 Background
Background
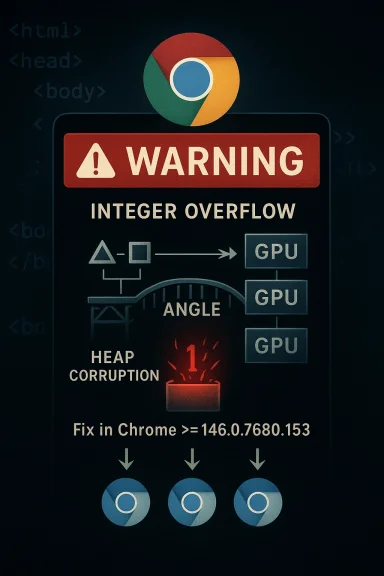
Microsoft’s March 2026 security guidance for CVE-2026-4452 lands in a familiar place for anyone who tracks Chromium: the browser engine’s graphics stack remains one of the highest-value targets in modern client software. The issue is described as an integer overflow in ANGLE, the graphics translation layer used by Chromium-based browsers, and it affects Google Chrome on Windows prior to 146.0.7680.153. In practical terms, a remote attacker could use a crafted HTML page to trigger heap corruption, which is exactly the kind of browser flaw that security teams treat with urgency. s not just because the CVE is marked High, but because it sits in a category that keeps recurring across browser release trains: memory-safety bugs in rendering and graphics subsystems. Google’s Chrome release cadence shows that March 2026 was already a heavy security month, with multiple stable-channel updates and multiple serious bugs shipping in quick succession. Chrome’s March 12 stable update, for example, explicitly called out active exploitation of two other vulnerabilities, underscoring how quickly browser security can shift from routine patching to emergency response.For Windows users, the key question is not whether the vulnerability exists in Chromium — it does — but whether their installed browser has already moved beyond the affected build. Microsoft’s Security Update Guide entry makes the remediation threshold explicit: the vulnerable Chrome versions are those earlier than 146.0.7680.153, and Microsoft also maps the issue to Windows as the affected platform in its advisory metadata. That makes this a classic downstream tracking story: the fix originates upstream in Chromium, then arriverity ecosystem as browsers and embedded web components ingest it.
The broader implication is that ANGLE remains a high-risk attack surface. Because it sits between web content and the GPU stack, flaws there can turn ordinary page rendering into memory corruption with potentially serious exploitation paths. That is why this CVE belongs in the same mental bucket as prior ANGLE bugs, including earlier heap corruption and use-after-free issues in Chrome’s graphics path.
Overview
ANGLE, short for Almost Native Graphics Layer Engine, translates graphics APIs such as OpenGL ES into backend-specific calls that can run on Windows, macOS, Linux, and other platforms. In Chromium, that translation layer is important because it lets web apps and browser features rely on hardware acceleration without writing separate code for every driver stack. The trade-off is straightforward: anything that parses attacker-influenced rendering data and then talks to a complex graphics pipeline becomes a prime candidate for memory corruption.The security history of ANGLE is instructive. Chrome has repeatedly patched memory-safety flaws in that component, and the recurring pattern is not accidental. Graphics code is highly optimized, typically written in C and C++, and frequently operates on buffers whose sizes are derived from attacker-controlled input or from complex internal state. An integer overflow in that environment is especially dangerous because it can convert a large or malformed calculation into a smaller allocation, setting the stage for heap overwrite or other corruption.
That is why the wording in the CVE matters. “Potentially exploit heap corruption via a crafted HTML page” signals remote, web-delivered attack potential rather than a local-only crash. The user interaction requirement also matters: the browser must render ut that is a low bar in a phishing or drive-by scenario. In other words, this is not merely a crash bug; it is a bug class with real exploitation history across browser ecosystems.
Microsoft’s own documentation strategy reinforces the same point. Since 2024, MSRC has emphasized publishing CWEs and other structured vulnerability data in the Security Update Guide to improve transparency and accelerate remediation. That means the entry for CVE-2026-4452 is not just a label; it is part of a downstream patch-tracking system that enterprise admins, security platforms, and vulnerability scanners can consume.
What CVE-2026-4452 Actually Is
At the technical level, CVE-2026-4452 is an integer overflow in ANGLE that can be triggered by a specially crafted HTML page in Chrome on Windows prior to 146.0.7680.153. The NVD enrichment notes map t Integer Overflow or Wraparound and also list CWE-472 External Control of Assumed-Immutable Web Parameter** as part of the weakness profile. That combination is a useful reminder that browser vulnerabilities often emerge from more than one flawed assumption at once.The exploit narrative is important. A malicious page delivered over the web can push the browser into a bad calculation, which in turn can corrupt the heap. Because the trigger is HTML contee is broad: it does not require a plugin, a local binary, or unusual privileges. A browser flaw with that profile is one of the most practical classes for attackers because it maps cleanly onto phishing, malvertising, and compromised site scenarios.
Why integer overflows are still dangerous
An integer overflow is not just a math error. In security-sensitive code, it can become a control-flow primitive if it causes the program to allocate too little memory or to miscompute bounds before writing data. Once the program writes past the intended buffer, the attacker can sometimes steer execution toward code-reuse or other corruption techniques, depending on the surrounding mitigations. That is why a “simple overflow” often turns into a serious browser bug.The CVSS posture also supports serious treatment. CISA-ADP’s ve CVSS 3.1 8.8 High, with network attack vector, low attack complexity, no privileges required, and user interaction required. That profile is consistent with a remote browser exploit that depends on a user loading hostile content, yet still yields high impact if successful.
Why heap corruption changes the stakes
Heap corruption is the red flag because it is often the step between a crash and code execution. Not every heap corruption bug is exploitable, but attackers prize them because they can sometimes be shaped into reliable exploitation chains on a specific browser build and OS combination. In a browser context, that can mean sandbox escape staging, renderer compromise, or credential theft if follow-on bugs are available.The Windows-specific wording in Microsoft’s advisory should also be read carefully. Chrome on Windows is the cited affecteests the advisory is focused on the Windows build channel rather than all Chromium implementations equally. That said, the underlying Chromium component still deserves attention elsewhere because Edge, WebView-based applications, and other Chromium consumers may inherit similar fixes on their own schedule.
Why ANGLE Keeps Appearing in Browser CVEs
ANGLE is valuable precisely because it is complicated. It sits at the intersection of browser rendering, graphics acceleration, and platform abstraction, and that means it handles diverse inputs at high speed. Every extra translation step increases the chance that one malformed structure or unexpected edge case will lead to a bad calculation, an invalid buffer size, or an out-of-bounds write.The repeated appearance of ANGLE in browser advisories shows a broader truth about modern web security: the most exposed code is often the most layered code. A browser has to accept untrusted content, render it, isolate it, and do so across wildly different GPU drivers and operating systems. That complexity creates fertile ground for integer arithmetic mistakes, especially where the code must reconcile page-supplied data with platform-specific graphics constraints.
Historical pattern in Chrome security
Google has patched ANGLE-related bugs before, including a use-after-free in early 2026 and older heap corruption issues in prior release cycles. That is not a sign that the engineering team is negligent; it is a sign that graphics code is relentlessly adversarial territory where fuzzing, sanitizers, and code review still leave a long tail of edge cases. The Chrome release notes repeatedly show that security fixes in graphics and rendering are a regular part of the stable-channel maintenance load.The market implication is that browser vendors compete not only on features but on how quickly they can absorb and harden upstream graphics fixes. Chrome, Edge, and other Chromium-based browsers all live downstream of the same code base, so one ANGLE defect can become a synchronization problem across multiple products. When one vendor ships faster than another, the lag becomes a measurable security exposure window.
Why admins should care even if “browser RCE” sounds routine
A browser exploit is not routine when the attacker can turn it into a foothold inside a managed workstation. Enterprise environments often assume that the browser is the least-trusted app on the endpoint, but it is also the one application that almost everyone uses constantly. That makes browser patch latency especially consequential, because an unpatched client can become the first stage in a larger intrusion chain.- Attackers value browser bugs because they are reachable from a simple link.
- ANGLE bugs are especially dangerous because they sit near memory-management boundaries.
- A stable-channel fix is only useful once the fleet actually receives it.
- Enterprises with delayed update rings should treat browser CVEs as priority one.
- Consumer users benefit from automatic updates, but only if the browser restarts promptly.
- GPU and graphics bugs often require deeper testing, which can slow remediation in controlled environments.
Microsoft’s Security Update Guide Role
Microsoft’s entry for CVE-2026-4452 is a good example of how the Security Update Guide has evolved into a downstream signal for Chromium fixes. Microsoft has spent the last several years making the SUG more transparent and more machine-readable, including support for CWE data and CSAF files. That matters because vulnerability management tools increasingly ingest these records automatically rather than relying solely on manual analyst review.In practical terms, the SUG entry tells Windows administrators two things at once: the issue exists upstream in Chromium, and Microsoft considers the advisory relevant for tracking in thehat does not necessarily mean Microsoft independently authored the flaw; it usually means the downstream product, such as Edge or a Chromium-based component, needs to reflect the upstream fix status for Windows customers.
What the SUG data tells us
The advisory metadata in the uploaded material shows the CVE was received from Chrome on March 19, 2026 and then enriched by NVD and CISA-ADP on March 20, 2026. That sequence is useful because it illustrates the normal vulnerability pipeline: vendor disclosure, public indexing, and then score enrichment and taxonomy mapping. It is a reminder that early-advisory data often evolves in the first 24 to 48 hours.It also explains why the precise score may shift over time. NVD may initially leave a base score unset while another source publishes a provisional vector, and later updates can refine the classification. For security teams, the lesson is to treat the first public advisory as actionable but not necessarily final.
Why Windows relevance is emphasized
Microsoft’s ecosystem is especially sensitive to Chromium changes because Edge is Chromium-based and because many Windows applications embed web-rendering components that ride on the same upstream code base. Even when a bug is discovered and fixed in Chrome, the true operational question for Windows administrators is when the patched Chromium bits land in the downstream software they actually deploy. That is why Microsoft’s security guide has become a key reference point for enterprise patch governance.- The SUG acts as a bridge between upstream Chromium and downstream Microsoft products.
- Mories help SIEM, EDR, and asset tools keep pace.
- Enrichment data may lag by hours or days, so timing matters.
- The advisory is useful even when remediation is already available in Chrome.
- Windows admins should align browser patching with endpoint maintenance windows.
The Exploitation Model
The most important practical detail in this CVE is the delivery mechanism: a crafted HTML page. That means an attacker does not need to persuade the victim to install software or run a binary. Instead, the browser itself becomes the execution environment for the exploit chain, which is why browser vulnerabilities remain among the most operationally flexible tools in an attacker’s kit.The user-interaction requirement does slightly reduce the automation potential, but not by much. Phishing links, compromised websites, ad networks, and malvertising all provide realistic trigger paths. In the real world, “user interaction required” often means “click a link once,” which is why defenders should not interpret it as a meaningful safety margin. It is a risk reducer, not a risk eliminator.
Attack chain possibilities
A successful browser-memory exploit usually does not stop at heap corruption. Attackers may use it to crash the renderer, defeat a sandbox boundary, or combine it with a second bug for code execution. The exact chain depends on patch level, mitigations, and whether the attacker is chasing mass exploitation or a more targeted intrusion.Because ANGLE is tied to GPU-related rendering paths, exploit reliability can be affected by driver version and platform configuration. That is both good and bad for defenders: it can complicate broad weaponization, but it can also make exploitation unpredictable in a way that leaves security teams with more forensic ambiguity after the fact.
Why “heap corruption” alarms incident responders
Incident responders tend to classify heap corruption bugs as high-priority even before exploitability is fully confirmed. The reason is simple: by the time the browser crashes, an attacker may already have learned enough about memory layout, allocator behavior, or mitigation bypass opportunities to move toward a working exploit. In a web browser, that can convert a single malicious page into a repeatable intrusion vector.- Drive-by web delivery is the core danger.
- Malicious HTML is easier to weaponize than many people assume.
- GPU and graphics bugs often sit close to high-value memory targets.
- A crash may be the visible symptom of deeper exploit development.
- Patch adoption speed matters as much as patch availability.
Enterprise Impact vs Consumer Impact
For consumers, the guidance is straightforward: update Chrome immediately and restart the browser so the fixed build is actually loaded. Automatic updates reduce friction, but they do not help if the browser sits open for days or if the user delays restart prompts. In the consumer world, patch latency is often driven by convenience, which is precisely why browser vendors emphasize silent background updates.For enterprises, the issue is more complicated because patch velocity is constrained by change-control policy, testing, and software-deployment rings. A graphics or rendering fix can raise compatibility concerns, especially where line-of-business apps, virtual desktop environments, or GPU remoting systems depend on stable browser behavior. That is why browser CVEs often expose an uncomfortable tension between operational stability and security urgency.
Enterprise considerations
Administrators should assume that fleets containing Chrome or Chromium-embedded software are in the blast radius until the fixed version is confirmed. Endpoint inventories often undercount embedded browsers, so teams need to look beyond the primary browser binary and into packaged apps, Electron-style wrappers, and enterprise portals that might embed the same engine. That broader inventory is often where exposure hides.Microsoft’s structured advisory model helps here because it provides a central place to correlate vulnerability IDs with affected products and remediation status. Security teams can feed the CVE into remediation dashboards, verify whether downstream packages have absorbed the fix, and enforce patch compliance through endpoint management tooling.
Consumer considerations
Consumers generally benefit from Chrome’s fast update cadence, but browser security still depends on human behavior. If a user ignores update prompts, postpones restarts, or relies on a stale portable build, the automatic update machinery can be undermined. The CVE underscores that “self-updating” is only as effective as the last successful restart.- Enterprises should validate browser build numbers, not just “update status.”
- Consumer systems need a restart after patching to close the window.
- Embedded Chromium apps may remain vulnerable even when Chrome itself is fixed.
- Security teams should watch for alternate channels and portable installations.
- Update rings should be accelerated for browser-engine CVEs.
How This Fits the 2026 Chrome Security Pattern
CVE-2026-4452 is not an isolated event. Chrome’s March 2026 release cycle shows a steady drumbeat of vulnerability fixes across multiple components, with some of the bugs serious enough that Google explicitly said exploits existed in the wild. That matters because it demonstrates how browser defenders increasingly operate in a world where the patch cycle is compressed by real exploitation, not hypothetical risk.Seen in that context, CVE-2026-4452 strengthens a familiar lesson: rendering, graphics, and media subsystems are still the browser’s most fragile surfaces. The fact that the bug is classified as High but not accompanied here by an “exploited in the wild” note does not make it low-priority. It simply means defenders should treat it as a credible pre-exploitation or early-exploitation risk and patch accordingly.
Why release cadence matters
Chrome’s stable channel moved to 146.0.7680.71/72 on March 10 and then to 146.0.7680.75/76 on March 12, showing that the version line was still actively receiving security maintenance within days. The vulnerable threshold for CVE-2026-4452 is later in that same branch, at 146.0.7680.153, which suggests a separate maintenance trajectory and a later fix point within the 146 line. That kind of versioning complexity is why admins should verify exact build numbers rather than rely on rough release-family assumptions.What this says about browser hardening
The recurrence of ANGLE bugs suggests that browser vendors continue to benefit from fuzzing, sanitizer instrumentation, and defense-in-depth measures, but they have not eliminated the class entirely. That is not surprising. Modern browser engines are among the most heavily attacked software stacks on the planet, and their graphics layers must balance speed, compatibility, and safety under a relentless stream of hostile input.- Security response is increasingly measured in hours, not weeks.
- Exact build verification is essential for trust.
- Browser engines remain a top target for attackers.
- Graphics subsystems are especially rich in memory-safety risks.
- Downstream vendors must keep pace with upstream remediation.
Strengths and Opportunities
The good news in this case is that the vulnerability is already publicly cataloged, the affected version boundary is clear, and the fix is available in the current Chrome line. Microsoft’s Security Update Guide also gives defenders a downstream tracking point, which improves the odds that enterprise tooling will surface the issue quickly. That combination makes this a manageable but urgent patch event rather than an open-ended mystery.- The affected version range is explicit.
- The flaw has a recognized CWE classification.
- The CVE is already in Microsoft’s downstream tracking ecosystem.
- Enterprises can automate build verification.
- Consumers benefit from Chrome’s built-in update model.
- The issue reinforces the value of browser hardening investment.
- Security teams can use the event to refine patch-response playbooks.
Risks and Concerns
The main concern is exploitability. A remote browser bug that can induce heap corruption from HTML content is exactly the sort of issue attackers study closely, even when no public exploit has been disclosed yet. If patch adoption lags, the gap between “known vulnerability” and “active exploitation” can become very short indeed.- Delayed browser restarts can leave systems exposed.
- Embedded Chromium apps may be overlooked in inventory scans.
- Compatibility fears can slow enterprise deployment.
- Heap corruption may be only the first stage of a larger exploit chain.
- Mixed-version fleets increase incident-response complexity.
- Driver-specific behavior could make detection inconsistent.
- Users on unsupported or stale channels are at higher risk.
Looking Ahead
The next thing to watch is how quickly the fix propagates through the Chromium ecosystem beyond the main Chrome desktop channel. Chromium-derived products often move at different speeds, and that can create a patch gap even when the upstream bug is already closed. In a world where browser code is shared across products, the real story is not just the CVE, but the distribution velocity of the fix.Security teams should also watch for additional advisories in the ANGLE and graphics stack area. A single integer overflow rarely appears in isolation; it often sits beside other parser, allocator, or bounds-checking bugs that reflect the same underlying risk family. The industry should expect continued scrutiny of GPU-adjacent browser code as fuzzing and attackers both keep pressure on the same surfaces.
- Confirm all Chrome installations are at or beyond the fixed build.
- Verify whether Edge or embedded Chromium apps have received corresponding downstream fixes.
- Audit managed devices for stale browser restarts.
- Monitor exploit intelligence for any movement from disclosure to weaponization.
- Review enterprise policies that slow browser patch adoption.
- Recheck vulnerability-management feeds after NVD enrichment updates.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center