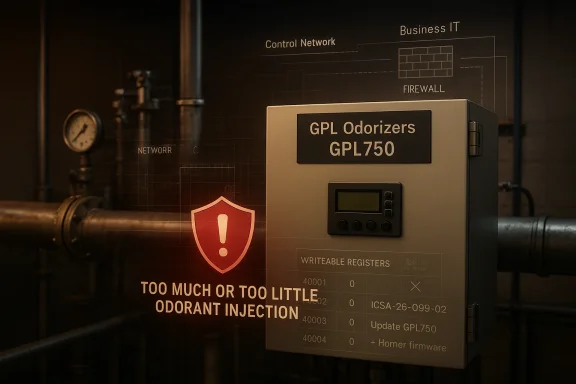
The release of ICSA-26-099-02 turns a niche industrial product into a straightforward reminder of how dangerous missing authentication can be in operational technology. CISA says a low-privileged remote attacker could send Modbus packets to manipulate register values in GPL Odorizers GPL750 systems, causing too much or too little odorant to be injected into a gas line. The affected versions span multiple controller families and firmware lines, and the mitigation path is already clear: update the GPL750 software and the underlying Horner firmware stack, then harden access to the control network. ial cybersecurity incidents often sound abstract until they map to a physical process, and this one does exactly that. Odorization is not cosmetic; it is the safety layer that allows humans and operators to detect natural gas leaks. If an attacker can influence the injection logic by changing register values, the result is not just a software integrity issue but a potential safety and compliance problem that touches public infrastructure.
CISA’s advisory fram306: Missing Authentication for Critical Function, with a CVSS 3.1 score of 8.6 HIGH. That rating reflects a particularly worrying combination: network reachability, no user interaction, no required privileges, and a direct effect on system behavior. In other words, this is not a bug that merely leaks data or crashes a dashboard; it alters the logic that governs a real-world industrial control action.
The affected product list is specific and operationally. CISA identifies GPL750 variants on XL4, XL4 Prime, XL7, and XL7 Prime** controller families, with vulnerable ranges beginning at early firmware milestones and extending up to, but not including, the fixed releases. The advisory also notes that the equipment is deployed worldwide and that the vendor headquarters are in the United States, which means the issue has both domestic and global relevance.
This disclosure fits a pattern that has become increasingly famiurity: a control device exposes an externally reachable protocol, the protocol lacks adequate authentication on a critical path, and an attacker can influence a safety-relevant process without needing deep footholds first. CISA’s own historical advisories show that this is a recurring class of failure across vendors and sectors, not an isolated lapse. The lesson is that industrial convenience features are often the same features that become attack surfaces.
At a technical level, the advisory says the attacker can send Modbus packets to manipulate register values that feed odorant injection logic. That matters because Modbus is a classic industrial protocol designed around trust and simplicity, not modern identity controls. When authentication is absent or weak, the protocol becomes a write path into process logic rather than a mere telemetry channel.
The impact description is unusually c consequence is too much or too little odorant being injected into a gas line. Too little odorant can reduce leak detectability, which raises safety risks and can complicate emergency response. Too much odorant can create operational problems of its own, including nuisance alarms, product waste, and compliance concerns.
That is why the advisory is more alarming than a generic “unauthorized access” nonot just browsing configuration screens; they are altering the data path that informs a safety-critical actuation function. In industrial systems, that is the difference between viewing the process and steering it.
Key implications include:
CISA identifies the affected equipment as known_affected, which removes ambiguity about whether the problem is theoretical or already validated by the vendor. The advisory also states that no known public expltargeting this vulnerability had been reported to CISA at the time of publication. That is reassuring only in the narrowest sense; the absence of public exploitation is not the same as the absence of adversary interest.
That complication is normal in OT, but it is also exactly why attackers target it. The more fragmented the installed base, the easier it is for defenders to fall behind on version tracking. In a gas infrastructure context, version confusion is more than an n become a process safety issue.
Horner’s documentation confirms that firmware updates for Prime-series controllers are delivered via removable media and that the
Horner’s release pages also show recent firmware activity, including 15.76 for XL4-class devices and 17.30 for Prime-class controllers. Those release references are useful because they indicate the vendor ecosystem is actively maintained, but they also imply that patching may require matching the correct controller generation to the correct branch. In OT, a mismatched update is not a nuisance; it can be a downtime event.
The vendor guidance around SD-card hygiene is practical and telling. GPL Odorizers tells users to clear old files, preserve only required folders and license files, and deploy the extracted update package to the card root. That may sound mundane, but it underscores a common OT truth: the maintenance process is part of the security perimeter.
CISA’s wording indicates the attacker can send packets remotely and low-privileged, which suggests there is either an exposed service or an accessible trust boundary that should not have been reachable in the first place. That is exactly the kind of problem defenders see when operational convenience outpaces securityocess controller accepts writes from the wrong place, the protocol is no longer the problem alone; the network design is.
This is why the advisory’s recommended mitigations focus so heavily on exposure reduction. CISA tells organizations to minimize network exposure, isolate control networks behind firewalls, and use VPNs only as part of a broader defense-in-depth strategy. That guidance reflects the reality that protocol hardening alone rarely solves an OT trust problem.
A usedvisory is as a checklist of what should never have been left open:
Horner’s update guide explains that operators can use a non-bootable microSD card or USB drive, place the firmware package at the root, and invoke the upgrade from the controller’s System menu or system registers. The documentation also says the system will reboot after completion and that version numbers should be checked afterward. That procedural detail is important because successful deployment should be confirmed on-device, not assumed from the presence of a file copy.
Horner’s firmware documentation also warns that firmware upgrades can clear program data and register data, unless the operator intentionally uses retention options. That means remediation teams must plan backup, rollback, and verification before they start. In plain terms, you do not patch these systems the way you patch a browser.
The practical sequence for operators looks like this:
For operators in gas distribution and related critical manufacturing environments, the issue is even more concrete. The advisory describes a condition that could alter odorant injection levels, which means the business impact includes safety, regulatory compliance, and process quality, not just cybersecurity metrics. That broadens the incident response conversation far beyond the IT department.
The advisory’s global deployment note also means multinational operators may face inconsistent remediation timelines, especially if local maintenance windows, safety rules, or remote-access policies differ by region. That nts, many rules* problem, and it usually slows patch adoption even when everyone agrees the patch is urgent.
Important operational takeaways:
The consistency of these aething uncomfortable about OT security maturity. Vendors have improved disclosure and patching, but many deployed systems still depend on trust assumptions that are no longer reasonable on modern networks. The challenge is not just vulnerability removal; it is redesigning deployment patterns so that a single exposed service cannot influence a critical process.
CISA’s repeated emphasis on segmentation, VPN use, and exposure reduction is not boilerplate; it is a response to this structural problem. In systems like GPL750, the vulnerability is not only whether the attacker can send packets but whether the architecture allows those packets to arrive at all. That is why defense in depth is still the central principle in OT.
There is also an opportunity here to improve more than one control at once. A patch campaign can become a catalyst for network segmentation, asset cleanup, and backup validation, all of which strengthen the environment beyond this single issue. In that sense, the advisory can be used as a forcing function for broader OT hygiene.
Another concern is operational inertia. Firmware and application updates in OT are often dol, plant uptime requirements, and the need for field access. That delay is understandable, but it also means an attacker may have a longer runway than defenders expect.
The broader lesson is that OT vendors can no longer rely on protocol familiarity as a substitute for access control. If a register write can influence a safety-relevant physical process, then authen, and monitoring need to be treated as first-class designience is not a security model*.
Watch these items closely:
Source: CISA GPL Odorizers GPL750 | CISA
CISA’s advisory fram306: Missing Authentication for Critical Function, with a CVSS 3.1 score of 8.6 HIGH. That rating reflects a particularly worrying combination: network reachability, no user interaction, no required privileges, and a direct effect on system behavior. In other words, this is not a bug that merely leaks data or crashes a dashboard; it alters the logic that governs a real-world industrial control action.
The affected product list is specific and operationally. CISA identifies GPL750 variants on XL4, XL4 Prime, XL7, and XL7 Prime** controller families, with vulnerable ranges beginning at early firmware milestones and extending up to, but not including, the fixed releases. The advisory also notes that the equipment is deployed worldwide and that the vendor headquarters are in the United States, which means the issue has both domestic and global relevance.
This disclosure fits a pattern that has become increasingly famiurity: a control device exposes an externally reachable protocol, the protocol lacks adequate authentication on a critical path, and an attacker can influence a safety-relevant process without needing deep footholds first. CISA’s own historical advisories show that this is a recurring class of failure across vendors and sectors, not an isolated lapse. The lesson is that industrial convenience features are often the same features that become attack surfaces.
 What the Vulnerability Actually Means
What the Vulnerability Actually Means
At a technical level, the advisory says the attacker can send Modbus packets to manipulate register values that feed odorant injection logic. That matters because Modbus is a classic industrial protocol designed around trust and simplicity, not modern identity controls. When authentication is absent or weak, the protocol becomes a write path into process logic rather than a mere telemetry channel.The impact description is unusually c consequence is too much or too little odorant being injected into a gas line. Too little odorant can reduce leak detectability, which raises safety risks and can complicate emergency response. Too much odorant can create operational problems of its own, including nuisance alarms, product waste, and compliance concerns.
Why register manipulation is so serious
Industrial confinal behavior from a small set of input registers, flags, timers, and scaling values. If an attacker can change those values, they may not need to rewrite the whole application or defeat the logic engine. They only need to bend the inputs far enough to change the physical outcome, which is often easier than many defenders assume.That is why the advisory is more alarming than a generic “unauthorized access” nonot just browsing configuration screens; they are altering the data path that informs a safety-critical actuation function. In industrial systems, that is the difference between viewing the process and steering it.
Key implications include:
- Process integrity is at risk, not just device confidentiality.
- **Op may remain intact while the output becomes unsafe or noncompliant.
- **Detection may be difficuls like a normal register write.
- Protocol trust assumptions are the root of the exposure.
ions and Scope
CISA identifies the affected equipment as known_affected, which removes ambiguity about whether the problem is theoretical or already validated by the vendor. The advisory also states that no known public expltargeting this vulnerability had been reported to CISA at the time of publication. That is reassuring only in the narrowest sense; the absence of public exploitation is not the same as the absence of adversary interest.
Why the version split matters
The version thresholds suggest multiple product baselines and likely multiple internal build trains. In practice, that means remediation may not be as simple as applying one universal patch. Operatorsinstalled controller to its exact software lineage, then coordinate both application-layer and firmware-layer updates.That complication is normal in OT, but it is also exactly why attackers target it. The more fragmented the installed base, the easier it is for defenders to fall behind on version tracking. In a gas infrastructure context, version confusion is more than an n become a process safety issue.
Vendor and Platform Context
GPL Odorizers recommends updating to the latest software version of the GPL750 together with the latest Horner Automation firmware for the XL4, XL4 Prime, XL7, and XL7 Prime devices. That dual dependency matters because the vuars to sit at the intersection of the vendor application and the controller platform underneath it. The fix is therefore not merely an app update or a firmware refresh in isolation; it is a coordinated change set.Horner’s documentation confirms that firmware updates for Prime-series controllers are delivered via removable media and that the
.ZIP package should be placed directly on the root of a microSD card or USB drive. The documentation also warns that updating firmware clears the application program, sc and register data unless the operator takes explicit backup and retention steps. That makes remediation operationally heavier than a casual reboot-and-patch cycle.The platform layer is part of the risk
That dependency chain matters because the security weakness is not isolated to one small binary. It lives inside a broader industrial stack that includes controller firmware, vendor logic, removable-media update workflows, and field deployment practices. Each of those layers can either reduce risk or create a bottleneck when the patch has to move quickly.Horner’s release pages also show recent firmware activity, including 15.76 for XL4-class devices and 17.30 for Prime-class controllers. Those release references are useful because they indicate the vendor ecosystem is actively maintained, but they also imply that patching may require matching the correct controller generation to the correct branch. In OT, a mismatched update is not a nuisance; it can be a downtime event.
The vendor guidance around SD-card hygiene is practical and telling. GPL Odorizers tells users to clear old files, preserve only required folders and license files, and deploy the extracted update package to the card root. That may sound mundane, but it underscores a common OT truth: the maintenance process is part of the security perimeter.
Why Modbus Is the Weak Link Here
Modbus remains popular because it is lightweight, well understood, and widely supported. Those same strengths become liabilities when systems expose Modbus pathways without authentication or network segmentation. In a trusted internal network, the protocmodern threat environment, simplicity can turn into a direct command channel.CISA’s wording indicates the attacker can send packets remotely and low-privileged, which suggests there is either an exposed service or an accessible trust boundary that should not have been reachable in the first place. That is exactly the kind of problem defenders see when operational convenience outpaces securityocess controller accepts writes from the wrong place, the protocol is no longer the problem alone; the network design is.
The protocol problem is really a deployment problem
Modbus itself is not “bad” so much as it is assumed trusted. The vulnerability becomes dangerous because the device accepts critical values over a channel that does not seem to require strong identity proofing. Once a service accepts writes from an attacker, the distinction betweentrol begins to disappear.This is why the advisory’s recommended mitigations focus so heavily on exposure reduction. CISA tells organizations to minimize network exposure, isolate control networks behind firewalls, and use VPNs only as part of a broader defense-in-depth strategy. That guidance reflects the reality that protocol hardening alone rarely solves an OT trust problem.
A usedvisory is as a checklist of what should never have been left open:
- Unauthenticated access to critical write functions.
- Network paths from untrusted segments to process logic.
- Default trust in industrial protocol traffic.
- Poor separation between business and control networks.
- Weak monitoring for register-level tampering.
Path
The vendor’s mitigation guidance is direct: update the GPL750 software in connection with the latest Horner firmware for the relevant controller family. CISA adds that organizations should verify the update process carefully, especially because firmware updates can alter or clear operational state. In industrial environments, the patch itself is only half the job; vahalf.Horner’s update guide explains that operators can use a non-bootable microSD card or USB drive, place the firmware package at the root, and invoke the upgrade from the controller’s System menu or system registers. The documentation also says the system will reboot after completion and that version numbers should be checked afterward. That procedural detail is important because successful deployment should be confirmed on-device, not assumed from the presence of a file copy.
Why update discipline matters
The advisory mentions that if IT permissions prevent direct access to microSD cards, GPL Odorizers can provide preconfigured SD cards for technicians. That is a pragmatic workaround, but it also reveals the operational friction around OT patching. If the easiest path is to ship cards or coordinate field service, the attack window may remain open longer than anyone would like.Horner’s firmware documentation also warns that firmware upgrades can clear program data and register data, unless the operator intentionally uses retention options. That means remediation teams must plan backup, rollback, and verification before they start. In plain terms, you do not patch these systems the way you patch a browser.
The practical sequence for operators looks like this:
- Identify every GPL750 deployment and map the exact controller model.
- Verify the inirmware versions.
- Back up programs, screens, and register data.
- Apply the vendor-recommended software and firmware updates.
- Recheck controller version and process behavior after reboot.
Enterprise and Operator Impact
For enterprises, the immediate issue is asset visibility. If you do not know exactly where GPL750 devices are deployed, you cannot tell whether the vulnerability is reachable. That is a familiar enterprise blind spot in OT: the security team may understand the advisory, but the operations team owns the plant floor, and the two sides may not share a live inventory.For operators in gas distribution and related critical manufacturing environments, the issue is even more concrete. The advisory describes a condition that could alter odorant injection levels, which means the business impact includes safety, regulatory compliance, and process quality, not just cybersecurity metrics. That broadens the incident response conversation far beyond the IT department.
Enterprise concerns differ from field concerns
An enterprise SOC may look for anomalous network traffic, authentication failures, or device fingerprints.nwhile, is likely to care about whether the odorization process remains within expected tolerances after the patch. Both views are necessary, but they are not interchangeable.The advisory’s global deployment note also means multinational operators may face inconsistent remediation timelines, especially if local maintenance windows, safety rules, or remote-access policies differ by region. That nts, many rules* problem, and it usually slows patch adoption even when everyone agrees the patch is urgent.
Important operational takeaways:
- Inventory exact GPL750 deployments first.
- Separate network reachability from mere device ownership.
- Treat odorant injection integrity as a process safety issue.
- Expect **maintenance schedulieal-world patch timeline.
How This Fits the Broader ICS Threat Landscape
This advisory is not just about one odorizer platform. It reflects an enduring industrial security pattern where low-friction control protocols and missing access controls create pathways into the physical layer. CISA has repeatedly warned about similar weaknesses inbuilding-automation products, and those warnings tend to follow the same arc: a smals a meaningful operational risk.The consistency of these aething uncomfortable about OT security maturity. Vendors have improved disclosure and patching, but many deployed systems still depend on trust assumptions that are no longer reasonable on modern networks. The challenge is not just vulnerability removal; it is redesigning deployment patterns so that a single exposed service cannot influence a critical process.
Why the pattern keeps repeating
Industrial systems often evolve by accretion. A controller gets a web interface, then remote diagnostics, then remote maintenance, then compatibility layers for older tooling. Each layer seems sensible in isolation, but the cumulative effect is a larger attack surface than the original system design ever anticipated. That is how “useful features” become security liabilities.CISA’s repeated emphasis on segmentation, VPN use, and exposure reduction is not boilerplate; it is a response to this structural problem. In systems like GPL750, the vulnerability is not only whether the attacker can send packets but whether the architecture allows those packets to arrive at all. That is why defense in depth is still the central principle in OT.
Strengths and Opportunities
The good news is that this is a vulnerability with a clear remediation story. The vendor has identified the affected lines, CISA has published practical guidance, and Horner’s firmware update documentation makes the deployment path concrete.ready maintain disciplined OT inventories should be able to move faster than the industry average.There is also an opportunity here to improve more than one control at once. A patch campaign can become a catalyst for network segmentation, asset cleanup, and backup validation, all of which strengthen the environment beyond this single issue. In that sense, the advisory can be used as a forcing function for broader OT hygiene.
- Clear vulnerability scope and version boundaries.
- Available vendor remediation guidance.
- Practical controller firmware update path.
- No known public exploitation reported at publication time.
- Strong alignment with standard CISA hardening practices.
- A chance to inventory and segment control networks better.
Risks and Concerns
The most obvious concern is that the exposure is not merely theoretical. CISA’s description implies a path from network traffic to process manipulation, which is exactly the sort of thing defenders want to prevent before any active exploitation appears. If attackers discover exposed systems in the field, the consequence could extend into physical safety and supply reliability.Another concern is operational inertia. Firmware and application updates in OT are often dol, plant uptime requirements, and the need for field access. That delay is understandable, but it also means an attacker may have a longer runway than defenders expect.
- Control-network exposure may brs believe.
- Register tampering can be subtle and hard to detect.
- Firmware updates may disrupt application state if not planned carefully.
- Version sprgenerations can slow remediation.
- Safety and compliance impacts can emerge even without a visible outage.
- The lack of public exploitation is not a reason to delay patching.
Looking Ahead
What happens next will depend less on the existence of the advisory than on how quickly operators can reconcile inventories, schedules, and field access. In well-run environments, this should become a pri immediately. In loosely managed environments, it may linger until the first security audit, the first abnormal odorant reading, or the first external scan reveals the exposed service.The broader lesson is that OT vendors can no longer rely on protocol familiarity as a substitute for access control. If a register write can influence a safety-relevant physical process, then authen, and monitoring need to be treated as first-class designience is not a security model*.
Watch these items closely:
- Confirmation of patched releases for each GPL750 branch.
- Adoption of updated Horner firmware in theCISA updates indicating exploitation or increased urgency.
- Whether operato improve network segmentation.
- Evidence of related Modbus exposure orization or gas infrastructure products.
Source: CISA GPL Odorizers GPL750 | CISA
Last edited: