The Go standard library has picked up a subtle but meaningful security fix: a time‑of‑check/time‑of‑use (TOCTOU) race in the
Go introduced traversal‑resistant filesystem primitives a few releases back—
In short: when a program opened a directory via a
A few practical takeaways up front:
Source: MSRC Security Update Guide - Microsoft Security Response Center
os package could let a returned FileInfo refer to a file outside a previously opened Root, allowing an attacker to probe filesystem metadata outside the intended root. The issue has been tracked as CVE‑2026‑27139 and fixed in the March 2026 point releases (Go 1.26.1 and the corresponding 1.25.8 maintenance release). (groups.google.com)
 Background / Overview
Background / Overview
Go introduced traversal‑resistant filesystem primitives a few releases back—os.Root and family—specifically to give programs a safe way to operate inside a directory tree without accidental escapes via .. or symlink tricks. Those APIs made it easier for server software, container runtimes, and other sandboxing components to restrict access to a subtree of the filesystem. The new CVE arises not from the idea of a root API itself, but from an implementation gap in how directory listings return metadata about entries in that root.In short: when a program opened a directory via a
Root and then called ReadDir/Readdir to enumerate entries, the os package populated returned FileInfo values using lstat. On Unix systems lstat follows or resolves pathname components in ways that can be influenced by symlink swaps between the time the directory listing is read and the time lstat runs. That race condition allows the FileInfo object to be populated from a path outside the original root—even though opening or reading the file is still blocked—resulting in disclosure of metadata (file existence, size, mode, timestamps) from arbitrary paths. The upstream Go team categorized the impact as limited and classified the issue on the public track. (go.dev)A few practical takeaways up front:
- This is a metadata disclosure problem, not an arbitrary file‑read/write escape: an attacker cannot use this bug to read the bytes of an outside file or to write files outside the root. (go.dev)
- The vulnerability is platform‑specific in behavior and arises on Unix‑like platforms where the
lstatpath resolution semantics plus symlink behavior can be exploited. - Go maintainers released patched versions quickly; updating the Go toolchain to Go 1.26.1 (or applying the 1.25.8 maintenance release if on that branch) addresses the defect. (groups.google.com)
What exactly went wrong (technical analysis)
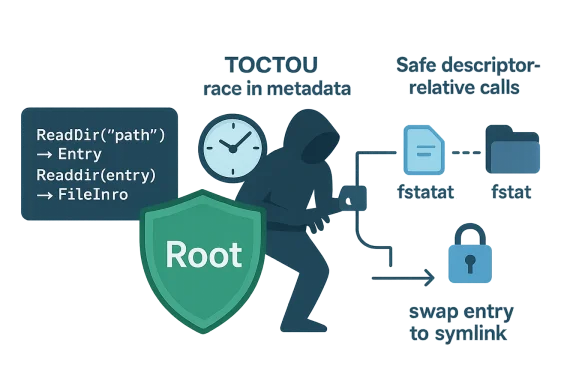
The TOCTOU root of the problem
The bug is a classic TOCTOU window: the code first reads directory entries (the check) and later performs lstat on the pathname built from those entries (the use). In that window an attacker with the ability to modify the filesystem under the directory—normally a threat model for some server environments, build systems, container hosts, or multi‑tenant systems—can replace a directory entry with a symlink pointing outside the root. Whenlstat is executed on that path it resolves to the symlink target outside the root, and the returned FileInfo reflects the target rather than the intended in‑root entry. The Go issue discussion contains a short test case that demonstrates the sequence: create a directory, perform a ReadDir to enumerate entries, remove the directory and replace it with a symlink to an external directory, then call Info() on the previously enumerated DirEntry and observe metadata for the external file. The Go project explicitly recognizes this scenario in the issue and in their internal classification of the fix. (go.dev)Why lstat is the culprit
On Unix,lstat takes a pathname and returns file metadata without following the final symlink (unlike stat, which follows final symlinks). However, lstat remains vulnerable to path resolution races: the pathname is interpreted anew against the current filesystem namespace at the moment of the lstat call. If the filesystem contents are changed between directory readdir() and later lstat(), the perceived target of the path can change. In short, pathname-based metadata collection is raceable unless the implementation uses file-descriptor–relative operations (like fstatat with the directory FD and AT_SYMLINK_NOFOLLOW flags), which bind metadata queries to the exact directory object that was opened. The Go fix moves toward that safer approach. Evidence for the root cause and the chosen fix strategy appears in the upstream issue discussion and patch references. (go.dev)The fix: use descriptor-relative metadata calls
The Go maintainers remedied the race by switching the metadata collection to functions that operate relative to an already-open directory file descriptor (for example, usingfstatat/fstat) rather than re-resolving string paths through lstat. Descriptor-relative system calls remove the window where a directory entry could be swapped out for a symlink that points elsewhere, because the kernel resolves the target relative to the opened directory handle. The upstream change set and the vulnerability trackers show that the patch implements such a change for the affected ReadDir/Readdir code paths. This patch eliminates the TOCTOU vector for directory-listing metadata collection.Scope and impact
What functions and versions are affected
Inventorying the affected APIs and versions is essential for developers and packagers:- Affected Go APIs:
File.ReadDir,File.Readdir, and severalReadDirimplementations that ultimately call the same directory‑listing codepaths (for example,ReadDirondirFSandrootFS). These APIs could returnos.FileInfovalues whose metadata was gathered bylstatand thus could reflect files outside the openedRoot. - Affected Go releases: the bug is present in Go 1.26 (prior to 1.26.1) and in the corresponding unpatched 1.25 series; it was fixed in the point releases Go 1.26.1 and Go 1.25.8. The Go team’s announcement and distribution package updates reflect those versions. (groups.google.com)
Practical impact: limited but useful to an attacker
Although the bug doesn’t confer read/write access outside the root, metadata leakage is not trivial. An attacker who can cause the race (e.g., by swapping directory entries or creating symlinks at the right time) can:- Probe for the existence of files outside the root (presence/absence).
- Learn file sizes and modes and potentially timestamps for files they should not be able to observe.
- Use that metadata as an oracle in further exploitation (for example mapping which system files exist, informing targeted timing or side‑channel attacks, or verifying the presence of particular configuration files). (go.dev)
Root to sandbox workspace directories, or any service that lists directories where untrusted actors can race changes against the listing, the bug becomes materially interesting.Downstream and distribution impact
Linux distributions and downstream packaging systems that ship Go, or that embed the Go runtime in container images and language images, have already flagged the CVE and pushed updates. SUSE, Debian/OSV trackers, and other vendor pages list the CVE and mark Go packages in certain channels as affected or fixed. That distribution-level reaction means operators who rely on distribution packages should expect updated package versions to be available via normal security channels. For self‑installed Go toolchains (downloaded tarballs or installers), developers should update to the newly published Go point releases. (suse.com)Mitigation and remediation guidance
Immediate steps for operators and developers
- Prioritize patching: update your Go toolchain to Go 1.26.1 (or Go 1.25.8 if you maintain the older branch). These point releases contain the fix for CVE‑2026‑27139 along with several other security updates. If you rely on distribution packages, apply vendor-supplied security updates as they become available. (groups.google.com)
- Audit usage of
ReadDir/Readdir: identify code that: - Runs in multi‑tenant or untrusted contexts, and
- Uses
os.RootordirFS/rootFSAPIs to constrain filesystem access while also enumerating directory contents.
Such code paths should be considered higher risk and prioritized for patching and testing. - Harden environment assumptions: where feasible, ensure that directories passed into sandboxing APIs are not writable by untrusted actors, or apply additional locking/synchronization on directory content if concurrent modification by untrusted users is possible.
- Add defensive checks: if your application depends on directory listings for security decisions, consider double‑checking metadata against file descriptors or re-checking with descriptor-relative calls (where applicable) in your own code before acting on the information. However, note that doing ad‑hoc fixes in userland is error prone; the recommended approach is to use the fixed standard‑library release.
Testing after patching
- Rebuild applications that vendor Go modules or link to Go toolchain artifacts, and run unit/regression tests that exercise directory enumeration on Unix platforms. Deploy staged updates to test environments where you can simulate symlink swaps and directory races.
- For CI systems and container images, rebuild images that include the Go runtime or developer tool images so that the fixed toolchain is present in ephemeral runners.
- Validate package upgrades in distribution channels by checking vendor advisories and package metadata (ensure the package version is the patched one indicated by the vendor).
Risk management: how serious is CVE‑2026‑27139?
From a defender’s standpoint, CVE‑2026‑27139 is noteworthy because it undermines a security assumption that aRoot object provides a complete barrier to filesystem observation within its subtree. However, the vulnerability’s described capabilities are narrower than the worst cases:- It does not grant arbitrary file content disclosure or the ability to mutate files outside the root.
- The attacker must have the ability to race filesystem modifications against the directory listing operation—this generally requires local or write capability inside the filesystem being enumerated, which narrows the threat model compared with a remote code execution or full sandbox escape.
Why this matters to the Go ecosystem and to downstream consumers
This CVE underscores a few broader lessons for language runtime and systems library authors, and for the teams that consume them:- Library boundary correctness matters. When a library offers traversal‑resistant primitives, the guarantees must hold across all code paths, including seemingly mundane operations like directory listing. A naive combination of
readdirplus pathname‑basedlstatreintroduces the exact class of race the API was designed to prevent. - Descriptor‑relative system calls are the right primitive for safe metadata access. Modern kernels provide
openat,fstatat, and related calls that bind operations to directory file descriptors. Using those calls eliminates many string‑path races. - CVEs that leak metadata are not purely academic. Metadata oracles can be chained with other bugs or used to validate environment assumptions; they can also be used to fingerprint systems and guide targeted exploitation.
- Patching the standard library is not the end of the story. Downstream ecosystems must pick up, package, and distribute those fixes promptly; developers must update toolchains and rebuild artifacts where applicable. The distribution and container image landscape adds delay and complexity to remediation.
Recommendations for security teams and maintainers
- Inventory and triage: catalog systems that run Go binaries or build Go artifacts. Include CI runners, container image build pipelines, platform images, and any multi‑user services that use
ospackage functions on untrusted directories. - Patch the toolchain: upgrade the Go runtime/toolchain to the fixed releases and rebuild critical binaries and images. If you rely on distribution packages, apply vendor security updates as they are released. Confirm the specific patched package versions in your distro of choice—SUSE and Debian trackers list the CVE and the affected package states. (suse.com)
- Consider runtime hardening: where possible, reduce exposure by ensuring code that lists directories runs with minimal privileges and against directories that cannot be written by untrusted processes.
- Add monitoring: when directory enumeration APIs are used against directories that can be modified by external actors, add logging and anomaly detection to catch rapid create/delete/symlink activity that could be attempts to exploit this or related TOCTOU issues.
- Communicate with developers: make sure your application developers understand that listing a directory and trusting the returned metadata can be unsafe in contexts where untrusted actors can intervene. Encourage use of secure APIs and up-to-date toolchains.
Unverifiable/limited claims and cautionary notes
- Public exploit code: at the time of writing, there is no confirmed public exploit demonstrating chained high‑impact outcomes from this specific metadata leakage. The upstream issue and the CVE classification emphasize the limited nature of impact (metadata disclosure) and the public track designation. Treat any claim of widespread exploitation with skepticism until demonstrable proof is published. (go.dev)
- Vendor advisories: your distribution vendor may provide more context about the exact patched package name and version in their channels. The Microsoft Security Response Center page the user cited is a dynamic web app that may not render in simple fetches; the page content can require JavaScript for display. We observed the MSRC update‑guide endpoint respond with a client‑side app message when retrieved non‑interactively, so checklisting vendor advisories across multiple vendors is a good practice. (msrc.microsoft.com)
Developer notes and code hygiene
- If you wrote code that relies on
os.FileInforeturned byReadDir/Readdirfor security decisions (for example, whitelisting certain filenames or asserting presence/absence of files before taking privileged actions), refactor that logic. After updating the toolchain, test behavior under concurrent directory changes. - Vendor upgrades: if your project vendors the standard library or ships prebuilt images containing a Go toolchain, ensure those vendored copies are upgraded. Rebuild and redeploy images to avoid running unpatched toolchains inside ephemeral containers.
- Use defensive programming: avoid making security decisions from a single metadata snapshot if raceable state changes can occur. For critical decisions, prefer operations that open and act on the target via a file descriptor you control.
Conclusion
CVE‑2026‑27139 is a focused but instructive reminder that file system safety demands more than surface‑level APIs. A TOCTOU race in directory‑listing metadata gathering allowedos.FileInfo values to reflect files outside the intended Root, enabling metadata disclosure if an attacker could race directory modifications. The Go team has fixed the defect in Go 1.26.1 and 1.25.8 by switching to descriptor‑relative metadata calls, and distributors and trackers have cataloged and rolled the fix into vendor packages. Administrators and developers should prioritize updating Go toolchains, rebuilding artifacts where necessary, and auditing any code that trusts directory listing metadata in multi‑tenant or otherwise untrusted environments. The risk is real in the right operational contexts, but the remediation is straightforward: update, rebuild, and test. (groups.google.com)Source: MSRC Security Update Guide - Microsoft Security Response Center