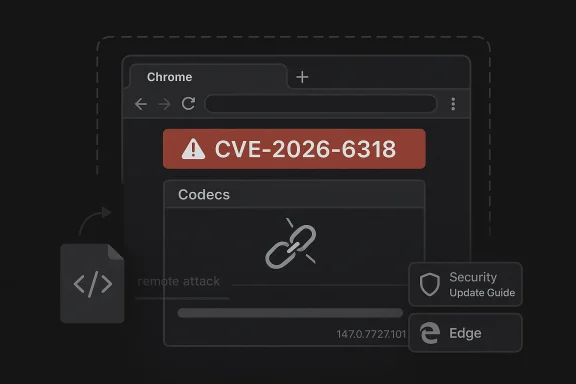
Google’s disclosure of CVE-2026-6318 is another reminder that the browser security story is still dominated by memory safety bugs, not just policy bypasses and UI tricks. The flaw is a use-after-free in Codecs affecting Google Chrome prior to 147.0.7727.101, and Google says a crafted HTML page could let a remote attacker execute code inside the browser sandbox. Microsoft’s Security Update Guide now tracks the issue for downstream visibility, which matters because Edge inherits Chromium fixes through the normal upstream-to-downstream pipeline gleblog.com]
CVE-2026-6318 fits an increasingly familiar pattern in Chromium security: a bug in a core browser subsystem, a coordinated upstream fix, and a fast downstream propagation story for products that embed Chromium. Google’s April 15, 2026 stable-channel update explicitly identifies the issue as “Use after free in Codecs” and links it to the release that closed the hole, Chrome 147.0.7727.101/102 on desktop. Microsoft’s advisory mirrors that upstream record see whether the vulnerability still applies to their Edge builds
The most important detail is that the bug lives in Codecs, not in a fringe component that only specialists ever touch. Browser codec paths are deeply embedded in modern web usage: video playback, media previews, conferencing, streaming, ad delivery, and content rendering all lean on the same broad media stack. That means a memory corruption flaw in this area is not a niche defect, even if the vendor labels it Medium severity in Chromium’s own internal taxonomy
The description also matters because it frames the attack as remote and page-driven. A victim does not need to install a helper app or open a local file; they only need to load a crafted HTML page. That is exactly why browser bugs retain such high operational significance even when they are not scored as “Critical” by the vendor. If a page can reliably drive the browser into a use-after-free, the attacker is already inside the most common software path on the machine
What makes this especially notable in 2026 is the cadence. Chrome 147 arrived as the stable desktop line on April 7, and Google issued the follow-up security update on April 15 with a long list of fixes, including multiple use-after-free bugs across different components. That rapid patch rhythm is now the norm for Chromium, but it also tells us something uncomfortable: the browser engine remains a high-value target with a steady stream of exploitable memory issues that need constant triage
Use-after-free flaws are especially important in browser code because they often appear when an object’s lifetime is mismanaged across asynchronous callbacks, media state changes, or cleanup paths. In a media stack, that can happen when a stream is paused, a frame is replaced, a renderer is torn down, or a page triggers an edge-case sequence that the code did not expect. The vulnerability class itself is not new, but its persistence in Chromium shows how hard it is to eliminate lifetime bugs in large, multi-process codebases.
Google’s own release note for the fix gives the issue a clear CVE and a straightforward description, but it also carries an implicit warning: the fix was held back in detail until a majority of users had been updated. That is standard vendor practice, and it exists for a reason. When a bug is still being rolled out, publishing too much exploit detail too early can hand adversaries a ready-made roadmap before the patch is widely deployed
The Microsoft Security Update Guide adds a second layer of practical context. Microsoft has spent years using the SUG to tell Edge customers when a Chromium CVE has been absorbed into Microsoft’s downstream browser builds. That makes the entry less about originating the flaw and more about operational confirmation: has the fix made it from upstream Chromium into the browser Windows users actually run? Microsoft’s own guidance on the SUG explains that the guide is intended as a unified and authoritative source for current public security-update information, including issues assigned by industry partners such as Chrome
A codec bug is dangerous for a simple reason: media code often runs automatically. Users do not always consciously “open” media content; the browser may load it as part of a page render, embedded preview, or autoplay sequence. That gives attackers a path that is both technically deep and psychologically shallow. The victim may think they are just browsing a page, while the browser is negotiating a complex decoder state machine.
This is why browser vendors still treat memory corruption as serious even when sandboxing is in place. The sandbox changes the blast radius, but it does not erase the exploit primitive. In practice, it just forces adversaries to do more work or chain more bugs.
That is important because browser exploitation often depends on reliability, not just theoretical memory corruption. A use-after-free in a codec path may be difficult to turn into full arbitrary code execution in the wild, but the danger is that browser exploit developers only need one reliable path. Once a page can trigger the condition consistently, attackers can spend the rest of their time refining the post-corruption steps.
Google’s public language also hints at why the issue was rated Medium in Chromium terms rather than being called out as a worst-case browser takeover bug. A use-after-free can be severe without always being trivially weaponizable. The vendor’s severity label should not be mistaken for a dismissal; it is better read as important, but not the single most catastrophic issue in the release train
The good news is that this is not the same thing as instant full-system compromise. The bad news is that modern browser exploit kits are built precisely to capitalize on these intermediate footholds. A sandboxed code execution bug can still be enough to steal cookies, session tokens, or other data if the attacker can pair it with additional techniques.
For defenders, UI:R should never be read as “low risk.” It often just means the attacker needs a clickable path, which is exactly how most real-world browser attacks start anyway. The difference is that this vulnerability does not require a local helper app or special privileges to reach the vulnerable code.
Versioning matters because browser security is now a release-management problem as much as it is a code problem. If an enterprise is two patch trains behind, it may still be exposed even after the upstream vendor has already disclosed and fixed the bug. That is why administrators increasingly track browser versions the same way they track OS cumulative updates.
The Google release note also says the update would roll out over the coming days/weeks, which means exposure does not disappear at the moment the advisory is posted. That lag is critical. Attackers know that patch publication and patch adoption are not the same event, and they often race the window between them.
In practice, administrators should treat the version number as the first verification step, not the only one. A device that reports Chrome 147.0.7727.101 or later is materially safer with respect to this CVE, but patch compliance is only one layer. Policy enforcement, extension hygiene, and safe-browsing controls remain relevant because browser exploitation rarely happens in isolation.
They also reduce thevlike “update your browser.” In a high-volume environment, that is not operationally precise enough. Version-specific guidance is how patch teams turn an abstract CVE into a concrete remediation task.
Because Edge is Chromium-based, Microsoft routinely inherits and republishes upstream Chromium CVEs for customer awareness. We have seen the same pattern across many recent browser vulnerabilities: Google publishes the primary fix, and Microsoft records the issue so that Windows administrators can map it to their own rollout cadence. That is a practical bridge between upstream engineering and enterprise deployment realities
This matters because enterprises do not run browsers in a vacuum. They run them in fleets, often with update deferrals, pilot rings, and compatibility exceptions. A Chromium CVE may be fixed upstream, but if Edge has not yet ingested the relevant branch or the organization has paused updates, exposure can persist longer than users expect.
This is one reason the Security Update Guide has become such an important artifact for enterprise defenders. Microsoft says it is intended as a unified and authoritative source for public security-update information, including issues assigned by external CNAs like Chrome. In practice, that makes it the place where downstream exposure becomes visible in Microsoft-centric environments
That means browser CVEs often have a sharper enterprise tail than their consumer-facing description suggests. A single outdated build on a high-trust workstation can be enough to create a foothold for credential theft or internal reconnaissance.
The recurring lesson is that large, mature browser engines are still very much living systems. They inherit old complexity, new features, multiple process boundaries, and a huge compatibility burden. Each of those layers adds opportunities for lifetime bugs, and codecs are especially vulnerable because the code has to juggle object lifetimes across asynchronous playback events.
That is why a use-after-free in Codecs still draws immediate attention even when the label says Medium. A bug in a high-value attack surface that can be triggered remotely through a web page is not a minor maintenance issue. It is a strategic security event.
The result is that exploit mitigation becomes a layered game. Vendors rely on fuzzing, sanitizers, code review, sandboxing, and rapid updates. That model works, but only if the update ecosystem is fast enough to outrun attackers.
That disclosure is more than boilerplate. It reflects the reality that many browser security issues are now found by automated instrumentation before public exploitation occurs. The challenge is that the same complexity that makes Chrome heavily fuzzed also creates an endless stream of subtle lifetime mistakes.
From an operational standpoint, browser patching should be treated like a security baseline, not an optional convenience update. Chrome and Edge are not just productivity tools; they are execution environments for untrusted content. That reality deserves the same seriousness as patching a mail client or document viewer.
These assumptions are how attackers win the update race. Browser security is a moving target, and the CVE record is only the beginning of the story.
The second thing to watch is whether this bug becomes part of a broader exploitation chain. Single-browser-process RCE is valuable on its own, but attackers often want a combined path that starts with a page and ends with data access or persistence. A codec use-after-free is exactly the kind of bug that can serve as a link in that chain.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 Overview
Overview
CVE-2026-6318 fits an increasingly familiar pattern in Chromium security: a bug in a core browser subsystem, a coordinated upstream fix, and a fast downstream propagation story for products that embed Chromium. Google’s April 15, 2026 stable-channel update explicitly identifies the issue as “Use after free in Codecs” and links it to the release that closed the hole, Chrome 147.0.7727.101/102 on desktop. Microsoft’s advisory mirrors that upstream record see whether the vulnerability still applies to their Edge buildsThe most important detail is that the bug lives in Codecs, not in a fringe component that only specialists ever touch. Browser codec paths are deeply embedded in modern web usage: video playback, media previews, conferencing, streaming, ad delivery, and content rendering all lean on the same broad media stack. That means a memory corruption flaw in this area is not a niche defect, even if the vendor labels it Medium severity in Chromium’s own internal taxonomy
The description also matters because it frames the attack as remote and page-driven. A victim does not need to install a helper app or open a local file; they only need to load a crafted HTML page. That is exactly why browser bugs retain such high operational significance even when they are not scored as “Critical” by the vendor. If a page can reliably drive the browser into a use-after-free, the attacker is already inside the most common software path on the machine
What makes this especially notable in 2026 is the cadence. Chrome 147 arrived as the stable desktop line on April 7, and Google issued the follow-up security update on April 15 with a long list of fixes, including multiple use-after-free bugs across different components. That rapid patch rhythm is now the norm for Chromium, but it also tells us something uncomfortable: the browser engine remains a high-value target with a steady stream of exploitable memory issues that need constant triage
Background
Chromium’s media pipeline has always been security-sensitive because it sits at the intersection of untrusted input and complex state. A codec parser or decoder is not just taking bytes and drawing pixels; it is negotiating timing, buffers, references, and format expectations while trying to stay performant enough for real-time playback. That combination makes Codecs one of the most dangerous places to carry legacy C++ memory management mistakes into a modern browser engine.Use-after-free flaws are especially important in browser code because they often appear when an object’s lifetime is mismanaged across asynchronous callbacks, media state changes, or cleanup paths. In a media stack, that can happen when a stream is paused, a frame is replaced, a renderer is torn down, or a page triggers an edge-case sequence that the code did not expect. The vulnerability class itself is not new, but its persistence in Chromium shows how hard it is to eliminate lifetime bugs in large, multi-process codebases.
Google’s own release note for the fix gives the issue a clear CVE and a straightforward description, but it also carries an implicit warning: the fix was held back in detail until a majority of users had been updated. That is standard vendor practice, and it exists for a reason. When a bug is still being rolled out, publishing too much exploit detail too early can hand adversaries a ready-made roadmap before the patch is widely deployed
The Microsoft Security Update Guide adds a second layer of practical context. Microsoft has spent years using the SUG to tell Edge customers when a Chromium CVE has been absorbed into Microsoft’s downstream browser builds. That makes the entry less about originating the flaw and more about operational confirmation: has the fix made it from upstream Chromium into the browser Windows users actually run? Microsoft’s own guidance on the SUG explains that the guide is intended as a unified and authoritative source for current public security-update information, including issues assigned by industry partners such as Chrome
Why codecs are such a pressure point
The media subsystem is a broad attack surface because it is designed to be permissive. Browsers must play old files, live streams, weird ad assets, and modern web formats without punishing users for visiting ordinary sites. That breadth is useful for compatibility, but it also means the code must continuously interpret untrusted structure and state transitions.A codec bug is dangerous for a simple reason: media code often runs automatically. Users do not always consciously “open” media content; the browser may load it as part of a page render, embedded preview, or autoplay sequence. That gives attackers a path that is both technically deep and psychologically shallow. The victim may think they are just browsing a page, while the browser is negotiating a complex decoder state machine.
Why browser sandboxing does not make it harmless
Google’s wording says the attack could execute code inside a sandbox, which is significant but not reassuring. A sandbox is a containment boundary, not a guarantee of safety. If an attacker gets code execution in the renderer or media sandbox, the next question is whether they can chain it with another bug to escape or to pivot into data theft, credential harvesting, or session hijacking.This is why browser vendors still treat memory corruption as serious even when sandboxing is in place. The sandbox changes the blast radius, but it does not erase the exploit primitive. In practice, it just forces adversaries to do more work or chain more bugs.
Exploitability and Attack Surface
The public description indicates that a remote attacker could exploit the flaw through a crafted HTML page. That puts the vulnerability squarely in the class of drive-by browser bugs that administrators care about the most. The attacker’s entry point is not an internal workflow, and the victim’s only necessary action is opening the page or being redirected to it.That is important because browser exploitation often depends on reliability, not just theoretical memory corruption. A use-after-free in a codec path may be difficult to turn into full arbitrary code execution in the wild, but the danger is that browser exploit developers only need one reliable path. Once a page can trigger the condition consistently, attackers can spend the rest of their time refining the post-corruption steps.
Google’s public language also hints at why the issue was rated Medium in Chromium terms rather than being called out as a worst-case browser takeover bug. A use-after-free can be severe without always being trivially weaponizable. The vendor’s severity label should not be mistaken for a dismissal; it is better read as important, but not the single most catastrophic issue in the release train
The real-world attack chain
In practical terms, exploitation usually depends on a chain rather than a single bug. A malicious page might trigger the codec flaw, use it to achieve code execution in the sandboxed process, and then try to exfiltrate data or exploit another browser weakness. The page could arrive through a phishing link, a malvertising redirect, a compromised site, or a booby-trapped embed in an otherwise legitimate page.The good news is that this is not the same thing as instant full-system compromise. The bad news is that modern browser exploit kits are built precisely to capitalize on these intermediate footholds. A sandboxed code execution bug can still be enough to steal cookies, session tokens, or other data if the attacker can pair it with additional techniques.
Why user interaction still matters
The Chromium record and Microsoft’s tracking entry both imply a user-driven path rather than a silent background exploit. That usually means the attacker must convince someone to visit the page, or must find a route to make the victim’s browser render malicious content. This reduces reach, but only modestly.For defenders, UI:R should never be read as “low risk.” It often just means the attacker needs a clickable path, which is exactly how most real-world browser attacks start anyway. The difference is that this vulnerability does not require a local helper app or special privileges to reach the vulnerable code.
- Remote delivery through a crafted webpage is enough.
- A victim can be targeted through normal browsing behavior.
- The sandbox lowers the immediate blast radius, but not the initial compromise path.
- The bug is dangerous because codec paths are deeply integrated into page rendering.
- Attack success depends on exploitability, not on whether the user is locally authenticated.
Patch Timing and Versioning
The remediation threshold is clear: Chrome prior to 147.0.7727.101 is affected, while the fixed build begins at that version. Google’s stable update post of April 15, 2026 explicitly associates CVE-2026-6318 with that release line, and it notes that the patch was part of a broader security update containing 31 fixes. In other words, this was not a one-off patch but part of a routine security cycle that bundled multiple memory-safety problems at onceVersioning matters because browser security is now a release-management problem as much as it is a code problem. If an enterprise is two patch trains behind, it may still be exposed even after the upstream vendor has already disclosed and fixed the bug. That is why administrators increasingly track browser versions the same way they track OS cumulative updates.
The Google release note also says the update would roll out over the coming days/weeks, which means exposure does not disappear at the moment the advisory is posted. That lag is critical. Attackers know that patch publication and patch adoption are not the same event, and they often race the window between them.
What the fixed version means for administrators
For IT teams, the practical question is not whether Google published a fix, but whether every endpoint has the fixed Chromium build. That includes managed Chrome installations, unmanaged personal browsers on corporate devices, and downstream browsers that share the engine. The Microsoft Security Update Guide exists partly to make that downstream visibility easier for Windows shopsIn practice, administrators should treat the version number as the first verification step, not the only one. A device that reports Chrome 147.0.7727.101 or later is materially safer with respect to this CVE, but patch compliance is only one layer. Policy enforcement, extension hygiene, and safe-browsing controls remain relevant because browser exploitation rarely happens in isolation.
Why version thresholds are so useful
Version thresholds cut through a lot of noise. They tell security teams exactly where to start inventory checks, and they let incident responders separate currently vulnerable systems from already-patched ones. That is especially valuable in a browser ecosystem where a single engine can exist in multiple brands and delivery channels.They also reduce thevlike “update your browser.” In a high-volume environment, that is not operationally precise enough. Version-specific guidance is how patch teams turn an abstract CVE into a concrete remediation task.
Microsoft Edge and Downstream Exposure
Microsoft’s inclusion of the issue in the Security Update Guide is not an announcement that Edge invented or independently fixed the bug. It is a downstream tracking mechanism that tells customers when the Chromium fix has landed in Edge and whether their installed builds are still vulnerable. That distinction is crucial for understanding the broader browser ecosystem in 2026Because Edge is Chromium-based, Microsoft routinely inherits and republishes upstream Chromium CVEs for customer awareness. We have seen the same pattern across many recent browser vulnerabilities: Google publishes the primary fix, and Microsoft records the issue so that Windows administrators can map it to their own rollout cadence. That is a practical bridge between upstream engineering and enterprise deployment realities
This matters because enterprises do not run browsers in a vacuum. They run them in fleets, often with update deferrals, pilot rings, and compatibility exceptions. A Chromium CVE may be fixed upstream, but if Edge has not yet ingested the relevant branch or the organization has paused updates, exposure can persist longer than users expect.
Why Edge tracking changes the admin workflow
For Windows administrators, a Microsoft advisory is often more actionable than a Google blog post because it lives in the same inventory and compliance world as the rest of Microsoft security guidance. That does not make Google’s update less authoritative; it just makes Microsoft’s presentation easier to fold into patch dashboards and change-management reports.This is one reason the Security Update Guide has become such an important artifact for enterprise defenders. Microsoft says it is intended as a unified and authoritative source for public security-update information, including issues assigned by external CNAs like Chrome. In practice, that makes it the place where downstream exposure becomes visible in Microsoft-centric environments
Consumer versus enterprise impact
For consumers, the primary risk is opportunistic exploitation through malicious links, compromised sites, or ad-driven redirects. For enterprises, the risk is broader and often less visible. Employees may not realize they are running an outdated browser build, and managed endpoints may lag because of staged deployment policies or application-compatibility concerns.That means browser CVEs often have a sharper enterprise tail than their consumer-facing description suggests. A single outdated build on a high-trust workstation can be enough to create a foothold for credential theft or internal reconnaissance.
- Edge customers need to verify downstream update status.
- Microsoft’s advisory is a tracking tool, not the original fix notice.
- Patch deferral can extend exposure even after the upstream fix exists.
- Consumer risk is more opportunistic; enterprise risk is more operational.
- Inventory accuracy is the difference between presumed and actual protection.
What the Bug Tells Us About Chromium Security
CVE-2026-6318 is not an outlier; it is part of a broader pattern in Chromium where memory corruption still shows up in the most performance-sensitive paths. That is especially true in the browser’s media stack, graphics stack, and other code that must process large volumes of untrusted content at speed. The fact that Google’s April 15 release included multiple memory-safety fixes alongside this one underscores how active the bug-finding pipeline remainsThe recurring lesson is that large, mature browser engines are still very much living systems. They inherit old complexity, new features, multiple process boundaries, and a huge compatibility burden. Each of those layers adds opportunities for lifetime bugs, and codecs are especially vulnerable because the code has to juggle object lifetimes across asynchronous playback events.
Memory safety is still the browser’s central problem
The browser industry has spent years hardening sandboxing, site isolation, and process separation. Those are all important, but they do not eliminate the base problem: unsafe memory handling in C++ code can still yield serious bugs. The industry has made progress, but it has not reached the point where memory corruption is rare enough to ignore.That is why a use-after-free in Codecs still draws immediate attention even when the label says Medium. A bug in a high-value attack surface that can be triggered remotely through a web page is not a minor maintenance issue. It is a strategic security event.
Why media bugs are hard to eradicate
Media processing code has to balance correctness, compatibility, and performance. If developers tighten validation too aggressively, they risk breaking legitimate content; if they relax it, they risk leaving dangerous edge cases open. That tension makes codec code notoriously difficult to harden completely.The result is that exploit mitigation becomes a layered game. Vendors rely on fuzzing, sanitizers, code review, sandboxing, and rapid updates. That model works, but only if the update ecosystem is fast enough to outrun attackers.
The role of fuzzing and sanitizers
Google’s release note explicitly acknowledges the value of tools like AddressSanitizer, MemorySanitizer, UndefinedBehaviorSanitizer, Control Flow Integrity, libFuzzer, and AFL in surfacing browser bugs before they ship to stable usersThat disclosure is more than boilerplate. It reflects the reality that many browser security issues are now found by automated instrumentation before public exploitation occurs. The challenge is that the same complexity that makes Chrome heavily fuzzed also creates an endless stream of subtle lifetime mistakes.
Operational Guidance for Windows Users
The immediate action item is simple: make sure Chrome is updated to 147.0.7727.101 or later on affected desktop systems, and verify that any Chromium-based browsers in your environment have received the corresponding upstream fix. For Edge environments, the Microsoft Security Update Guide is the obvious place to confirm whether the downstream browser has inherited the patchFrom an operational standpoint, browser patching should be treated like a security baseline, not an optional convenience update. Chrome and Edge are not just productivity tools; they are execution environments for untrusted content. That reality deserves the same seriousness as patching a mail client or document viewer.
Practical steps for defenders
- Inventory browser versions across managed endpoints and shared workstations.
- Prioritize rapid deployment for systems used by administrators, developers, and finance staff.
- Check downstream products that embed Chromium, not just Google Chrome itself.
- Review web filtering and phishing controls to reduce exposure to crafted pages.
- Audit long-patch-delay devices such as kiosks, VDI images, and shared lab systems.
- Monitor for crash telemetry if your environment has browser diagnostics turned on.
What users should not assume
Users should not assume that “sandboxed” means “safe enough to ignore.” They should not assume that a Medium label means the issue is trivial. And they should not assume that a Chrome fix automatically protects every Chromium-based browser on the same day.These assumptions are how attackers win the update race. Browser security is a moving target, and the CVE record is only the beginning of the story.
Strengths and Opportunities
The best news in this disclosure is that the issue was patched quickly and clearly, with a precise version threshold and a corresponding downstream tracking record. That makes life easier for defenders and reduces the ambiguity that often surrounds browser CVEs. It also reinforces the value of the Chromium release process, which continues to catch and ship fixes at a remarkable pace.- Clear fixed version: Chrome 147.0.7727.101 gives admins an exact remediation target.
- Rapid upstream response: Google disclosed and patched the issue in the same stable cycle.
- Downstream visibility: Microsoft’s advisory helps Edge customers map exposure.
- Strong containment: The sandbox limits immediate blast radius.
- Better tooling: Fuzzing and sanitizers continue to surface bugs before mass exploitation.
- Operational clarity: The bug is easy to classify as a browser-update priority.
- Enterprise relevance: The advisory fits neatly into standard patch governance workflows.
Risks and Concerns
The concerns are equally clear: this is a remotely reachable browser memory-safety bug in a high-use subsystem, and those are exactly the sorts of flaws attackers like to weaponize. Even with sandboxing, a successful exploit can create a foothold for credential theft, content injection, or chaining with another browser weakness. The patch exists, but the rollout window is still a real exposure window.- Drive-by attack potential: A crafted HTML page is enough to trigger the issue.
- Memory corruption risk: Use-after-free bugs remain highly exploitable in practice.
- Sandbox is not immunity: Containment reduces damage but does not eliminate compromise.
- Patch lag: Real-world deployment often trails vendor disclosure.
- Downstream uncertainty: Chromium-based browsers may update on different schedules.
- User behavior: Phishing, redirects, and malvertising can deliver the malicious page.
- Operational blind spots: Unmanaged or forgotten devices can remain exposed.
Looking Ahead
The most important thing to watch now is how quickly Chrome and Chromium-based browsers converge on the fixed code across desktop fleets. The advisory history suggests that the industry has become better at this than it was a few years ago, but browser patch latency still creates a meaningful exposure window. For security teams, the next few days are about confirming adoption, not admiring the release note.The second thing to watch is whether this bug becomes part of a broader exploitation chain. Single-browser-process RCE is valuable on its own, but attackers often want a combined path that starts with a page and ends with data access or persistence. A codec use-after-free is exactly the kind of bug that can serve as a link in that chain.
- Confirm every Chrome installation is at 147.0.7727.101 or later.
- Verify Edge’s downstream Chromium build status through Microsoft guidance.
- Watch for any sign of exploitation against media-heavy web content.
- Treat high-value workstations as priority targets for immediate patching.
- Keep browser crash telemetry and anomaly detection enabled where possible.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
Last edited: