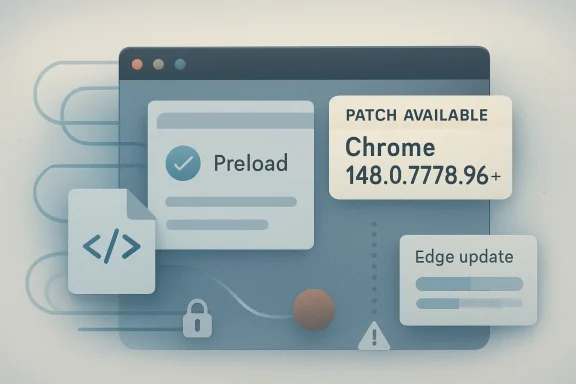
Google’s CVE-2026-8014 is a low-severity Chromium vulnerability in Chrome’s Preload implementation, disclosed May 6, 2026, fixed before Chrome 148.0.7778.96, and capable of letting a remote attacker leak cross-origin data through a crafted HTML page if the user visits it. The short version is reassuring; the longer version is more interesting. This is not the kind of bug that should send administrators into emergency-change-control mode, but it is exactly the kind of browser flaw that explains why “low” no longer means “ignore.” In 2026, browser security is less about spectacular single exploits and more about the steady erosion of assumptions that the web platform is supposed to enforce.
CVE-2026-8014 sits in a quiet part of the browser, not in the cinematic territory of sandbox escapes or remote-code execution. The affected component, Preload, is part of the machinery that helps a browser fetch or prepare resources before they are explicitly needed. Done right, preloading makes the web feel faster. Done wrong, it can make the browser reveal more than it should about data that belongs to another origin.
That distinction matters because the browser’s great bargain is not merely that it renders pages quickly. It is that it lets hostile, indifferent, and trustworthy sites coexist in the same application without collapsing into one another. The same-origin policy is the rulebook that makes that coexistence possible, and cross-origin leakage bugs are failures at the edge of that rulebook.
The disclosed impact is narrow: a crafted HTML page could leak cross-origin data. The attacker needs a user to interact with malicious web content by visiting or loading it, and the listed confidentiality impact is low. There is no stated integrity or availability impact, and no public indication in the provided record that this specific vulnerability was exploited in the wild.
But the bug’s shape is familiar. It is another reminder that browser vulnerabilities do not have to “own the box” to matter. Sometimes the prize is a sliver of information: a response timing difference, a cache state, a speculative fetch, a protection boundary that behaves differently when a victim is logged in somewhere else. Modern attackers are often happy to collect slivers.
That context changes how defenders should read this CVE. CVE-2026-8014 is low severity on its own, but it rode into production as part of a major browser security train. Enterprises that patch only by scanning individual CVSS numbers miss the more operational reality: Chrome 148 is a browser-wide risk reduction release, not merely a patch for one Preload bug.
The NVD record also shows the usual lag and layering that administrators have learned to navigate. The CVE was received from Chrome on May 6, modified by CISA-ADP later that day, and initially analyzed by NIST on May 7. CISA-ADP assigned a CVSS 3.1 base score of 4.3, medium, while the Chromium severity is listed as low and NVD’s own scoring was not yet provided in the user-supplied record.
That mismatch is not scandalous; it is the vulnerability ecosystem doing what it does. Vendor severity, CVSS scoring, automated enrichment, CPE mapping, and downstream product advisories all answer slightly different questions. The browser team asks how dangerous the bug is in Chromium’s architecture. CVSS asks how the vulnerability behaves under a standardized model. Enterprise scanners ask whether the installed product is below a fixed version. None of those views is complete by itself.
The security problem is that anticipation can create observable side effects. If a browser fetches something early, caches something differently, exposes timing differences, follows metadata too eagerly, or applies origin checks at the wrong point in the pipeline, the attacker may not need direct access to a protected response. The attacker may only need to infer whether a protected resource was fetched, how it behaved, or whether a victim’s authenticated state changed the browser’s behavior.
That is why “inappropriate implementation” is such a maddening but meaningful phrase in Chromium CVEs. It does not describe a memory corruption flaw with a tidy primitive. It describes logic that was not wrong in the ordinary user-visible sense, but wrong against the web platform’s security contract.
For WindowsForum readers, this is where the story intersects with everyday administration. A user can be fully patched at the OS level, running as a standard account, behind a reputable firewall, and still be exposed to browser-origin bugs because the browser is the place where hostile code is expected to run. The modern browser is simultaneously an application runtime, document viewer, identity surface, sync client, password broker, and update channel. Preload is one of many subsystems that makes that complexity look seamless until it does not.
That is a perfectly reasonable score for a standalone vulnerability. It is also a poor reason to defer browser patching. Browsers are not patched like obscure server packages with narrow exposure and carefully controlled input. Browsers are deliberately pointed at untrusted input all day, every day, by users whose work requires them to click links, preview documents, authenticate to SaaS applications, and live inside federated identity flows.
The other problem with CVSS triage is composition. A low-severity cross-origin leak can be more useful when paired with phishing, session probing, login detection, intranet reachability checks, XS-Leak techniques, or a second browser bug. Attack chains rarely respect the neat accounting of a single CVE entry.
This does not mean every low-severity Chromium bug is a crisis. It means the patching decision should be made at the browser release level rather than the single-CVE level. Chrome 148 contains enough security work that the correct operational question is not, “Is CVE-2026-8014 scary?” It is, “Why would we knowingly run a pre-148 browser on internet-facing endpoints after the stable fix is available?”
This is where the Microsoft ecosystem can be both helpful and confusing. MSRC entries bring Chromium CVEs into the world that Windows administrators already understand: Update Guide pages, CVE IDs, severity labels, and security dashboards. But Edge is updated through its own browser update mechanisms, enterprise policies, and release channels. It is adjacent to Windows Update without being reducible to Windows Update.
That matters for shops that still think of browser patching as part of the monthly operating-system ritual. Chromium does not wait for Patch Tuesday when the release train is ready or when an out-of-band fix is needed. Edge often moves on a browser cadence, not a classic Windows cadence. Chrome does the same. The asset inventory that says “Windows fully patched” may say little about whether the browser engine that actually parses the attacker’s HTML is current.
The prudent assumption is simple: if a Chromium CVE is relevant enough to appear in Microsoft’s security universe, Edge should be checked independently. Managed environments should verify the installed Edge version, update policy state, and whether users are pinned to an extended stable channel. Consumer and small-business users should open the browser’s About page and let the updater do its work.
So are we missing a CPE? Probably, in the practical sense, yes. Chromium is an upstream project used by many browsers and embedded runtimes, and not every downstream consumer of Chromium will necessarily appear cleanly in a single early NVD configuration. But that does not mean the NVD record is defective in the narrow sense. It means CPEs are a blunt instrument for an ecosystem that is increasingly built from shared engines, vendored components, and evergreen application runtimes.
Chrome is the obvious product. Edge is the obvious WindowsForum concern. But the operational blast radius can include Electron applications, embedded browser controls, automated headless Chromium deployments, kiosk systems, PDF rendering services, testing containers, and Linux packages maintained by distributions. Not all of those are necessarily vulnerable in the same way, and not all will expose Preload behavior identically, but the question is broader than “Is Google Chrome installed?”
This is one reason vulnerability management teams increasingly supplement CPE-based scanning with software bills of materials, application inventory, executable version checks, and endpoint telemetry. A scanner can tell you that Chrome is old. It may not tell you that a line-of-business app ships a stale Chromium runtime buried three directories deep, or that a container image used for HTML-to-PDF conversion has not been rebuilt since the last fiscal year.
The reason these bugs persist is not that browser engineers are careless. It is that the web platform is an enormous compatibility machine. Features are added, optimized, deprecated, partially preserved, and reinterpreted across decades of content. Every new performance optimization has to coexist with an old site, a new framework, a corporate proxy, a CDN, a privacy boundary, and a security model that was never designed for today’s application density.
Preload belongs to the class of features that make this tension visible. Developers want pages to start faster and feel more native. Browsers want to anticipate safely. Security engineers want origin checks to hold even when work is moved earlier in the pipeline. Privacy engineers want fewer observable side channels. Users just want the page to load.
The result is a constant negotiation. CVE-2026-8014 is one line item in that negotiation. It is not an indictment of Preload as a concept; it is evidence that performance plumbing must be treated as security-sensitive code.
A malicious HTML page can arrive by email, chat, search result, malvertising, compromised legitimate site, shared document workflow, ticketing system, or a forum post. None of those paths requires Hollywood hacking. They require attention, timing, and a victim whose work involves opening links.
This is especially true for environments where the browser is also the access layer for internal systems. A user logged into webmail, HR, CRM, identity dashboards, cloud consoles, and internal portals has a richer cross-origin environment than a freshly installed browser on a lab machine. Even if a low-severity leak reveals only a small fact, that fact may be valuable if it confirms authentication state, resource existence, tenant configuration, or application behavior.
The practical response is not panic, and it is not user-blaming. It is defense in depth. Keep the browser current, reduce unnecessary ambient authentication where possible, use site isolation and modern browser defaults, harden enterprise policies without breaking workflows, and recognize that web content is a hostile input format even when it arrives in business clothing.
Evergreen browsers have moved the security boundary from the installation event to the update pipeline. The question is not whether Chrome 148 exists. It is whether endpoints actually received it, restarted into it, and stopped running old renderer processes. Browsers can download an update and still leave risk alive until the user relaunches. In managed fleets, update policies can be set correctly and still fail if devices are offline, profiles are broken, or stale sessions run for days.
This is why admins should treat browser version verification as a first-class control. It is not enough to assume automatic update succeeded because the product usually updates itself. The useful control is measured state: how many endpoints are at or above the fixed build, how many are pending restart, how many are outside policy, and how many are running unmanaged Chromium derivatives.
For small offices and home users, the advice is simpler but not weaker. Open Chrome or Edge’s About page, let the browser check for updates, and relaunch. The relaunch is not administrative theater; it is the moment the fixed code replaces the vulnerable process.
But prioritization is not binary. CVE-2026-8014 does not deserve the same response as an actively exploited remote-code execution bug. It does deserve inclusion in the normal browser patch rhythm, and that rhythm should be measured in days, not quarters. For most organizations, the right answer is expedited routine patching: verify update availability, deploy through existing browser channels, watch telemetry, and chase stragglers.
The difference is important. Emergency patching consumes trust. If every low-severity browser issue becomes a stop-the-line incident, users and change boards eventually tune out. But if low-severity browser issues are ignored until the next quarterly maintenance window, the organization has misunderstood the exposure model of the web.
The healthy middle is boring and disciplined. Browser updates should be frequent enough that a low-severity web-platform fix does not require a special meeting. The process should already exist, the telemetry should already be wired, and the exception list should already be short.
The cost is correlated risk. A subtle Chromium bug can affect multiple products, platforms, and workflows before defenders fully understand the reach. Even when downstream vendors ship quickly, the ecosystem moves in waves: upstream fix, Chrome release, Edge release, distribution packages, embedded runtimes, container rebuilds, third-party application updates, and finally endpoint reality.
CVE-2026-8014 is not the most alarming example of that dynamic, but it illustrates it cleanly. The CVE name says Chrome. The source page may be Microsoft. The component is Chromium. The affected behavior is web-platform logic. The installed exposure may live in a browser, a kiosk, a renderer service, or an application nobody thinks of as a browser.
That is the modern patch-management problem in miniature. We used to inventory products. Now we also have to inventory engines.
The second action is policy review. Enterprises should confirm that Chrome and Edge update policies are not pinned too aggressively, that extended stable channels are used intentionally, and that restart prompts are not being deferred into irrelevance. A browser that downloaded the fix but has not restarted is a half-solved problem.
The third action is to widen the search beyond the obvious browsers. Headless Chromium in automation stacks, Electron apps, embedded WebView-like components, and browser-based rendering services deserve periodic review. They may not all be affected by this precise bug, but stale Chromium components are a recurring source of avoidable exposure.
Finally, administrators should resist the temptation to convert this into a user-awareness story. Users should not be expected to reason about Preload, origins, CVSS vectors, or whether a page can trigger a cross-origin leak. The whole point of the browser security model is that users can navigate the web without becoming protocol analysts.
Those details point to a patch-now-but-do-not-panic response. The bug does not, on the public record provided, grant code execution, alter data, or crash systems. It does, however, weaken a fundamental browser boundary, and it arrives in a release that carries a larger set of security fixes.
For a home user, that means checking for browser updates and restarting. For an enterprise, it means confirming fleet compliance and looking for unmanaged Chromium. For a security team, it means treating low-severity browser leaks as part of a cumulative attack surface rather than isolated trivia.
The most concrete takeaways are not dramatic, but they are actionable.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 A Low-Severity Bug Still Cuts Across the Browser’s Core Promise
A Low-Severity Bug Still Cuts Across the Browser’s Core Promise
CVE-2026-8014 sits in a quiet part of the browser, not in the cinematic territory of sandbox escapes or remote-code execution. The affected component, Preload, is part of the machinery that helps a browser fetch or prepare resources before they are explicitly needed. Done right, preloading makes the web feel faster. Done wrong, it can make the browser reveal more than it should about data that belongs to another origin.That distinction matters because the browser’s great bargain is not merely that it renders pages quickly. It is that it lets hostile, indifferent, and trustworthy sites coexist in the same application without collapsing into one another. The same-origin policy is the rulebook that makes that coexistence possible, and cross-origin leakage bugs are failures at the edge of that rulebook.
The disclosed impact is narrow: a crafted HTML page could leak cross-origin data. The attacker needs a user to interact with malicious web content by visiting or loading it, and the listed confidentiality impact is low. There is no stated integrity or availability impact, and no public indication in the provided record that this specific vulnerability was exploited in the wild.
But the bug’s shape is familiar. It is another reminder that browser vulnerabilities do not have to “own the box” to matter. Sometimes the prize is a sliver of information: a response timing difference, a cache state, a speculative fetch, a protection boundary that behaves differently when a victim is logged in somewhere else. Modern attackers are often happy to collect slivers.
Chrome 148 Was Not a Routine Point Release
The fix for CVE-2026-8014 arrived in the broader Chrome 148 stable release, with Google promoting version 148.0.7778.96 for Linux and 148.0.7778.96/97 for Windows and macOS. That release was not a tiny hotfix for one obscure issue. Public reporting on the stable update describes more than 100 security fixes, including critical vulnerabilities elsewhere in Chromium.That context changes how defenders should read this CVE. CVE-2026-8014 is low severity on its own, but it rode into production as part of a major browser security train. Enterprises that patch only by scanning individual CVSS numbers miss the more operational reality: Chrome 148 is a browser-wide risk reduction release, not merely a patch for one Preload bug.
The NVD record also shows the usual lag and layering that administrators have learned to navigate. The CVE was received from Chrome on May 6, modified by CISA-ADP later that day, and initially analyzed by NIST on May 7. CISA-ADP assigned a CVSS 3.1 base score of 4.3, medium, while the Chromium severity is listed as low and NVD’s own scoring was not yet provided in the user-supplied record.
That mismatch is not scandalous; it is the vulnerability ecosystem doing what it does. Vendor severity, CVSS scoring, automated enrichment, CPE mapping, and downstream product advisories all answer slightly different questions. The browser team asks how dangerous the bug is in Chromium’s architecture. CVSS asks how the vulnerability behaves under a standardized model. Enterprise scanners ask whether the installed product is below a fixed version. None of those views is complete by itself.
Preload Is Performance Plumbing With Security Consequences
Preload sounds like a performance feature because it is one. Browsers try to anticipate what a page will need next: scripts, stylesheets, images, fonts, documents, and connections. The web is slow enough that milliseconds matter, and modern browser engines are full of mechanisms designed to hide latency from users.The security problem is that anticipation can create observable side effects. If a browser fetches something early, caches something differently, exposes timing differences, follows metadata too eagerly, or applies origin checks at the wrong point in the pipeline, the attacker may not need direct access to a protected response. The attacker may only need to infer whether a protected resource was fetched, how it behaved, or whether a victim’s authenticated state changed the browser’s behavior.
That is why “inappropriate implementation” is such a maddening but meaningful phrase in Chromium CVEs. It does not describe a memory corruption flaw with a tidy primitive. It describes logic that was not wrong in the ordinary user-visible sense, but wrong against the web platform’s security contract.
For WindowsForum readers, this is where the story intersects with everyday administration. A user can be fully patched at the OS level, running as a standard account, behind a reputable firewall, and still be exposed to browser-origin bugs because the browser is the place where hostile code is expected to run. The modern browser is simultaneously an application runtime, document viewer, identity surface, sync client, password broker, and update channel. Preload is one of many subsystems that makes that complexity look seamless until it does not.
The CVSS Number Is a Floor, Not a Strategy
CISA-ADP’s vector for CVE-2026-8014 is straightforward: network attack vector, low attack complexity, no privileges required, user interaction required, unchanged scope, low confidentiality impact, and no integrity or availability impact. In practical language, an attacker can exploit the bug remotely through web content, but the user has to encounter that content, and the expected result is limited information disclosure.That is a perfectly reasonable score for a standalone vulnerability. It is also a poor reason to defer browser patching. Browsers are not patched like obscure server packages with narrow exposure and carefully controlled input. Browsers are deliberately pointed at untrusted input all day, every day, by users whose work requires them to click links, preview documents, authenticate to SaaS applications, and live inside federated identity flows.
The other problem with CVSS triage is composition. A low-severity cross-origin leak can be more useful when paired with phishing, session probing, login detection, intranet reachability checks, XS-Leak techniques, or a second browser bug. Attack chains rarely respect the neat accounting of a single CVE entry.
This does not mean every low-severity Chromium bug is a crisis. It means the patching decision should be made at the browser release level rather than the single-CVE level. Chrome 148 contains enough security work that the correct operational question is not, “Is CVE-2026-8014 scary?” It is, “Why would we knowingly run a pre-148 browser on internet-facing endpoints after the stable fix is available?”
Microsoft’s Edge Stake Is Bigger Than the MSRC Page
The user-provided source is Microsoft’s vulnerability page, and that is appropriate because Edge inherits much of this risk through Chromium. Microsoft Edge is not Chrome with a different icon, but its security posture is inseparable from the Chromium engine underneath. When Chromium fixes a web platform bug, Edge administrators need to watch Microsoft’s update cadence just as Chrome administrators watch Google’s.This is where the Microsoft ecosystem can be both helpful and confusing. MSRC entries bring Chromium CVEs into the world that Windows administrators already understand: Update Guide pages, CVE IDs, severity labels, and security dashboards. But Edge is updated through its own browser update mechanisms, enterprise policies, and release channels. It is adjacent to Windows Update without being reducible to Windows Update.
That matters for shops that still think of browser patching as part of the monthly operating-system ritual. Chromium does not wait for Patch Tuesday when the release train is ready or when an out-of-band fix is needed. Edge often moves on a browser cadence, not a classic Windows cadence. Chrome does the same. The asset inventory that says “Windows fully patched” may say little about whether the browser engine that actually parses the attacker’s HTML is current.
The prudent assumption is simple: if a Chromium CVE is relevant enough to appear in Microsoft’s security universe, Edge should be checked independently. Managed environments should verify the installed Edge version, update policy state, and whether users are pinned to an extended stable channel. Consumer and small-business users should open the browser’s About page and let the updater do its work.
The CPE Record Tells a Smaller Story Than Administrators Want
The NVD change history in the user’s excerpt includes a CPE configuration for Google Chrome versions before 148.0.7778.96, with Windows, Linux, and macOS operating-system CPEs listed as part of the affected configuration. It also includes the familiar “Are we missing a CPE here?” prompt, which appears when NVD’s known affected software mapping may not capture every downstream product or packaging variant.So are we missing a CPE? Probably, in the practical sense, yes. Chromium is an upstream project used by many browsers and embedded runtimes, and not every downstream consumer of Chromium will necessarily appear cleanly in a single early NVD configuration. But that does not mean the NVD record is defective in the narrow sense. It means CPEs are a blunt instrument for an ecosystem that is increasingly built from shared engines, vendored components, and evergreen application runtimes.
Chrome is the obvious product. Edge is the obvious WindowsForum concern. But the operational blast radius can include Electron applications, embedded browser controls, automated headless Chromium deployments, kiosk systems, PDF rendering services, testing containers, and Linux packages maintained by distributions. Not all of those are necessarily vulnerable in the same way, and not all will expose Preload behavior identically, but the question is broader than “Is Google Chrome installed?”
This is one reason vulnerability management teams increasingly supplement CPE-based scanning with software bills of materials, application inventory, executable version checks, and endpoint telemetry. A scanner can tell you that Chrome is old. It may not tell you that a line-of-business app ships a stale Chromium runtime buried three directories deep, or that a container image used for HTML-to-PDF conversion has not been rebuilt since the last fiscal year.
Cross-Origin Leaks Are the Web’s Long-Running Tax
Cross-origin data leaks are not new. The web has spent years patching variants of the same broad class: timing attacks, cache probing, speculative execution side effects, resource inclusion quirks, redirect behavior, MIME confusion, service worker boundaries, history sniffing, and increasingly subtle ways to infer facts about another origin without reading its response directly.The reason these bugs persist is not that browser engineers are careless. It is that the web platform is an enormous compatibility machine. Features are added, optimized, deprecated, partially preserved, and reinterpreted across decades of content. Every new performance optimization has to coexist with an old site, a new framework, a corporate proxy, a CDN, a privacy boundary, and a security model that was never designed for today’s application density.
Preload belongs to the class of features that make this tension visible. Developers want pages to start faster and feel more native. Browsers want to anticipate safely. Security engineers want origin checks to hold even when work is moved earlier in the pipeline. Privacy engineers want fewer observable side channels. Users just want the page to load.
The result is a constant negotiation. CVE-2026-8014 is one line item in that negotiation. It is not an indictment of Preload as a concept; it is evidence that performance plumbing must be treated as security-sensitive code.
User Interaction Is Not Much of a Comfort
The CVSS vector requires user interaction, and for some classes of vulnerability that would materially reduce concern. In a browser, it is less comforting. “The user must visit a crafted page” describes the normal operating condition of the web.A malicious HTML page can arrive by email, chat, search result, malvertising, compromised legitimate site, shared document workflow, ticketing system, or a forum post. None of those paths requires Hollywood hacking. They require attention, timing, and a victim whose work involves opening links.
This is especially true for environments where the browser is also the access layer for internal systems. A user logged into webmail, HR, CRM, identity dashboards, cloud consoles, and internal portals has a richer cross-origin environment than a freshly installed browser on a lab machine. Even if a low-severity leak reveals only a small fact, that fact may be valuable if it confirms authentication state, resource existence, tenant configuration, or application behavior.
The practical response is not panic, and it is not user-blaming. It is defense in depth. Keep the browser current, reduce unnecessary ambient authentication where possible, use site isolation and modern browser defaults, harden enterprise policies without breaking workflows, and recognize that web content is a hostile input format even when it arrives in business clothing.
The Patch Cadence Is Now the Security Boundary
There was a time when browser updates were visible events. Users downloaded installers. IT departments packaged releases. People debated whether a new browser version would break the intranet. That world has not disappeared, but it is no longer the default for Chrome or Edge.Evergreen browsers have moved the security boundary from the installation event to the update pipeline. The question is not whether Chrome 148 exists. It is whether endpoints actually received it, restarted into it, and stopped running old renderer processes. Browsers can download an update and still leave risk alive until the user relaunches. In managed fleets, update policies can be set correctly and still fail if devices are offline, profiles are broken, or stale sessions run for days.
This is why admins should treat browser version verification as a first-class control. It is not enough to assume automatic update succeeded because the product usually updates itself. The useful control is measured state: how many endpoints are at or above the fixed build, how many are pending restart, how many are outside policy, and how many are running unmanaged Chromium derivatives.
For small offices and home users, the advice is simpler but not weaker. Open Chrome or Edge’s About page, let the browser check for updates, and relaunch. The relaunch is not administrative theater; it is the moment the fixed code replaces the vulnerable process.
The Low-Severity Label Should Change Priorities, Not Excuse Delay
Security teams are tired for good reason. Every week brings a new batch of CVEs, vendor advisories, scanner findings, and breathless headlines. A low-severity Chromium bug can feel like background noise, especially when the same release includes more dramatic vulnerabilities.But prioritization is not binary. CVE-2026-8014 does not deserve the same response as an actively exploited remote-code execution bug. It does deserve inclusion in the normal browser patch rhythm, and that rhythm should be measured in days, not quarters. For most organizations, the right answer is expedited routine patching: verify update availability, deploy through existing browser channels, watch telemetry, and chase stragglers.
The difference is important. Emergency patching consumes trust. If every low-severity browser issue becomes a stop-the-line incident, users and change boards eventually tune out. But if low-severity browser issues are ignored until the next quarterly maintenance window, the organization has misunderstood the exposure model of the web.
The healthy middle is boring and disciplined. Browser updates should be frequent enough that a low-severity web-platform fix does not require a special meeting. The process should already exist, the telemetry should already be wired, and the exception list should already be short.
The Chrome Monoculture Makes Small Bugs Travel Farther
Chromium’s dominance has obvious benefits for security. Bugs found and fixed upstream can protect a huge portion of the web quickly. Researchers have a clear target. Vendors can share fixes. Enterprises can standardize policy and testing across browsers that share much of the same engine.The cost is correlated risk. A subtle Chromium bug can affect multiple products, platforms, and workflows before defenders fully understand the reach. Even when downstream vendors ship quickly, the ecosystem moves in waves: upstream fix, Chrome release, Edge release, distribution packages, embedded runtimes, container rebuilds, third-party application updates, and finally endpoint reality.
CVE-2026-8014 is not the most alarming example of that dynamic, but it illustrates it cleanly. The CVE name says Chrome. The source page may be Microsoft. The component is Chromium. The affected behavior is web-platform logic. The installed exposure may live in a browser, a kiosk, a renderer service, or an application nobody thinks of as a browser.
That is the modern patch-management problem in miniature. We used to inventory products. Now we also have to inventory engines.
Windows Administrators Should Read This as an Edge and Chrome Hygiene Test
For Windows shops, the immediate action is version verification. Chrome installations should be at 148.0.7778.96 or later on affected desktop platforms, with Windows and macOS also seeing the 148.0.7778.97 build in Google’s release channel. Edge administrators should check Microsoft’s corresponding Chromium-based Edge security update status rather than assuming Windows Update compliance is enough.The second action is policy review. Enterprises should confirm that Chrome and Edge update policies are not pinned too aggressively, that extended stable channels are used intentionally, and that restart prompts are not being deferred into irrelevance. A browser that downloaded the fix but has not restarted is a half-solved problem.
The third action is to widen the search beyond the obvious browsers. Headless Chromium in automation stacks, Electron apps, embedded WebView-like components, and browser-based rendering services deserve periodic review. They may not all be affected by this precise bug, but stale Chromium components are a recurring source of avoidable exposure.
Finally, administrators should resist the temptation to convert this into a user-awareness story. Users should not be expected to reason about Preload, origins, CVSS vectors, or whether a page can trigger a cross-origin leak. The whole point of the browser security model is that users can navigate the web without becoming protocol analysts.
The Practical Reading of CVE-2026-8014 Is Narrow but Not Trivial
The concrete facts are mercifully simple, and the interpretation is where the value lies. CVE-2026-8014 is a confidentiality bug in Chromium’s Preload implementation. The fixed Chrome baseline is 148.0.7778.96. The attack requires crafted HTML and user interaction. Chromium labels it low severity; CISA-ADP’s CVSS 3.1 score lands at 4.3, medium. NVD enrichment and CPE mapping followed after the CVE was published.Those details point to a patch-now-but-do-not-panic response. The bug does not, on the public record provided, grant code execution, alter data, or crash systems. It does, however, weaken a fundamental browser boundary, and it arrives in a release that carries a larger set of security fixes.
For a home user, that means checking for browser updates and restarting. For an enterprise, it means confirming fleet compliance and looking for unmanaged Chromium. For a security team, it means treating low-severity browser leaks as part of a cumulative attack surface rather than isolated trivia.
The Lesson Hidden in Chrome 148’s Quietest CVE
CVE-2026-8014 will not be remembered as the defining browser bug of 2026. That is precisely why it is useful. It shows how the ordinary mechanics of browser security now work: small logic bugs in performance features, rapid upstream fixes, downstream vendor advisories, partial scoring data, CPE uncertainty, and an operational burden that falls on whoever owns endpoint hygiene.The most concrete takeaways are not dramatic, but they are actionable.
- Chrome installations older than 148.0.7778.96 should be treated as exposed to CVE-2026-8014 and the broader Chrome 148 security fix set.
- Edge administrators should verify the Chromium-based Edge update state separately instead of assuming Windows patch compliance covers the browser.
- The vulnerability’s known impact is limited to low-confidence confidentiality leakage, not public remote-code execution or system compromise.
- The user-interaction requirement should not be overvalued, because visiting untrusted web content is the browser’s ordinary job.
- Asset inventories should include embedded, headless, and application-bundled Chromium runtimes, not just the visible Chrome and Edge icons.
- Browser update telemetry should track installed version and pending relaunch state, because downloaded updates do not fully protect still-running old processes.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center