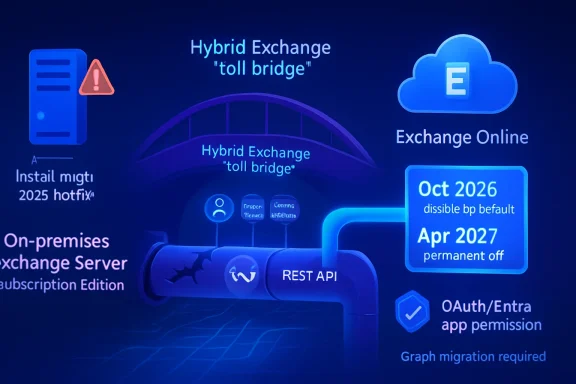
Microsoft is now telling Exchange Server Subscription Edition hybrid customers that, by October 2026 and no later than April 2027, they must install the May 2026 hotfix or newer and move rich coexistence calls from Exchange Web Services to Microsoft Graph. This is not a cosmetic plumbing change for the Exchange faithful. It is Microsoft turning a long-signaled API retirement into an operational deadline for hybrid shops that still depend on on-premises mailboxes. The message is blunt: if your coexistence story still runs through EWS, the clock is now louder than the calendar.
For years, Exchange hybrid has lived in a carefully balanced compromise. Organizations could keep some mailboxes on-premises, move others to Exchange Online, and still offer the everyday connective tissue users expect: free/busy lookups, MailTips, and profile photo sharing across the boundary. That “rich coexistence” layer was never glamorous, but it made hybrid feel less like two mail systems taped together.
The new Exchange Team guidance makes clear that this layer is being rebuilt around Microsoft Graph. Stage 1 of Microsoft’s hybrid security work, completed in October 2025, pushed customers toward a dedicated Exchange hybrid application in Microsoft Entra ID. Stage 2 is the bigger architectural turn: deprecating EWS calls for hybrid coexistence and replacing them with REST-based Graph API calls.
That sounds neat in a roadmap slide. In the real world, it means hybrid administrators now have two overlapping migrations to reconcile. They must be on Exchange Server Subscription Edition, they must install the May 2026 hotfix update or a later update, and they must rework the dedicated hybrid application’s permissions so the model is more granular than the broad EWS permission set used in the first stage.
The key word is granular. Microsoft’s security argument is that hybrid should no longer rely on a shared first-party service principal or overly broad EWS app permissions. A tenant-owned app with Graph permissions narrows the blast radius and gives administrators more direct control. That is the right direction, but it arrives with the usual Microsoft 365 trade-off: stronger identity boundaries, paid for in operational churn.
Starting in October 2026, EWS in Exchange Online begins being turned off by default. By April 2027, it is permanently disabled in Exchange Online. For cloud-only developers and SaaS vendors, that is already a major migration event. For hybrid Exchange customers, it is worse because the protocol being retired is also part of the bridge between two worlds.
Microsoft is careful to say that not every rich coexistence scenario is fully supported yet and that not every cloud environment may support Graph hybrid calls immediately. That caveat matters. It means the technically correct answer is not simply “turn on Graph tomorrow.” The better reading is that Microsoft has opened the lane for supported scenarios, and administrators need to begin testing while keeping a close eye on documented parity.
Still, the direction is irreversible. Hybrid Exchange has always depended on Microsoft maintaining a shared understanding of identity, OAuth, Autodiscover, and mailbox location. Once Exchange Online stops accepting EWS, the on-premises side must speak the cloud’s newer language. Microsoft is not offering Exchange 2016 or Exchange 2019 a translator.
That creates a hard distinction between being “still running” and being “still viable.” An Exchange 2019 server might continue to route mail, host mailboxes, and survive on inertia. But if it cannot perform Graph-based hybrid coexistence calls after Exchange Online turns off EWS, it no longer supports the hybrid user experience many organizations assume they have.
For admins who treat Exchange on-premises as a management server, the impact may be limited. If there are no on-premises mailboxes and no need for cross-premises Free/Busy, MailTips, or profile photos, the dedicated hybrid app may not be central to daily operations. But if the organization still hosts mailboxes locally, this is no longer a theoretical modernization project.
The deadline has an awkward two-step shape. Customers on unsupported Exchange versions who still need coexistence can keep allowing EWS past October 2026, buying time through the default-disablement phase. But April 2027 is the wall. Once EWS is permanently removed from Exchange Online, those unsupported on-premises deployments lose rich coexistence permanently unless they have moved to Exchange SE.
This is Microsoft’s preferred enforcement model: not a single dramatic cutoff, but an ecosystem dependency that slowly stops accommodating the old thing. The server may boot. The mailbox database may mount. The users may still send mail. But the hybrid fabric frays until the business case writes itself.
Under the Stage 1 model, the dedicated app still used EWS permissions. Microsoft’s documentation framed this as transitional: the broad EWS permission mirrored what the shared service principal already had, while moving ownership of the app into the customer tenant. That reduced dependence on Microsoft’s shared first-party configuration, but it did not eliminate the old API.
Stage 2 finishes that sentence. Once Exchange SE has the required update, administrators can shift the hybrid workflow to Graph and replace the more permissive EWS model with a more specific Graph permission set. This is where the security design becomes more convincing. It is not just “same access, different app.” It is a narrower app model aligned with the API Microsoft intends to keep.
The complexity is that this sequence depends on order. Install the Exchange SE update across on-premises servers first. Then follow Microsoft’s documentation to enable the Graph workflow for supported scenarios. Then verify that the right app ID, permissions, and OAuth behavior are actually in use. This is not the kind of change to make from a hotel Wi-Fi connection during a maintenance window that already includes a cumulative update.
Hybrid shops with multiple forests or multiple tenants need even more care. Dedicated apps may need to be created per tenant or per Exchange organization, and certificate cleanup cannot be treated casually while older servers remain in play. The operational shape is familiar to Exchange veterans: identity changes are easy to type, hard to reverse, and very unforgiving when half the estate is in one state and half is in another.
Graph is not magic, and it is not automatically safer simply because it is newer. But Graph sits inside Microsoft’s current identity, consent, permission, auditing, and conditional access strategy. It is where Microsoft is concentrating engineering attention. From a risk-management perspective, keeping Exchange Online tied to EWS indefinitely would mean preserving a legacy access path precisely when Microsoft is trying to shrink them.
The dedicated hybrid app also gives customers more explicit ownership. Instead of relying on a shared service principal arrangement, organizations get a tenant-specific application they can manage, audit, and eventually constrain. For larger enterprises, that matters. Security teams are increasingly suspicious of inherited trust relationships they cannot easily explain to auditors.
But Microsoft’s messaging still has a habit of making these changes sound cleaner than administrators experience them. “Install the update and follow the documentation” hides a lot of work: change control, coexistence testing, Entra permissions, firewall rules, outbound connectivity to Graph endpoints, certificate state, HCW behavior, and user-impact validation. The Exchange Team is right to push the ecosystem away from EWS. It should also be honest that hybrid customers are being asked to modify one of the most sensitive seams in their messaging environment.
Free/Busy failures become scheduling confusion. MailTips failures become avoidable mistakes. Profile photo inconsistencies become another visible sign that “the system” is unreliable. None of these is as dramatic as a database dismounting, but they generate the kind of low-grade help desk noise that makes IT look careless.
That is why rich coexistence matters. Hybrid deployments are often long-lived not because organizations love complexity, but because business constraints make full cloud migration slow. Regulatory requirements, application dependencies, latency, mergers, divestitures, and political compromises all keep mailboxes on-premises longer than cloud-first roadmaps expect.
Microsoft’s announcement effectively says that long-lived hybrid is still allowed, but only if it keeps up with the cloud control plane. Exchange SE is the supported on-premises anchor. Graph is the supported API path into Exchange Online. Everything else is borrowed time.
For administrators, the safest approach is to treat this as a user-experience migration, not just an API migration. Test cross-premises calendar lookups. Test MailTips. Test photos. Test from different mailbox locations, different Outlook clients, and different network paths. The failure mode may not announce itself as “Graph hybrid workflow misconfigured.” It may arrive as an executive assistant unable to schedule a meeting with someone who moved to the cloud three years ago.
Many organizations have kept older Exchange servers around because the immediate cost of change looked larger than the immediate risk of staying put. Extended Security Updates can reinforce that thinking by making unsupported feel negotiable. Microsoft’s Graph hybrid cutoff undermines the comfort of that middle ground.
ESU may address selected security exposure, but it does not deliver the new hybrid API stack. That distinction is crucial. Security updates keep a server less vulnerable; they do not make it architecturally current. If the cloud side requires Graph for rich coexistence and the on-premises side cannot produce it, no patch-only strategy solves the problem.
This also affects migration planning. An organization that intended to “ride out” Exchange 2019 while slowly moving mailboxes online must now ask whether coexistence degradation is acceptable during that period. If not, Exchange SE becomes a prerequisite for maintaining the bridge. If yes, the business must knowingly accept that the hybrid experience will deteriorate after April 2027.
That is a governance decision, not just an Exchange admin decision. The technical owner can describe the risk. The business owner must decide whether stale hybrid infrastructure is worth the visible friction users will experience.
Patch hygiene comes first. Every on-premises Exchange SE server participating in the relevant hybrid workflow needs to be brought to the required level. Mixed states are where administrators get hurt, especially when authentication and organization-wide settings are involved. A lab or pilot environment is not optional for cautious shops; it is the place to discover whether the documented happy path matches your topology.
Then comes application permission work. The dedicated Exchange hybrid app must move from the transitional EWS permission model to the more granular Graph model. That usually means coordination between Exchange admins and Entra admins, because the people who understand hybrid coexistence are not always the people allowed to grant tenant-wide admin consent.
Finally, validation has to be practical rather than ceremonial. A green command output is useful, but it is not the same as proving that real users can retrieve availability across the hybrid boundary. The best test plan will include both protocol verification and human workflow checks.
The timing matters. October 2026 is close in enterprise change-management terms, particularly for organizations with year-end freezes, regulated maintenance windows, or outsourced messaging operations. April 2027 sounds farther away, but it is the date after which there is no EWS fallback in Exchange Online. If procurement, testing, and server upgrades are not already on the calendar, the calendar is now part of the risk.
That does not mean administrators should wait. Waiting for perfect parity is how organizations end up discovering dependencies during a service retirement. It does mean they should map which coexistence scenarios matter in their environment and match those scenarios against Microsoft’s current support statements before flipping switches in production.
Cloud environment support is another wrinkle. Commercial Microsoft 365 tenants generally see features first, while government and sovereign clouds often move on different timelines. Hybrid organizations in those environments should assume that the public roadmap needs verification against their actual tenant and documentation set.
This is where Microsoft’s staged approach helps. October 2026 begins default disablement; April 2027 is permanent retirement. The gap gives organizations a short runway to identify what still depends on EWS and, where absolutely necessary, manage the temporary exception. But the word temporary is doing a lot of work. The exception is a bridge, not a strategy.
But the harder work is organizational. Someone needs to identify whether the business actually still requires on-premises mailboxes. Someone needs to decide whether Exchange SE is the long-term platform or merely the last stepping stone to Exchange Online. Someone needs to inventory EWS dependencies beyond hybrid itself, including backup products, archiving tools, migration utilities, custom line-of-business integrations, and forgotten service accounts.
That inventory is often ugly. EWS usage may not be obvious from a product name or an admin portal. Vendors may say they are “working on Graph support” without committing to the exact scenario you use. Internal scripts may have been written by employees who left years ago. A deprecation deadline has a way of turning institutional memory into a ticket queue.
The Exchange hybrid Graph change should therefore be folded into a broader EWS retirement program. If the organization only fixes rich coexistence and ignores every other EWS consumer, October 2026 will still be painful. Microsoft’s hybrid announcement is one chapter in a larger API retirement, not a carve-out from it.
There is also a communication problem. Users do not care whether Free/Busy failed because of EWS, Graph, OAuth, Entra app permissions, or a missing hotfix. They care that scheduling broke. IT should prepare business stakeholders for testing windows and possible coexistence anomalies, not because failure is inevitable, but because silence makes any failure look like negligence.
For many organizations, that is reasonable. Hybrid was never supposed to be a museum exhibit for old server builds. If a company wants the cloud service to interoperate with local mailboxes, it should expect to keep the local side aligned with the cloud’s security model.
For others, this will feel like coercion. Exchange administrators who have spent years stabilizing an on-premises deployment may see Graph as another cloud-first requirement imposed on infrastructure that used to be more self-contained. They are not wrong to feel the squeeze. Microsoft’s cloud cadence increasingly dictates what “supported” means even inside the data center.
The practical answer is not nostalgia. It is planning. Hybrid customers should decide now whether they are maintaining hybrid as a strategic architecture or simply delaying a full migration. If hybrid is strategic, Exchange SE and Graph coexistence are table stakes. If hybrid is temporary, the organization needs a mailbox migration timeline that beats April 2027 without depending on wishful thinking.
Source: Microsoft Exchange Team Blog Update Your Exchange SE Hybrid On-premises Rich Coexistence to Graph | Microsoft Community Hub
 Microsoft Turns Hybrid Coexistence Into a Graph Migration
Microsoft Turns Hybrid Coexistence Into a Graph Migration
For years, Exchange hybrid has lived in a carefully balanced compromise. Organizations could keep some mailboxes on-premises, move others to Exchange Online, and still offer the everyday connective tissue users expect: free/busy lookups, MailTips, and profile photo sharing across the boundary. That “rich coexistence” layer was never glamorous, but it made hybrid feel less like two mail systems taped together.The new Exchange Team guidance makes clear that this layer is being rebuilt around Microsoft Graph. Stage 1 of Microsoft’s hybrid security work, completed in October 2025, pushed customers toward a dedicated Exchange hybrid application in Microsoft Entra ID. Stage 2 is the bigger architectural turn: deprecating EWS calls for hybrid coexistence and replacing them with REST-based Graph API calls.
That sounds neat in a roadmap slide. In the real world, it means hybrid administrators now have two overlapping migrations to reconcile. They must be on Exchange Server Subscription Edition, they must install the May 2026 hotfix update or a later update, and they must rework the dedicated hybrid application’s permissions so the model is more granular than the broad EWS permission set used in the first stage.
The key word is granular. Microsoft’s security argument is that hybrid should no longer rely on a shared first-party service principal or overly broad EWS app permissions. A tenant-owned app with Graph permissions narrows the blast radius and gives administrators more direct control. That is the right direction, but it arrives with the usual Microsoft 365 trade-off: stronger identity boundaries, paid for in operational churn.
EWS Has Finally Run Out of Calendar
Exchange Web Services has been dying slowly for almost a decade. Microsoft stopped investing in new EWS functionality years ago, then told developers to move toward Graph, then began filling enough Graph gaps to make the retirement credible. The newest dates remove the last ambiguity.Starting in October 2026, EWS in Exchange Online begins being turned off by default. By April 2027, it is permanently disabled in Exchange Online. For cloud-only developers and SaaS vendors, that is already a major migration event. For hybrid Exchange customers, it is worse because the protocol being retired is also part of the bridge between two worlds.
Microsoft is careful to say that not every rich coexistence scenario is fully supported yet and that not every cloud environment may support Graph hybrid calls immediately. That caveat matters. It means the technically correct answer is not simply “turn on Graph tomorrow.” The better reading is that Microsoft has opened the lane for supported scenarios, and administrators need to begin testing while keeping a close eye on documented parity.
Still, the direction is irreversible. Hybrid Exchange has always depended on Microsoft maintaining a shared understanding of identity, OAuth, Autodiscover, and mailbox location. Once Exchange Online stops accepting EWS, the on-premises side must speak the cloud’s newer language. Microsoft is not offering Exchange 2016 or Exchange 2019 a translator.
Exchange SE Becomes the Toll Booth
The most consequential part of the announcement is not Graph itself. It is the line that Exchange 2016 and Exchange 2019 will not receive this Graph hybrid capability, even under Extended Security Updates. Those versions are already out of support, and Microsoft is using the EWS retirement to make that status operationally unavoidable.That creates a hard distinction between being “still running” and being “still viable.” An Exchange 2019 server might continue to route mail, host mailboxes, and survive on inertia. But if it cannot perform Graph-based hybrid coexistence calls after Exchange Online turns off EWS, it no longer supports the hybrid user experience many organizations assume they have.
For admins who treat Exchange on-premises as a management server, the impact may be limited. If there are no on-premises mailboxes and no need for cross-premises Free/Busy, MailTips, or profile photos, the dedicated hybrid app may not be central to daily operations. But if the organization still hosts mailboxes locally, this is no longer a theoretical modernization project.
The deadline has an awkward two-step shape. Customers on unsupported Exchange versions who still need coexistence can keep allowing EWS past October 2026, buying time through the default-disablement phase. But April 2027 is the wall. Once EWS is permanently removed from Exchange Online, those unsupported on-premises deployments lose rich coexistence permanently unless they have moved to Exchange SE.
This is Microsoft’s preferred enforcement model: not a single dramatic cutoff, but an ecosystem dependency that slowly stops accommodating the old thing. The server may boot. The mailbox database may mount. The users may still send mail. But the hybrid fabric frays until the business case writes itself.
The Dedicated Hybrid App Was the Setup, Not the Finish Line
Stage 1 was easy to misunderstand. Creating a dedicated Exchange hybrid application in Entra ID looked, to many admins, like the security fix. In practice, it was the staging ground for the bigger protocol shift.Under the Stage 1 model, the dedicated app still used EWS permissions. Microsoft’s documentation framed this as transitional: the broad EWS permission mirrored what the shared service principal already had, while moving ownership of the app into the customer tenant. That reduced dependence on Microsoft’s shared first-party configuration, but it did not eliminate the old API.
Stage 2 finishes that sentence. Once Exchange SE has the required update, administrators can shift the hybrid workflow to Graph and replace the more permissive EWS model with a more specific Graph permission set. This is where the security design becomes more convincing. It is not just “same access, different app.” It is a narrower app model aligned with the API Microsoft intends to keep.
The complexity is that this sequence depends on order. Install the Exchange SE update across on-premises servers first. Then follow Microsoft’s documentation to enable the Graph workflow for supported scenarios. Then verify that the right app ID, permissions, and OAuth behavior are actually in use. This is not the kind of change to make from a hotel Wi-Fi connection during a maintenance window that already includes a cumulative update.
Hybrid shops with multiple forests or multiple tenants need even more care. Dedicated apps may need to be created per tenant or per Exchange organization, and certificate cleanup cannot be treated casually while older servers remain in play. The operational shape is familiar to Exchange veterans: identity changes are easy to type, hard to reverse, and very unforgiving when half the estate is in one state and half is in another.
The Security Argument Is Stronger Than the Messaging
Microsoft’s case for moving away from EWS is not merely about developer fashion. EWS is old, broad, and deeply embedded in automation, third-party tools, and Microsoft’s own legacy integrations. In modern cloud identity terms, that is a problem. APIs with wide permissions and long tails are exactly where attackers, misconfigured apps, and forgotten service accounts tend to congregate.Graph is not magic, and it is not automatically safer simply because it is newer. But Graph sits inside Microsoft’s current identity, consent, permission, auditing, and conditional access strategy. It is where Microsoft is concentrating engineering attention. From a risk-management perspective, keeping Exchange Online tied to EWS indefinitely would mean preserving a legacy access path precisely when Microsoft is trying to shrink them.
The dedicated hybrid app also gives customers more explicit ownership. Instead of relying on a shared service principal arrangement, organizations get a tenant-specific application they can manage, audit, and eventually constrain. For larger enterprises, that matters. Security teams are increasingly suspicious of inherited trust relationships they cannot easily explain to auditors.
But Microsoft’s messaging still has a habit of making these changes sound cleaner than administrators experience them. “Install the update and follow the documentation” hides a lot of work: change control, coexistence testing, Entra permissions, firewall rules, outbound connectivity to Graph endpoints, certificate state, HCW behavior, and user-impact validation. The Exchange Team is right to push the ecosystem away from EWS. It should also be honest that hybrid customers are being asked to modify one of the most sensitive seams in their messaging environment.
The Risk Is Not Mail Flow, It Is User Trust
The first instinct in any Exchange change is to ask whether mail will flow. In this case, that may be the wrong starting point. The affected features are the small conveniences that make users believe the migration already happened cleanly.Free/Busy failures become scheduling confusion. MailTips failures become avoidable mistakes. Profile photo inconsistencies become another visible sign that “the system” is unreliable. None of these is as dramatic as a database dismounting, but they generate the kind of low-grade help desk noise that makes IT look careless.
That is why rich coexistence matters. Hybrid deployments are often long-lived not because organizations love complexity, but because business constraints make full cloud migration slow. Regulatory requirements, application dependencies, latency, mergers, divestitures, and political compromises all keep mailboxes on-premises longer than cloud-first roadmaps expect.
Microsoft’s announcement effectively says that long-lived hybrid is still allowed, but only if it keeps up with the cloud control plane. Exchange SE is the supported on-premises anchor. Graph is the supported API path into Exchange Online. Everything else is borrowed time.
For administrators, the safest approach is to treat this as a user-experience migration, not just an API migration. Test cross-premises calendar lookups. Test MailTips. Test photos. Test from different mailbox locations, different Outlook clients, and different network paths. The failure mode may not announce itself as “Graph hybrid workflow misconfigured.” It may arrive as an executive assistant unable to schedule a meeting with someone who moved to the cloud three years ago.
Unsupported Exchange Is Now a Business Continuity Problem
Exchange 2016 and 2019 being out of support is not news. What is new is that Microsoft has tied a future Exchange Online service behavior to functionality those products will never receive. That changes the conversation with management.Many organizations have kept older Exchange servers around because the immediate cost of change looked larger than the immediate risk of staying put. Extended Security Updates can reinforce that thinking by making unsupported feel negotiable. Microsoft’s Graph hybrid cutoff undermines the comfort of that middle ground.
ESU may address selected security exposure, but it does not deliver the new hybrid API stack. That distinction is crucial. Security updates keep a server less vulnerable; they do not make it architecturally current. If the cloud side requires Graph for rich coexistence and the on-premises side cannot produce it, no patch-only strategy solves the problem.
This also affects migration planning. An organization that intended to “ride out” Exchange 2019 while slowly moving mailboxes online must now ask whether coexistence degradation is acceptable during that period. If not, Exchange SE becomes a prerequisite for maintaining the bridge. If yes, the business must knowingly accept that the hybrid experience will deteriorate after April 2027.
That is a governance decision, not just an Exchange admin decision. The technical owner can describe the risk. The business owner must decide whether stale hybrid infrastructure is worth the visible friction users will experience.
The May 2026 Hotfix Is a Starting Gun
The immediate action item is straightforward: Exchange SE servers need the May 2026 hotfix update or newer before the Graph hybrid workflow can be enabled. But treating the hotfix as the project is a mistake. The update is the starting gun.Patch hygiene comes first. Every on-premises Exchange SE server participating in the relevant hybrid workflow needs to be brought to the required level. Mixed states are where administrators get hurt, especially when authentication and organization-wide settings are involved. A lab or pilot environment is not optional for cautious shops; it is the place to discover whether the documented happy path matches your topology.
Then comes application permission work. The dedicated Exchange hybrid app must move from the transitional EWS permission model to the more granular Graph model. That usually means coordination between Exchange admins and Entra admins, because the people who understand hybrid coexistence are not always the people allowed to grant tenant-wide admin consent.
Finally, validation has to be practical rather than ceremonial. A green command output is useful, but it is not the same as proving that real users can retrieve availability across the hybrid boundary. The best test plan will include both protocol verification and human workflow checks.
The timing matters. October 2026 is close in enterprise change-management terms, particularly for organizations with year-end freezes, regulated maintenance windows, or outsourced messaging operations. April 2027 sounds farther away, but it is the date after which there is no EWS fallback in Exchange Online. If procurement, testing, and server upgrades are not already on the calendar, the calendar is now part of the risk.
Graph Parity Remains the Uncomfortable Caveat
Microsoft’s own warning that not all rich coexistence scenarios are fully supported yet deserves attention. Graph has grown enormously, but Exchange has decades of edge cases, and hybrid Exchange has some of the strangest. The reality is that not every feature path moves at the same speed.That does not mean administrators should wait. Waiting for perfect parity is how organizations end up discovering dependencies during a service retirement. It does mean they should map which coexistence scenarios matter in their environment and match those scenarios against Microsoft’s current support statements before flipping switches in production.
Cloud environment support is another wrinkle. Commercial Microsoft 365 tenants generally see features first, while government and sovereign clouds often move on different timelines. Hybrid organizations in those environments should assume that the public roadmap needs verification against their actual tenant and documentation set.
This is where Microsoft’s staged approach helps. October 2026 begins default disablement; April 2027 is permanent retirement. The gap gives organizations a short runway to identify what still depends on EWS and, where absolutely necessary, manage the temporary exception. But the word temporary is doing a lot of work. The exception is a bridge, not a strategy.
The Admin Work Is Smaller Than the Organizational Work
The PowerShell steps will get most of the attention because they are concrete. Run the script. Update the app. Install the hotfix. Verify OAuth. Refresh configuration. Those steps matter, and getting them wrong can break things.But the harder work is organizational. Someone needs to identify whether the business actually still requires on-premises mailboxes. Someone needs to decide whether Exchange SE is the long-term platform or merely the last stepping stone to Exchange Online. Someone needs to inventory EWS dependencies beyond hybrid itself, including backup products, archiving tools, migration utilities, custom line-of-business integrations, and forgotten service accounts.
That inventory is often ugly. EWS usage may not be obvious from a product name or an admin portal. Vendors may say they are “working on Graph support” without committing to the exact scenario you use. Internal scripts may have been written by employees who left years ago. A deprecation deadline has a way of turning institutional memory into a ticket queue.
The Exchange hybrid Graph change should therefore be folded into a broader EWS retirement program. If the organization only fixes rich coexistence and ignores every other EWS consumer, October 2026 will still be painful. Microsoft’s hybrid announcement is one chapter in a larger API retirement, not a carve-out from it.
There is also a communication problem. Users do not care whether Free/Busy failed because of EWS, Graph, OAuth, Entra app permissions, or a missing hotfix. They care that scheduling broke. IT should prepare business stakeholders for testing windows and possible coexistence anomalies, not because failure is inevitable, but because silence makes any failure look like negligence.
The Hybrid Bridge Now Has a Toll Schedule
The most concrete reading of Microsoft’s announcement is that hybrid Exchange remains supported, but the terms have changed. The bridge still exists, but Microsoft is charging an architectural toll: Exchange SE, current updates, a dedicated tenant app, and Graph permissions.For many organizations, that is reasonable. Hybrid was never supposed to be a museum exhibit for old server builds. If a company wants the cloud service to interoperate with local mailboxes, it should expect to keep the local side aligned with the cloud’s security model.
For others, this will feel like coercion. Exchange administrators who have spent years stabilizing an on-premises deployment may see Graph as another cloud-first requirement imposed on infrastructure that used to be more self-contained. They are not wrong to feel the squeeze. Microsoft’s cloud cadence increasingly dictates what “supported” means even inside the data center.
The practical answer is not nostalgia. It is planning. Hybrid customers should decide now whether they are maintaining hybrid as a strategic architecture or simply delaying a full migration. If hybrid is strategic, Exchange SE and Graph coexistence are table stakes. If hybrid is temporary, the organization needs a mailbox migration timeline that beats April 2027 without depending on wishful thinking.
The Dates That Should Be on Every Exchange Change Board
This is the part of the story that belongs in CAB decks, budget meetings, and risk registers. The details are technical, but the consequences are operational.- Stage 1 of Microsoft’s hybrid security shift finished in October 2025, requiring hybrid customers with on-premises mailboxes and rich coexistence needs to create the dedicated Exchange hybrid application.
- Stage 2 is now underway, moving supported hybrid rich coexistence calls away from EWS and onto Microsoft Graph.
- Exchange SE servers need the May 2026 hotfix update or a later update before administrators enable the Graph hybrid workflow for supported scenarios.
- Exchange 2016 and Exchange 2019 will not receive the Graph hybrid capability, even through Extended Security Updates.
- EWS starts being disabled by default in Exchange Online in October 2026 and is permanently disabled in April 2027.
- Organizations that still need on-premises mailboxes with rich coexistence must either upgrade to Exchange SE and move to Graph or accept that those features will stop working when the final EWS cutoff arrives.
Source: Microsoft Exchange Team Blog Update Your Exchange SE Hybrid On-premises Rich Coexistence to Graph | Microsoft Community Hub