Dragos’ 2026 Year‑in‑Review makes bluntly clear what industrial defenders have long feared: adversaries are no longer content to merely probe and persist inside industrial networks — they are mapping control loops, handing off footholds to specialized operators, and increasingly engineering ransomware and destructive operations that translate digital access into real‑world disruption. The report, released February 17, 2026, documents a measurable maturation of OT threat ecosystems in 2025 and ties that maturation to concrete operational risk: more threat groups, deeper process‑level understanding by attackers, persistent misclassification of incidents as “IT only,” and glaring visibility gaps that repeatedly make detection and response reactive and prolonged.
Industrial cybersecurity firm Dragos published its ninth annual OT/ICS Year in Review on February 17, 2026, synthesizing telemetry, incident response casework, vendor telemetry, and threat intelligence to produce a threat picture focused on 2025 activity. The core findings are stark:
Dragos documents that adversaries in 2025 deliberately targeted the elements that expose process semantics: engineering workstations, HMIs, variable frequency drives, metering modules, and gateways — effectively reconstructing how an operation actually works. That knowledge shortens the chain from access to physical impact.
Important note on conflicting percentages: some industry coverage reproduced a 64% year‑over‑year increase figure, while Dragos’ own press material and several reputable outlets (Infosecurity, Dragos blog) state a 49% increase. This discrepancy illustrates how aggregations and headline metrics can shift depending on which time windows and inclusion rules are used; the correct approach for defenders is to treat the direction and scale as the signal (significant growth), while verifying exact percentages against original Dragos tables before making actuarial or policy decisions.
Concrete trends to monitor in 2026:
That said, translating Dragos’ recommendations into practice requires organizational commitment: procurement and governance work for cloud and SIEM integrations, investment in OT‑specific telemetry and staff training, and a cultural shift away from IT‑only incident characterization. The report should prompt board‑level attention where industrial downtime, safety consequences, or supply chain interruption can drive real economic and societal harm.
The immediate, pragmatic steps leaders can take today are clear:
Source: Industrial Cyber Dragos 2025 Threat Landscape flags control loop mapping and escalation of OT intent - Industrial Cyber
 Background / Overview
Background / Overview
Industrial cybersecurity firm Dragos published its ninth annual OT/ICS Year in Review on February 17, 2026, synthesizing telemetry, incident response casework, vendor telemetry, and threat intelligence to produce a threat picture focused on 2025 activity. The core findings are stark:- Adversaries progressed from reconnaissance to attempted operational effects, with explicit mapping of control loops (HMIs, field devices, gateways, actuators) to find where a digital action could trigger a physical consequence.
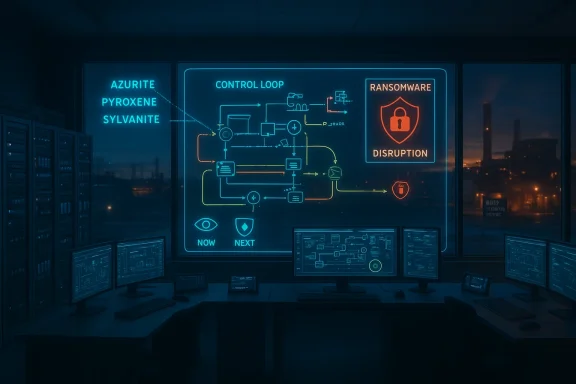
- Dragos added three new OT‑focused threat groups — AZURITE, PYROXENE, and SYLVANITE — expanding its tracked roster to 26 groups, 11 of which were active during 2025.
- Ransomware targeting industrial organizations surged, with Dragos reporting 119 ransomware groups impacting roughly 3,300 industrial victims in 2025. Multiple outlets quoting the report show a year‑over‑year increase (numbers vary slightly by outlet).
- Visibility and telemetry remain the decisive defensive differentiator: organizations with comprehensive OT visibility contained OT ransomware incidents in an average of five days, versus an industry average of 42 days.
Why “control loop mapping” matters
What control loop mapping is — and why attackers want it
A control loop in industrial settings refers to the set of devices and software that sense a physical variable (temperature, pressure, flow), compare that reading to a setpoint, and actuate devices to change the process. Attackers that understand these loops know not just that a device exists, but how commands travel, which interlocks prevent unsafe actions, and what sequences will produce downtime or damage.Dragos documents that adversaries in 2025 deliberately targeted the elements that expose process semantics: engineering workstations, HMIs, variable frequency drives, metering modules, and gateways — effectively reconstructing how an operation actually works. That knowledge shortens the chain from access to physical impact.
The operational risk of loop knowledge
Mapping loops removes a layer of uncertainty for adversaries. Instead of guessing which change will cause an outage, attackers can simulate or test conditions on engineering workstations or extract configuration files and alarm thresholds. Dragos observed groups handing off mapped access to more capable operators — accelerating the breach‑to‑impact timeline and compressing the defender’s window to detect and respond.Ransomware: an OT problem disguised as IT
Scale and targets
Dragos’ Year‑in‑Review attributes a major share of 2025 operational disruption to ransomware activity. The report states Dragos tracked 119 ransomware groups targeting industrial organizations and that roughly 3,300 industrial organizations were impacted in 2025. Manufacturing bore the brunt, accounting for more than two‑thirds of victims in Dragos’ dataset. Independent reporting on the report reproduces those figures and the overall trendline of substantial year‑over‑year growth.Important note on conflicting percentages: some industry coverage reproduced a 64% year‑over‑year increase figure, while Dragos’ own press material and several reputable outlets (Infosecurity, Dragos blog) state a 49% increase. This discrepancy illustrates how aggregations and headline metrics can shift depending on which time windows and inclusion rules are used; the correct approach for defenders is to treat the direction and scale as the signal (significant growth), while verifying exact percentages against original Dragos tables before making actuarial or policy decisions.
Misclassification: why plant shutdowns are labeled “IT incidents”
A frequent pattern Dragos highlights is incident misclassification. When Windows servers, VMware hypervisors, or engineering workstations hosting SCADA/HMI software are impacted, organizations or responders without OT context often call these IT incidents. That understates the operational risk and can cause mis‑prioritization of mitigations, playbooks, and legal or regulatory reporting. Dragos’ incident engagements and insurance actuarial data suggest this mislabeling is widespread enough to obscure how frequently OT operations are truly affected.Threat actor dynamics: specialization and ecosystems
New actors, division of labor
Dragos’ 2025 dataset surfaced three new OT‑focused groups — AZURITE (engineering‑workstation targeting and data exfiltration), PYROXENE (supply‑chain and social engineering), and SYLVANITE (initial access/rapid exploitation broker) — and describes operational relationships where some groups gain access and others exploit it for OT effects. This specialization resembles criminal ecosystems in ransomware but applied to process‑aware intrusion.Advanced operators and destructive tools
Established disruptive actors — named in Dragos material as KAMACITE, ELECTRUM, VOLTZITE and others — displayed expanded capabilities in 2025, including wipers, targeted attacks on distributed energy resources, and manipulation of engineering workstation software to extract configuration and alarm logic. These behaviors are consistent with deliberate attempts to find operational leverage rather than merely to gain persistence or exfiltrate data.Vulnerability and asset‑management problems
Dragos flags systemic issues in vulnerability scoring and vendor advisories that complicate prioritization:- Dragos found ~25% of ICS‑CERT and NVD entries had incorrect CVSS scores in 2025 and that ~26% of advisories lacked vendor patches or mitigations. Only ~2% of ICS‑relevant vulnerabilities qualified as “Now” in Dragos’ risk‑based “Now, Next, Never” model.
BESS and grid‑adjacent exposure
Dragos’ research into battery energy storage systems (BESS) surfaced authentication bypass and command injection vulnerabilities and identified over 100 internet‑exposed devices, including ~1MW inverters capable of supplying grid power. As utilities and industrial operators adopt distributed energy resources, these Internet‑exposed control planes become attractive leverage points that can bridge cyber events to grid‑level effects.Defensive gains and where they work
The report is not all doom. Dragos documents measurable defensive wins tied to concrete capabilities:- Organizations with comprehensive OT visibility contained OT ransomware incidents in an average of five days versus a 42‑day industry average — a dramatic reduction in dwell and recovery time.
- Incident patterns show that when ICS‑aware telemetry and historical logging are available, root‑cause analysis is faster and less speculative; conversely, missing telemetry translates to long outages and longer forensic timelines.
Root causes: why defenders keep losing the time advantage
Dragos’ analysis points to several persistent defensive deficits:- Incomplete asset inventories and blind spots in telemetry make it trivial for attackers to establish persistence and reconnoiter control loops without being seen.
- Weak privileged credentials, poorly managed hypervisor access, and exposed internet‑facing OT assets provide high‑leverage entry points. Dragos saw attackers exploit ESXi/hypervisors and OT support servers to amplify impact.
- Organizational divides between IT and OT lead to misclassification and misaligned incident response, which delays appropriate containment and remediation.
Critical analysis: strengths, gaps, and what to watch
Strengths of the Dragos dataset and thesis
- OT‑native telemetry and incident experience. Dragos’ conclusions are grounded in platform telemetry, practitioner incident response cases, and insurance actuarial inputs — a blend that ties technical findings to operational consequence. That makes their emphasis on process‑level understanding credible.
- Actionable prioritization. The “Now, Next, Never” model and the explicit call for ICS‑specific detection engineering shift the conversation from generic hygiene checklists to consequence‑oriented defense.
- Visibility as a measurable lever. The empirical gap in containment time between organizations with and without OT visibility is a clear, defensible metric that leaders can translate into investment cases.
Limitations and caveats
- Attribution and headline metrics can vary. As noted, different outlets and summaries reported different percentage increases (49% vs 64%) for ransomware growth; such variance may result from differing inclusion rules (e.g., which groups are counted as “ransomware,” time windows, or duplication in tallies). Decision makers should inspect Dragos’ tables and methodology directly when precise figures drive governance or insurance decisions.
- Sampling and reporting bias. No industry dataset perfectly captures every incident; industrial incidents are often underreported for commercial or regulatory reasons. Dragos’ dataset is large and OT‑focused, but defenders should combine multiple telemetry and public sources to form policy.
- Operationalizing recommendations is hard. Dragos’ prescriptions — inventories, meaningful telemetry, ICS‑aware detection — are operationally heavy. Many asset owners face procurement, staffing, and change‑control obstacles that slow adoption. Integrating OT telemetry into enterprise SOCs without safe operational guardrails can introduce new risks; technical integration plans must include strict role separation and manual‑first runbooks for any automated response to OT incidents.
Practical defenses: a prioritized blueprint
Below is a defensible, prioritized roadmap for industrial defenders that aligns with Dragos’ findings and translates them into executable steps.- Establish and validate an authoritative OT asset inventory
- Identify engineering workstations, HMIs, historians, hypervisors, RTUs, PLCs, gateways, and cloud‑connected BESS/inverters.
- Treat engineering workstations and HMIs as high‑value operational assets, not ordinary IT endpoints.
- Deploy process‑aware telemetry and historical collection
- Collect flow/temperature/alarm/command traces and preserve sufficient retention for multiday forensic timelines.
- Ensure telemetry includes industrial protocols (Modbus, DNP3, IEC104, etc.) and contextual mappings to asset models.
- Implement ICS‑specific detection engineering
- Build analytic rules that understand control sequences, not just file‑based IOCs.
- Prioritize detections that indicate anomalous control commands, unexpected engineering‑tool activity, or alarm suppression.
- Harden boundary systems and hypervisors
- Restrict management access to ESXi and other hypervisors with zero‑trust access controls and multi‑factor authentication.
- Monitor and log hypervisor console access and snapshot operations.
- Treat vulnerability advisories with operational impact analysis
- Map CVEs to the process impact (loss of view, loss of control, safety risk) rather than just CVSS.
- Use a “Now, Next, Never” triage to schedule maintenance windows rationally.
- Run multidisciplinary drills and playbooks
- Execute IR exercises that include OT engineers, process owners, legal, procurement, and insurers.
- Test recovery from ransomware and destructive orchestration in a controlled manner.
- Vet third parties and cloud integrations
- Require transparency on third‑party telemetry pipelines, supply chain CI/CD controls, and data residency for OT telemetry pipelines.
- Share and consume trusted OT intelligence
- Participate in sector‑specific information sharing and validate operational indicators that imply control‑loop targeting.
The cloud, SIEM integrations, and governance
Integrating OT telemetry into enterprise SIEMs and cloud analytics is a logical evolution for scaling detection, hunting, and metrics. But integration is not frictionless.- Dragos and multiple analyst briefings emphasize that cloud/SIEM integrations must preserve OT context (asset models, process impact, playbooks) and must be accompanied by governance controls about automated actions and data residency. Mistakes here can cause unsafe automation or leak sensitive process data.
- Practical procurement questions defenders should insist on include: which telemetry types are forwarded to the cloud; what controls limit automated responses; encryption and retention guarantees; and whether the integration supports role separation to prevent unsafe cross‑domain actions.
What to expect in 2026
Dragos’ report closes with forward‑looking admonitions: expect continued targeting of ICS‑adjacent technologies, sustained ransomware pressure with OT consequences, and increased exploitation of distributed energy resources and AI‑enabled operational tools where blind spots persist. The firm advises defenders to prioritize attack‑surface reduction but to accept that detection capability and operational context will determine whether intrusions are interrupted before physical harm.Concrete trends to monitor in 2026:
- Con initial‑access brokers and OT operators will increasingly collaborate or trade access.
- Energy and grid adjacency: BESS, inverters, and microgrid controllers will remain high‑value targets as utilities decarbonize and decentralize.
- Hypervisor and virtualization targeting: attackers will continue to exploit hypervisor pathways for maximum lateral impact.
- Misclassification of incidents will remain a systemic problem unless organizations embed OT expertise into detection and incident classification processes.
Final assessment and call to action
Dragos’ 2026 Year‑in‑Review is both a warning and a playbook. Its central thesis — that adversaries now understand industrial operations at the process level and are using that knowledge to escalate from intrusion to attempted operational impact — is supported by multi‑modal evidence in the report and mirrored across independent industry coverage. The defensive implication is unambiguous: visibility, asset context, and ICS‑aware detection engineering are not optional. Investing in these capabilities materially shortens recovery times and reduces operational exposure.That said, translating Dragos’ recommendations into practice requires organizational commitment: procurement and governance work for cloud and SIEM integrations, investment in OT‑specific telemetry and staff training, and a cultural shift away from IT‑only incident characterization. The report should prompt board‑level attention where industrial downtime, safety consequences, or supply chain interruption can drive real economic and societal harm.
The immediate, pragmatic steps leaders can take today are clear:
- Validate an authoritative OT asset inventory.
- Collect process and protocol telemetry with sufficient retention for forensic analysis.
- Treat engineering workstations, HMIs, and hypervisors as high‑value assets requiring hardened access controls and monitoring.
- Adopt a risk‑based vulnerability prioritization that factors operational consequence over raw CVSS.
- Run multidisciplinary drills that test not just IT recovery but OT recovery and safe human procedures.
Source: Industrial Cyber Dragos 2025 Threat Landscape flags control loop mapping and escalation of OT intent - Industrial Cyber