Microsoft said on May 8, 2026, that Exchange Online will stop supporting direct Exchange ActiveSync certificate-based authentication by the end of 2026, forcing affected mobile mail clients to authenticate certificates through Microsoft Entra ID instead of presenting them straight to Exchange. The move is narrow, but its message is broad: Microsoft is still dismantling the old Exchange authentication perimeter, one exception at a time. For most users, nothing changes. For the organizations that deliberately built mobile email around EAS client certificates, the clock has started.
This is not another mass-market Outlook change, and it is not a general retirement of certificate-based authentication. Microsoft is targeting a specific legacy path: Exchange ActiveSync clients, often native mobile mail apps, that send user certificates directly to Exchange Online for validation. Outlook Mobile, Exchange Server on-premises, and other Exchange Online authentication scenarios are outside the stated scope.
That distinction matters because certificate-based authentication has usually been sold as the more secure option, not the one administrators expect to see on a retirement list. The problem is not the certificate itself. The problem is where the certificate is validated and what the client does, or does not, receive afterward.
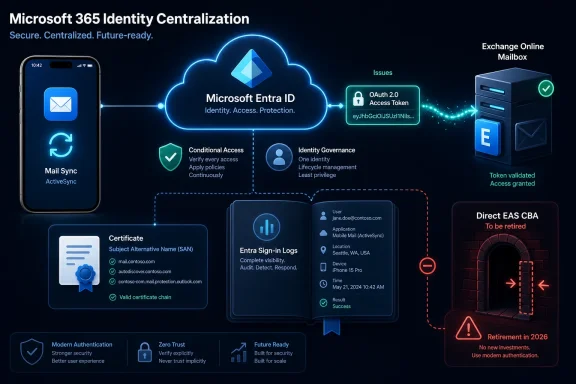
In the legacy EAS CBA flow, Exchange Online handles the certificate validation internally. The mobile client never obtains a normal OAuth access token from Microsoft’s identity plane. That leaves administrators with a security model that may be passwordless, but is still structurally out of step with modern Microsoft 365 authentication.
Microsoft’s argument is therefore less “certificates are bad” than “Exchange should not be the identity broker.” In the new model, Microsoft Entra ID validates the client certificate, issues an OAuth token, and Exchange Online consumes that token like a modern resource service. The mailbox server stops being the special case.
Basic Authentication was the obvious villain because it sent reusable credentials to services that attackers loved to spray, stuff, and phish. But legacy authentication is a broader category than username-and-password prompts. It includes any path that sidesteps the modern controls Microsoft wants administrators to use consistently: Conditional Access, sign-in risk, device compliance, token claims, and unified identity logs.
Direct EAS CBA sits awkwardly in that world. It is stronger than Basic Auth in the narrow cryptographic sense because the user’s private key is not transmitted over the network. But it is weaker in Microsoft’s modern cloud operating model because the authentication transaction does not start and end cleanly in Entra ID.
That is the tension Microsoft is now resolving. A certificate presented to Exchange may be passwordless, but it is not necessarily modern. In Microsoft 365, modern means OAuth, Entra-mediated policy enforcement, and a resource service that trusts tokens rather than inventing its own parallel authentication lane.
That endurance has also made EAS a recurring pain point for administrators. A protocol designed for convenient mailbox synchronization has lived through multiple eras of identity architecture. It has supported Basic Auth, modern auth, certificate auth, device controls, and combinations thereof, depending on tenant configuration, client capability, and history.
The latest retirement does not kill EAS. It does, however, remove another exception that let EAS behave differently from the rest of Microsoft 365. That is the real direction of travel: protocols may persist, but the identity path around them is being standardized.
For WindowsForum readers managing Microsoft 365 estates, that means old mobile email decisions deserve fresh scrutiny. A profile that looked hardened five years ago because it used certificates may now be the profile that prevents a clean Conditional Access design.
That architecture gives administrators a cleaner enforcement point. Conditional Access policies no longer need to make awkward distinctions for a protocol-specific certificate flow. Sign-in logs become more meaningful because identity events are processed where the rest of the tenant’s identity events are processed. Security teams can reason about access without carrying a mental footnote for direct EAS CBA.
It also aligns with Microsoft’s broader marketing of Entra CBA as phishing-resistant and passwordless. The certificate still does the important work of proving possession of a private key. But the proof is now fed into the cloud identity platform rather than into Exchange’s own legacy machinery.
There is a vendor strategy here, too. Microsoft wants Entra ID to be the control plane for Microsoft 365 access. Every authentication flow that bypasses it weakens that story, even if the bypass exists for historically good reasons. Retiring direct EAS CBA is both a security move and an architectural consolidation.
That is how Microsoft increasingly handles legacy cleanup in cloud services. First, it stops the population from growing. Then it targets known usage with Message Center notices. Finally, it retires the path once the migration window has closed or the operational risk becomes unacceptable.
For administrators, this is a warning against interpreting “supported until late 2026” as “safe to ignore until late 2026.” The flow is already being treated as legacy. New deployments should not be designed around it, and existing deployments should be considered technical debt with a published expiration date.
Microsoft says impacted tenants will receive Message Center posts. That matters because many organizations may not remember whether a mobile certificate configuration was inherited from an old MDM rollout, a government compliance project, or a pre-Outlook-Mobile standard. Tenant-level notification is useful, but it is not a substitute for inventory.
But “similar PKI” does not mean “flip a switch.” Entra ID must trust the relevant certificate authorities. Intermediate CAs must be configured correctly. Certificate revocation lists must be reachable from internet-facing locations. User certificates must contain identity values that Entra ID can map to the right account.
For Exchange ActiveSync clients, Microsoft’s stated requirement is especially concrete: the certificate needs the user’s routable Exchange Online email address in the Subject Alternative Name field, either as Principal Name or RFC822 Name. That is the sort of detail that can turn a clean pilot into a noisy help desk week if certificate templates were customized years ago and never revisited.
The mobile device side may be the harder part. MDM profiles that currently specify certificate authentication may need to move to OAuth-based configurations that still use certificates at the Entra sign-in stage. Depending on the client, platform, and vendor, that could require profile replacement, user re-enrollment, app updates, or vendor-specific guidance.
Native mail clients are where Exchange ActiveSync still does much of its quiet work. They are also where authentication transitions can become visible to users. A certificate-selection prompt, a re-created mail profile, or a failed sync after a policy change is not an abstract identity architecture issue to an executive on a phone at an airport.
The risk is not that the migration is impossible. The risk is that mobile mail is often treated as “already solved” infrastructure. The people who built the original profile may have moved on, the MDM console may contain years of cloned settings, and the user population may include devices that only surface during an outage.
That is why the discovery phase matters. Administrators should not merely ask whether the tenant uses certificate-based authentication. They should ask which apps, which OS versions, which MDM payloads, which certificate templates, and which user groups depend on the direct Exchange flow.
Moving certificate validation to Entra ID makes the model easier to reason about. The certificate becomes an authentication method inside the identity platform, not a protocol-specific shortcut. Administrators can then apply controls more uniformly across client apps and services.
This is especially important for organizations that have spent the last several years tightening Microsoft 365 access. Blocking legacy authentication, requiring compliant devices, enforcing phishing-resistant MFA, and monitoring risky sign-ins all depend on consistent identity telemetry. Exceptions are where attackers and auditors both tend to look.
There is still complexity, of course. Certificate authentication itself has policies, bindings, issuer hints, revocation behavior, and user mapping rules. But that complexity belongs in the identity system. Microsoft is saying Exchange Online should not be the place where a special certificate trust path keeps living indefinitely.
Microsoft does not need to describe every internal implementation detail for the direction to be clear. Cloud services built over decades often contain privileged internal paths that made sense when the service boundary was different. As identity centralizes, those paths become liabilities, especially when they serve a shrinking population of clients.
The move to OAuth tokens is a way of narrowing trust. Exchange receives a token scoped and issued by the identity provider. The client participates in the same basic model as other modern clients. Access decisions can be anchored in Entra ID rather than in Exchange-specific legacy handling.
That does not mean Entra-based CBA is magically risk-free. Certificates can be misissued, mishandled, left on unmanaged devices, or mapped too broadly. But the control surface is more coherent, and coherence is a security feature.
Microsoft’s mention of dedicated CBA endpoints for worldwide multi-tenant, GCC High, and DoD environments underscores that this is not only a commercial tenant cleanup. The public sector and regulated cloud variants are part of the same modernization arc, even if their migration processes may be slower and more formal.
Those tenants should resist the temptation to view the deadline as generous. End of 2026 is close in enterprise change-management terms, especially for environments that require certificate template review, MDM profile validation, security sign-off, pilot groups, communications, and exception handling.
The hard part may be vendor coordination. If a third-party mobile mail client or MDM platform does not yet support the exact Entra CBA flow an organization needs, the calendar becomes partly dependent on someone else’s roadmap. That is why early testing is not optional.
That is enough to begin triage, but mature organizations will need more than a yes-or-no answer. They should identify affected users, device platforms, app versions, certificate issuers, and mail profile sources. They should also determine whether any Conditional Access exceptions exist solely to keep the legacy flow alive.
The migration should then be piloted like any identity change. Start with a controlled device set, confirm certificate prompts and token issuance, validate mailbox sync, and monitor sign-in logs. Only then should administrators scale the change through MDM.
The most dangerous assumption is that certificates currently working with direct EAS CBA will automatically work with Entra CBA. They may, and Microsoft suggests many will. But certificate mapping is unforgiving, and revocation accessibility is one of those infrastructure details that tends to fail only when the pilot becomes real.
For administrators, the cumulative effect can feel relentless. Each individual change is defensible. Together, they create a rolling program of discovery, migration, vendor validation, and user communication around systems that many organizations considered stable.
That is not simply Microsoft being capricious. Exchange Online is one of the most attacked collaboration platforms on the planet, and legacy access mechanisms are difficult to defend at cloud scale. Still, the burden of modernization often lands on customers who deployed Microsoft-supported features exactly as documented years earlier.
This is the cloud bargain in miniature. Microsoft can improve the security baseline for everyone by removing legacy paths. Customers get a safer platform, but they also inherit the obligation to keep up with the platform’s changing definition of “safe.”
That matters during migrations because ambiguity slows decisions. A mobile team may talk about EAS CBA, an identity team may talk about Entra CBA, a security team may talk about legacy authentication, and an MDM team may talk about OAuth profiles. They may all be describing the same transition from different angles.
The fix is not a branding lecture. The fix is a shared internal design note that states the current flow, the target flow, the affected device profiles, and the success criteria in plain language. If the organization cannot explain the migration without vendor terminology, it probably is not ready to execute it.
Microsoft’s terminology will continue to evolve. Your runbooks should not depend on everyone remembering which label was current when the original profile was built.
There is also a version that becomes a familiar enterprise mess. A forgotten executive device uses native mail with a legacy certificate profile. A certificate template lacks the expected email value. A CRL URL is not reachable externally. A third-party app handles OAuth differently than expected. Conditional Access policies behave correctly but surprise the help desk.
The difference between those two outcomes is not the calendar; it is inventory. Organizations that know their mobile email estate can treat this as another planned authentication modernization. Organizations that rely on inherited assumptions will discover their architecture through user complaints.
Microsoft has given a long runway, but long runways can create their own risk. Teams defer the work because the date sounds far away, then collide with procurement freezes, mobile OS changes, vendor lag, or competing Microsoft 365 retirements. The right time to find the edge cases is while the old path still works.
This is the rare retirement where the affected group is narrow but the diagnostic value is wide. Even if you find no direct EAS CBA, the audit may reveal stale ActiveSync devices, old native mail profiles, Conditional Access exceptions, or certificate templates that no longer match your identity strategy.
Source: Microsoft Exchange Team Blog Retirement of Direct Exchange ActiveSync Certificate-Based Authentication by End of 2026 | Microsoft Community Hub
 Microsoft Is Closing a Small Door With a Large Security Shadow
Microsoft Is Closing a Small Door With a Large Security Shadow
This is not another mass-market Outlook change, and it is not a general retirement of certificate-based authentication. Microsoft is targeting a specific legacy path: Exchange ActiveSync clients, often native mobile mail apps, that send user certificates directly to Exchange Online for validation. Outlook Mobile, Exchange Server on-premises, and other Exchange Online authentication scenarios are outside the stated scope.That distinction matters because certificate-based authentication has usually been sold as the more secure option, not the one administrators expect to see on a retirement list. The problem is not the certificate itself. The problem is where the certificate is validated and what the client does, or does not, receive afterward.
In the legacy EAS CBA flow, Exchange Online handles the certificate validation internally. The mobile client never obtains a normal OAuth access token from Microsoft’s identity plane. That leaves administrators with a security model that may be passwordless, but is still structurally out of step with modern Microsoft 365 authentication.
Microsoft’s argument is therefore less “certificates are bad” than “Exchange should not be the identity broker.” In the new model, Microsoft Entra ID validates the client certificate, issues an OAuth token, and Exchange Online consumes that token like a modern resource service. The mailbox server stops being the special case.
The Legacy Auth War Was Never Only About Passwords
The industry shorthand around Microsoft’s authentication cleanup has often been “Basic Auth is dead.” That was true as far as it went, but it understated the bigger project. Microsoft has spent years trying to collapse Exchange Online access into token-based, policy-aware, centrally logged authentication flows.Basic Authentication was the obvious villain because it sent reusable credentials to services that attackers loved to spray, stuff, and phish. But legacy authentication is a broader category than username-and-password prompts. It includes any path that sidesteps the modern controls Microsoft wants administrators to use consistently: Conditional Access, sign-in risk, device compliance, token claims, and unified identity logs.
Direct EAS CBA sits awkwardly in that world. It is stronger than Basic Auth in the narrow cryptographic sense because the user’s private key is not transmitted over the network. But it is weaker in Microsoft’s modern cloud operating model because the authentication transaction does not start and end cleanly in Entra ID.
That is the tension Microsoft is now resolving. A certificate presented to Exchange may be passwordless, but it is not necessarily modern. In Microsoft 365, modern means OAuth, Entra-mediated policy enforcement, and a resource service that trusts tokens rather than inventing its own parallel authentication lane.
Exchange ActiveSync Survives, but Its Exceptions Keep Shrinking
Exchange ActiveSync has a long tail because mobile email has a long tail. Native iOS and Android mail clients, third-party enterprise mail apps, MDM-issued profiles, and sector-specific device fleets have kept EAS relevant even as Microsoft has pushed Outlook Mobile and Graph-era APIs.That endurance has also made EAS a recurring pain point for administrators. A protocol designed for convenient mailbox synchronization has lived through multiple eras of identity architecture. It has supported Basic Auth, modern auth, certificate auth, device controls, and combinations thereof, depending on tenant configuration, client capability, and history.
The latest retirement does not kill EAS. It does, however, remove another exception that let EAS behave differently from the rest of Microsoft 365. That is the real direction of travel: protocols may persist, but the identity path around them is being standardized.
For WindowsForum readers managing Microsoft 365 estates, that means old mobile email decisions deserve fresh scrutiny. A profile that looked hardened five years ago because it used certificates may now be the profile that prevents a clean Conditional Access design.
Entra ID Becomes the Checkpoint Microsoft Always Wanted
The practical change Microsoft wants is straightforward. Instead of a mobile EAS client presenting a certificate directly to Exchange Online, the client authenticates with Microsoft Entra ID using certificate-based authentication. Entra ID validates the certificate, maps it to the user, evaluates applicable controls, and issues an OAuth token. Exchange Online then accepts that token for mailbox access.That architecture gives administrators a cleaner enforcement point. Conditional Access policies no longer need to make awkward distinctions for a protocol-specific certificate flow. Sign-in logs become more meaningful because identity events are processed where the rest of the tenant’s identity events are processed. Security teams can reason about access without carrying a mental footnote for direct EAS CBA.
It also aligns with Microsoft’s broader marketing of Entra CBA as phishing-resistant and passwordless. The certificate still does the important work of proving possession of a private key. But the proof is now fed into the cloud identity platform rather than into Exchange’s own legacy machinery.
There is a vendor strategy here, too. Microsoft wants Entra ID to be the control plane for Microsoft 365 access. Every authentication flow that bypasses it weakens that story, even if the bypass exists for historically good reasons. Retiring direct EAS CBA is both a security move and an architectural consolidation.
The Immediate Block on New Tenants Is the Real Tell
The end-of-2026 deadline is the headline, but the immediate change for new tenants is just as revealing. Microsoft says it will roll out blocks so no new tenants can start using the legacy direct CBA flow. Existing customers get runway; new customers get the future by default.That is how Microsoft increasingly handles legacy cleanup in cloud services. First, it stops the population from growing. Then it targets known usage with Message Center notices. Finally, it retires the path once the migration window has closed or the operational risk becomes unacceptable.
For administrators, this is a warning against interpreting “supported until late 2026” as “safe to ignore until late 2026.” The flow is already being treated as legacy. New deployments should not be designed around it, and existing deployments should be considered technical debt with a published expiration date.
Microsoft says impacted tenants will receive Message Center posts. That matters because many organizations may not remember whether a mobile certificate configuration was inherited from an old MDM rollout, a government compliance project, or a pre-Outlook-Mobile standard. Tenant-level notification is useful, but it is not a substitute for inventory.
The Migration Is Mostly Identity Plumbing, Not Mailbox Plumbing
Microsoft is presenting the move to Entra-based CBA as a manageable migration because the underlying PKI requirements are broadly similar. Organizations already using direct EAS CBA should have user certificates, trusted issuing authorities, and MDM distribution processes in place. The work is not starting from zero.But “similar PKI” does not mean “flip a switch.” Entra ID must trust the relevant certificate authorities. Intermediate CAs must be configured correctly. Certificate revocation lists must be reachable from internet-facing locations. User certificates must contain identity values that Entra ID can map to the right account.
For Exchange ActiveSync clients, Microsoft’s stated requirement is especially concrete: the certificate needs the user’s routable Exchange Online email address in the Subject Alternative Name field, either as Principal Name or RFC822 Name. That is the sort of detail that can turn a clean pilot into a noisy help desk week if certificate templates were customized years ago and never revisited.
The mobile device side may be the harder part. MDM profiles that currently specify certificate authentication may need to move to OAuth-based configurations that still use certificates at the Entra sign-in stage. Depending on the client, platform, and vendor, that could require profile replacement, user re-enrollment, app updates, or vendor-specific guidance.
Native Mail Apps Are Again the Operational Edge Case
Microsoft is careful to say that Outlook Mobile is not affected by this specific retirement. That line will be reassuring for organizations that standardized on Microsoft’s mobile client. It will be less reassuring for those that still depend on native mobile mail apps because of user preference, regulatory packaging, device constraints, or long-standing MDM templates.Native mail clients are where Exchange ActiveSync still does much of its quiet work. They are also where authentication transitions can become visible to users. A certificate-selection prompt, a re-created mail profile, or a failed sync after a policy change is not an abstract identity architecture issue to an executive on a phone at an airport.
The risk is not that the migration is impossible. The risk is that mobile mail is often treated as “already solved” infrastructure. The people who built the original profile may have moved on, the MDM console may contain years of cloned settings, and the user population may include devices that only surface during an outage.
That is why the discovery phase matters. Administrators should not merely ask whether the tenant uses certificate-based authentication. They should ask which apps, which OS versions, which MDM payloads, which certificate templates, and which user groups depend on the direct Exchange flow.
Conditional Access Finally Gets a Cleaner Story
One of Microsoft’s strongest arguments is that direct EAS CBA complicates Conditional Access. If the authentication flow is classified as legacy, then policies designed to block legacy authentication can also block the very certificate-based access an organization intentionally deployed. That creates an unpleasant choice: weaken a broad security policy or maintain an exception for a shrinking use case.Moving certificate validation to Entra ID makes the model easier to reason about. The certificate becomes an authentication method inside the identity platform, not a protocol-specific shortcut. Administrators can then apply controls more uniformly across client apps and services.
This is especially important for organizations that have spent the last several years tightening Microsoft 365 access. Blocking legacy authentication, requiring compliant devices, enforcing phishing-resistant MFA, and monitoring risky sign-ins all depend on consistent identity telemetry. Exceptions are where attackers and auditors both tend to look.
There is still complexity, of course. Certificate authentication itself has policies, bindings, issuer hints, revocation behavior, and user mapping rules. But that complexity belongs in the identity system. Microsoft is saying Exchange Online should not be the place where a special certificate trust path keeps living indefinitely.
High-Privilege Internal Tokens Make the Security Case Less Academic
Microsoft’s blog post also points to an internal concern: the direct Exchange implementation relies on a high-privilege mechanism to access data after certificate validation. That phrase should get administrators’ attention. It suggests that the issue is not merely cleanliness of logs or policy alignment, but the blast radius of a legacy service-side design.Microsoft does not need to describe every internal implementation detail for the direction to be clear. Cloud services built over decades often contain privileged internal paths that made sense when the service boundary was different. As identity centralizes, those paths become liabilities, especially when they serve a shrinking population of clients.
The move to OAuth tokens is a way of narrowing trust. Exchange receives a token scoped and issued by the identity provider. The client participates in the same basic model as other modern clients. Access decisions can be anchored in Entra ID rather than in Exchange-specific legacy handling.
That does not mean Entra-based CBA is magically risk-free. Certificates can be misissued, mishandled, left on unmanaged devices, or mapped too broadly. But the control surface is more coherent, and coherence is a security feature.
Government and Regulated Tenants Will Feel the Calendar Most
Certificate-based authentication is common in environments that care deeply about phishing resistance, smart-card-style workflows, and device-bound credentials. That includes government, defense-adjacent, healthcare, finance, and other regulated sectors. These are also the organizations least likely to treat mobile email changes casually.Microsoft’s mention of dedicated CBA endpoints for worldwide multi-tenant, GCC High, and DoD environments underscores that this is not only a commercial tenant cleanup. The public sector and regulated cloud variants are part of the same modernization arc, even if their migration processes may be slower and more formal.
Those tenants should resist the temptation to view the deadline as generous. End of 2026 is close in enterprise change-management terms, especially for environments that require certificate template review, MDM profile validation, security sign-off, pilot groups, communications, and exception handling.
The hard part may be vendor coordination. If a third-party mobile mail client or MDM platform does not yet support the exact Entra CBA flow an organization needs, the calendar becomes partly dependent on someone else’s roadmap. That is why early testing is not optional.
The Admin Checklist Starts in the Logs
Microsoft gives administrators two basic discovery paths: check the MDM configuration and inspect Entra sign-in logs. If the MDM email profile uses Certificate as the authentication type rather than OAuth, that is a strong signal. In Entra logs, the relevant sign-ins appear as Exchange ActiveSync with certificate authentication details.That is enough to begin triage, but mature organizations will need more than a yes-or-no answer. They should identify affected users, device platforms, app versions, certificate issuers, and mail profile sources. They should also determine whether any Conditional Access exceptions exist solely to keep the legacy flow alive.
The migration should then be piloted like any identity change. Start with a controlled device set, confirm certificate prompts and token issuance, validate mailbox sync, and monitor sign-in logs. Only then should administrators scale the change through MDM.
The most dangerous assumption is that certificates currently working with direct EAS CBA will automatically work with Entra CBA. They may, and Microsoft suggests many will. But certificate mapping is unforgiving, and revocation accessibility is one of those infrastructure details that tends to fail only when the pilot becomes real.
Microsoft’s Exchange Cleanup Is Becoming a 2026 Theme
This retirement lands in a broader Exchange Online cleanup cycle. Microsoft has already removed Basic Authentication from Exchange Online protocols and has been moving customers away from older Exchange Web Services dependencies toward Microsoft Graph. The pattern is unmistakable: old access paths are being narrowed, fenced, or retired.For administrators, the cumulative effect can feel relentless. Each individual change is defensible. Together, they create a rolling program of discovery, migration, vendor validation, and user communication around systems that many organizations considered stable.
That is not simply Microsoft being capricious. Exchange Online is one of the most attacked collaboration platforms on the planet, and legacy access mechanisms are difficult to defend at cloud scale. Still, the burden of modernization often lands on customers who deployed Microsoft-supported features exactly as documented years earlier.
This is the cloud bargain in miniature. Microsoft can improve the security baseline for everyone by removing legacy paths. Customers get a safer platform, but they also inherit the obligation to keep up with the platform’s changing definition of “safe.”
The Naming Problem Still Hurts Customers
There is also an unavoidable communications problem. Azure AD became Microsoft Entra ID, but administrators still encounter old and new names in documentation, logs, scripts, vendor consoles, and institutional memory. Microsoft’s own explanation references both Entra ID and Azure AD concepts because the ecosystem still straddles the rename.That matters during migrations because ambiguity slows decisions. A mobile team may talk about EAS CBA, an identity team may talk about Entra CBA, a security team may talk about legacy authentication, and an MDM team may talk about OAuth profiles. They may all be describing the same transition from different angles.
The fix is not a branding lecture. The fix is a shared internal design note that states the current flow, the target flow, the affected device profiles, and the success criteria in plain language. If the organization cannot explain the migration without vendor terminology, it probably is not ready to execute it.
Microsoft’s terminology will continue to evolve. Your runbooks should not depend on everyone remembering which label was current when the original profile was built.
The Best Migration Is the One Users Barely Notice
There is a version of this retirement that goes smoothly. The tenant receives a Message Center notice, administrators confirm a small affected population, Entra CBA is already configured or easily enabled, certificates contain the right SAN values, MDM profiles are updated, and users see at most a certificate prompt before mail continues syncing.There is also a version that becomes a familiar enterprise mess. A forgotten executive device uses native mail with a legacy certificate profile. A certificate template lacks the expected email value. A CRL URL is not reachable externally. A third-party app handles OAuth differently than expected. Conditional Access policies behave correctly but surprise the help desk.
The difference between those two outcomes is not the calendar; it is inventory. Organizations that know their mobile email estate can treat this as another planned authentication modernization. Organizations that rely on inherited assumptions will discover their architecture through user complaints.
Microsoft has given a long runway, but long runways can create their own risk. Teams defer the work because the date sounds far away, then collide with procurement freezes, mobile OS changes, vendor lag, or competing Microsoft 365 retirements. The right time to find the edge cases is while the old path still works.
The 2026 Mobile Mail Audit Just Became Mandatory
The concrete lesson is not that every tenant must panic. Most organizations never configured direct EAS CBA, and Microsoft says those tenants are not affected. The lesson is that any tenant with managed mobile email should now prove its assumptions rather than inherit them.This is the rare retirement where the affected group is narrow but the diagnostic value is wide. Even if you find no direct EAS CBA, the audit may reveal stale ActiveSync devices, old native mail profiles, Conditional Access exceptions, or certificate templates that no longer match your identity strategy.
- Organizations using Outlook Mobile are not the target of this specific retirement, but they should still verify whether any native mail or third-party EAS clients remain in production.
- Tenants with MDM-issued mail profiles should check whether those profiles use Certificate authentication directly against Exchange Online or OAuth-based authentication through Microsoft Entra ID.
- Administrators should review Entra sign-in logs for Exchange ActiveSync events that show certificate authentication and map those events back to users, devices, and profiles.
- Certificate templates should be checked for routable Exchange Online email addresses in the required Subject Alternative Name values before broad migration begins.
- Pilot migrations should validate the full chain: CA trust in Entra ID, internet-reachable revocation data, certificate selection on the device, OAuth token issuance, Conditional Access behavior, and mailbox synchronization.
- Any dependency on third-party mobile mail clients or MDM vendors should be escalated early, because vendor support timelines can become the real migration blocker.
Source: Microsoft Exchange Team Blog Retirement of Direct Exchange ActiveSync Certificate-Based Authentication by End of 2026 | Microsoft Community Hub