 NSA GRASSMARLIN Vulnerability Brief — CVE-2026-6807
NSA GRASSMARLIN Vulnerability Brief — CVE-2026-6807
Executive summary
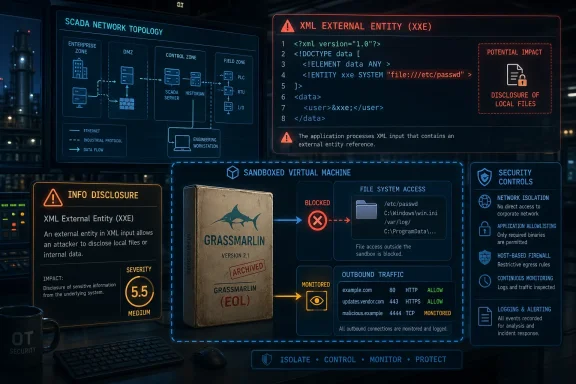
CISA has published ICS Advisory ICSA-26-118-01 for NSA GRASSMARLIN, identifying CVE-2026-6807, a medium-severity information-disclosure vulnerability tied to improper handling of XML input. The vulnerability is classified as CWE-611: Improper Restriction of XML External Entity Reference, commonly associated with XML External Entity, or XXE, weaknesses.According to the advisory text you provided, successful exploitation could allow an attacker to disclose sensitive information. The reported CVSS v3.1 score is 5.5 Medium, with the vector:
CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:NThe key operational issue is that NSA GRASSMARLIN is end-of-life. NSA has indicated that the project has been unsupported since 2017, is archived, and will not receive patches or future updates. The public GitHub repository also identifies GRASSMARLIN v3.2.1 as the latest release from June 27, 2017, and shows the repository as archived/read-only.
What is GRASSMARLIN?
GRASSMARLIN is an open-source passive network-mapping tool developed by the NSA for industrial control system and SCADA environments. Its purpose is to help defenders visualize ICS/SCADA network topology, identify devices, and understand communications without actively probing sensitive operational technology networks. NIST describes GRASSMARLIN as an open-source passive network mapper for industrial networks that provides a snapshot of devices, communications, and metadata extracted from network traffic.That passive design matters in OT environments because active scanning can disrupt fragile or safety-critical systems. Tools like GRASSMARLIN are often used with packet captures to build situational awareness while reducing the risk of interfering with controllers, sensors, gateways, HMIs, and other ICS assets.
Vulnerability details
CVE
CVE-2026-6807Affected product
NSA GRASSMARLINAffected versions
The advisory lists:GRASSMARLIN vers:all/*The vulnerability description specifically mentions GRASSMARLIN v3.2.1, but the affected-product entry indicates all versions are considered affected.
Weakness type
CWE-611: Improper Restriction of XML External Entity ReferenceCWE-611 covers software that processes XML documents containing entities that resolve to resources outside the intended control boundary. MITRE notes that this weakness can allow attackers to read application data, read files or directories, and in some cases cause a vulnerable application to make unintended outbound requests.
Impact
The advisory states that crafted session data can trigger improper handling of XML input, potentially resulting in unintended exposure of sensitive information.In practical terms, the risk depends on how GRASSMARLIN is used and what files, captures, session data, or system resources are available to the process parsing the XML. Because the CVSS vector is local attack vector and low privileges required, this is not presented as a remote unauthenticated internet-facing vulnerability. However, it still matters in environments where analysts exchange session files, load externally supplied project/session data, or run the tool on systems containing sensitive OT network information.
Why XXE matters here
XML External Entity vulnerabilities occur when an XML parser accepts untrusted XML and permits features such as external entities, DTDs, or external document references. OWASP’s XXE guidance recommends disabling DTDs and external entities as the safest prevention pattern, because weak XML parser configuration can lead to file disclosure, SSRF-style behavior, port scanning from the parsing host, or denial-of-service conditions.For GRASSMARLIN, the advisory’s concern is information disclosure from crafted session data. That suggests the most relevant scenario is not someone attacking a live ICS device directly, but rather someone supplying a malicious or manipulated GRASSMARLIN-related file that is later opened by an analyst or engineer.
Risk assessment
This vulnerability is rated Medium, but the operational risk may be higher in specific environments.Organizations should pay close attention if they:
- Still use GRASSMARLIN in OT/ICS assessment workflows.
- Store sensitive network maps, host metadata, or packet-derived information in GRASSMARLIN session files.
- Share GRASSMARLIN project/session files between teams, vendors, contractors, or third parties.
- Run GRASSMARLIN on analyst workstations that also contain sensitive credentials, reports, packet captures, or access to internal OT documentation.
- Use legacy tools without sandboxing or strict file-handling controls.
Recommended actions
1. Identify whether GRASSMARLIN is still in use
Search analyst workstations, OT security toolkits, lab systems, jump boxes, and shared engineering environments for GRASSMARLIN installations, downloaded releases, scripts, shortcuts, and historical project files.Look for:
- GRASSMARLIN binaries or Java archives.
- Old installation folders.
- Session/project files.
- Documentation or workflows that reference GRASSMARLIN.
- Archived VM images containing OT assessment tools.
2. Treat GRASSMARLIN session data as untrusted input
Do not open GRASSMARLIN session files from unknown, external, or untrusted sources. If legacy files must be reviewed, handle them as potentially malicious.Recommended precautions include:
- Open files only in a disposable VM or sandbox.
- Remove internet access from the analysis VM.
- Prevent access to sensitive local directories.
- Use a non-privileged account.
- Do not run the tool from a system that has OT credentials or privileged network access.
- Snapshot and revert the VM after analysis.
3. Retire the tool where possible
Because the project is end-of-life and no patch is expected, the safest long-term action is to remove GRASSMARLIN from production and assessment workflows.If passive OT visibility is still required, evaluate actively maintained alternatives that support:
- Passive asset discovery.
- ICS protocol awareness.
- Secure import/export handling.
- Vendor support.
- Regular security updates.
- Role-based access controls.
- Integration with SOC or OT monitoring platforms.
4. Restrict file exchange workflows
If teams continue to use archived GRASSMARLIN outputs for historical reasons, establish strict controls around file handling.Recommended controls:
- Only accept files from trusted internal sources.
- Require malware scanning before opening.
- Store legacy files in read-only repositories.
- Document provenance for imported session data.
- Avoid email-based exchange of project/session files.
- Use controlled transfer mechanisms with logging.
- Block execution or parsing of files from unmanaged removable media.
5. Isolate legacy analysis environments
If GRASSMARLIN must be used temporarily, run it in a dedicated legacy-analysis environment.That environment should be:
- Segmented from production IT and OT networks.
- Denied direct internet access.
- Denied access to sensitive file shares.
- Non-persistent where possible.
- Monitored for unexpected outbound connection attempts.
- Rebuilt or reverted after use.
6. Review exposed sensitive information
Because the vulnerability could disclose sensitive information, organizations should review what information may be present on systems where GRASSMARLIN is run.Examples include:
- Packet captures.
- OT network diagrams.
- Device inventories.
- IP addressing schemes.
- Engineering notes.
- Credentials or credential-like artifacts.
- VPN profiles.
- Remote access configuration files.
- Reports containing site names, vendor details, or asset criticality.
7. Follow CISA’s general ICS defensive guidance
The advisory recommends minimizing network exposure for control system devices, ensuring they are not accessible from the internet, placing control system networks and remote devices behind firewalls, and isolating OT networks from business networks. It also recommends using secure remote access methods such as VPNs while recognizing that VPNs themselves require maintenance and patching.These are broad but important compensating controls, especially when unsupported tools remain in an environment.
Detection and monitoring considerations
There may not be a simple network signature for this issue, especially if exploitation occurs locally when a crafted session file is opened. However, defenders can monitor for suspicious behavior from systems used for GRASSMARLIN analysis.Watch for:
- Unexpected outbound HTTP, HTTPS, SMB, LDAP, or DNS requests after opening a session file.
- Attempts by Java or the GRASSMARLIN process to access sensitive local files.
- Unusual file reads from directories unrelated to the analysis task.
- Connections from an analysis workstation to internal services it does not normally contact.
- Newly created files or logs after opening suspicious project/session data.
- Alerts involving XML entity expansion, DTD loading, or suspicious XML parser behavior.
Practical mitigation checklist
| Priority | Action |
|---|---|
| High | Determine whether GRASSMARLIN is installed or still used. |
| High | Stop opening untrusted GRASSMARLIN session/project files. |
| High | Remove GRASSMARLIN from production workflows where possible. |
| High | If use is unavoidable, run it only in an isolated VM or sandbox. |
| Medium | Restrict access to historical GRASSMARLIN files and outputs. |
| Medium | Monitor Java/GRASSMARLIN processes for unexpected file and network activity. |
| Medium | Review analyst systems for sensitive files that could be exposed. |
| Low | Document the tool as unsupported and track replacement plans. |
Bottom line
CVE-2026-6807 is not a high-severity remote code execution issue, but it is still important because GRASSMARLIN is unsupported and no patch is expected. The main concern is the handling of crafted session/XML data that could expose sensitive information from systems used to analyze OT/ICS environments.Organizations should treat this advisory as a prompt to find and retire lingering GRASSMARLIN deployments. Where the tool must be retained for historical or compatibility reasons, it should be isolated, sandboxed, and prevented from accessing sensitive local files or networks.
Source: CISA NSA GRASSMARLIN | CISA