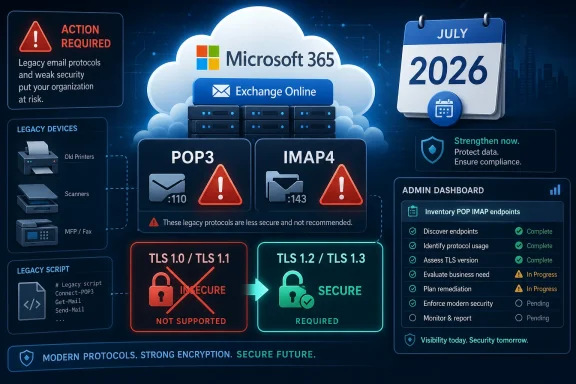
Microsoft will begin blocking Exchange Online POP3 and IMAP4 client connections that still negotiate TLS 1.0 or TLS 1.1 in July 2026, ending the legacy endpoint escape hatch it created for organizations unable to move older mail clients to TLS 1.2 or newer. The decision is less a surprise than a delayed bill coming due. Microsoft has been telling customers since 2020 that these protocols no longer belong in the service, but Exchange Online’s long tail of old clients, appliances, and scripts forced a slow-motion retirement. The real story is not that TLS 1.0 and 1.1 are finally being blocked; it is that cloud email has reached the point where compatibility exceptions are themselves becoming a security liability.
The July 2026 enforcement window closes a chapter Microsoft opened when it stopped supporting TLS 1.0 and TLS 1.1 in Exchange Online in October 2020 but continued to allow some POP and IMAP connections to negotiate the old protocols. That distinction mattered: unsupported did not mean impossible. For years, a customer could still keep a creaking email client alive if it connected through the right path and the tenant had opted into the legacy accommodation.
That compromise made sense in the messy middle period of cloud migration. POP3 and IMAP4 are simple, durable, and everywhere, which is precisely why they survive in places modern identity and mail clients often do not. They sit in scanners, ticketing systems, monitoring tools, payroll software, line-of-business applications, Linux scripts, and forgotten mailboxes that no one wants to touch because they are still, annoyingly, working.
Microsoft’s 2026 move says that “still working” is no longer a sufficient reason to keep the door open. The company says modern clients and libraries already support TLS 1.2 or higher, and that most POP and IMAP traffic to Exchange Online now uses newer protocols. In other words, the old endpoint has become a special-purpose risk surface for a shrinking population of clients.
That is the right security call. It is also the sort of decision that creates a disproportionate amount of help desk noise because the affected systems are rarely the visible ones. Nobody notices the forgotten invoice parser until the invoices stop arriving.
That timeline should make the July 2026 cutoff feel almost generous. TLS 1.2 has been with us since 2008, and TLS 1.3 since 2018. By the time Microsoft starts blocking these connections, TLS 1.2 will be old enough to vote in many countries.
The security case is not merely aesthetic version chasing. TLS 1.0 and 1.1 are tied to older cryptographic assumptions and weaker negotiation patterns. They lack the modern posture administrators now expect from internet-facing services, and they complicate compliance conversations for organizations that must prove they have disabled obsolete encryption.
The stubbornness of these protocols is a reminder that the internet does not retire technology when it becomes unsafe. It retires technology when enough major platforms are finally willing to break the clients that depend on it. Microsoft has now decided Exchange Online has reached that point for POP and IMAP.
That is why Microsoft created the opt-in legacy endpoint in the first place. The company acknowledged there was significant usage from POP and IMAP clients that did not support TLS 1.2 or later. Rather than break those customers immediately, it offered a separate endpoint for legacy TLS clients: a buffer zone for organizations that needed time to replace or reconfigure brittle systems.
The problem with buffer zones is that they become permanent unless someone imposes a deadline. Once a tenant admin flips a compatibility toggle, the pressure to modernize often vanishes. The affected application remains obscure, the vendor upgrade remains postponed, and the risk becomes normalized because nothing dramatic happens.
July 2026 changes that psychology. Administrators now have a date they can take to application owners, facilities teams, finance departments, and vendors. The message is simple: this is not an IT preference, and it is not a speculative best practice. The service will stop accepting the connection.
That distinction matters because affected organizations should be easier to identify than in a broad, platform-wide retirement. Microsoft’s expectation is that the impact should fall mainly on customers who explicitly opted into the legacy endpoints. If a tenant never enabled the setting and clients are already using TLS 1.2 or later, July 2026 should be uneventful.
But “should” is doing a lot of work here. Many organizations have years of tenant configuration drift. Administrators leave, managed service providers change, documentation goes stale, and settings applied during a crisis become part of the furniture. A tenant that opted in during a 2022 scramble may have no obvious institutional memory of doing so.
The first task is therefore not remediation but discovery. Admins need to know whether the tenant allows legacy TLS clients, which clients are still using POP or IMAP, which endpoints they target, and whether those clients can negotiate TLS 1.2 or newer. Only after that can the organization decide whether it is dealing with a configuration change, a software upgrade, a vendor escalation, or a retirement project.
The risk lives in the corners. Multifunction printers that scan to mailboxes, embedded controllers that send status reports, applications built against ancient SSL libraries, and scripts running on old runtimes are the sort of things that keep using outdated TLS because nobody has had a reason to inspect them. They are also the sort of things business units treat as infrastructure, not software.
This is where Exchange Online’s cloud model creates a hard edge. In an on-premises environment, a sufficiently determined administrator could sometimes keep an old protocol alive behind a compensating control, at least for a while. In Microsoft 365, the platform owner sets the floor. When Microsoft blocks the negotiation, the client either speaks the required protocol or it does not connect.
That rigidity is frustrating when it breaks a workflow. It is also the central security benefit of SaaS. Microsoft can raise the baseline for millions of tenants at once, including tenants that would otherwise postpone the change forever.
This is why the Exchange Online change is part of a broader pattern across Microsoft 365 and the wider software industry. Vendors are becoming less willing to maintain old cryptographic compatibility because doing so weakens the shared service and increases audit complexity. The cloud provider’s tolerance for customer-specific insecurity has limits.
Enterprise customers sometimes experience these cutoffs as unilateral vendor behavior, and in a narrow sense they are right. Microsoft is choosing to enforce a standard on its timetable. But the alternative is worse: an internet where every major platform preserves obsolete encryption indefinitely because some customer, somewhere, has a device that cannot be patched.
There is a governance lesson here. Organizations that treat legacy protocol use as an exception with an owner, an expiration date, and a migration plan will absorb this change smoothly. Organizations that treat exceptions as a way to avoid decisions will rediscover those decisions during an outage.
Browsers had a relatively direct path to enforcement. The major vendors could coordinate, warn, and then make old TLS visibly fail for web sessions. Email is more distributed and more embedded. The client might not be a user-facing app at all; it might be a service account buried inside a workflow designed a decade ago.
Microsoft’s move may therefore become a useful market signal. If Exchange Online can close this exception for POP and IMAP, other providers will face pressure to do the same. Security baselines tend to move slowly until the largest platforms make an old behavior indefensible.
That does not mean every organization should wait for providers to force the issue. If a device or application cannot support TLS 1.2 in 2026, the larger question is not whether it can keep fetching mail. The question is what else it cannot do securely.
This is the part of the project most likely to bog down. A mailbox might be owned by “AP Automation,” but the actual client could be a vendor appliance in a locked room, a scheduled job on a forgotten VM, or a module in a SaaS connector nobody has updated in years. Technical discovery and organizational discovery have to happen together.
Once the client list exists, the migration paths are usually clear. Some systems need only a configuration change to use TLS 1.2. Others need a software update, a newer runtime, or a vendor-supported connector. The worst cases need replacement, and those are the ones July 2026 is meant to flush out early.
This is also a good moment to ask whether POP or IMAP should remain enabled at all. Modern authentication, Graph-based integrations, and purpose-built connectors are often better fits for automated workflows than mailbox scraping. TLS retirement is the immediate deadline, but protocol hygiene should be the broader project.
Microsoft’s announcement gives IT leaders a useful forcing function. It allows them to reclassify legacy mail access from “working system” to “dated dependency with a platform deadline.” That framing matters when asking for budget, vendor attention, or downtime windows.
There is also a security culture issue. Too many organizations tolerate legacy compatibility because the risk feels abstract and the disruption feels immediate. A fixed cutoff reverses that calculus. The disruption becomes concrete if nothing changes, and the safer option becomes the path of least future pain.
Exchange admins should resist the urge to treat this as a narrow TLS ticket. The better move is to use the deadline to clean up dormant mailboxes, disable unused POP and IMAP access, review service accounts, and document the remaining exceptions. If the work ends with the same opaque workflows running on newer TLS, the organization has solved only the smallest version of the problem.
Source: theregister.com Exchange Online blocks legacy TLS from July 2026
 Microsoft Finally Puts a Date on the Grace Period
Microsoft Finally Puts a Date on the Grace Period
The July 2026 enforcement window closes a chapter Microsoft opened when it stopped supporting TLS 1.0 and TLS 1.1 in Exchange Online in October 2020 but continued to allow some POP and IMAP connections to negotiate the old protocols. That distinction mattered: unsupported did not mean impossible. For years, a customer could still keep a creaking email client alive if it connected through the right path and the tenant had opted into the legacy accommodation.That compromise made sense in the messy middle period of cloud migration. POP3 and IMAP4 are simple, durable, and everywhere, which is precisely why they survive in places modern identity and mail clients often do not. They sit in scanners, ticketing systems, monitoring tools, payroll software, line-of-business applications, Linux scripts, and forgotten mailboxes that no one wants to touch because they are still, annoyingly, working.
Microsoft’s 2026 move says that “still working” is no longer a sufficient reason to keep the door open. The company says modern clients and libraries already support TLS 1.2 or higher, and that most POP and IMAP traffic to Exchange Online now uses newer protocols. In other words, the old endpoint has become a special-purpose risk surface for a shrinking population of clients.
That is the right security call. It is also the sort of decision that creates a disproportionate amount of help desk noise because the affected systems are rarely the visible ones. Nobody notices the forgotten invoice parser until the invoices stop arriving.
The Insecure Protocols Were Not Waiting for a Verdict
TLS 1.0 was published in 1999, when Windows 98 was still familiar, Internet Explorer 5 was current, and cloud productivity suites as we understand them did not exist. TLS 1.1 followed in 2006, a transitional update that arrived before the modern consensus around stronger cipher suites, authenticated encryption, and protocol hardening. The Internet Engineering Task Force formally deprecated both TLS 1.0 and TLS 1.1 in 2021.That timeline should make the July 2026 cutoff feel almost generous. TLS 1.2 has been with us since 2008, and TLS 1.3 since 2018. By the time Microsoft starts blocking these connections, TLS 1.2 will be old enough to vote in many countries.
The security case is not merely aesthetic version chasing. TLS 1.0 and 1.1 are tied to older cryptographic assumptions and weaker negotiation patterns. They lack the modern posture administrators now expect from internet-facing services, and they complicate compliance conversations for organizations that must prove they have disabled obsolete encryption.
The stubbornness of these protocols is a reminder that the internet does not retire technology when it becomes unsafe. It retires technology when enough major platforms are finally willing to break the clients that depend on it. Microsoft has now decided Exchange Online has reached that point for POP and IMAP.
POP and IMAP Are Where Old Assumptions Go to Hide
It is tempting to frame this as a minor cleanup for a pair of old mail protocols. That understates the operational role POP3 and IMAP4 still play in enterprise environments. Outlook, mobile mail apps, and Exchange ActiveSync may dominate the human side of email, but POP and IMAP remain the duct tape connecting unattended systems to mailboxes.That is why Microsoft created the opt-in legacy endpoint in the first place. The company acknowledged there was significant usage from POP and IMAP clients that did not support TLS 1.2 or later. Rather than break those customers immediately, it offered a separate endpoint for legacy TLS clients: a buffer zone for organizations that needed time to replace or reconfigure brittle systems.
The problem with buffer zones is that they become permanent unless someone imposes a deadline. Once a tenant admin flips a compatibility toggle, the pressure to modernize often vanishes. The affected application remains obscure, the vendor upgrade remains postponed, and the risk becomes normalized because nothing dramatic happens.
July 2026 changes that psychology. Administrators now have a date they can take to application owners, facilities teams, finance departments, and vendors. The message is simple: this is not an IT preference, and it is not a speculative best practice. The service will stop accepting the connection.
The Opt-In Endpoint Was a Warning Label, Not a Strategy
The legacy endpoint was never a promise that Microsoft would indefinitely preserve old encryption for POP and IMAP. It was a pressure-release valve. Customers had to opt in, and Microsoft’s own documentation treated it as an exception to the normal Exchange Online security posture.That distinction matters because affected organizations should be easier to identify than in a broad, platform-wide retirement. Microsoft’s expectation is that the impact should fall mainly on customers who explicitly opted into the legacy endpoints. If a tenant never enabled the setting and clients are already using TLS 1.2 or later, July 2026 should be uneventful.
But “should” is doing a lot of work here. Many organizations have years of tenant configuration drift. Administrators leave, managed service providers change, documentation goes stale, and settings applied during a crisis become part of the furniture. A tenant that opted in during a 2022 scramble may have no obvious institutional memory of doing so.
The first task is therefore not remediation but discovery. Admins need to know whether the tenant allows legacy TLS clients, which clients are still using POP or IMAP, which endpoints they target, and whether those clients can negotiate TLS 1.2 or newer. Only after that can the organization decide whether it is dealing with a configuration change, a software upgrade, a vendor escalation, or a retirement project.
The Systems That Break Will Not Look Like Email Clients
The most visible mail clients are unlikely to be the main problem. Current Outlook, Apple Mail, Thunderbird, and mainstream mobile clients have long supported modern TLS. Even many older but still maintained libraries have supported TLS 1.2 for years.The risk lives in the corners. Multifunction printers that scan to mailboxes, embedded controllers that send status reports, applications built against ancient SSL libraries, and scripts running on old runtimes are the sort of things that keep using outdated TLS because nobody has had a reason to inspect them. They are also the sort of things business units treat as infrastructure, not software.
This is where Exchange Online’s cloud model creates a hard edge. In an on-premises environment, a sufficiently determined administrator could sometimes keep an old protocol alive behind a compensating control, at least for a while. In Microsoft 365, the platform owner sets the floor. When Microsoft blocks the negotiation, the client either speaks the required protocol or it does not connect.
That rigidity is frustrating when it breaks a workflow. It is also the central security benefit of SaaS. Microsoft can raise the baseline for millions of tenants at once, including tenants that would otherwise postpone the change forever.
Compliance Has Become the Forcing Function
Microsoft frames the retirement in terms of security and compliance, and the two are now inseparable. Security teams do not merely want stronger encryption; they need to demonstrate to auditors, insurers, customers, and regulators that deprecated protocols are not in use. An exception endpoint complicates that story even if only a tiny amount of traffic uses it.This is why the Exchange Online change is part of a broader pattern across Microsoft 365 and the wider software industry. Vendors are becoming less willing to maintain old cryptographic compatibility because doing so weakens the shared service and increases audit complexity. The cloud provider’s tolerance for customer-specific insecurity has limits.
Enterprise customers sometimes experience these cutoffs as unilateral vendor behavior, and in a narrow sense they are right. Microsoft is choosing to enforce a standard on its timetable. But the alternative is worse: an internet where every major platform preserves obsolete encryption indefinitely because some customer, somewhere, has a device that cannot be patched.
There is a governance lesson here. Organizations that treat legacy protocol use as an exception with an owner, an expiration date, and a migration plan will absorb this change smoothly. Organizations that treat exceptions as a way to avoid decisions will rediscover those decisions during an outage.
Google’s Contrast Shows How Uneven the Retirement Still Is
One awkward detail is that not every major provider has moved at the same pace. Google Workspace documentation has continued to describe support for TLS 1.0 and TLS 1.1 in some mail contexts, even as browsers from Google, Mozilla, Microsoft, and Apple moved years ago to push the protocols out of mainstream web use. That contrast underscores how email’s legacy surface differs from the web’s.Browsers had a relatively direct path to enforcement. The major vendors could coordinate, warn, and then make old TLS visibly fail for web sessions. Email is more distributed and more embedded. The client might not be a user-facing app at all; it might be a service account buried inside a workflow designed a decade ago.
Microsoft’s move may therefore become a useful market signal. If Exchange Online can close this exception for POP and IMAP, other providers will face pressure to do the same. Security baselines tend to move slowly until the largest platforms make an old behavior indefensible.
That does not mean every organization should wait for providers to force the issue. If a device or application cannot support TLS 1.2 in 2026, the larger question is not whether it can keep fetching mail. The question is what else it cannot do securely.
The Admin Work Starts With Boring Inventory
The practical response is not glamorous, but it is straightforward. Administrators should begin by checking whether the tenant opted into legacy TLS clients and whether any clients are configured to use the legacy POP or IMAP endpoints. Then they need to map those clients to owners and business processes.This is the part of the project most likely to bog down. A mailbox might be owned by “AP Automation,” but the actual client could be a vendor appliance in a locked room, a scheduled job on a forgotten VM, or a module in a SaaS connector nobody has updated in years. Technical discovery and organizational discovery have to happen together.
Once the client list exists, the migration paths are usually clear. Some systems need only a configuration change to use TLS 1.2. Others need a software update, a newer runtime, or a vendor-supported connector. The worst cases need replacement, and those are the ones July 2026 is meant to flush out early.
This is also a good moment to ask whether POP or IMAP should remain enabled at all. Modern authentication, Graph-based integrations, and purpose-built connectors are often better fits for automated workflows than mailbox scraping. TLS retirement is the immediate deadline, but protocol hygiene should be the broader project.
The Deadline Is Really a Test of Ownership
The organizations most at risk are not necessarily the ones with the oldest technology. They are the ones where no one owns the old technology. A scanner maintained by facilities, a mail parser owned by finance, and a vendor integration managed by an outside partner can all depend on Exchange Online while remaining invisible to the messaging team.Microsoft’s announcement gives IT leaders a useful forcing function. It allows them to reclassify legacy mail access from “working system” to “dated dependency with a platform deadline.” That framing matters when asking for budget, vendor attention, or downtime windows.
There is also a security culture issue. Too many organizations tolerate legacy compatibility because the risk feels abstract and the disruption feels immediate. A fixed cutoff reverses that calculus. The disruption becomes concrete if nothing changes, and the safer option becomes the path of least future pain.
Exchange admins should resist the urge to treat this as a narrow TLS ticket. The better move is to use the deadline to clean up dormant mailboxes, disable unused POP and IMAP access, review service accounts, and document the remaining exceptions. If the work ends with the same opaque workflows running on newer TLS, the organization has solved only the smallest version of the problem.
July 2026 Will Reward the Tenants That Already Know Their Mail Flows
The operational lesson is simple: Exchange Online is only as predictable as the systems connected to it. The tenants that already inventory client protocols, service accounts, and mail-enabled automation will treat this as routine maintenance. The tenants that do not will turn a known 2026 deadline into a mystery outage.- Microsoft will begin blocking Exchange Online POP3 and IMAP4 connections that use TLS 1.0 or TLS 1.1 starting in July 2026.
- The change primarily targets customers that opted into Microsoft’s legacy TLS endpoint for older POP and IMAP clients.
- TLS 1.0 and TLS 1.1 have been deprecated for years and no longer fit modern security or compliance expectations.
- The highest-risk clients are likely to be unattended systems, appliances, scripts, and third-party applications rather than mainstream human email clients.
- Administrators should verify tenant settings, identify POP and IMAP usage, contact application owners, and replace or upgrade anything that cannot use TLS 1.2 or newer.
- The deadline is an opportunity to reduce dependence on legacy mail protocols, not merely to swap one encryption version for another.
Source: theregister.com Exchange Online blocks legacy TLS from July 2026