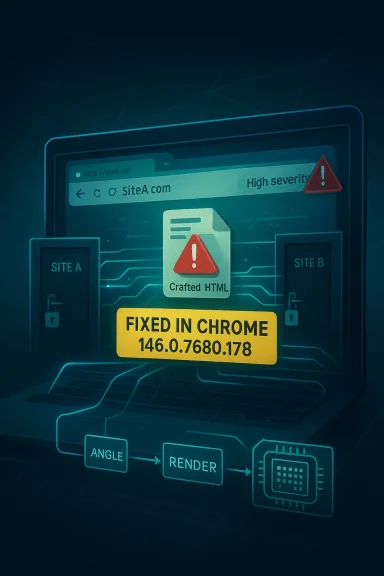
In Google Chrome’s latest security cycle, CVE-2026-5283 stands out less because of its exploit mechanics than because of what it says about the browser’s attack surface in 2026: a crafted HTML page can still be enough to pry loose cross-origin data from a widely deployed Chromium stack. Google’s fix lands in Chrome 146.0.7680.178, and the vulnerability is classified by Chromium as High severity, with Microsoft’s update guide surfacing it for enterprise defenders who track Chromium-linked risk across Edge and other downstream products. The broader message is familiar but still uncomfortable: even as browser vendors harden rendering pipelines, the combination of graphics acceleration, complex policy boundaries, and web content parsing continues to produce security bugs with meaningful confidentiality impact.
Chrome’s March 2026 release train was already busy before CVE-2026-5283 arrived. Google had pushed Chrome 146 to Stable on March 10, then followed with a March 13 update and additional maintenance releases as the branch matured, a pattern that reflects how quickly Chromium now moves through stabilization and security hardening. By the time CVE-2026-5283 appeared in the public record on April 1, 2026, the Stable channel was already carrying several rounds of fixes, which is typical of modern browser security where the first patched build is rarely the last stop.
The vulnerability is described as an inappropriate implementation in ANGLE, Chromium’s graphics abstraction layer. That phrasing matters, because ANGLE sits at the junction between web content and the operating system’s native graphics APIs, translating OpenGL ES calls into back-end implementations such as DirectX, OpenGL, Vulkan, or Metal depending on platform. When an issue in that layer leaks data across origins, it suggests that the bug is not just a conventional memory safety flaw but a failure in how the browser enforces the separation between different web security contexts.
The practical risk is straightforward: a remote attacker could lure a user to a malicious page and extract cross-origin data. The public description does not indicate arbitrary code execution, but it does indicate confidentiality compromise, which can still be severe in a browser environment where tokens, page state, embedded content, or sensitive rendering artifacts may be exposed in unexpected ways. In enterprise settings, that kind of issue can be especially troublesome because browser data leaks often become the first step in a larger compromise chain.
What makes this advisory worth attention is that it lands in a year when Chromium security has already been under pressure from multiple high-profile fixes. Chrome’s release notes in March 2026 repeatedly highlight high-severity issues, and Google has also warned about exploits in the wild for other vulnerabilities in the same release stream. Against that backdrop, CVE-2026-5283 looks less like an isolated bug and more like part of a recurring pattern: web browsers remain one of the most aggressively targeted pieces of software in the enterprise and consumer stack. (chromereleases.googleblog.com)
ANGLE has been a recurring security focal point because it is both widely used and deeply embedded. Its job is not just to draw pixels efficiently; it is to bridge a portability gap between web APIs and native graphics stacks. That makes it a natural place for bugs involving shader handling, rendering state, or cross-process data flows. Chrome has previously shipped fixes for ANGLE-related issues, including high-severity bugs that highlight how graphics code can be abused even when the browser’s higher-level policy machinery appears intact.
The wording of this specific CVE is notable for its emphasis on cross-origin data leakage rather than corruption or crash behavior. That suggests the flaw likely sits in a path where the browser or graphics layer exposes information that should have remained isolated by origin boundaries. In browser security, confidentiality bugs are often underappreciated by consumers because they do not always produce visible symptoms, yet they can expose authentication state, page content, or internal rendering artifacts in ways that are highly useful to attackers.
The public record does not provide exploit primitives, and that is important. We should not assume this is a simple memory corruption bug, nor should we assume the attacker’s path is universal across all devices. What we can say is that the vulnerability is severe enough to be classified as High, and that the impact is described in terms of information disclosure rather than direct code execution. In security terms, that still warrants rapid patching because leaks often reveal enough state to defeat subsequent defenses.
The phrase crafted HTML page also signals that exploit delivery is likely simple. Attackers do not need a bespoke binary or local access; they need only convince a user to visit a malicious site, click a compromised link, or load hostile content through normal browsing behavior. That keeps the attack model aligned with other browser vulnerabilities that have historically been effective in phishing and watering-hole campaigns.
Google’s Chrome release process typically stages fixes through Stable updates, and security notes may deliberately withhold details until the majority of users are protected. That is consistent with the company’s own policy language in its release notes, which says bug details and links may be restricted until most users are updated. The practice reflects a tradeoff: disclose enough for defenders to act, but not so much that attackers get a head start. (chromereleases.googleblog.com)
Managed environments also face a timing problem. Chrome and Edge updates may be approved, staged, or delayed by endpoint management workflows, and browser sessions can remain active long after a patch is available. That creates a dangerous lag between the public availability of a fix and the actual reduction of exposure on user machines. The more heavily a company depends on browser-based SaaS, the more painful that lag becomes.
The good news is that consumer remediation is usually simple: update Chrome or allow the browser to auto-update to a fixed build. The harder part is the ecosystem around Chrome, especially on Windows systems where Edge, enterprise wrappers, and other Chromium-based tools may remain in use even after the main browser is patched. Consumers who use multiple Chromium browsers should not assume one update automatically protects all of them. (msrc.microsoft.com)
For Microsoft, the inclusion of the CVE in the Security Update Guide is a reminder that Edge’s value proposition depends partly on how quickly it can track Chromium fixes. Enterprises may see the browser as a managed platform choice, but beneath that branding is the same upstream engine. The market implication is subtle but real: differentiation in browser security increasingly comes from response speed, policy controls, and enterprise manageability rather than from the core rendering engine alone. (msrc.microsoft.com)
Earlier Chrome releases in 2026 also showed that ANGLE remains a recurring target. Google’s March 3 stable update included a high-severity integer overflow in ANGLE, demonstrating that the graphics layer continues to attract both bug finders and attackers. CVE-2026-5283 therefore fits a larger pattern rather than arriving as a one-off anomaly.
Second, organizations should examine whether they have exposed browser-based workflows to untrusted content in the same session as sensitive apps. The exploit description centers on a crafted HTML page, which means phishing and link handling controls matter as much as endpoint patching. Security teams should treat this as a browser-layer issue with user-behavior implications, not as a purely technical defect.
Another question is how quickly enterprises absorb the fix across browser fleets. In a world where Chrome, Edge, WebView-based apps, and embedded browsers all coexist, a single upstream patch does not guarantee uniform protection. The organizations that fare best will be those with disciplined update telemetry and aggressive endpoint compliance checks. (msrc.microsoft.com)
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Chrome’s March 2026 release train was already busy before CVE-2026-5283 arrived. Google had pushed Chrome 146 to Stable on March 10, then followed with a March 13 update and additional maintenance releases as the branch matured, a pattern that reflects how quickly Chromium now moves through stabilization and security hardening. By the time CVE-2026-5283 appeared in the public record on April 1, 2026, the Stable channel was already carrying several rounds of fixes, which is typical of modern browser security where the first patched build is rarely the last stop.The vulnerability is described as an inappropriate implementation in ANGLE, Chromium’s graphics abstraction layer. That phrasing matters, because ANGLE sits at the junction between web content and the operating system’s native graphics APIs, translating OpenGL ES calls into back-end implementations such as DirectX, OpenGL, Vulkan, or Metal depending on platform. When an issue in that layer leaks data across origins, it suggests that the bug is not just a conventional memory safety flaw but a failure in how the browser enforces the separation between different web security contexts.
The practical risk is straightforward: a remote attacker could lure a user to a malicious page and extract cross-origin data. The public description does not indicate arbitrary code execution, but it does indicate confidentiality compromise, which can still be severe in a browser environment where tokens, page state, embedded content, or sensitive rendering artifacts may be exposed in unexpected ways. In enterprise settings, that kind of issue can be especially troublesome because browser data leaks often become the first step in a larger compromise chain.
What makes this advisory worth attention is that it lands in a year when Chromium security has already been under pressure from multiple high-profile fixes. Chrome’s release notes in March 2026 repeatedly highlight high-severity issues, and Google has also warned about exploits in the wild for other vulnerabilities in the same release stream. Against that backdrop, CVE-2026-5283 looks less like an isolated bug and more like part of a recurring pattern: web browsers remain one of the most aggressively targeted pieces of software in the enterprise and consumer stack. (chromereleases.googleblog.com)
Background
Chromium’s security model depends on a very sharp boundary between origins. In theory, one site should not be able to read another site’s data unless explicit browser policy or server configuration permits it. In practice, that boundary is enforced by a long chain of components: network code, renderer logic, process isolation, sandboxing, frame policies, and, increasingly, GPU-accelerated rendering paths. When one of those pieces misimplements an origin check or mishandles a data flow, the browser’s most fundamental protection starts to fray.ANGLE has been a recurring security focal point because it is both widely used and deeply embedded. Its job is not just to draw pixels efficiently; it is to bridge a portability gap between web APIs and native graphics stacks. That makes it a natural place for bugs involving shader handling, rendering state, or cross-process data flows. Chrome has previously shipped fixes for ANGLE-related issues, including high-severity bugs that highlight how graphics code can be abused even when the browser’s higher-level policy machinery appears intact.
The wording of this specific CVE is notable for its emphasis on cross-origin data leakage rather than corruption or crash behavior. That suggests the flaw likely sits in a path where the browser or graphics layer exposes information that should have remained isolated by origin boundaries. In browser security, confidentiality bugs are often underappreciated by consumers because they do not always produce visible symptoms, yet they can expose authentication state, page content, or internal rendering artifacts in ways that are highly useful to attackers.
Why Chrome’s release cadence matters
Chrome’s stable channel now behaves like a high-frequency security distribution system rather than a traditional quarterly software release. Google’s March 2026 notes show multiple Stable updates within days, and that cadence is part of the defense strategy: shrink the window between patch publication and wide deployment. The downside is that users and administrators must keep up with a more fluid, less forgiving patch rhythm.Why Microsoft is listing it too
Microsoft’s Security Update Guide includes CVE-2026-5283 because Chromium bugs frequently affect Microsoft Edge and other products built atop the Chromium engine. Even when the core fix originates in Google Chrome, downstream vendors must integrate the remediation into their own release trains. That makes coordinated disclosure and patch propagation essential for enterprise environments that standardize on Edge but still inherit Chromium risk. (msrc.microsoft.com)Technical Significance
At a technical level, an ANGLE implementation flaw is interesting because it sits in a layer where browser logic, GPU behavior, and platform abstractions collide. That makes root-cause analysis harder than in a pure JavaScript or DOM bug. It also means the exploitability surface can vary by operating system, driver stack, and rendering path, which complicates both testing and mitigation.The public record does not provide exploit primitives, and that is important. We should not assume this is a simple memory corruption bug, nor should we assume the attacker’s path is universal across all devices. What we can say is that the vulnerability is severe enough to be classified as High, and that the impact is described in terms of information disclosure rather than direct code execution. In security terms, that still warrants rapid patching because leaks often reveal enough state to defeat subsequent defenses.
Cross-origin data leaks are not “just privacy bugs”
A browser-origin leak can be much more than an abstract privacy issue. If a malicious page can read data from another origin, it may expose authentication tokens, embedded application state, internal dashboards, or sensitive content rendered in an iframe or canvas-like path. In enterprise web apps, those leaks can be enough to pivot from an untrusted tab into a business-critical workflow.The phrase crafted HTML page also signals that exploit delivery is likely simple. Attackers do not need a bespoke binary or local access; they need only convince a user to visit a malicious site, click a compromised link, or load hostile content through normal browsing behavior. That keeps the attack model aligned with other browser vulnerabilities that have historically been effective in phishing and watering-hole campaigns.
Patch Positioning
The fixed version is explicit: Chrome prior to 146.0.7680.178 is vulnerable. That means organizations running Stable builds earlier than that branch point should treat the issue as unresolved until they have verified deployment of the patched version or an equivalent downstream release from a vendor such as Microsoft. The version floor matters because it turns a vague advisory into a concrete compliance checkpoint.Google’s Chrome release process typically stages fixes through Stable updates, and security notes may deliberately withhold details until the majority of users are protected. That is consistent with the company’s own policy language in its release notes, which says bug details and links may be restricted until most users are updated. The practice reflects a tradeoff: disclose enough for defenders to act, but not so much that attackers get a head start. (chromereleases.googleblog.com)
What defenders should verify
Administrators should check more than the browser version string. They should also confirm whether managed Edge channels, embedded Chromium apps, or third-party browsers have inherited the same Chromium branch and whether update policies allow automatic rollout. In many enterprises, a “Chrome fix” is not really finished until every Chromium derivative in the fleet has been reconciled. (msrc.microsoft.com)Enterprise Impact
For enterprises, CVE-2026-5283 is primarily a confidentiality risk, but that label can understate its operational impact. Data leaks in the browser often become credential theft, session hijacking, or exposure of business logic that can be chained into larger attacks. In other words, a leak today can become a foothold tomorrow.Managed environments also face a timing problem. Chrome and Edge updates may be approved, staged, or delayed by endpoint management workflows, and browser sessions can remain active long after a patch is available. That creates a dangerous lag between the public availability of a fix and the actual reduction of exposure on user machines. The more heavily a company depends on browser-based SaaS, the more painful that lag becomes.
The risk profile for regulated sectors
Financial services, healthcare, government, and legal organizations should care disproportionately about this kind of browser flaw. Those sectors routinely keep highly sensitive information in web apps, and even a limited cross-origin leak can trigger compliance and incident-response obligations. A browser issue does not need to reach the kernel to become a reportable security event.Consumer Impact
Consumers are less likely to notice the vulnerability directly because it does not read like a classic pop-up scam or visible browser crash. That can create a false sense of safety. The threat model is the same one that has made browser zero-days so valuable for years: a user visits a page, the page triggers hidden browser behavior, and data is exposed without a dramatic on-screen warning.The good news is that consumer remediation is usually simple: update Chrome or allow the browser to auto-update to a fixed build. The harder part is the ecosystem around Chrome, especially on Windows systems where Edge, enterprise wrappers, and other Chromium-based tools may remain in use even after the main browser is patched. Consumers who use multiple Chromium browsers should not assume one update automatically protects all of them. (msrc.microsoft.com)
Why this matters beyond browsers
Chromium is not just “Chrome.” It is the engine behind a wide range of desktop applications, webviews, and productivity tools. That means a rendering-layer bug can travel farther than many users realize, especially on Windows where browser technology is commonly reused inside apps. The practical effect is that a single Chromium flaw can surface as a security issue in multiple products at once.Competitive and Market Implications
This CVE also reinforces a broader market truth: the browser wars are now security wars. Chrome’s massive install base makes every flaw consequential, but Chromium’s ubiquity also means downstream products absorb the same risk whether they want it or not. That gives Google a de facto responsibility for the security posture of a much larger ecosystem than just Chrome itself. (chromereleases.googleblog.com)For Microsoft, the inclusion of the CVE in the Security Update Guide is a reminder that Edge’s value proposition depends partly on how quickly it can track Chromium fixes. Enterprises may see the browser as a managed platform choice, but beneath that branding is the same upstream engine. The market implication is subtle but real: differentiation in browser security increasingly comes from response speed, policy controls, and enterprise manageability rather than from the core rendering engine alone. (msrc.microsoft.com)
The pressure on alternative browsers
Competing browsers built on Chromium inherit both the upside and the burden of Google’s security cadence. They get the fixes, but they also inherit the patch dependency chain. Browsers that rely on their own engines can market independence, yet they must prove they can deliver equivalent speed and rigor when their own bugs emerge. (chromereleases.googleblog.com)Context from Recent Chrome Security
The timing of CVE-2026-5283 should be read in the context of a particularly active Chrome security quarter. In March 2026 alone, Google’s release notes highlighted several major fixes, including one update where the company explicitly said it was aware of exploits in the wild for CVE-2026-3909. That reinforces the reality that browser exploit chains are not theoretical exercises; they are active operational tools. (chromereleases.googleblog.com)Earlier Chrome releases in 2026 also showed that ANGLE remains a recurring target. Google’s March 3 stable update included a high-severity integer overflow in ANGLE, demonstrating that the graphics layer continues to attract both bug finders and attackers. CVE-2026-5283 therefore fits a larger pattern rather than arriving as a one-off anomaly.
What the pattern suggests
The recurring presence of ANGLE bugs suggests a deeper engineering challenge: graphics abstraction layers are inherently complex, high-performance, and cross-platform. Those are all characteristics that make software more difficult to verify exhaustively. It is likely that security researchers will continue probing this area because the payoff remains high and the attack surface remains broad.Detection and Response
The first response step is obvious but still critical: confirm that Chrome has been updated to 146.0.7680.178 or later, or that the equivalent downstream Chromium-based product has shipped the fix. In managed environments, administrators should also review update success metrics rather than assuming policy compliance guarantees installation. Version compliance on paper is not always the same as patched reality on endpoints.Second, organizations should examine whether they have exposed browser-based workflows to untrusted content in the same session as sensitive apps. The exploit description centers on a crafted HTML page, which means phishing and link handling controls matter as much as endpoint patching. Security teams should treat this as a browser-layer issue with user-behavior implications, not as a purely technical defect.
A practical response order
- Update Chrome and Chromium-based browsers to the fixed version or vendor equivalent.
- Verify managed deployment across desktop fleets, VDI sessions, and remote workers.
- Audit browser policy for risky combinations of sensitive apps and untrusted browsing.
- Review incident telemetry for unusual browser data access or suspicious page loads.
- Communicate the risk to users with clear guidance on malicious links and unexpected HTML content.
Strengths and Opportunities
The upside of this episode is that the Chromium ecosystem has become unusually transparent about high-severity security problems, and that transparency helps defenders move quickly. Google’s public versioning, Microsoft’s downstream tracking, and the industry’s reliance on shared vulnerability identifiers create a patchable ecosystem even when the initial bug is serious. The challenge is execution, not visibility.- The fixed build is clearly identified as 146.0.7680.178 or later.
- The vulnerability is disclosed with enough specificity for defenders to triage it.
- Chromium’s release cadence allows rapid remediation across Stable channels. (chromereleases.googleblog.com)
- Microsoft surfaces the issue for enterprise customers who track Edge and Chromium-linked exposure. (msrc.microsoft.com)
- The public description makes it easier to align phishing defenses with browser patching.
- The recurring attention on ANGLE should improve long-term scrutiny of graphics code paths.
Risks and Concerns
The main concern is that cross-origin data leakage can be deceptively powerful. Attackers do not need a flashy crash or immediate code execution if they can quietly extract useful information from a victim’s browsing session. In modern incidents, that kind of low-noise access is often more valuable than a loud exploit.- Cross-origin exposure can reveal sensitive business or identity data.
- Users may not notice anything unusual when the bug is triggered.
- Delayed browser updates leave a wide real-world exposure window. (chromereleases.googleblog.com)
- Chromium derivatives can inherit the same risk even if Chrome is patched first.
- Graphics-layer bugs are difficult to test exhaustively across devices and drivers.
- Attackers can likely deliver the exploit through ordinary web traffic and phishing.
- Enterprises may underestimate the issue because it is framed as a leak rather than an RCE.
Looking Ahead
The next question is not whether Chromium will fix this class of issue, but how often related bugs will keep appearing in graphics and rendering subsystems. ANGLE has already featured in multiple Chrome security advisories, and that history suggests continued scrutiny will be necessary. The browser security community will likely keep treating GPU-adjacent code as high-value territory for bug discovery.Another question is how quickly enterprises absorb the fix across browser fleets. In a world where Chrome, Edge, WebView-based apps, and embedded browsers all coexist, a single upstream patch does not guarantee uniform protection. The organizations that fare best will be those with disciplined update telemetry and aggressive endpoint compliance checks. (msrc.microsoft.com)
- Confirm that Chrome is at 146.0.7680.178 or newer.
- Verify the same fix in Microsoft Edge and other Chromium-based software.
- Watch for follow-up Chrome releases that may refine the fix or address related issues. (chromereleases.googleblog.com)
- Review browser isolation and phishing controls as part of the response.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center