if the access control inprocess_type2_route is flawed, an attacker with a way to inject or influence EVPN routing information could try to get a route accepted under conditions where it should be denied. That would be the most straightforward abuse model.Such an attacker would not need to break cryptography or perform a complex memory exploit. They would only need to find the right route attributes, the right import condition, or the right topology assumption. In networking security, those are often the most practical attacks because they exploit the system’s own trust model.
Plausible Abuse Paths
- Inject a Type-2 route that slips past a policy check.
- Trigger incorrect import into a tenant VRF or VNI.
- Cause host reachability to be learned from an unauthorized peer.
- Exploit route ambiguity between MAC-only and MAC/IP semantics.
- Leverage a misclassification to influence downstream forwarding state.
Mitigation and Defensive Posture
The first defensive move is obvious: update FRR to a version that contains the fix once the vendor’s guidance identifies the remedied release. If you operate FRR in production, you should also review whether your EVPN deployments rely heavily on Type-2 routes, because that is the path implicated here. When a vulnerability lives in a specific feature family, exposure is usually uneven across the installed base.The second move is to tighten your operational assumptions. Make sure EVPN peering is only enabled where it is genuinely needed, and validate that route-targets, import policies, and SoO controls are applied consistently. FRR’s documentation makes clear that import filtering and self-origin logic are part of the EVPN model, which means administrators should treat those controls as security boundaries, not optional tuning knobs. (docs.frrouting.org)
Practical Steps for Operators
- Inventory FRR versions across all network nodes.
- Identify where EVPN Type-2 routes are in active use.
- Verify that route-target policies are intentionally scoped.
- Review SoO and import filtering behavior.
- Test failover and convergence after patching.
- Monitor for unexpected route churn or policy drift.
Strengths and Opportunities
There is a positive side to a vulnerability disclosure like this: it highlights where the ecosystem is maturing. The fact that the issue is identified down to a source file and function suggests that the defensive and review process around FRR is sufficiently active to surface deep logic problems. That is a sign of a healthy open-source security culture, even if the bug itself is unwelcome.It also creates an opportunity for operators to reassess their EVPN design assumptions. Many networks grow organically, with policy exceptions layered over time. A security review prompted by a CVE is a chance to simplify those paths and reduce future exposure.
- Clearer source-level attribution helps defenders focus review effort.
- Targeted patching is easier when the vulnerable path is known.
- EVPN policy audits can uncover related misconfigurations.
- Route filtering hygiene often improves overall fabric resilience.
- Version modernization reduces exposure to adjacent defects.
- Documentation review helps align intent with actual behavior.
- Testing discipline gets stronger when teams revisit route semantics.
Risks and Concerns
The biggest concern is that access-control bugs are often underestimated because they do not always announce themselves as dramatic crashes. A control-plane logic error can quietly distort forwarding decisions or route visibility long before anyone notices. That makes detection harder and the operational consequences more insidious.Another concern is patch lag. Infrastructure teams tend to move cautiously with routing software upgrades, especially in live EVPN fabrics, and that caution is understandable. But delays in applying a fix to the route-processing path can leave a widely trusted subsystem exposed longer than anyone intends.
- Silent policy failure can be harder to detect than a crash.
- Patch latency can keep exposure open for weeks or months.
- Complex topologies make reproduction and validation difficult.
- Multi-vendor fabrics may amplify troubleshooting complexity.
- Misread advisories can cause teams to underestimate scope.
- Adjacent logic bugs may remain hidden in nearby code paths.
- Operational fatigue can slow response to “non-sexy” routing CVEs.
Looking Ahead
What happens next will depend on whether the security community receives more detail about the exact access-control failure and whether FRR publishes a corresponding fix advisory or release note. If a patch is already available, the story quickly shifts from disclosure to remediation. If not, administrators will need to rely more heavily on topology hardening and cautious peering restrictions until vendor guidance clarifies the affected versions.There is also a broader industry lesson here. As EVPN becomes even more central to data-center design, route semantics will remain a fertile area for security bugs. The more logic we embed into the control plane, the more important it becomes to treat routing software with the same rigor traditionally reserved for operating-system privilege boundaries. That shift in mindset is overdue.
- Watch for FRR release notes that mention the CVE explicitly.
- Compare your deployment against affected EVPN Type-2 usage patterns.
- Review whether untrusted peers can influence EVPN route injection.
- Validate that upgrade testing includes control-plane policy checks.
- Monitor logs for unusual route import or suppression behavior.
process_type2_route, the difference between a valid route and an authorized route is everything.Source: MSRC Security Update Guide - Microsoft Security Response Center