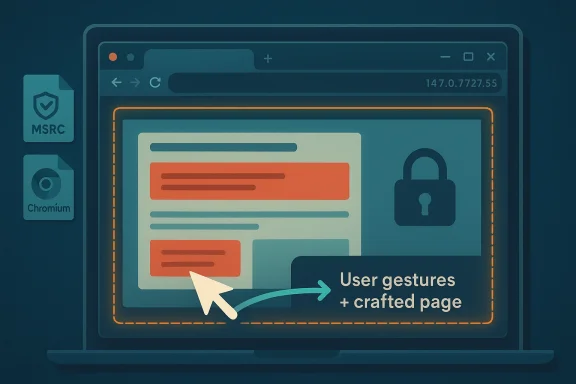
Chromium’s newly disclosed CVE-2026-5896 is a reminder that browser security failures are not always dramatic memory-corruption bugs. Sometimes the danger lies in a quieter category of flaw: a policy bypass that turns ordinary user interaction into a way around built-in protections. In this case, Google says a remote attacker could persuade a user to perform specific UI gestures on a crafted HTML page and thereby bypass sandbox download restrictions in Chrome versions before 147.0.7727.55. Microsoft’s Security Update Guide has already mirrored the CVE entry, signaling that Edge administrators should treat this as part of the standard Chromium patch flow rather than an isolated Chrome-only concern. and Edge users have become accustomed to seeing a steady stream of Chromium security fixes, but not every one of them maps neatly onto the popular idea of “a browser exploit.” Some vulnerabilities are classic memory-safety issues, some are sandbox escapes, and some are subtler violations of browser policy that only matter when an attacker can shape the user’s behavior. CVE-2026-5896 falls into that last category, and that is exactly what makes it worth close attention. It does not promise instant remote code execution, but it can still erode one of the browser’s most important safety rails: the download sandbox boundary.
The timing matters as well. Chrome’s release train has spent much of 2026 moving through a familiar pattern of stable-channel updates that bundle security fixes, rewards, and post-patch documentation. Google’s March and early-April release notes show Chrome 146 and early Chrome 147 activity, while the specific CVE entry for 5896 points to the fix landing before Chrome 147.0.7727.55. That places the issue in the current stable-generation cycle rather than some older, long-tail branch.
The language in the disclosure is also revealing. Google describes the issue as a policy bypass in Audio, and the attack requires “specific UI gestures” on a “crafted HTML page.” That combination strongly suggests a user-interaction bug rather than a drive-by exploit. The attacker’s leverage comes not from brute force, but from steering the victim into a sequence of clicks, drags, or other browse the browser to misapply its own download policies.
For Windows users, the Microsoft update-guide entry is important not because Microsoft authored the flaw, but because Edge inherits Chromium fixes downstream. That means the practical question is not “Did Microsoft create the bug?” but “Has my Edge build absorbed the fixed Chromium code?” The WindowsForum material on recent Chromium CVEs repeatedly shows the same pattern: MSRC lists upstream browser-engine CVEs so customeratus across the Edge ecosystem.
In the broader browser-security landscape, this is part of a familiar shift. Browsers increasingly protect users through layered restrictions on downloads, permissions, and content handling. Yet attackers keep looking for ways to bend those layers without fully breaking them. A policy bypass is often more useful than a noisy crash bug because it can be stealthier, more repeatable, and easier to fit into phishing or lure-based campaigns. That is why a “Low” Chromium severity label should never be mistakeelevance.”
At the center of CVE-2026-5896 is the browser’s handling of downloads and audio-related policy enforcement. Google’s description says a remote attacker could bypass sandbox download restrictions by tricking a user into interacting with a specially crafted HTML page. The attacker does not get a free pass; they still need the user to complete a set of UI gestures. But once that interaction happens, the page can apparently cause the browser to treat a blocked action as if it were ters because browser sandbox rules are designed to make hostile web content less dangerous even when users visit untrusted pages. If a site can trick the browser into relaxing those restrictions at the wrong moment, the attacker gains an opening for follow-on abuse. In practical terms, that could mean a path to delivering payloads or driving a victim toward a malicious file they would otherwise have been protected from handling. The CVE description does not claim full compromise, but it does describe a meaningful erosion of trust boundaries.
The fact that Google frames ty bypass** rather than a direct memory corruption also says something about modern browser threat models. The browser is not only trying to keep attackers out of memory; it is also trying to keep them out of privileged behaviors, hidden file flows, and cross-context interactions. When policy enforcement fails, the result can be less flashy than a crash but still highly consequential for enterprise environments that depend on those policies to keep downloads contained.
Microsoft’s handli with its broader Edge security posture. The company regularly republishes Chromium CVEs in its guidance when Edge adopts the upstream fix, helping enterprise customers confirm whether their browser fleet has moved past the vulnerable build. In other words, the MSRC entry is a status marker, not a separate exploit narrative. That distinction is easy to miss if you only skim the headline.
What stands out is how many recent Chromium fixes involve some form of enforcement failure rather than outright code execution. That has implications for browser design. As core memory defenses get stronger, attackers and researchers alike are increasingly hunting for the gray areas: permission prompts, download trust, UI affordances, gesture requirements, and cross-component policy transitions. CVE-2026-5896 fits squarely into that trend.
This is especialld Windows fleets where browser updates may be staged, paused, or pinned for compatibility reasons. A vulnerable version can remain in circulation long after a fix is public if admins have not advanced the channel. Because the attack requires the user to engage with the page, defenders may assume the risk is remote enough to defer, but that assumption becomes dangerous when phishing campaigns or internal web portals can reproduce the interaction pattern.
For consumer users, the biggest practical safeguard is promrprise teams, the bigger issue is patch compliance visibility. If an organization runs both Chrome and Edge, or allows employees to choose between them, the patch state must be checked on both sides. The downstream browser may carry the same fix but not on the same day, and that timing gap is where risk tends to concentrate.
That makes phishing and social engineering the natural delivery mechanisms. Attackers are already skilled at convincing users to click, drag, comething. A browser bug that converts those gestures into policy bypass conditions gives them a technical payoff for a behavioral trick. The real risk, then, is not the raw code path alone but the blend of UI manipulation and malicious page design.
This is why defenders often prefer to block or scrutinize high-risk content flows even when the exploit chain looks “low severity” on paper. If the attacker can repeatedly farm gesturesctive risk climbs sharply. In a well-tuned campaign, a low-grade browser policy bug can become a reliable foothold for broader fraud or malware delivery.
But execution is where organizations often slip. A browser fix can be available while still missing from endpoints because of update deferrals, update rings, frozen images, or incompatible enterprise policy settings. The browser may also be bundled with other software hat obscure the actual executable version. That means patch validation should be version-based, not assumption-based.
The other positive is that policy-bypass bugs, once understood, are usually easier to validate than ambiguous behavioral flaws. Security teams can test version numbers, confirm update rollout, and measure exposure with more certainty than they can for many active-exploit scenarios. That makes this a manageable problem if organizations move quickly.
A second concern is update lag, especially browser rollout is tied to broader validation cycles. If Chrome and Edge are not patched simultaneously, attackers may simply target whichever browser or endpoint lags behind. That kind of window is often where opportunistic attacks find their easiest wins.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
The timing matters as well. Chrome’s release train has spent much of 2026 moving through a familiar pattern of stable-channel updates that bundle security fixes, rewards, and post-patch documentation. Google’s March and early-April release notes show Chrome 146 and early Chrome 147 activity, while the specific CVE entry for 5896 points to the fix landing before Chrome 147.0.7727.55. That places the issue in the current stable-generation cycle rather than some older, long-tail branch.
The language in the disclosure is also revealing. Google describes the issue as a policy bypass in Audio, and the attack requires “specific UI gestures” on a “crafted HTML page.” That combination strongly suggests a user-interaction bug rather than a drive-by exploit. The attacker’s leverage comes not from brute force, but from steering the victim into a sequence of clicks, drags, or other browse the browser to misapply its own download policies.
For Windows users, the Microsoft update-guide entry is important not because Microsoft authored the flaw, but because Edge inherits Chromium fixes downstream. That means the practical question is not “Did Microsoft create the bug?” but “Has my Edge build absorbed the fixed Chromium code?” The WindowsForum material on recent Chromium CVEs repeatedly shows the same pattern: MSRC lists upstream browser-engine CVEs so customeratus across the Edge ecosystem.
In the broader browser-security landscape, this is part of a familiar shift. Browsers increasingly protect users through layered restrictions on downloads, permissions, and content handling. Yet attackers keep looking for ways to bend those layers without fully breaking them. A policy bypass is often more useful than a noisy crash bug because it can be stealthier, more repeatable, and easier to fit into phishing or lure-based campaigns. That is why a “Low” Chromium severity label should never be mistakeelevance.”
 What the Vulnerability Actually Does
What the Vulnerability Actually Does
At the center of CVE-2026-5896 is the browser’s handling of downloads and audio-related policy enforcement. Google’s description says a remote attacker could bypass sandbox download restrictions by tricking a user into interacting with a specially crafted HTML page. The attacker does not get a free pass; they still need the user to complete a set of UI gestures. But once that interaction happens, the page can apparently cause the browser to treat a blocked action as if it were ters because browser sandbox rules are designed to make hostile web content less dangerous even when users visit untrusted pages. If a site can trick the browser into relaxing those restrictions at the wrong moment, the attacker gains an opening for follow-on abuse. In practical terms, that could mean a path to delivering payloads or driving a victim toward a malicious file they would otherwise have been protected from handling. The CVE description does not claim full compromise, but it does describe a meaningful erosion of trust boundaries.Why h a big deal
User-interaction requirements often make vulnerabilities sound less serious, but that can be misleading. A gesture requirement is not much of a barrier when the attacker can wrap it inside a fake prompt, a lure page, or an imitation document portal. The browser may still be secure in a purely technical sense, yet the real-world attack surface expands because people are trainable and predictable. That is especially true when the page is designed to look like a normal download or preview workflow.The fact that Google frames ty bypass** rather than a direct memory corruption also says something about modern browser threat models. The browser is not only trying to keep attackers out of memory; it is also trying to keep them out of privileged behaviors, hidden file flows, and cross-context interactions. When policy enforcement fails, the result can be less flashy than a crash but still highly consequential for enterprise environments that depend on those policies to keep downloads contained.
- The attack is remote, but it is not fully drr needs the victim to perform specific UI gestures.
- The effect is a bypass of sandbox download restrictions.
- The issue is tied to the Audio area of Chromium.
- Google rated it Low in Chromium’s internal severity model.
Why the Audio label may confuse readers
The “Audio” label does not bug is about music playback or microphones in the obvious sense. In Chromium, component labels often reflect the subsystem where the flaw was found or where the enforcement failure occurred, not just the user-facing feature a person might associate with the name. That means the real operational lesson is to focus on the affected policy path, not the label alone. The label helps route the fix, but the impact is about download handling and browser trust boundaries.How Google and Microsoft Are Framing the Risk
Google’s release notes are the primar the Chrome-side fix, and the Chrome Releases archive shows that the 2026 stable update cycle has been busy with security work throughout March and April. The specific CVE entry for 5896 is reflected in Microsoft’s Security Update Guide as well, which is exactly how downstream Chromium consumers typically surface inherited browser bugs. That cross-listing matters because it tells administrators the issue is not hypothetical and not confined to a single vendor’s UI layer.Microsoft’s handli with its broader Edge security posture. The company regularly republishes Chromium CVEs in its guidance when Edge adopts the upstream fix, helping enterprise customers confirm whether their browser fleet has moved past the vulnerable build. In other words, the MSRC entry is a status marker, not a separate exploit narrative. That distinction is easy to miss if you only skim the headline.
Why downstream tracking matters fors, the practical challenge is rarely “Is Chrome fixed?” It is “Are all my Chromium-based endpoints fixed?” Edge often moves on a similar cadence, but validation is still necessary because patch windows, policy baselines, and update deferrals can create lag. Microsoft’s CVE listing gives admins a clean way to line up their internal inventory against the upstream Chromium patch train.
That makes the CVE important even when the score is Low. A lead to complacency, yet policy bypass bugs are exactly the sort of issues that can be chained with social engineering or misuse of browser features. An attacker does not need a blockbuster exploit if they can abuse a control path that defenders assume is safe.- Google is the source of the Chrome fix and the vulnerability description.
-cking the issue for Edge consumers. - The patch threshold is 147.0.7727.55 for Chrome.
- The real-world risk depends on user interaction and browser update lag.
- Administrators should verify both Chromium version and Edge deployment state.
The significance of a Low severity label
A Low severity label is not a statement of irrelevanthe vendor expects a narrower exploit path, less impact, or a smaller blast radius than with critical memory corruption. But low-severity browser policy bugs can still matter because they are often used as building blocks in a longer attack chain. If an attacker can get past a download boundary, they may not need a kernel escape to create real damage.The Wider Chromium Pattern in 2026
CVE-2026-5896 is not appearing in a vacuum. Chrome Releases throughout 2026 havbeat of fixes across rendering, UI trust, Web APIs, and policy enforcement. March’s stable update cycle alone included multiple security items, and April’s early stable rollout shows the browser project still pushing rapid channel transitions. The practical lesson is that Chrome’s security surface remains broad, and policy bugs continue to sit alongside more traditional memory issues in the fix queue.What stands out is how many recent Chromium fixes involve some form of enforcement failure rather than outright code execution. That has implications for browser design. As core memory defenses get stronger, attackers and researchers alike are increasingly hunting for the gray areas: permission prompts, download trust, UI affordances, gesture requirements, and cross-component policy transitions. CVE-2026-5896 fits squarely into that trend.
Policy bugs are a growing class of browser is policy engine as much as it is a rendering engine. It decides when to show warnings, when to gate file access, when to respect the sandbox, and when to trust user intent. Each of those decisions is a potential security boundary, and each can fail in subtle ways. That is why the browser-security conversation is no longer dominated only by buffer overflows and use-after-free bugs.
This also explains why vendor language can sometimes appear understate“bypasses policy” can sound abstract, but in the browser world policy is the thing standing between an ordinary website and a privileged local action. The difference between blocked and allowed is often the difference between annoyance and incident.- Chromium’s 2026 release cycle has been packed with policy and UI trust issues.
- ingly interested in user-driven exploit paths.
- Browser security now depends on more than memory safety alone.
- The sandbox is only as good as the enforcement layer around it.
- Subtle bugs can have outsized operational impact in managed environments.
Why This Matters for Windows and Edge Users
For Windows users, the most important question is whether their browser is Chrome, Edge, or another Chromium-based product that consumes upstream fixes. Microsoft’s Security Update Guide exists precisely because Chromium issues ripple into Edge deployments and enterprise baselines. That makes CVE-2026-5896 relevant beyond the Chrome brand, even if the exploit description originated with Google.This is especialld Windows fleets where browser updates may be staged, paused, or pinned for compatibility reasons. A vulnerable version can remain in circulation long after a fix is public if admins have not advanced the channel. Because the attack requires the user to engage with the page, defenders may assume the risk is remote enough to defer, but that assumption becomes dangerous when phishing campaigns or internal web portals can reproduce the interaction pattern.
Enterprise versus consumer impact
to experience the issue as a general browser safety problem: a suspicious page may manipulate them into doing something the browser should not permit. Enterprises face a broader exposure surface because the browser is often the front door to internal apps, file exchanges, and cloud storage workflows. That means a policy bypass tied to downloads can become a data-governance issue, not just a browser bug.For consumer users, the biggest practical safeguard is promrprise teams, the bigger issue is patch compliance visibility. If an organization runs both Chrome and Edge, or allows employees to choose between them, the patch state must be checked on both sides. The downstream browser may carry the same fix but not on the same day, and that timing gap is where risk tends to concentrate.
- Chrome and Edge may both be affected until their respective fixed builds a updates can leave a temporary exposure window.
- User training helps, but it does not replace browser patching.
- Internal portals can be as risky as public websites when gesture-based trust is involved.
- Managed endpoints need version audits, not just generic security policies.
What admins should verify
Administrators should verify the installed browser build, the release te policy that governs each endpoint. They should also watch for exceptions such as VDI images, offline laptops, and long-lived kiosks, because those environments often miss the latest stable release first. In many organizations, those are the exact systems that spend the most time in browsers for transactions or documentation.Attack Scenarios and Likely Abuse Patterns
The disclosure does not describe active exploitation in the wild, and Still, the structure of the bug suggests very plausible abuse patterns. A malicious actor could host a page that imitates a file preview, a download gate, or a media workflow and then coax the user into the precise sequence of gestures needed to trigger the bypass. The lure would not need to be sophisticated; it would only need to be believable enough to get the user to play along.That makes phishing and social engineering the natural delivery mechanisms. Attackers are already skilled at convincing users to click, drag, comething. A browser bug that converts those gestures into policy bypass conditions gives them a technical payoff for a behavioral trick. The real risk, then, is not the raw code path alone but the blend of UI manipulation and malicious page design.
What a crafted HTML page likely tries to do
A crafted HTML page in this context probably aims to simulate a legitimate workflow while quietly steering the browate. That can include fake download buttons, misleading play controls, or staged prompts that appear to request harmless interaction. The key is that the user does not feel they are authorizing something sensitive, even though the browser might be internally treating the gesture as permission.This is why defenders often prefer to block or scrutinize high-risk content flows even when the exploit chain looks “low severity” on paper. If the attacker can repeatedly farm gesturesctive risk climbs sharply. In a well-tuned campaign, a low-grade browser policy bug can become a reliable foothold for broader fraud or malware delivery.
- The most likely abuse path is phishing plus browser gesture abuse.
- A fake download or media interaction is a credible lure.
- The attacker benefits from the user believing the action is safe.
- Th useful as a delivery enabler, not a final payload.
- Repetition makes even a narrow bug operationally attractive.
Why sandbox bypasses still matter without code execution
Security teams sometimes rank issues by whether they permit code execution, but that approach can miss how attackers actually work. If a sandbox restriction can be bmay gain access to files, downloads, or workflows that were supposed to be isolated. Even without immediate execution, that can be enough to move a campaign forward. In the browser world, boundary break is often the first milestone in a larger intrusion.Patch Management Implications
From a patch-management standpoint, CVE-2026-5896 is straightforward: get to the fixed Chrome build and ensure Edge has incorporated the upstream Chromium patch. The version number matters because browser close not by a standalone hotfix artifact but by moving the entire browser forward to the corrected build. In this case, that threshold is Chrome 147.0.7727.55.But execution is where organizations often slip. A browser fix can be available while still missing from endpoints because of update deferrals, update rings, frozen images, or incompatible enterprise policy settings. The browser may also be bundled with other software hat obscure the actual executable version. That means patch validation should be version-based, not assumption-based.
A practical verification sequence
- Check the deployed browser version on representative endpoints.
- Confirm whether the channel is stable, beta, or otherwise managed.
- Verify whether Edge has already ingested the relevant Chromium fix.
- Audit exceptions such as VDI, kiosms.
- Re-test after any policy-controlled update window closes.
- Version checks beat generic “we patch regularly” assurances.
- Channel awareness matters because not every install updates at the same speed.
- Image-based deployments can lag behind the live browser release.
- Edge and Chrome should both be included in verification.
- Post-patch validation sart of the fix, not an afterthought.
Why this is a Windows ecosystem issue
Even though the bug lives in Chromium, Windows shops feel the impact because browsers are deeply integrated into daily productivity. Downloads, document workflows, remote collaboration, and cloud storage all funnel through browser sessions. A policy bypass in that layer is therefore not joblem; it is a workflow integrity problem. That is why MSRC’s downstream tracking is so useful for Windows administrators.Strengths and Opportunities
The encouraging part of this disclosure is that the security ecosystem is working the way it should. Google identified the bug, fixed it before the affected stable build threshold, and Microsoft surfaced the issue so Edge customers can align their own deployments. That transparency gives administrators a clean pathit reduces the odds that the issue remains hidden in a downstream browser build.The other positive is that policy-bypass bugs, once understood, are usually easier to validate than ambiguous behavioral flaws. Security teams can test version numbers, confirm update rollout, and measure exposure with more certainty than they can for many active-exploit scenarios. That makes this a manageable problem if organizations move quickly.
- Upstream disclosure able**.
- The fixed version is specific and easy to audit.
- Edge customers get downstream visibility through MSRC.
- The issue is likely patchable without major configuration changes.
- Security teams can validate exposure with version checks.
- The bug reinforces the value of rapid browser update pipelines.
- Awareness of gesture-based attacks may improve user training.
Risks and Concerns
The biggest concern is that “Low” severity may lull teams into delaying action. Policy bypasses are exactly the sort of issues that can be abused in campaigns where users are already primed to click, confirm, or drag something on a page. If the lure is good enough, the exploit requirement may not be much of a barrier at all.A second concern is update lag, especially browser rollout is tied to broader validation cycles. If Chrome and Edge are not patched simultaneously, attackers may simply target whichever browser or endpoint lags behind. That kind of window is often where opportunistic attacks find their easiest wins.
- Severity labels can understate real operational risk.
- Human interaction is a duraatch lag** creates a temporary but real exposure window.
- Enterprise exceptions often outlive the main rollout.
- Downstream browsers may not update at exactly the same pace.
- Phishing lures can be tailored to the required UI gestures.
- Policy bypasses can become part of a larger multi-stage attack chain.
Looking Ahead
The main thing to watch next is how quickly the fixed build propagates through Chrome’s stable channel and into Edge deployments. If the patch lands cleanly and organizations move promptly, CVE-2026-5896 may fade into the background as just another entry in a busy Chromium security calendar. But if update windows stretch out, the bug could become a useful target for low-noise phishing and download-abuse campaig worth watching whether more details emerge about the exact UI gesture sequence or whether the issue is folded into broader discussions about browser gesture trust. Chromium has spent the year shipping fixes across many categories, and policy enforcement bugs are becoming one of the more interesting battlegrounds because they sit at the intersection of design, usability, and security. That intersection is where attackers tend to find lever.googleblog.com]- Confirm the rollout of Chrome 147.0.7727.55 or later.
- Watch for Edge update status in Microsoft’s guidance.
- Look for any sign of gesture-based phishing lures.
- Check whether the bug is discussed in future Chromium security notes.
- Monitor managed endpoints where browser updates are delayed or pinned.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
Last edited: