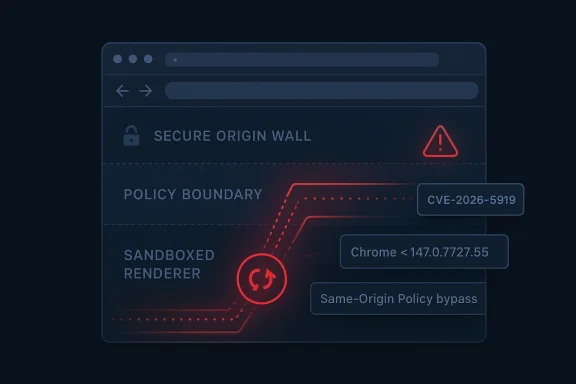
Chromium’s latest browser security disclosure, CVE-2026-5919, is a reminder that “low” severity does not always mean low operational importance. Microsoft’s Security Update Guide records the flaw as insufficient validation of untrusted input in WebSockets in Google Chrome prior to 147.0.7727.55, and says a remote attacker who had already compromised the renderer process could bypass the same-origin policy using a crafted HTML page. The issue was received into Microsoft’s guidance on April 8, 2026, and it was modified the next day with CWE-20 Improper Input Validation and a CVSS 3.1 base score of 6.5 Medium. ser CVEs often look deceptively narrow when you first read them. A weakness in a single subsystem, a single API, or a single page state can still become meaningful once an attacker already has a foothold inside the browser’s most privileged execution path. In this case, the phrase renderer process compromise is the real tell: the bug is not described as a clean, one-click remote code execution issue, but as a post-compromise policy bypass that turns an existing beachhead into something more dangerous.
That distinction mam’s architecture is built around layered containment. The renderer is supposed to be the least trusted part of the browser stack, while higher-trust components and policy boundaries prevent one bad page from breaking out into broader access. When a flaw lets untrusted input slip through WebSockets validation and then weakens same-origin policy protections, it undermines the trust model that keeps web content separated in the first place.
The timing also fits a familiar pattern.le update cadence continues to push patched builds into the channel quickly, and Microsoft’s Security Update Guide mirrors those upstream Chromium issues so Edge and enterprise defenders can track whether downstream builds have absorbed the fix. Microsoft has spent the last few years making the Security Update Guide more transparent, adding CWE data and better structured vulnerability records to help customers interpret the root cause rather than just the CVE label.
In practical terms, this is the kind of browser issue that does not look dramatic to consumers but does matter to defenders. Chrome’s own stable-channel release notes have repeatedly emphasized that security details may be held back until most users are protected, and that caution is especially common for browser flaws that can be chained with other bugs or depend on a preexisting compromise. That context makes CVE-2026-5919 part of a wider security cycle, not an isolated bug report.
At its core, CVE-2026-5919 is a validation failure. The advisory says untrusted input in WebSockets was not sufficiently checked in Chrome versions before 147.0.7727.55, creating a path for a remote attacker to bypass the same-origin policy after the renderer had already been compromspecific attack shape, but it tells a larger story about how browser trust boundaries fail: small parsing mistakes often become policy mistakes.
That distinction should not reduce concern. Once an attacker can defeat same-origin protections, the browser’s data separation model starts to collapse, and the value of other bugs or social-engineering lures rises sharply. In a real campaign, a renderer compromise plus a policy bypass can be enough to turn an initial web compromise into credential theft, session abuse, trusted sites. That is why policy bypass bugs deserve more attention than their “Low” labels suggest.
This is also why the root cause lands in CWE-20, not a memory-safety category. The weakness is about accepting, interpreting, or passing along data in a way the browser should have rejected. In modern browser security, validation failures often look mundane compared with a crash, but ul to attackers because they alter policy, not just stability.
A browser weakness can be low severity in isolation and still be important because it fits neatly into a multi-step intrusion path. Security teams should therefore read the exploit preconditions as carefully as the CVSS number. In this case, the prerequisite renderer compromise narrows the threat model, but it does not eliminate the need to patch quickly because renderer compromises are exactly what many browsedesigned to achieve.
The fact that this issue is tied to WebSockets also suggests a broad threat surfacd by consumer applications, enterprise SaaS platforms, and internal dashboards alike, so the exploitability of the bug depends as much on ecosystem usage as on the browser implementation itself. That is why a single validation mistake in a core protocol path can ripple far beyond the browser team’s immediate patch window.
This is also where Microsoft’s Security Update Guide becomes useful. Microsoft’s transparency work around CWE labels, CVE ingestion, and machine-a exists to help customers track whether downstream products like Edge have absorbed the upstream Chromium fix. That downstream mapping is a core part of how Chromium security actually reaches corporate fleets.
That creates both convenience and risk. It is convenient because one upstream fix often protects multiple browser families. It is risky because organizations that assume “we only use Edge” may delay action if they do not watch Chromium advisories closely enough. Browser dependency chains can hide exposure in plain sight.
That is why browser patching belongs in the same conversation as endpoint hardening and identity protection. If a malicious session can abuse origin boundaries to access authenticated content, then MFA, conditional access, and SSO discipline maed unless the browser itself is kept current. Patch lag is an exposure multiplier.
Organizations with heavy web-app dependency should also think about compensating controls. Logging unusual renderer crashes, detecting anomalous session behavior, and tightening browser extension policy can all help reduce the chance that a post-compromise browser flaw turns into broader access. These controls do not replace the patch,blast radius while rollout is in progress.
The market implication is clear: browser vendors are now judged not only on feature velocity, but on how quickly they can close policy bugs that threaten the assumptions of the web itself. In that sense, CVE-2026-5919 is another example of why browser security is now a board-level concern, not a niche
That is why Google and Microsoft both increasingly emphasize root-cause labeling. Microsoft’s adoption of CWE in the Security Update Guide is meant to help defenders spot patterns across advisories, and here the CWE-20 tag instantly signals a class of mistake rather than a one-off implementation glitch. That kind of taxonomy is useful because it helps teams think in systemic terms, not just patch-by-patch terms.
That means defenders need to interpret low-severity browser CVEs through the lens of chaining potential. If a bug weakefter a renderer compromise, it may not be the exploit headline, but it is still a force multiplier. Attack chains are where small browser bugs become large incidents.
That visibility matters because many organizations operate mixed browser environments. If the fix lands in Chrome first and in Edge later, or if one managed browser build lags another, attackers can target the weaker update posture. The practical lesson is that cross-browser patch parity is now part of basic hygiene.
The CWE tagging is particularly useful here. Microsoft has explicitly said it uses CWE to improve transparency and help customers and developers understand root causes, and this record fits that model exactly. A browser input-validation bug is not just a one-off line item; it is an example of the kind of weakness that can recur across subsystems if engineering teams do not treat it as a pattern.
In broader market terms, this also shows how quickly Chrome security work now becomes a Microsoft tracking event. Because Chromium is the common engine for both Chrome and Edgork now has an immediate downstream enterprise dimension. The patch is rarely just a Chrome patch anymore.
The broader security trend is equally clear. Browser vulnerabilities are increasingly about trust boundaries, policy enforcement, and cross-origin behavior rather than only obviors. That means defenders will keep seeing CVEs that look modest until they are placed inside a chain, which is exactly why speed, telemetry, and version management matter so much in 2026.
What to watch next:
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
That distinction mam’s architecture is built around layered containment. The renderer is supposed to be the least trusted part of the browser stack, while higher-trust components and policy boundaries prevent one bad page from breaking out into broader access. When a flaw lets untrusted input slip through WebSockets validation and then weakens same-origin policy protections, it undermines the trust model that keeps web content separated in the first place.
The timing also fits a familiar pattern.le update cadence continues to push patched builds into the channel quickly, and Microsoft’s Security Update Guide mirrors those upstream Chromium issues so Edge and enterprise defenders can track whether downstream builds have absorbed the fix. Microsoft has spent the last few years making the Security Update Guide more transparent, adding CWE data and better structured vulnerability records to help customers interpret the root cause rather than just the CVE label.
In practical terms, this is the kind of browser issue that does not look dramatic to consumers but does matter to defenders. Chrome’s own stable-channel release notes have repeatedly emphasized that security details may be held back until most users are protected, and that caution is especially common for browser flaws that can be chained with other bugs or depend on a preexisting compromise. That context makes CVE-2026-5919 part of a wider security cycle, not an isolated bug report.
 What CVE-2026-5919 Actually Means
What CVE-2026-5919 Actually Means
At its core, CVE-2026-5919 is a validation failure. The advisory says untrusted input in WebSockets was not sufficiently checked in Chrome versions before 147.0.7727.55, creating a path for a remote attacker to bypass the same-origin policy after the renderer had already been compromspecific attack shape, but it tells a larger story about how browser trust boundaries fail: small parsing mistakes often become policy mistakes.The attack model
The most important phrase is “who had compromised the renderer process.” That means this flaw is not, by itself, a universal drive-by exploit in the usual sense. Instead, it is a post-exploitation opportunity r escalate the value of a renderer foothold by crossing origin boundaries or reading data that should have remained isolated.That distinction should not reduce concern. Once an attacker can defeat same-origin protections, the browser’s data separation model starts to collapse, and the value of other bugs or social-engineering lures rises sharply. In a real campaign, a renderer compromise plus a policy bypass can be enough to turn an initial web compromise into credential theft, session abuse, trusted sites. That is why policy bypass bugs deserve more attention than their “Low” labels suggest.
Why WebSockets are sensitive
WebSockets are not just another web API. They establish persistent, bidirectional communication and can sit at the center of realtime apps, authenticated workflows, collaboration tools, and service dashboards. Because WebSockets often carry authenticated application state, bad validation insite outsized consequences if the browser misclassifies or mishandles untrusted data.This is also why the root cause lands in CWE-20, not a memory-safety category. The weakness is about accepting, interpreting, or passing along data in a way the browser should have rejected. In modern browser security, validation failures often look mundane compared with a crash, but ul to attackers because they alter policy, not just stability.
What the severity label does and does not say
Chromium’s own severity classification for this issue is Low, but Microsoft’s enrichment adds a 6.5 Medium score through CISA-ADP. That mismatch is not unusual when a vendor’s internal severity model is compared with a broader scoring framework. It also underscores a practical poiare not the same thing as exploit value*.A browser weakness can be low severity in isolation and still be important because it fits neatly into a multi-step intrusion path. Security teams should therefore read the exploit preconditions as carefully as the CVSS number. In this case, the prerequisite renderer compromise narrows the threat model, but it does not eliminate the need to patch quickly because renderer compromises are exactly what many browsedesigned to achieve.
Why the Same-Origin Policy Bypass Matters
The same-origin policy is one of the browser’s foundational protections. It prevents a page from reading or manipulating data belonging to a different origin unless the browser explicitly allows it. If an attacker can abuse a Chromium subsystem to bypass that policy, the browser stops behaving like a collection of isolated security compartments and starts looking more like a looselyTrust boundaries in the browser
Browsers rely on multiple trust boundaries: origin separation, process isolation, sandboxing, and permission gates. A renderer compromise already means the attacker is inside one of the least trusted zones, but the goal of most modern exploit chains is to pivot outward from there. CVE-2026-5919 is interesting because it helps make that pivot by abusing a validation failure in a communications feature that many apps assume is trustworthy. at enterprise defenders should care about most. If a malicious page can coerce the browser into relaxing or misapplying origin checks, then internal portals, webmail, admin consoles, and SSO-dependent apps become more exposed. The vulnerability is not just a “Chrome bug”; it is a shortcut around a security principle that many organizations rely on every day.What an attackeft’s description stops short of claiming full remote code execution, and that restraint is important. But policy bypasses can still expose high-value data, especially in workflows that depend on browser session state. In the wrong chain, bypassing origin protections can enable cross-site data reads, token misuse, or interaction with privileged pages that should have remained off-limits.
It is also worth noting that browser expn prizes these “secondary” bugs. Attackers frequently use a memory corruption flaw to get into a renderer, then use a logic bug or policy bypass to extract secrets or cross a compartment boundary. In that sense, CVE-2026-5919 looks like the sort of enabling flaw that helps a bigger attack pay off.Why this is different from a crash bug
A crash is noisy.be much quieter. That makes validation bugs especially tricky in web security, because the malicious path may look like ordinary browser behavior from the outside while subtly breaking assumptions under the hood. Silent failure is often the more dangerous failure.The fact that this issue is tied to WebSockets also suggests a broad threat surfacd by consumer applications, enterprise SaaS platforms, and internal dashboards alike, so the exploitability of the bug depends as much on ecosystem usage as on the browser implementation itself. That is why a single validation mistake in a core protocol path can ripple far beyond the browser team’s immediate patch window.
The Patch and Version Line
Google’s fix lands in Chrome 147.0.7727.55 and earlier builds ar. That version boundary is the central operational fact for administrators and for users who simply want to know whether they are exposed. If your Chromium-based browser has not yet crossed that build number, it deserves immediate attention.Why version-based guidance matters
Version-specific advisories are the cleanest way to translate a technical issue into. They let administrators map the vendor’s disclosure to their patch inventory and decide whether managed update channels have already delivered the fix. For browser security, that is especially important because consumers, small businesses, and enterprises do not all update at the same pace.This is also where Microsoft’s Security Update Guide becomes useful. Microsoft’s transparency work around CWE labels, CVE ingestion, and machine-a exists to help customers track whether downstream products like Edge have absorbed the upstream Chromium fix. That downstream mapping is a core part of how Chromium security actually reaches corporate fleets.
Chrome, Edge, and the downstream effect
Because Microsoft Edge is Chromium-based, many organizations treat Chrome and Edge patch posture as linked rather than separate. Microsoft’s Security Update Guide routinely surfaces Chromium CVEs so security teams can align their browser patching policies across platforms and vendors. The broader lesson is that a Chrome CVE is often also an Edge readiness question.That creates both convenience and risk. It is convenient because one upstream fix often protects multiple browser families. It is risky because organizations that assume “we only use Edge” may delay action if they do not watch Chromium advisories closely enough. Browser dependency chains can hide exposure in plain sight.
Operational steps for administrators
A good patch response to a Chromium policy bypass is simple, but it should still be disciplined. The goal is to eliminate the vulnerable build, confirm version compliance, and reduce the chaoit while the fix rolls out. In large environments, this usually means validating browser versions through management tooling rather than relying on end-user reporting.- Confirm browser versions on managed endpoints.
- Prioritize any Chrome or Chromium-based build earlier than 147.0.7727.55.
- Validate whether Edge or another embedded Chromium runtime has already ingested throwser update policies with the organization’s patch window.
- Treat any renderer-compromise indicators as high urgency when paired with this CVE.
The Enterprise Security Angle
For enterprises, CVE-2026-5919 is less about one browser tab and more about the reliability of browser-based work. Many companies now depend on web applications for identity, collaboration, admin functions, reporting, and helpdesk workflows. If a browser issue casolation after a renderer compromise, the downstream business risk extends to sessions, portals, and browser-hosted workflows.Why defenders should care even if the flaw is “Low”
Security teams often triage based on severity labels, but the browser world punishes that shortcut. A low-severity bug in the browser’s trust model can be a stepping stone in a much larger chain, especially when the attacker has already achieved initial compromise through phishing, malicious ads, drive-by conten flaw. In other words, the weakness may not be the first domino, but it can be the one that matters most.That is why browser patching belongs in the same conversation as endpoint hardening and identity protection. If a malicious session can abuse origin boundaries to access authenticated content, then MFA, conditional access, and SSO discipline maed unless the browser itself is kept current. Patch lag is an exposure multiplier.
Enterprise vs. consumer impact
For consumers, the most immediate outcome is straightforward: update the browser. For enterprises, the issue is more structural because browser updates are filtered through policy, packaging, testing, and change management. That means the real question is not whether the fix exiit reaches all managed endpoints and embedded browser surfaces.Organizations with heavy web-app dependency should also think about compensating controls. Logging unusual renderer crashes, detecting anomalous session behavior, and tightening browser extension policy can all help reduce the chance that a post-compromise browser flaw turns into broader access. These controls do not replace the patch,blast radius while rollout is in progress.
The hidden cost of browser normalization
One of the challenges with Chromium security is that the browser has become infrastructure. People think of browsers as apps, but in enterprise environments they function more like a delivery platform for identity, communication, and cloud operations. That makes any origin-bypass issue more consequenve been a decade ago.The market implication is clear: browser vendors are now judged not only on feature velocity, but on how quickly they can close policy bugs that threaten the assumptions of the web itself. In that sense, CVE-2026-5919 is another example of why browser security is now a board-level concern, not a niche
How This Fits Chromium’s Broader Security Pattern
Chromium has spent years shipping fixes for flaws that range from memory corruption to policy enforcement bugs to UI deception and information leaks. Recent Chrome release cycles have included many issues where the exploit story depends on how a bug interacts with the sandbox, the renderer, or browser policy rather than on a single dramatic overwrite. That pattern makes CVE-2026-5919 feel very familiar.Validation bugs keep showing up
Input validation failures remain a persistent browser problem because they are easy to underestimate. Developers may think they are simply accepting structured data from a trusted browser feature, but attack traffic often arrives through paths that are only partly constrained or whose assumptions differ between components. When that happens in a subsystem likurity impact can be much wider than the code path appears at first glance.That is why Google and Microsoft both increasingly emphasize root-cause labeling. Microsoft’s adoption of CWE in the Security Update Guide is meant to help defenders spot patterns across advisories, and here the CWE-20 tag instantly signals a class of mistake rather than a one-off implementation glitch. That kind of taxonomy is useful because it helps teams think in systemic terms, not just patch-by-patch terms.
Browser exploits are increasingly chained
A few years ago, many security discussions treated browser bugs as” or “full RCE.” The current reality is subtler. Attack chains often combine a renderer compromise, a policy bypass, and a data-exposure flaw, with each step doing only one part of the job.That means defenders need to interpret low-severity browser CVEs through the lens of chaining potential. If a bug weakefter a renderer compromise, it may not be the exploit headline, but it is still a force multiplier. Attack chains are where small browser bugs become large incidents.
Why Microsoft’s tracking matters
Microsoft’s role here is not incidental. The company’s Security Update Guide now serves as an important downstream map for Chromium-origin vulnerabilities, especially when customers are trying to determine whether Edge has received the upstream fix. Its CVE records, CWE annotations, and advisory pages make it easier to align patch cadence across products that share the same browser engine.That visibility matters because many organizations operate mixed browser environments. If the fix lands in Chrome first and in Edge later, or if one managed browser build lags another, attackers can target the weaker update posture. The practical lesson is that cross-browser patch parity is now part of basic hygiene.
What Microsofuide Tells Us
Microsoft’s Security Update Guide records CVE-2026-5919 as a Chromium issue received from Chrome, and its change history shows the CVSS and CWE enrichment added on April 9, 2026. That tells us two things: Microsoft is surfacing the upstream issue quickly, and the advisory is already being normalized into the structured data customers use for patch management.Structured data is part of the defense
This matters because modern vulnerability management is increasingly machine-assisted. Security teams ingest CVEs into dashboards, patch prioritization platforms, and compliance systems, then use that data to decide which endpoints need attention first. The richer the record, the less likely a browser vulnerability is to be missed or misclassified.The CWE tagging is particularly useful here. Microsoft has explicitly said it uses CWE to improve transparency and help customers and developers understand root causes, and this record fits that model exactly. A browser input-validation bug is not just a one-off line item; it is an example of the kind of weakness that can recur across subsystems if engineering teams do not treat it as a pattern.
The limitations of the advisory model
At the same time, Security Update Guide entries are not detailed exploit writeups. They cted, what the weakness is, and what version boundary matters, but they do not usually expose the full exploit chain. That is by design, especially for active or newly published browser issues where disclosure timing must balance transparency with user protection. ([chromereleases.googleblog.com](Stable Channel Update for Desktop readers, that means the advisory should be used as a remediation signal, not a forensic dossier. If you need the exact technical chain, you may need additional research from upstream Chrome security notes or issue trackers. But for patch planning, the Microsoft record is already enough to justify immediate action.What the publication timeline implies
The CVE was published by NVD on April 8, 2026 and modified on April 9, 2026, matching the same window in Microsoft’s update guide. That tight turnaround suggests the issue moved through normal disclosure channels rather than sitting dormant for long. In browser security, speed like that usually means defenders should move just as quickly.In broader market terms, this also shows how quickly Chrome security work now becomes a Microsoft tracking event. Because Chromium is the common engine for both Chrome and Edgork now has an immediate downstream enterprise dimension. The patch is rarely just a Chrome patch anymore.
Strengths and Opportunities
The encouraging side of CVE-2026-5919 is that it is clearly bounded, already assigned a version fix, and already visible in Microsoft’s tracking system. That makes r simpler than it would be for a hidden or actively exploited zero-day with no obvious remediation path. It also shows the valueam security coordination across the Chromium ecosystem.- The affected version line is explicit: Chrome prior to 147.0.7727.55.
- The weakness is classified as CWE-20 Improper Input Validation, which helps de similar bugs.
- Microsoft has already surfaced the issue in the Security Update Guide, helping Edge customers track downstream exposure.
- The advisory indicates the attacker must already have compromised the renderer process, which narrows the direct attack model.
- The same-origin policy is a foundational browser control, so fixing this class of bug preserves a core trust b arrived with structured metadata, making it easier to automate patch prioritization. ([msrc.micrrc.microsoft.com/blog/2024/04/toward-greater-transparency-adopting-the-cwe-standard-for-microsoftnai))
- Consumers and enterprises both have a simple action item: update the browser promptly.
Ren with a modest severity label, this CVE still exposes several risks that matter in the real world. The chief cndalone bug description; it is how easily a policy bypass can extend the value of a separate browser compromise. That makes the vulnerability more relevant to intrusion chains than to casual users reading the label at face value.
- A **renderer comtic starting point for a broader browser exploit chain.
- Bypassing the same-origin policy can exposat should remain isolated.
- WebSockets are widely used in authenticated apps, raising the chance of meaningful real-world impact.
- Enterprises with slow patch cycles may leave a vulnerable browser build in circulation longer than intended.
- Mixed browser estates can create uneven exposure if Chrome updates faster than Edge or embedded Chromium runtimes.
- Low-severity labels can encourage complacency, especially when the exploit story is conditional.
- Attackers tend to value quiet policy bugs because they can be easier to chain and harder to detect.
Looking Ahead
The next question is not whether CVE-2026-5919 will be patched, but how quickly fleets remove the vulnerable build from circulation. Chrome has already moved to the fixed version boundary, and Microsoft’s publication indicates the issue is now part of the downstream tracking lstrators use for validation. In practice, that means patch verification, not just patch availability, becomes the decisive task.The broader security trend is equally clear. Browser vulnerabilities are increasingly about trust boundaries, policy enforcement, and cross-origin behavior rather than only obviors. That means defenders will keep seeing CVEs that look modest until they are placed inside a chain, which is exactly why speed, telemetry, and version management matter so much in 2026.
What to watch next:
- Confirmation that managed Chrome fleets are at 147.0.7727.55 or later.
- Edge’s downstream patch status in Microsoft’s Security Update Guide.
- Whether additional Chromium components receive related validation fixes in later stable releases.
- Any signs that the flaw was used as part of a broader exploit chain.
- Follow-on advisories that clarify whether other browser-based products inherited the same code path.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center