Microsoft has quietly updated the Defender package that should be injected into Windows installation images (WIM/VHD/ISO) used for fresh installs and deployments, delivering a new antimalware platform, engine, and security intelligence snapshot intended to close the “first‑boot” protection gap on Windows 11, Windows 10, and supported Windows Server images. ([support.microsoft.microsoft.com/en-gb/topic/microsoft-defender-update-for-windows-operating-system-installation-images-1c89630b-61ff-00a1-04e2-2d1f3865450d))
The problem Microsoft is addressing is simple but important: installation media and offline images can contain stale antimalware binaries. That means freshly installed devices may be exposed until Defender receives its next online update. Microsoft has long recommended servicing OS images regularly to prevent that exposure, and the company now publishes dedicated Defender update packages specifically for offline installation images so customers can slipstream current Defender binaries before deployment. (support.microsoft.com) (learn.microsoft.com)
This latest package — published as part of Microsoft’s DISM/installation‑image servicing guidance — contains updated Defender components (platform, engine) plus a snapshot of security intelligence signatures. Microsoft’s support article and Defender documentation explain the intended usage, distribution channels, prerequisites, and the recommended cadence for image servicing. (support.microsoft.com) (microsoft.com)
Community and administrative forums have repeatedly flagged the operational impact of stale images (long post‑install update times, patching complexity for offline environments, and security exposure), and this Defender image package is Microsoft’s targeted fix for that class of problem.
Key distribution/management notes:
Source: Neowin Microsoft releases new Defender update for Windows 11, 10, Server ISO installations
 Background / Overview
Background / Overview
The problem Microsoft is addressing is simple but important: installation media and offline images can contain stale antimalware binaries. That means freshly installed devices may be exposed until Defender receives its next online update. Microsoft has long recommended servicing OS images regularly to prevent that exposure, and the company now publishes dedicated Defender update packages specifically for offline installation images so customers can slipstream current Defender binaries before deployment. (support.microsoft.com) (learn.microsoft.com)This latest package — published as part of Microsoft’s DISM/installation‑image servicing guidance — contains updated Defender components (platform, engine) plus a snapshot of security intelligence signatures. Microsoft’s support article and Defender documentation explain the intended usage, distribution channels, prerequisites, and the recommended cadence for image servicing. (support.microsoft.com) (microsoft.com)
What this update contains (technical snapshot)
Microsoft’s published package information for the February 2026 refresh lists the following concrete items for the Windows installation‑image Defender package:- Defender package version: 1.445.6.0. (support.microsoft.com)
- Platform version: 4.18.26010.5. (support.microsoft.com)
- Engine version: 1.1.26010.1. (support.microsoft.com)
- Security intelligence: the package includes the security intelligence snapshot current at the package release; Microsoft also publishes rolling security intelligence updates (for example, a later security intelligence release shows versions in the 1.445.xxx family). (support.microsoft.com)
- ARM64: ~120 MB 64: ~225 MB. (support.microsoft.com)
Why this matters: the protection gap explained
When you deploy Windows from an ISO/WIM/VHD that was built weeks or months earlier, the Defender binaries inside that image reflect the Defender platform/engine and signatures that shipped with the image. Immediately after a fresh install there is a window where those binaries are older than what Microsoft is protecting devices with in the wild — attackers can target that window. Updating the installation image itself removes that window for every device produced from that image, because the antimalware binaries come preinstalled with the image rather than waiting for the first online update. Microsoft explicitly recommends a three‑month servicing cadence to keep images reasonably current. (support.microsoft.com)Community and administrative forums have repeatedly flagged the operational impact of stale images (long post‑install update times, patching complexity for offline environments, and security exposure), and this Defender image package is Microsoft’s targeted fix for that class of problem.
How to obtain and apply the update
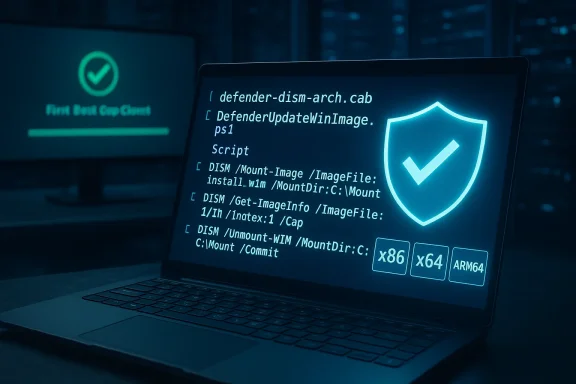
Microsoft publishes the Defender image update packages for x86, x64 and ARM64 architectures. Each download is a zip that contains:- a CAB file with the Defender update (defender-dism-[arch].cab), and
- a PowerShell helper tool, DefenderUpdateWinImage.ps1, to assist offline servicing of WIM/VHD(x) files. (support.microsoft.com)
- A 64‑bit Windows 10 or later host to run the PowerShell script (PowerShell 5.1+).
- The Microsoft.Powershell.Security and DISM modules must be available.
- Run PowerShell with administrative privileges. (support.microsoft.com)
- Inspect the image to determine the ImageIndex you need:
- Dism /get-imageinfo /imagefile:<path_t
 S_Image>
S_Image> - Add the update to the chosen image index using the helper:
- DefenderUpdateWinImage.ps1 -WorkingDirectory <path> -ImageIndex <ImageIndexNumber> -Action AddUpdate -ImagePath <path_t
 s_Image> -Package <To remove the update (if needed for testing/rollback), use:
s_Image> -Package <To remove the update (if needed for testing/rollback), use: - DefenderUpdateWinImage.ps1 -WorkingDirectory <path> -Action RemoveUpdate -ImagePath <path_t
 s_Image>
s_Image> - To list installed updates on an image:
- DefenderUpdateWinImage.ps1 -WorkingDirectory <path> -Action ShowUpdate -ImagePath <path_t
 s_Image>
s_Image>
These commands are the supported path for injecting and verifying the package. Always operate on copies of images and keep backups; Microsoft warns against running this against a live VM’s system image as it can damage a running installation. (support.microsoft.com)
Deployment channels and enterprise delivery options
For organizations that control update delivery centrally, the Defender image packages are available from Microsoft Update services (Microsoft Update Catalog) and can be synchronized via WSUS or imported into your deployment servers. If you operate with System Center Configuration Manager (ConfigMgr/SCCM) or Microsoft Endpoint Manager, you can include the CAB/zip in your image servicing pipelines or pipeline artifacts.Key distribution/management notes:
- Use the Microsoft Update Catalog for offline ingestion and to preserve formal catalog metadata and signing.
- WSUS can be used where online downloads are restricted, but you must configure the appropriate classifications and product selections to surface Defender image packages.
- Many organizations automate WIM/VHD servicing in their image build pipelines (Packer, MDT, custom CI) to ensure the golden image is updated before capture and storage. (support.microsoft.com)
Practical rollout strategy and checklist for imaging teams
The following is a practical, conservative rollout plan that imaging teams can apply:- Inventory: Identify all WIM/VHD images you maintain and catalog architecture and edition indexes.
- Backup: Snapshot or archive a copy of the pre‑serviced image with metadata and checksums.
- Download: Fetch the correct architecture package (x86/x64/ARM64) from the Update Catalog; verify digital signatures and checksums.
- Inject: Use DefenderUpdateWinImage.ps1 to add the package to each image index you plan to deploy.
- Verify: Run DefenderUpdateWinImage.ps1 -Action ShowUpdate and/or mount the image and inspect file versions in the relevant System32 components. Also validate recovery flows if you serviced WinRE.
- Pilot: Build a lab device from the serviced image and validate the OOBE, first boot, and update behavior; ensure Defender reports the expected security intelligence and engine/platform versions after the first boot.
- Automate: Add the download→verify→inject→verify→archive steps to CI so future refreshe Schedule: Repeat every three months (or sooner if an urgent Defender release is published). (support.microsoft.com)
Integration with other dynamic update types (setup / Safe OS)
Microsoft publishes other narrowly scoped packages (Setup Dynamic Updates and Safe OS / WinRE Dynamic Updates) that address setup/runtime and recovery images, respectively. Imaging teams should align Defender image injection with those Safe OS/serviceable updates because they each touch different parts of install and recovery flows. The WinRE packages are often non‑removable once injected and therefore carry stronger rollback obligations; Defender image packages are optional but similarly important for security. Coordinate pilot windows and rollbacks accordingly.Risks, pitfalls, and known cautions
No update is zero‑risk. The important operational caveats are:- Do not run the package on a live installation image inside a running VM — Microsoft explicitly warns this can damage the running Windows instance. Always operate on offline images. (support.microsoft.com)
- Backups are mandatory — once you service images and publish them, you must be able to restore a pre‑serviced golden image if unexpected regressions surface. This is especially critical for Safe OS and some dynamic updates that are effectively irreversible within an image.
- Verification steps are not optional — verify file versions, behavioral checks (OOBE, Defender service start), and connecting to your update infrastructure. A failed injection can cause post‑install issues that are expensive to diagnose at scale. (support.microsoft.com)
- Third‑party AV interactions — if your deployment sequence installs a third‑party AV product during OS setup, test the interaction thoroughly; Defender changes in platform/engine can affect detection and startup timing. Community reports show admins encountering update timing quirks when third‑party security products are also in use.
- Air‑gapped environments — ensure you transport the correct architecture package artifact and its checksum; do not rely on a single offline copy without validation. (support.microsoft.com)
Automation: CI/CD example and verification recipe
For teams that use automated image builds, a recommended pipeline stage (pseudo‑flow):- Stage A: Download latest Defender package zip for each architecture; verify SHA256 and signature.
- Stage B: Extract CAB and DefenderUpdateWinImage.ps1 into artifacts.
- Stage C: Mount the target WIM/VHD as part of the pipeline (or operate on a copy) and run DefenderUpdateWinImage.ps1 -Action AddUpdate -ImagePath <image> -ImageIndex <index> -Package <cab>.
- Stage D: Run DefenderUpdateWinImage.ps1 -Action ShowUpdate and a short set of functional smoke tests: reboot a VM built from the image, confirm Defender service runs, confirm engine/platform versions and security intelligence version using the public APIs or local file version checks.
- Stage E: Archive the new image with a manifest and publish to your image catalog.
- Stage F: If any step fails, fail the build and automatically revert to the archived pre‑serviced image.
What this means for home users and small teams
For individual users or small shops that rarely recapture images, the operational takeaway is simpler: if you install from official ISO media, ensure Windows Update runs promptly after the first boot and confirm Windows Security shows a recent Security Intelligence update. For those who maintain custom ISOs or golden images, plan one image refresh every quarter and inject Microsoft’s Defender image package to eliminate the first‑boot exposure. Community posts indicate many enthusiasts and small IT teams are now adding this step into monthly image refresh routines.Verification artifacts to check after injection
When you’ve injected the Defender package into an image or built a new ISO, validate the following:- Defender client platform and engine versions inside the image match the package metadata (for example, platform 4.18.26010.5 and engine 1.1.26010.1 for the Feb 2026 package). (support.microsoft.com)
- Security intelligence snapshot is present (compare the security intelligence version stamp). (support.microsoft.com)
- Run the DefenderUpdateWinImage.ps1 -Action ShowUpdate output and confirm it lists the package entry. (support.microsoft.com)
- Perform functional checks: Defender service starts on first boot, quick scan runs, Windows Update contact works. A lab pilot build will reveal the majority of integration issues. (support.microsoft.com)
Final analysis: strength, trade‑offs, and recommendations
This Defender image package is a pragmatic, narrowly scoped countermeasure to a real operational problem. Its strengths are clear:- It eliminates the initial protection gap for all devices derived from a serviced image, improving security posture at scale. (support.microsoft.com)
- Microsoft provides a supported tool (DefenderUpdateWinImage.ps1) and CAB packaging to make the process repeatable and automatable. (support.microsoft.com)
- The approach is compatible with central update mechanisms (Update Catalog, WSUS) so enterprise workflows can adopt it without bespoke tooling. (support.microsoft.com)
- Image servicing introduces an extra step in the build pipeline and requires disciplined backups and verification to avoid shipping broken media. (support.microsoft.com)
- Some dynamic updates (Safe OS, Setup) remain non‑removable once injected, which increases the imperative for a robust test/pilot cycle. Coordinate Defender injection with those other updates to avoid surprises.
- Small teams and home users must balance the simplicity of frequent fresh ISO downloads from Microsoft with the effort to service custom images; for many, ensuring Windows Update runs and Defender updates immediately after first boot is an acceptable lower‑effort mitigation.
Conclusion
Microsoft’s targeted Defender update for Windows installation images closes a practical and avoidable security gap by allowing organizations and power users to bake modern antimalware binaries and signatures into install media. The package is straightforward to obtain and apply, but it requires discipline: offline servicing on copies, verification, backups, and a pilot program. For administrators managing fleets, this is a low‑risk, high‑value addition to image hygiene that should become routine — ideally automated into build pipelines and scheduled every three months or more often for high‑security environments. The company’s published guidance and tooling make the technical steps clear; the operational work now falls to imaging teams to incorporate these updates into their established release and deployment practices. (support.microsoft.com)Source: Neowin Microsoft releases new Defender update for Windows 11, 10, Server ISO installations