Google and Microsoft disclosed CVE-2026-7358 on April 28, 2026, as a high-severity use-after-free flaw in Chrome’s Animation component affecting Google Chrome before version 147.0.7727.138, with exploitation possible through a crafted HTML page that can execute code inside Chrome’s sandbox. The bug is not the largest item in this week’s Chrome security rollup, but it is the kind that should make Windows admins move quickly rather than wait for the browser’s normal update rhythm. The uncomfortable truth is that modern browser security is now less about whether one CVE sounds spectacular and more about how fast organizations can drain vulnerable builds from fleets that live permanently on the Internet.
CVE-2026-7358 is, on paper, a familiar Chrome vulnerability: a memory-safety bug, categorized as CWE-416, in a browser subsystem that handles animation. The stated attack path is equally familiar. A remote attacker gets a user to open a malicious HTML page, and Chrome before 147.0.7727.138 can be pushed into arbitrary code execution inside the sandbox.
That “inside a sandbox” phrase is doing important work. It does not mean the bug is harmless, and it does not mean the attacker owns the whole machine by default. It means the first stage lands in Chrome’s constrained renderer environment, where attackers typically need a second vulnerability or a separate escape technique to reach the operating system with broader privileges.
But in 2026, that caveat is comfort only in the narrowest sense. Browsers are credential vaults, application runtimes, identity brokers, password managers, PDF readers, WebAuthn front ends, corporate SaaS launchers, and sometimes the only “desktop” an employee meaningfully uses. Code execution in the browser process boundary is not a theoretical inconvenience. It is the first half of many serious compromises.
CVE-2026-7358 sits in that larger pattern. It was reported by Google on March 25, carried a Chromium severity of High, and appeared publicly as part of the late-April stable-channel update. NVD published the entry on April 28 and modified it on April 30, with CISA-ADP assigning a CVSS 3.1 score of 8.8: network attack vector, low attack complexity, no privileges required, user interaction required, and high impact to confidentiality, integrity, and availability.
That score is useful but incomplete. CVSS treats user interaction as a mitigating factor, but the web is built out of user interaction. Clicking a link, opening a tab, previewing a document, visiting a compromised site, following a redirect chain, or hitting a malicious ad slot are all normal behaviors. In a browser vulnerability, “user interaction required” often means “the victim used the web.”
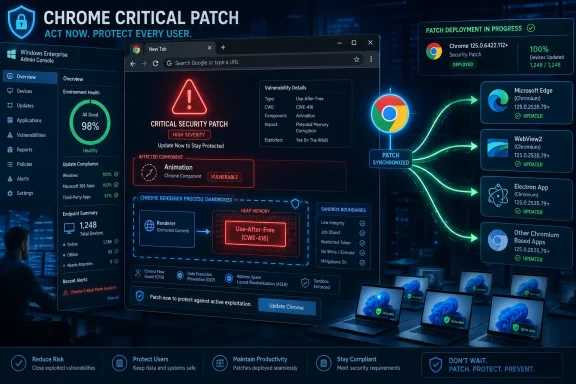
The practical fix is not complicated. Chrome needs to be at or beyond the fixed build on affected platforms, and Chromium-based browsers need their own vendor updates once they ingest the upstream patch. The operational problem is proving that this has happened everywhere: laptops asleep during maintenance windows, VDI images lagging behind, kiosks pinned to old builds, unmanaged developer machines, and third-party app bundles carrying embedded Chromium runtimes.
Animation is an especially plausible neighborhood for this kind of bug. Modern web animation is not merely decorative; it touches layout, compositing, GPU acceleration, timing, scripting, frame lifecycle, and DOM state. A malicious page can often manipulate those moving parts with precision, trying to force the browser into an unexpected sequence: create an object, detach it, free it, then cause stale code to reference it again.
That is why memory-safety bugs in browsers are so stubborn. The web platform is an adversarial programming interface exposed to every site on Earth. Browser vendors are not just building software; they are building a machine that accepts hostile input all day and still has to render a banking site, a Teams call, a WebGL dashboard, and a sketchy coupon popup without falling over.
Google has invested heavily in fuzzing, sanitizers, sandboxing, exploit mitigations, site isolation, and safer coding patterns. The April 28 release itself credits tools such as AddressSanitizer, MemorySanitizer, UndefinedBehaviorSanitizer, Control Flow Integrity, libFuzzer, and AFL for finding many classes of bugs before they become disasters. Yet the release also shows how much vulnerable surface remains. When one stable update includes 30 security fixes and a parade of memory corruption issues, the lesson is not that Chrome security is failing. The lesson is that the browser is one of the most aggressively tested pieces of software in the world because it has to be.
That shared Chromium foundation is one of the great engineering bargains of the modern web. Microsoft no longer maintains a fully separate browser engine for Edge; instead, it contributes to and consumes Chromium, gaining compatibility and velocity. Developers get fewer browser-specific surprises. Users get a modern engine with broad standards support.
The tradeoff is synchronized risk. A serious Chromium flaw becomes a multi-vendor coordination problem. Google Chrome, Microsoft Edge, Brave, Vivaldi, Opera, Electron apps, embedded WebViews, and Linux distribution Chromium packages do not all update at exactly the same moment or through the same management channel. The browser monoculture concern is no longer theoretical; it is visible every time one upstream CVE fans out across desktop fleets.
For Windows admins, that means patch status cannot stop at “Chrome updated.” Edge Stable, Edge Extended Stable, WebView2 Runtime, packaged browsers in app stores, and third-party software that embeds Chromium all deserve attention. The first vendor to ship the fix is not the same thing as the last vulnerable copy disappearing from the environment.
For CVE-2026-7358, the key Chrome line is prior to 147.0.7727.138, with Google’s April 28 desktop release using 147.0.7727.137/138 for Windows and macOS and 147.0.7727.137 for Linux. That small platform variation is exactly why vulnerability management systems sometimes become noisy or misleading. A scanner may flag “less than .138” while a Linux channel legitimately shows .137 from the vendor’s stable release. Another tool may wait for NVD enrichment before producing a clean CPE match. A third may conflate Chrome and Chromium packages.
NVD’s change history is a good example of the machinery behind the scenes. The CVE arrived from Chrome on April 28, received CISA-ADP scoring on April 29, and gained NIST CPE configuration data on April 30. That delay is normal, but normal is not the same as operationally harmless. If your patch process waits for every database to converge, you are letting metadata latency dictate exposure time.
The better approach is to treat the vendor release as the starting gun. Once Google says a stable build fixes high-severity memory corruption in the browser, the enterprise question becomes deployment verification, not advisory interpretation. Version inventory, browser restart enforcement, and update-channel health matter more than another hour spent debating whether a CPE string has settled.
But the sandbox should be understood as damage containment, not immunity. Attackers chain vulnerabilities. They pair renderer execution with sandbox escapes, kernel bugs, GPU driver flaws, broker-process weaknesses, credential theft, token abuse, extension compromise, and social-engineering steps. A high-severity renderer bug is often valuable precisely because it gives the attacker a foothold in a highly privileged user context: the authenticated browser session.
This is especially relevant in enterprise Windows environments. The browser is where SSO cookies live, where conditional access sessions are maintained, where admin portals are opened, and where internal applications often assume the endpoint is trustworthy. If an attacker can execute code in the browser’s sandbox, they may not need to pop SYSTEM to cause damage. Session riding, data theft from reachable origins, malicious extension installation paths, or staging for a second exploit can be enough.
That is why “inside a sandbox” should not be translated into “low priority.” It should be translated into “patch quickly, and be grateful the architecture provides layers.” The existence of a seatbelt is not an argument for delaying brake repairs.
But defenders should not confuse “no known exploitation” with “no meaningful risk.” Chrome’s own practice of restricting bug details until most users are updated reflects the reality that patch publication starts a race. Attackers can diff builds, study commits, infer crash conditions, and attempt to reconstruct exploit paths. The public CVE description may be sparse, but the fixed binary and the vulnerable binary are both available to people with time and skill.
This is the awkward paradox of responsible disclosure at browser scale. Vendors must tell users to update, but too much detail too early can arm attackers before the update reaches the majority of devices. So we get terse descriptions: “Use after free in Animation.” For defenders, terse should not mean trivial. It means the vendor is deliberately holding back the recipe.
The right response is urgency without panic. There is no need to unplug networks or declare every unpatched Chrome instance compromised. There is a need to compress the update window and confirm restarts. Chrome can download updates silently, but the fix often does not take effect until the browser restarts. In real fleets, that final step is where security intent goes to die.
That is how browser drift happens. A fleet that appears managed on paper slowly fragments across stable, extended stable, stale portable installs, old Chromium packages, and app-specific runtimes. Vulnerability dashboards then present a false binary: patched or unpatched. The reality is messier. Some machines have the update but need a restart. Some are blocked by policy. Some are offline. Some report through one management plane but browse through another.
CVE-2026-7358 is a useful forcing function because it is not exotic. It is exactly the kind of vulnerability that will recur. If your organization struggles to prove coverage for this bug, the problem is not this bug. The problem is the browser update system.
The healthier model treats browsers as tier-one security infrastructure, closer to endpoint protection than to productivity software. Admins should know which browsers are allowed, which update channels are permitted, how restarts are enforced, how extensions are governed, and how quickly a high-severity browser CVE can be remediated from disclosure to verified compliance. If that answer is measured in weeks, the organization is carrying avoidable risk.
The “Are we missing a CPE?” prompt on NVD pages can look like boilerplate, but for Chromium it is almost philosophical. What counts as affected software when the vulnerable code lives in an upstream engine consumed by many products? Is the answer only Google Chrome? What about Chromium packages? What about Edge? What about WebView2? What about Electron applications pinned to older Chromium baselines?
A CVE record is not an asset inventory. It is a pointer into a vulnerability ecosystem. Security teams still need to map that pointer onto their own software estate, and Chromium makes that harder because it is both a browser and a supply chain.
This is where Windows environments have a particular blind spot. Admins may be disciplined about Microsoft Update and still miss Chrome. They may manage Chrome and Edge but miss WebView2 runtimes. They may patch browsers but ignore Electron-based collaboration tools that carry old engine code. The vulnerability does not care which procurement category the software came through.
That reading is backwards. In browser security, patch velocity is a feature. The web’s attack surface is too large, too exposed, and too lucrative for monthly rituals to be enough. A browser that can move quickly can turn private bug reports into population-wide risk reduction before exploit developers catch up.
The real problem is not that Chrome updates often. The problem is that many organizations built software governance around a slower era. They want browser security to fit into the same cadence as printer drivers and line-of-business application updates. That world is gone. Browsers are closer to cloud services with local binaries than traditional desktop apps.
Extended Stable channels can be useful for feature control, but they should not become an excuse for security delay. Enterprises need to separate feature anxiety from security urgency. A memory-corruption fix in the rendering engine should not wait because a committee is still evaluating a UI tweak.
A malicious page can arrive through compromised legitimate sites, poisoned search results, malvertising, shortened links, injected redirects, attacker-controlled collaboration messages, fake document portals, and watering-hole attacks. The victim’s action may be mundane: opening a page that appears relevant to their job. The browser then does what browsers do: parses untrusted code from the Internet.
Security training helps at the margins, but it cannot be the primary control for browser memory bugs. Users cannot visually inspect a webpage and determine whether its animation timing triggers a use-after-free condition. Even highly technical users cannot be expected to reason about renderer object lifetimes before clicking a link.
That leaves layered defense. Patch quickly. Limit risky extensions. Use site isolation and modern browser defaults. Keep endpoint protection active. Harden identity so a stolen browser session does not become persistent domain compromise. Monitor for suspicious child processes, unusual browser behavior, and post-exploitation patterns. The vulnerability begins in Chrome, but the defense cannot end there.
For Windows users, the immediate answer is mundane: update Chrome, restart it, and verify the version. For admins, the deeper answer is to stop treating browser patching as a background convenience and start treating it as a measurable security control. If the browser is now the front door to work, identity, data, and applications, then a high-severity flaw in its animation machinery is not “just a Chrome bug.” It is a test of whether the organization can still move at Internet speed when the Internet pushes back.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 A Browser Bug That Looks Routine Until You Remember Where the Browser Sits
A Browser Bug That Looks Routine Until You Remember Where the Browser Sits
CVE-2026-7358 is, on paper, a familiar Chrome vulnerability: a memory-safety bug, categorized as CWE-416, in a browser subsystem that handles animation. The stated attack path is equally familiar. A remote attacker gets a user to open a malicious HTML page, and Chrome before 147.0.7727.138 can be pushed into arbitrary code execution inside the sandbox.That “inside a sandbox” phrase is doing important work. It does not mean the bug is harmless, and it does not mean the attacker owns the whole machine by default. It means the first stage lands in Chrome’s constrained renderer environment, where attackers typically need a second vulnerability or a separate escape technique to reach the operating system with broader privileges.
But in 2026, that caveat is comfort only in the narrowest sense. Browsers are credential vaults, application runtimes, identity brokers, password managers, PDF readers, WebAuthn front ends, corporate SaaS launchers, and sometimes the only “desktop” an employee meaningfully uses. Code execution in the browser process boundary is not a theoretical inconvenience. It is the first half of many serious compromises.
The Patch Is Simple; The Exposure Math Is Not
Google’s stable desktop update on April 28 moved Chrome to 147.0.7727.137/138 on Windows and macOS, and 147.0.7727.137 on Linux. The release contained 30 security fixes, including several critical use-after-free vulnerabilities and a long list of high-severity memory bugs across GPU, ANGLE, Views, WebRTC, Media, Cast, Codecs, Navigation, and other components.CVE-2026-7358 sits in that larger pattern. It was reported by Google on March 25, carried a Chromium severity of High, and appeared publicly as part of the late-April stable-channel update. NVD published the entry on April 28 and modified it on April 30, with CISA-ADP assigning a CVSS 3.1 score of 8.8: network attack vector, low attack complexity, no privileges required, user interaction required, and high impact to confidentiality, integrity, and availability.
That score is useful but incomplete. CVSS treats user interaction as a mitigating factor, but the web is built out of user interaction. Clicking a link, opening a tab, previewing a document, visiting a compromised site, following a redirect chain, or hitting a malicious ad slot are all normal behaviors. In a browser vulnerability, “user interaction required” often means “the victim used the web.”
The practical fix is not complicated. Chrome needs to be at or beyond the fixed build on affected platforms, and Chromium-based browsers need their own vendor updates once they ingest the upstream patch. The operational problem is proving that this has happened everywhere: laptops asleep during maintenance windows, VDI images lagging behind, kiosks pinned to old builds, unmanaged developer machines, and third-party app bundles carrying embedded Chromium runtimes.
Use-After-Free Remains the Browser Bug That Refuses to Retire
A use-after-free flaw occurs when software continues to use memory after it has been released. In a complex C++ application like Chrome, where objects are created, animated, passed between threads, rendered, composited, and destroyed at high speed, lifetime mistakes are a perennial source of exploitable behavior.Animation is an especially plausible neighborhood for this kind of bug. Modern web animation is not merely decorative; it touches layout, compositing, GPU acceleration, timing, scripting, frame lifecycle, and DOM state. A malicious page can often manipulate those moving parts with precision, trying to force the browser into an unexpected sequence: create an object, detach it, free it, then cause stale code to reference it again.
That is why memory-safety bugs in browsers are so stubborn. The web platform is an adversarial programming interface exposed to every site on Earth. Browser vendors are not just building software; they are building a machine that accepts hostile input all day and still has to render a banking site, a Teams call, a WebGL dashboard, and a sketchy coupon popup without falling over.
Google has invested heavily in fuzzing, sanitizers, sandboxing, exploit mitigations, site isolation, and safer coding patterns. The April 28 release itself credits tools such as AddressSanitizer, MemorySanitizer, UndefinedBehaviorSanitizer, Control Flow Integrity, libFuzzer, and AFL for finding many classes of bugs before they become disasters. Yet the release also shows how much vulnerable surface remains. When one stable update includes 30 security fixes and a parade of memory corruption issues, the lesson is not that Chrome security is failing. The lesson is that the browser is one of the most aggressively tested pieces of software in the world because it has to be.
Microsoft’s Role Is a Reminder That Chromium Is Now Infrastructure
The MSRC listing for CVE-2026-7358 matters to WindowsForum readers because Chrome vulnerabilities do not stay in Chrome-shaped boxes. Microsoft Edge is Chromium-based. WebView2 is deeply embedded in Windows application ecosystems. Enterprise security teams often consume browser CVEs through Microsoft’s Security Update Guide even when the assigning source is Chrome.That shared Chromium foundation is one of the great engineering bargains of the modern web. Microsoft no longer maintains a fully separate browser engine for Edge; instead, it contributes to and consumes Chromium, gaining compatibility and velocity. Developers get fewer browser-specific surprises. Users get a modern engine with broad standards support.
The tradeoff is synchronized risk. A serious Chromium flaw becomes a multi-vendor coordination problem. Google Chrome, Microsoft Edge, Brave, Vivaldi, Opera, Electron apps, embedded WebViews, and Linux distribution Chromium packages do not all update at exactly the same moment or through the same management channel. The browser monoculture concern is no longer theoretical; it is visible every time one upstream CVE fans out across desktop fleets.
For Windows admins, that means patch status cannot stop at “Chrome updated.” Edge Stable, Edge Extended Stable, WebView2 Runtime, packaged browsers in app stores, and third-party software that embeds Chromium all deserve attention. The first vendor to ship the fix is not the same thing as the last vulnerable copy disappearing from the environment.
The Version Number Is the Control, Not the Advisory
Security teams love advisories because advisories are legible. They have identifiers, scores, dates, product names, and a reassuring sense of closure. But the actual control is the version number running on endpoints.For CVE-2026-7358, the key Chrome line is prior to 147.0.7727.138, with Google’s April 28 desktop release using 147.0.7727.137/138 for Windows and macOS and 147.0.7727.137 for Linux. That small platform variation is exactly why vulnerability management systems sometimes become noisy or misleading. A scanner may flag “less than .138” while a Linux channel legitimately shows .137 from the vendor’s stable release. Another tool may wait for NVD enrichment before producing a clean CPE match. A third may conflate Chrome and Chromium packages.
NVD’s change history is a good example of the machinery behind the scenes. The CVE arrived from Chrome on April 28, received CISA-ADP scoring on April 29, and gained NIST CPE configuration data on April 30. That delay is normal, but normal is not the same as operationally harmless. If your patch process waits for every database to converge, you are letting metadata latency dictate exposure time.
The better approach is to treat the vendor release as the starting gun. Once Google says a stable build fixes high-severity memory corruption in the browser, the enterprise question becomes deployment verification, not advisory interpretation. Version inventory, browser restart enforcement, and update-channel health matter more than another hour spent debating whether a CPE string has settled.
The Sandbox Lowers the Blast Radius, But It Does Not Cancel the Fire
Chrome’s sandbox is one of the most consequential browser security mechanisms ever deployed. It is designed to keep renderer compromise from becoming immediate system compromise. That distinction has prevented countless bugs from becoming full-device takeovers.But the sandbox should be understood as damage containment, not immunity. Attackers chain vulnerabilities. They pair renderer execution with sandbox escapes, kernel bugs, GPU driver flaws, broker-process weaknesses, credential theft, token abuse, extension compromise, and social-engineering steps. A high-severity renderer bug is often valuable precisely because it gives the attacker a foothold in a highly privileged user context: the authenticated browser session.
This is especially relevant in enterprise Windows environments. The browser is where SSO cookies live, where conditional access sessions are maintained, where admin portals are opened, and where internal applications often assume the endpoint is trustworthy. If an attacker can execute code in the browser’s sandbox, they may not need to pop SYSTEM to cause damage. Session riding, data theft from reachable origins, malicious extension installation paths, or staging for a second exploit can be enough.
That is why “inside a sandbox” should not be translated into “low priority.” It should be translated into “patch quickly, and be grateful the architecture provides layers.” The existence of a seatbelt is not an argument for delaying brake repairs.
The Absence of a Zero-Day Label Is Good News, Not a Strategy
As of the public release information, CVE-2026-7358 is not being described by Google as actively exploited in the wild. That matters. Emergency response should distinguish between exploited zero-days and high-severity bugs fixed through the normal stable channel.But defenders should not confuse “no known exploitation” with “no meaningful risk.” Chrome’s own practice of restricting bug details until most users are updated reflects the reality that patch publication starts a race. Attackers can diff builds, study commits, infer crash conditions, and attempt to reconstruct exploit paths. The public CVE description may be sparse, but the fixed binary and the vulnerable binary are both available to people with time and skill.
This is the awkward paradox of responsible disclosure at browser scale. Vendors must tell users to update, but too much detail too early can arm attackers before the update reaches the majority of devices. So we get terse descriptions: “Use after free in Animation.” For defenders, terse should not mean trivial. It means the vendor is deliberately holding back the recipe.
The right response is urgency without panic. There is no need to unplug networks or declare every unpatched Chrome instance compromised. There is a need to compress the update window and confirm restarts. Chrome can download updates silently, but the fix often does not take effect until the browser restarts. In real fleets, that final step is where security intent goes to die.
Enterprise IT’s Real Enemy Is Browser Drift
Most consumer Chrome installations update themselves well enough, eventually. Enterprises are different. They have change-control windows, compatibility testing, legacy web apps, browser extensions, VDI images, application control rules, proxy dependencies, and users who keep 80 tabs open for three weeks because one of them contains “important work.”That is how browser drift happens. A fleet that appears managed on paper slowly fragments across stable, extended stable, stale portable installs, old Chromium packages, and app-specific runtimes. Vulnerability dashboards then present a false binary: patched or unpatched. The reality is messier. Some machines have the update but need a restart. Some are blocked by policy. Some are offline. Some report through one management plane but browse through another.
CVE-2026-7358 is a useful forcing function because it is not exotic. It is exactly the kind of vulnerability that will recur. If your organization struggles to prove coverage for this bug, the problem is not this bug. The problem is the browser update system.
The healthier model treats browsers as tier-one security infrastructure, closer to endpoint protection than to productivity software. Admins should know which browsers are allowed, which update channels are permitted, how restarts are enforced, how extensions are governed, and how quickly a high-severity browser CVE can be remediated from disclosure to verified compliance. If that answer is measured in weeks, the organization is carrying avoidable risk.
The CPE Wrinkle Shows Why Vulnerability Data Still Needs Human Judgment
The NVD entry’s CPE configuration ties vulnerable Chrome versions to common operating systems: Windows, Linux, and macOS. That is useful for scanners, but it also illustrates a recurring weakness in machine-readable vulnerability management. CPEs describe product applicability; they do not always capture packaging reality, downstream vendor timing, or browser forks with their own version schemes.The “Are we missing a CPE?” prompt on NVD pages can look like boilerplate, but for Chromium it is almost philosophical. What counts as affected software when the vulnerable code lives in an upstream engine consumed by many products? Is the answer only Google Chrome? What about Chromium packages? What about Edge? What about WebView2? What about Electron applications pinned to older Chromium baselines?
A CVE record is not an asset inventory. It is a pointer into a vulnerability ecosystem. Security teams still need to map that pointer onto their own software estate, and Chromium makes that harder because it is both a browser and a supply chain.
This is where Windows environments have a particular blind spot. Admins may be disciplined about Microsoft Update and still miss Chrome. They may manage Chrome and Edge but miss WebView2 runtimes. They may patch browsers but ignore Electron-based collaboration tools that carry old engine code. The vulnerability does not care which procurement category the software came through.
Patch Velocity Has Become a Competitive Security Feature
The Chrome team’s frequent security updates are sometimes mocked as churn. Users notice the “Relaunch to update” button. Admins notice the tickets. Developers notice when a browser change breaks some brittle internal workflow. It is tempting to see the cadence as instability.That reading is backwards. In browser security, patch velocity is a feature. The web’s attack surface is too large, too exposed, and too lucrative for monthly rituals to be enough. A browser that can move quickly can turn private bug reports into population-wide risk reduction before exploit developers catch up.
The real problem is not that Chrome updates often. The problem is that many organizations built software governance around a slower era. They want browser security to fit into the same cadence as printer drivers and line-of-business application updates. That world is gone. Browsers are closer to cloud services with local binaries than traditional desktop apps.
Extended Stable channels can be useful for feature control, but they should not become an excuse for security delay. Enterprises need to separate feature anxiety from security urgency. A memory-corruption fix in the rendering engine should not wait because a committee is still evaluating a UI tweak.
The User Is Still the Trigger, and That Is the Hardest Part to Defend
CVE-2026-7358 requires user interaction, which usually means a crafted page must be loaded. That sounds like a phishing-awareness problem, and partly it is. But browser exploitation has never depended solely on users clicking obviously suspicious links.A malicious page can arrive through compromised legitimate sites, poisoned search results, malvertising, shortened links, injected redirects, attacker-controlled collaboration messages, fake document portals, and watering-hole attacks. The victim’s action may be mundane: opening a page that appears relevant to their job. The browser then does what browsers do: parses untrusted code from the Internet.
Security training helps at the margins, but it cannot be the primary control for browser memory bugs. Users cannot visually inspect a webpage and determine whether its animation timing triggers a use-after-free condition. Even highly technical users cannot be expected to reason about renderer object lifetimes before clicking a link.
That leaves layered defense. Patch quickly. Limit risky extensions. Use site isolation and modern browser defaults. Keep endpoint protection active. Harden identity so a stolen browser session does not become persistent domain compromise. Monitor for suspicious child processes, unusual browser behavior, and post-exploitation patterns. The vulnerability begins in Chrome, but the defense cannot end there.
The April 28 Chrome Drop Leaves Windows Shops With a Short Checklist
CVE-2026-7358 is one item in a larger Chrome security release, but it gives admins a clean moment to check whether their browser patch process is real or merely assumed. The practical lesson is not complicated; the discipline is in doing it quickly and proving it.- Chrome installations on Windows and macOS should be moved to 147.0.7727.138 or a later fixed build, while Linux administrators should follow the fixed build made available through their distribution or Google’s channel.
- Microsoft Edge and other Chromium-based browsers should be checked separately, because an updated Chrome installation does not prove that every Chromium consumer on the machine has received the fix.
- Browser restarts should be treated as part of remediation, since downloaded updates do not fully protect users until the running vulnerable process is replaced.
- Vulnerability scanners should be validated against actual installed versions, because NVD enrichment, CPE matching, and downstream packaging can lag behind vendor releases.
- Organizations should review embedded Chromium exposure, including WebView2 and Electron-based applications, rather than limiting the search to user-facing browser icons.
- The absence of public active-exploitation language should lower panic, not priority, because high-severity browser memory bugs become more useful to attackers after patches reveal where to look.
This Is the Browser Security Model We Chose
The modern web won because it made the browser the universal client. That decision brought enormous convenience, and then it quietly concentrated risk into a handful of engines that parse hostile content at global scale. CVE-2026-7358 is not an outlier in that story; it is a weekly reminder of the bargain.For Windows users, the immediate answer is mundane: update Chrome, restart it, and verify the version. For admins, the deeper answer is to stop treating browser patching as a background convenience and start treating it as a measurable security control. If the browser is now the front door to work, identity, data, and applications, then a high-severity flaw in its animation machinery is not “just a Chrome bug.” It is a test of whether the organization can still move at Internet speed when the Internet pushes back.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center